Escolar Documentos
Profissional Documentos
Cultura Documentos
Bulletin (Part 2 of Candidate Handbook) : Exam Certification Objectives & Outcome Statements
Enviado por
Jawaid IqbalTítulo original
Direitos autorais
Formatos disponíveis
Compartilhar este documento
Compartilhar ou incorporar documento
Você considera este documento útil?
Este conteúdo é inapropriado?
Denunciar este documentoDireitos autorais:
Formatos disponíveis
Bulletin (Part 2 of Candidate Handbook) : Exam Certification Objectives & Outcome Statements
Enviado por
Jawaid IqbalDireitos autorais:
Formatos disponíveis
Bulletin (Part 2 of Candidate Handbook)
Exam Certification Objectives & Outcome Statements
The topic areas for each exam part follow: Backdoors & Trojan Horses The candidate will demonstrate a detailed understanding of how Backdoors are used to gain access to systems, and how to defend systems. Buffer Overflows The candidate will demonstrate an understanding of what a buffer overflow is, how they are created, and how to defend against them. Additionally, candidates will demonstrate a high-level understanding of how attackers use common tools to create and maintain a backdoor on a compromised system. Covering Tracks: Networks The candidate will demonstrate an understanding of how attackers use tunneling and covert channels to cover their tracks on a network, and the strategies involved in defending against them. Covering Tracks: Systems The candidate will demonstrate an understanding of how attackers hide files and directories on Windows and Linux hosts and how they attempt to cover their tracks. Denial of Service Attacks The candidate will demonstrate a comprehensive understanding of the different kinds of Denial of Service attacks and how to defend against them. Exploiting Systems using Netcat The candidate will demonstrate an understanding of how to properly use the Netcat utility and how to defend against it. Format String Attacks The candidate will demonstrate a comprehensive understanding of how format string attacks work and how to defend against them. Incident Handling Overview and Preparation The candidate will demonstrate an understanding of what Incident Handling is, why it is important, and an understanding of best practices to take in preparation for an Incident. Incident Handling Phase 2 Identification The candidate will demonstrate an understanding of important strategies to gather events, analyze them, and determine if we have an incident. Incident Handling Phase 3 Containment The candidate will demonstrate an understanding of high-level strategies to prevent an attacker from causing further damage to the victim after discovering the incident. Incident Handling: Recovering and Improving Capabilities The candidate will demonstrate an understanding of the general approaches to get rid of the attacker's artifacts on compromised machines, the general strategy to safely restore operations, and the importance of the incident report and "lessons learned" meetings. IP Address Spoofing The candidate will demonstrate an understanding of what IP Spoofing is, the three different types of spoofing, and strategies to defend against it. Network Sniffing The candidate will know what network sniffing is, how to use common sniffing tools, and how to defend against sniffers. Password Attacks The candidate will demonstrate a detailed understanding of the three methods of password cracking. Reconnaissance The candidate will demonstrate an understanding of public and open source reconnaissance techniques. Rootkits The candidate will demonstrate an understanding of how user-mode and kernel-mode rootkits operate, what their capabilities are and how to defend against them. Scanning: Host Discovery The candidate will demonstrate an understanding of the tools and techniques used for host discovery on wired and wireless networks. Scanning: Network and Application Vulnerability scanning and tools
The candidate will demonstrate an understanding of the fundamentals of network and application vulnerability scanners, common commercial and open source tools, and how to defend against them. Scanning: Network Devices (Firewall rules determination, fragmentation, and IDS/IPS evasion) The candidate will demonstrate an understanding of how to use Firewalk to determine firewall policies, the general principles of IP fragmentation attacks, why they are used, as well as the ability to identify them. Scanning: Service Discovery The candidate will demonstrate an understanding of the tools and techniques used for network mapping, port scanning, and passive fingerprinting techniques and how to defend against them. Session Hijacking, Tools and Defenses The candidate will demonstrate an understanding of the definition of session hijacking, the two methods commonly used and why it is effective. Additionally, the candidate will demonstrate an understanding of how to identify common hijacking tools and the strategies to prepare for, identify and contain hijacking attacks. Types of Incidents The candidate will demonstrate an understanding of multiple types of incidents, including espionage, unauthorized use, intellectual property, and insider threats and apply strategies to prevent or address these cases. Virtual Machine Attacks The candidate will demonstrate an understanding of the virtual machine environment from an attackers perspective, including targets and detection, and how to defend against threats. Web Application Attacks The candidate will demonstrate an understanding of the value of the Open Web Application Security Project (OWASP), as well as different Web App attacks such as account harvesting, SQL injection, Cross-Site Scripting and other Web Session attacks. Worms, Bots & Bot-Nets The candidate will demonstrate a detailed understanding of what worms, bots and bot-nets are, and how to protect against them.
Você também pode gostar
- Fleet ManagementDocumento8 páginasFleet ManagementDiana LorenaAinda não há avaliações
- Dissolved OxygenDocumento2 páginasDissolved OxygenAnonymous atBeojaAinda não há avaliações
- The Certified Ethical Hacker Exam - version 8 (The concise study guide)No EverandThe Certified Ethical Hacker Exam - version 8 (The concise study guide)Nota: 3 de 5 estrelas3/5 (9)
- Biological ExerciseDocumento6 páginasBiological ExerciseTanmoy BasakAinda não há avaliações
- Instruction Manual STR 155 RL-1Documento24 páginasInstruction Manual STR 155 RL-1VENDI100% (3)
- 20 - Ransomware Detection Using Machine Learning - A SurveyDocumento24 páginas20 - Ransomware Detection Using Machine Learning - A SurveylcoqzxnmAinda não há avaliações
- SLTRT Service Level Testing Reporting ToolDocumento110 páginasSLTRT Service Level Testing Reporting ToolChedli Dhouibi50% (2)
- Certified Information Security Expert (CISE Level 1 v2) Detailed Course ModuleDocumento18 páginasCertified Information Security Expert (CISE Level 1 v2) Detailed Course ModuleAkhil SreenadhAinda não há avaliações
- Ball MillsDocumento8 páginasBall MillsBoy Alfredo PangaribuanAinda não há avaliações
- NX Training Syllabus Module IDocumento5 páginasNX Training Syllabus Module IDharaiya HardikAinda não há avaliações
- Advanced clutter options for radio propagation modelingDocumento40 páginasAdvanced clutter options for radio propagation modelingLaura VillarrealAinda não há avaliações
- 7 Requirements of Data Loss PreventionDocumento8 páginas7 Requirements of Data Loss PreventionJawaid IqbalAinda não há avaliações
- Certified Ethical Hacker (CEH) v3.0 Official CourseDocumento578 páginasCertified Ethical Hacker (CEH) v3.0 Official CourseSomeone100% (2)
- Wired and Wireless NetworksDocumento17 páginasWired and Wireless NetworksManzoor SaiyedAinda não há avaliações
- Threats and CountermeasuresDocumento22 páginasThreats and CountermeasuresKeerthana SudarshanAinda não há avaliações
- Final Cisco EnglishDocumento29 páginasFinal Cisco EnglishKelson AlmeidaAinda não há avaliações
- Tutorial 12: Question 01. Elaborate The Necessity of The Penetration Testing Execution StandardDocumento7 páginasTutorial 12: Question 01. Elaborate The Necessity of The Penetration Testing Execution StandardSubesh Khadka Networking and IT SecurityAinda não há avaliações
- Ethical Hacking ReportDocumento22 páginasEthical Hacking ReportDhyana Swain50% (2)
- On Ethical Hacking: Prepared By:-Bhargav Dabhi (090010107040)Documento18 páginasOn Ethical Hacking: Prepared By:-Bhargav Dabhi (090010107040)Rijy LoranceAinda não há avaliações
- ANAD Ethical HackingDocumento4 páginasANAD Ethical HackingIvan DoriAinda não há avaliações
- Network HackingDocumento10 páginasNetwork Hackingguptanitesh7276Ainda não há avaliações
- Module 2Documento19 páginasModule 2usiddik331Ainda não há avaliações
- Usbcat - Towards An Intrusion Surveillance Toolset: Chris ChapmanDocumento13 páginasUsbcat - Towards An Intrusion Surveillance Toolset: Chris ChapmanFlavio58ITAinda não há avaliações
- ETHICAL Hacking Till MidDocumento11 páginasETHICAL Hacking Till MidAyushAinda não há avaliações
- Network and System Security CEH TrainingDocumento3 páginasNetwork and System Security CEH TrainingSamuel GetachewAinda não há avaliações
- ETHICAL HACKING TECHNIQUESDocumento12 páginasETHICAL HACKING TECHNIQUESmani3686Ainda não há avaliações
- Pen TestDocumento5 páginasPen TestHiepHenryAinda não há avaliações
- Chapter 3: Tools and Methods Used in CybercrimeDocumento34 páginasChapter 3: Tools and Methods Used in CybercrimeNarasimha MurthyAinda não há avaliações
- Assignment 1Documento19 páginasAssignment 1thazni kassimAinda não há avaliações
- Applied Sciences: A New Proposal On The Advanced Persistent Threat: A SurveyDocumento22 páginasApplied Sciences: A New Proposal On The Advanced Persistent Threat: A Surveycena018Ainda não há avaliações
- Lab 1 - Researching Network Attacks and Security Audit ToolsDocumento5 páginasLab 1 - Researching Network Attacks and Security Audit ToolsJood salemAinda não há avaliações
- Fin Irjmets1695749724Documento7 páginasFin Irjmets1695749724discoveryclbAinda não há avaliações
- Ethical HackingDocumento50 páginasEthical HackingGOLDEN BIRDAinda não há avaliações
- Seminar Report On HackingDocumento20 páginasSeminar Report On HackingJamesCarter100% (1)
- Ethical Hacking and Counter Measures Course OutlineDocumento7 páginasEthical Hacking and Counter Measures Course Outlineresearch.aiAinda não há avaliações
- Ethical Hacking ReportDocumento22 páginasEthical Hacking ReportSweta Leena Panda100% (1)
- Certified Information Security Expert (CISE Level 1 v2) Detailed Course ModuleDocumento18 páginasCertified Information Security Expert (CISE Level 1 v2) Detailed Course ModuleAmila KulathungaAinda não há avaliações
- Cyber Hacker Project 1Documento17 páginasCyber Hacker Project 1Jai ShreeramAinda não há avaliações
- Information Security MidDocumento2 páginasInformation Security MidAqsa NoumanAinda não há avaliações
- Unit II - Cyber OffensesDocumento57 páginasUnit II - Cyber Offensesakshaymm1616Ainda não há avaliações
- ReportDocumento12 páginasReportpkpscAinda não há avaliações
- Attacker Profiles Cyber-Attack Strategies 5Documento5 páginasAttacker Profiles Cyber-Attack Strategies 5serdal bilginAinda não há avaliações
- Executive Summary ch2Documento5 páginasExecutive Summary ch2Alfredo Con AlejandrinaAinda não há avaliações
- Ethical Hacking..Documento18 páginasEthical Hacking..Sad JokerAinda não há avaliações
- GIAC GCIH Certification Syllabus and Prep Guide - EDUSUM - EDUSUMDocumento3 páginasGIAC GCIH Certification Syllabus and Prep Guide - EDUSUM - EDUSUMdiogodonadoniAinda não há avaliações
- aricle-Towards a Framework to Detect Multi-StageDocumento6 páginasaricle-Towards a Framework to Detect Multi-StageZakariya KamagatéAinda não há avaliações
- Radware’s Behavioral Server Cracking Protection DefensePro WhitepaperDocumento10 páginasRadware’s Behavioral Server Cracking Protection DefensePro WhitepaperichilovAinda não há avaliações
- 1 InstructionsDocumento10 páginas1 InstructionsRennyAinda não há avaliações
- Understanding Ethical Hacking: Tools, Techniques and CertificationsDocumento19 páginasUnderstanding Ethical Hacking: Tools, Techniques and CertificationsRenjithAinda não há avaliações
- Network Security Essentials for BusinessesDocumento11 páginasNetwork Security Essentials for BusinessesRenzo FloresAinda não há avaliações
- Cyber Kill ChainDocumento4 páginasCyber Kill ChainAbhi NairAinda não há avaliações
- Cryptography, Network Security and Cyber Laws Notes 2019-2020Documento23 páginasCryptography, Network Security and Cyber Laws Notes 2019-2020Himanshu KumarAinda não há avaliações
- Security/Hacking: 2 Short CoursesDocumento1 páginaSecurity/Hacking: 2 Short Coursesabdel_lakAinda não há avaliações
- Ethical Hacking PDFDocumento127 páginasEthical Hacking PDFPrudhvi MaheshwaramAinda não há avaliações
- Introduction To Wireless HackingDocumento6 páginasIntroduction To Wireless Hackingparth.parsewar.csAinda não há avaliações
- Penetration TestingDocumento4 páginasPenetration TestingsipraAinda não há avaliações
- A Presentation On Ethical HackingDocumento30 páginasA Presentation On Ethical Hackingʚĩɞ IkRàm AkCha ʚĩɞ100% (1)
- A Presentation On Ethical HackingDocumento30 páginasA Presentation On Ethical HackingMukesh YadavAinda não há avaliações
- For Seminar On Ethical HackingDocumento30 páginasFor Seminar On Ethical Hackingitsjusttwoofus1420Ainda não há avaliações
- Network ThreatsDocumento16 páginasNetwork ThreatsEmma MakinAinda não há avaliações
- Unit 2Documento15 páginasUnit 2Gangisetti SrihariAinda não há avaliações
- Journal of Network and Computer Applications: Daniel Gibert, Carles Mateu, Jordi PlanesDocumento22 páginasJournal of Network and Computer Applications: Daniel Gibert, Carles Mateu, Jordi PlanesRahmat FebriansyahAinda não há avaliações
- Pentest RoadmapDocumento3 páginasPentest RoadmaplionciAinda não há avaliações
- Ethical HackingDocumento30 páginasEthical HackingMukesh YadavAinda não há avaliações
- Intrusion Bit Detection in Data Packet Transmitted Over Covert Channels Using K-NN Machine Learning AlgorithmDocumento7 páginasIntrusion Bit Detection in Data Packet Transmitted Over Covert Channels Using K-NN Machine Learning AlgorithmIJRASETPublicationsAinda não há avaliações
- CEH Version 7: WWW - Anninhmang.edu - VNDocumento4 páginasCEH Version 7: WWW - Anninhmang.edu - VNSilver SilverphoenixAinda não há avaliações
- Cyber Security ApponixDocumento4 páginasCyber Security ApponixAshokAinda não há avaliações
- 5831-Article Text-20365-1-10-20220127Documento8 páginas5831-Article Text-20365-1-10-20220127Akyll TutorAinda não há avaliações
- CEH Certification Notes: Complete Guide to Ethical Hacking ModulesDocumento97 páginasCEH Certification Notes: Complete Guide to Ethical Hacking ModulesSachjith MAinda não há avaliações
- 64/64 Kbps 128/128 Kbps 256/128 KBPS: Speed Monthly Bandwidth Setup STC Setup STC Monthly ADSL-DataDocumento1 página64/64 Kbps 128/128 Kbps 256/128 KBPS: Speed Monthly Bandwidth Setup STC Setup STC Monthly ADSL-DataJawaid IqbalAinda não há avaliações
- Design PrinciplesDocumento1 páginaDesign PrinciplesJawaid IqbalAinda não há avaliações
- PRD 5016Documento8 páginasPRD 5016Jawaid IqbalAinda não há avaliações
- Microbial Water TestingDocumento3 páginasMicrobial Water TestingJawaid IqbalAinda não há avaliações
- Competence and TrainingDocumento2 páginasCompetence and TrainingJawaid IqbalAinda não há avaliações
- What Is Virtual Machine EscapeDocumento2 páginasWhat Is Virtual Machine EscapesjmpakAinda não há avaliações
- PGH ChangementDocumento1 páginaPGH ChangementJawaid IqbalAinda não há avaliações
- Project Training OutlineDocumento1 páginaProject Training OutlineJawaid IqbalAinda não há avaliações
- Bulletin (Part 2 of Candidate Handbook) : Exam Certification Objectives & Outcome StatementsDocumento2 páginasBulletin (Part 2 of Candidate Handbook) : Exam Certification Objectives & Outcome StatementsJawaid IqbalAinda não há avaliações
- CE Course Reg Form Spring 2008Documento1 páginaCE Course Reg Form Spring 2008Jawaid IqbalAinda não há avaliações
- CE Course Notice Fall 2007Documento2 páginasCE Course Notice Fall 2007Jawaid IqbalAinda não há avaliações
- Mohammad Tariq NilDocumento7 páginasMohammad Tariq NilJawaid IqbalAinda não há avaliações
- PGS PDFDocumento2 páginasPGS PDFJawaid IqbalAinda não há avaliações
- MOI Payment Folders: New Reply Delete Archive Junk Sweep Move To CategoriesDocumento1 páginaMOI Payment Folders: New Reply Delete Archive Junk Sweep Move To CategoriesJawaid IqbalAinda não há avaliações
- Prof. Joseph M. Kizza - 07Documento11 páginasProf. Joseph M. Kizza - 07Jawaid IqbalAinda não há avaliações
- IG 2.4 - Information Lifecycle Policy - 17 DecDocumento27 páginasIG 2.4 - Information Lifecycle Policy - 17 DecJawaid IqbalAinda não há avaliações
- Lecturer 5Documento0 páginaLecturer 5Jawaid IqbalAinda não há avaliações
- Federation 2.0: An Identity EcosystemDocumento6 páginasFederation 2.0: An Identity EcosystemJawaid IqbalAinda não há avaliações
- Final MadnesDocumento16 páginasFinal MadnessjmpakAinda não há avaliações
- Zubulake - Res GestaeDocumento3 páginasZubulake - Res GestaeJawaid IqbalAinda não há avaliações
- PGS PDFDocumento2 páginasPGS PDFJawaid IqbalAinda não há avaliações
- What Is Virtual Machine EscapeDocumento2 páginasWhat Is Virtual Machine EscapesjmpakAinda não há avaliações
- Section 2: Storage Networking Technologies and VirtualizationDocumento36 páginasSection 2: Storage Networking Technologies and VirtualizationJawaid IqbalAinda não há avaliações
- Shaffer The2010eDiscoveryPrimer 022510v3Documento2 páginasShaffer The2010eDiscoveryPrimer 022510v3Jawaid IqbalAinda não há avaliações
- What Is Virtual Machine EscapeDocumento2 páginasWhat Is Virtual Machine EscapesjmpakAinda não há avaliações
- Auditing General and Application ControlsDocumento4 páginasAuditing General and Application ControlsSomshubhraAinda não há avaliações
- Law (8) of 2002 Commercial Agents - English PDFDocumento11 páginasLaw (8) of 2002 Commercial Agents - English PDFlondoncourseAinda não há avaliações
- Rectify Binary Plate Efficiency BubblesDocumento4 páginasRectify Binary Plate Efficiency BubblesCsaba AndrásAinda não há avaliações
- Udayanandan, Notes On Tensors PDFDocumento56 páginasUdayanandan, Notes On Tensors PDFhristos314Ainda não há avaliações
- Adobe Photoshop: The EditingDocumento10 páginasAdobe Photoshop: The EditingMer Cjielo BalloonsAinda não há avaliações
- Brandt M FR Btd500blnDocumento74 páginasBrandt M FR Btd500blnStéphane JoussetAinda não há avaliações
- CRCM Manual 2 9 16Documento33 páginasCRCM Manual 2 9 16Kamagara Roland AndrewAinda não há avaliações
- Power Tool Switches: Catalog 1308650 Issued 1-01Documento18 páginasPower Tool Switches: Catalog 1308650 Issued 1-01Gamal AhmadAinda não há avaliações
- Partitioned Data Set Extended Usage Guide Guide: Front CoverDocumento364 páginasPartitioned Data Set Extended Usage Guide Guide: Front CoverCsutka PocsAinda não há avaliações
- Tractor 2017 Catalogue WebDocumento36 páginasTractor 2017 Catalogue WebAnonymous 1XBCMXAinda não há avaliações
- Desizing of CottonDocumento16 páginasDesizing of CottonDeepali RastogiAinda não há avaliações
- Pure Chem p2 - 26pgDocumento26 páginasPure Chem p2 - 26pgJhomer CrespoAinda não há avaliações
- HVCB Timing ApplicationDocumento52 páginasHVCB Timing Applicationbhuban mohanAinda não há avaliações
- How To Sputter Thin Films of Metal Onto GlassDocumento5 páginasHow To Sputter Thin Films of Metal Onto Glassfred_m_48601Ainda não há avaliações
- Narayana 10 01 24 SR Star Co Scmodel A, B&C Jee Main GTM 12n Key&sDocumento10 páginasNarayana 10 01 24 SR Star Co Scmodel A, B&C Jee Main GTM 12n Key&sReddyAinda não há avaliações
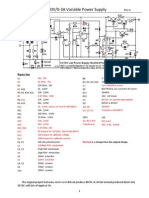
- Modified 0-30V - 0-3A Variable Power Supply - Rev.2Documento2 páginasModified 0-30V - 0-3A Variable Power Supply - Rev.2Manuel Cereijo NeiraAinda não há avaliações
- Earth Gravity and Satellite Orbits CalculationsDocumento9 páginasEarth Gravity and Satellite Orbits CalculationsYoobsan Asaffaa FufaaAinda não há avaliações
- MMMDocumento1 páginaMMMkhan22imranAinda não há avaliações
- 2020 Can Am Off Road - Apache Track Kits Leaflet - enDocumento7 páginas2020 Can Am Off Road - Apache Track Kits Leaflet - enNicolas VillamayorAinda não há avaliações
- Bots and Automation Over Twitter During The U.S. Election: CompropDocumento5 páginasBots and Automation Over Twitter During The U.S. Election: CompropRaninha MoraisAinda não há avaliações
- DatasheetDocumento13 páginasDatasheetebertecnicoAinda não há avaliações
- Introduction To Manufacturing Engineering: Lecturer: Ass - Prof.Dr. Nguyen Tien DuongDocumento14 páginasIntroduction To Manufacturing Engineering: Lecturer: Ass - Prof.Dr. Nguyen Tien DuongTOAN Du100% (1)
- Under Water WeldingDocumento23 páginasUnder Water WeldingNishanth GowdaAinda não há avaliações
- Aviation Week & Space Technology - September 22, 2014 USADocumento60 páginasAviation Week & Space Technology - September 22, 2014 USAJohn David Hoyos MarmolejoAinda não há avaliações