Escolar Documentos
Profissional Documentos
Cultura Documentos
r5210302 Oops Through Java
Enviado por
sivabharathamurthy0 notas0% acharam este documento útil (0 voto)
20 visualizações1 páginaJava is more secure than other languages. Write a while loop to find the smallest n such that n2 is greater than 10,000. Create an inheritance hierarchy of rodent: mouse, gerbil, hamster, etc. In the baseclass, provide methods that are common to all Rodents, and override these in the derived classes to perform different behaviors depending on the specific type of Rodent.
Descrição original:
Direitos autorais
© Attribution Non-Commercial (BY-NC)
Formatos disponíveis
PDF, TXT ou leia online no Scribd
Compartilhar este documento
Compartilhar ou incorporar documento
Você considera este documento útil?
Este conteúdo é inapropriado?
Denunciar este documentoJava is more secure than other languages. Write a while loop to find the smallest n such that n2 is greater than 10,000. Create an inheritance hierarchy of rodent: mouse, gerbil, hamster, etc. In the baseclass, provide methods that are common to all Rodents, and override these in the derived classes to perform different behaviors depending on the specific type of Rodent.
Direitos autorais:
Attribution Non-Commercial (BY-NC)
Formatos disponíveis
Baixe no formato PDF, TXT ou leia online no Scribd
0 notas0% acharam este documento útil (0 voto)
20 visualizações1 páginar5210302 Oops Through Java
Enviado por
sivabharathamurthyJava is more secure than other languages. Write a while loop to find the smallest n such that n2 is greater than 10,000. Create an inheritance hierarchy of rodent: mouse, gerbil, hamster, etc. In the baseclass, provide methods that are common to all Rodents, and override these in the derived classes to perform different behaviors depending on the specific type of Rodent.
Direitos autorais:
Attribution Non-Commercial (BY-NC)
Formatos disponíveis
Baixe no formato PDF, TXT ou leia online no Scribd
Você está na página 1de 1
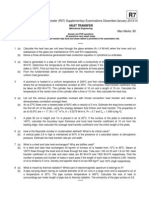
Code No: R5210302 R5
II B.Tech I Semester(R05) Supplementary Examinations, November 2010
OOPS THROUGH JAVA
(Mechanical Engineering)
Time: 3 hours Max Marks: 80
Answer any FIVE Questions
All Questions carry equal marks
?????
1. (a) How is java more secured than other languages?
(b) What is multithreading? How does it improve the performance of java?
(c) Write a while loop to find the smallest n such that n2 is greater than 10,000.
[4+4+8]
2. (a) What is the difference between equality of objects and equality of objects and equality of references
that refer to them?
(b) What is the difference between a public member and a private member of a class?
(c) write an application that computes the value of ex by using the formula:
ex = 1 + x/1! + x2 /2! + x3 /3! + .......... [4+4+8]
3. Create an inheritance hierarchy of Rodent: Mouse, Gerbil, Hamster, etc. In the baseclass, provide
methods that are common to all Rodents, and override these in the derived classes to perform different
behaviors depending on the specific type of Rodent.Create an array of Rodent, fill it with different
specific types of Rodents, and call your base-class methods.Explain what happens. [16]
4. Prove that the fields in an interface are implicitly static and final. [16]
5. (a) Explain throws statement in Java with the help of an example program.
(b) What is the difference between throw and throws statement. [8+8]
6. (a) What is the functionality supported by java related to drawing ellipses and circles.
(b) What is the functionality supported by java related to drawing arcs. [8+8]
7. (a) What is the use of JPasswordField? Explain with an aid of an application program.
(b) What are the differences between JPopupMenu and JMenu? [8+8]
8. Write short notes on:
(a) ”whois” port
(b) URL connection class
(c) Datagram packet. [5+5+6]
?????
Você também pode gostar
- A Heartbreaking Work Of Staggering Genius: A Memoir Based on a True StoryNo EverandA Heartbreaking Work Of Staggering Genius: A Memoir Based on a True StoryNota: 3.5 de 5 estrelas3.5/5 (231)
- The Sympathizer: A Novel (Pulitzer Prize for Fiction)No EverandThe Sympathizer: A Novel (Pulitzer Prize for Fiction)Nota: 4.5 de 5 estrelas4.5/5 (120)
- Devil in the Grove: Thurgood Marshall, the Groveland Boys, and the Dawn of a New AmericaNo EverandDevil in the Grove: Thurgood Marshall, the Groveland Boys, and the Dawn of a New AmericaNota: 4.5 de 5 estrelas4.5/5 (266)
- The Little Book of Hygge: Danish Secrets to Happy LivingNo EverandThe Little Book of Hygge: Danish Secrets to Happy LivingNota: 3.5 de 5 estrelas3.5/5 (399)
- Never Split the Difference: Negotiating As If Your Life Depended On ItNo EverandNever Split the Difference: Negotiating As If Your Life Depended On ItNota: 4.5 de 5 estrelas4.5/5 (838)
- The Emperor of All Maladies: A Biography of CancerNo EverandThe Emperor of All Maladies: A Biography of CancerNota: 4.5 de 5 estrelas4.5/5 (271)
- The Subtle Art of Not Giving a F*ck: A Counterintuitive Approach to Living a Good LifeNo EverandThe Subtle Art of Not Giving a F*ck: A Counterintuitive Approach to Living a Good LifeNota: 4 de 5 estrelas4/5 (5794)
- The World Is Flat 3.0: A Brief History of the Twenty-first CenturyNo EverandThe World Is Flat 3.0: A Brief History of the Twenty-first CenturyNota: 3.5 de 5 estrelas3.5/5 (2259)
- The Hard Thing About Hard Things: Building a Business When There Are No Easy AnswersNo EverandThe Hard Thing About Hard Things: Building a Business When There Are No Easy AnswersNota: 4.5 de 5 estrelas4.5/5 (344)
- Team of Rivals: The Political Genius of Abraham LincolnNo EverandTeam of Rivals: The Political Genius of Abraham LincolnNota: 4.5 de 5 estrelas4.5/5 (234)
- The Gifts of Imperfection: Let Go of Who You Think You're Supposed to Be and Embrace Who You AreNo EverandThe Gifts of Imperfection: Let Go of Who You Think You're Supposed to Be and Embrace Who You AreNota: 4 de 5 estrelas4/5 (1090)
- Hidden Figures: The American Dream and the Untold Story of the Black Women Mathematicians Who Helped Win the Space RaceNo EverandHidden Figures: The American Dream and the Untold Story of the Black Women Mathematicians Who Helped Win the Space RaceNota: 4 de 5 estrelas4/5 (895)
- Elon Musk: Tesla, SpaceX, and the Quest for a Fantastic FutureNo EverandElon Musk: Tesla, SpaceX, and the Quest for a Fantastic FutureNota: 4.5 de 5 estrelas4.5/5 (474)
- The Unwinding: An Inner History of the New AmericaNo EverandThe Unwinding: An Inner History of the New AmericaNota: 4 de 5 estrelas4/5 (45)
- The Yellow House: A Memoir (2019 National Book Award Winner)No EverandThe Yellow House: A Memoir (2019 National Book Award Winner)Nota: 4 de 5 estrelas4/5 (98)
- Sanskrit Subhashit CollectionDocumento110 páginasSanskrit Subhashit Collectionavinash312590% (72)
- Motivation Theories Description and CriticismDocumento14 páginasMotivation Theories Description and CriticismAhmed Elgazzar89% (18)
- EX200Documento7 páginasEX200shubbyAinda não há avaliações
- Healthymagination at Ge Healthcare SystemsDocumento5 páginasHealthymagination at Ge Healthcare SystemsPrashant Pratap Singh100% (1)
- John Wren-Lewis - NDEDocumento7 páginasJohn Wren-Lewis - NDEpointandspaceAinda não há avaliações
- Manual de Operacion y MantenimientoDocumento236 páginasManual de Operacion y MantenimientoalexAinda não há avaliações
- Soundarya Lahari Yantras Part 6Documento6 páginasSoundarya Lahari Yantras Part 6Sushanth Harsha100% (1)
- UAV Design TrainingDocumento17 páginasUAV Design TrainingPritam AshutoshAinda não há avaliações
- A Case On Marketing Strategy of Xiaomi IndiaDocumento39 páginasA Case On Marketing Strategy of Xiaomi IndiaSoumyajeet Rout0% (1)
- R7410407 Operating SystemsDocumento1 páginaR7410407 Operating SystemssivabharathamurthyAinda não há avaliações
- Control Systems (CS) Notes As Per JntuaDocumento203 páginasControl Systems (CS) Notes As Per Jntuasivabharathamurthy100% (3)
- 07A4EC01 Environmental StudiesDocumento1 página07A4EC01 Environmental StudiessivabharathamurthyAinda não há avaliações
- SSC Social Textbook (AP)Documento100 páginasSSC Social Textbook (AP)sivabharathamurthyAinda não há avaliações
- R7410506 Mobile ComputingDocumento1 páginaR7410506 Mobile ComputingsivabharathamurthyAinda não há avaliações
- SSC Telugu (FL) (AP)Documento232 páginasSSC Telugu (FL) (AP)sivabharathamurthyAinda não há avaliações
- R7311205 Distributed DatabasesDocumento1 páginaR7311205 Distributed DatabasessivabharathamurthyAinda não há avaliações
- 9A05707 Software Project ManagementDocumento4 páginas9A05707 Software Project ManagementsivabharathamurthyAinda não há avaliações
- R5410201 Neural Networks & Fuzzy LogicDocumento1 páginaR5410201 Neural Networks & Fuzzy LogicsivabharathamurthyAinda não há avaliações
- R7311506 Operating SystemsDocumento1 páginaR7311506 Operating SystemssivabharathamurthyAinda não há avaliações
- R7312301 Transport Phenomena in BioprocessesDocumento1 páginaR7312301 Transport Phenomena in BioprocessessivabharathamurthyAinda não há avaliações
- 9A14503 Principles of Machine DesignDocumento8 páginas9A14503 Principles of Machine DesignsivabharathamurthyAinda não há avaliações
- 9A13701 Robotics and AutomationDocumento4 páginas9A13701 Robotics and AutomationsivabharathamurthyAinda não há avaliações
- Code: R7311306: (Electronics & Control Engineering)Documento1 páginaCode: R7311306: (Electronics & Control Engineering)sivabharathamurthyAinda não há avaliações
- R5310204 Power ElectronicsDocumento1 páginaR5310204 Power ElectronicssivabharathamurthyAinda não há avaliações
- R7310506 Design & Analysis of AlgorithmsDocumento1 páginaR7310506 Design & Analysis of AlgorithmssivabharathamurthyAinda não há avaliações
- R7311006 Process Control InstrumentationDocumento1 páginaR7311006 Process Control InstrumentationsivabharathamurthyAinda não há avaliações
- R7310106 Engineering GeologyDocumento1 páginaR7310106 Engineering GeologysivabharathamurthyAinda não há avaliações
- R7310206 Linear Systems AnalysisDocumento1 páginaR7310206 Linear Systems AnalysissivabharathamurthyAinda não há avaliações
- R7310306 Heat TransferDocumento1 páginaR7310306 Heat Transfersivabharathamurthy100% (1)
- 9A23501 Heat Transfer in BioprocessesDocumento4 páginas9A23501 Heat Transfer in BioprocessessivabharathamurthyAinda não há avaliações
- 9A21506 Mechanisms & Mechanical DesignDocumento8 páginas9A21506 Mechanisms & Mechanical DesignsivabharathamurthyAinda não há avaliações
- 9A15502 Digital System DesignDocumento4 páginas9A15502 Digital System Designsivabharathamurthy100% (1)
- R7310406 Digital CommunicationsDocumento1 páginaR7310406 Digital CommunicationssivabharathamurthyAinda não há avaliações
- R5310406 Digital CommunicationsDocumento1 páginaR5310406 Digital CommunicationssivabharathamurthyAinda não há avaliações
- 9A05505 Operating SystemsDocumento4 páginas9A05505 Operating SystemssivabharathamurthyAinda não há avaliações
- 9A10505 Principles of CommunicationsDocumento4 páginas9A10505 Principles of CommunicationssivabharathamurthyAinda não há avaliações
- 9A02505 Electrical Machines-IIIDocumento4 páginas9A02505 Electrical Machines-IIIsivabharathamurthyAinda não há avaliações
- 9A04504 Digital IC ApplicationsDocumento4 páginas9A04504 Digital IC ApplicationssivabharathamurthyAinda não há avaliações
- 9A03505 Heat TransferDocumento4 páginas9A03505 Heat TransfersivabharathamurthyAinda não há avaliações
- Income Tax and VATDocumento498 páginasIncome Tax and VATshankar k.c.100% (2)
- Caradol sc48 08Documento2 páginasCaradol sc48 08GİZEM DEMİRAinda não há avaliações
- Raksha Mantralaya Ministry of DefenceDocumento16 páginasRaksha Mantralaya Ministry of Defencesubhasmita sahuAinda não há avaliações
- Jpedal ManualDocumento20 páginasJpedal ManualDamián DávilaAinda não há avaliações
- Academic Socialization and Its Effects On Academic SuccessDocumento2 páginasAcademic Socialization and Its Effects On Academic SuccessJustin LargoAinda não há avaliações
- Engineering DrawingDocumento1 páginaEngineering DrawingDreamtech PressAinda não há avaliações
- Planetary Gear DesignDocumento3 páginasPlanetary Gear DesignGururaja TantryAinda não há avaliações
- Electrical Engineering Lab Vica AnDocumento6 páginasElectrical Engineering Lab Vica Anabdulnaveed50% (2)
- Functional Programming in Swift by Eidhof Chris, Kugler Florian, Swierstra Wouter.Documento212 páginasFunctional Programming in Swift by Eidhof Chris, Kugler Florian, Swierstra Wouter.angloesamAinda não há avaliações
- Unbound DNS Server Tutorial at CalomelDocumento25 páginasUnbound DNS Server Tutorial at CalomelPradyumna Singh RathoreAinda não há avaliações
- Enzymes IntroDocumento33 páginasEnzymes IntropragyasimsAinda não há avaliações
- Prognostic Factors and Management of Patients With Choanal AtresiaDocumento7 páginasPrognostic Factors and Management of Patients With Choanal Atresiafarah maulida martaAinda não há avaliações
- Inventions Over The Last 100 YearsDocumento3 páginasInventions Over The Last 100 YearsHombreMorado GamerYTAinda não há avaliações
- SOCIAL MEDIA DEBATE ScriptDocumento3 páginasSOCIAL MEDIA DEBATE Scriptchristine baraAinda não há avaliações
- KMKT Pra PSPM ANS SCHEMEDocumento16 páginasKMKT Pra PSPM ANS SCHEMEElda AldaAinda não há avaliações
- Riqas Ri RQ9142 11aDocumento6 páginasRiqas Ri RQ9142 11aGrescia Ramos VegaAinda não há avaliações
- Galman V PamaranDocumento7 páginasGalman V PamaranChow Momville EstimoAinda não há avaliações
- Reflection in Sexually Transmitted DiseaseDocumento1 páginaReflection in Sexually Transmitted Diseasewenna janeAinda não há avaliações
- Vygotsky EssayDocumento3 páginasVygotsky Essayapi-526165635Ainda não há avaliações
- Paul Spicker - The Welfare State A General TheoryDocumento162 páginasPaul Spicker - The Welfare State A General TheoryTista ArumAinda não há avaliações
- 4B - Urp - Shavya's FarmDocumento22 páginas4B - Urp - Shavya's FarmSnehansh KishoreAinda não há avaliações