Escolar Documentos
Profissional Documentos
Cultura Documentos
Acl and Ace, Dacl, Sacl
Enviado por
aditimbaDescrição original:
Título original
Direitos autorais
Formatos disponíveis
Compartilhar este documento
Compartilhar ou incorporar documento
Você considera este documento útil?
Este conteúdo é inapropriado?
Denunciar este documentoDireitos autorais:
Formatos disponíveis
Acl and Ace, Dacl, Sacl
Enviado por
aditimbaDireitos autorais:
Formatos disponíveis
Whats the difference between ACL, ACE, DACL and SACL?
A security descriptor contains two access control lists (ACLs) used to assign and track security information for each object: the discretionary access control list (DACL) and the system access control list (SACL). Discretionary access control lists (DACLs). DACLs identify the users and groups that are assigned or denied access permissions on an object. If a DACL does not explicitly identify a user, or any groups that a user is a member of, the user will be denied access to that object. By default, a DACL is controlled by the owner of an object or the person who created the object, and it contains access control entries (ACEs) that determine user access to the object. System access control lists (SACLs). SACLs identify the users and groups that you want to audit when they successfully access or fail to access an object. Auditing is used to monitor events related to system or network security, to identify security breaches, and to determine the extent and location of any damage. By default, a SACL is controlled by the owner of an object or the person who created the object. A SACL contains access control entries (ACEs) that determine whether to record a successful or failed attempt by a user to access a object using a given permission, for example, Full Control and Read.
Definition - What does Access Control List (Microsoft) (ACL) mean?
In a Microsoft context, the Access Control List (ACL) is the list of a system object's security information that defines access rights for resources like users, groups, processes or devices. The system object may be a file, folder or other network resource. The object's security information is known as a permission, which controls resource access to view or modify system object contents. The Windows OS uses Filesystem ACL, in which the user/group permissions associated with an object are internally maintained in a data structure. This type of security model is also used in Open Virtual Memory System (OpenVMS) and Unix-like or Mac OS X operating systems. The ACL contains a list of items, known as Access Control Entities (ACE), which holds the security details of each trustee with system access. A trustee may be an individual user, group of users or process that executes a session. Security details are internally stored in a data structure, which is a 32-bit value that represents the permission set used to operate a securable object. The object security details include generic rights (read, write and execute), object-specific rights (delete and synchronization, etc.), System ACL (SACL) access rights and Directory Services access rights (specific to directory service objects). When a process requests an object's access rights from ACL, ACL retrieves this information from the ACE in the form of an access mask, which maps to that object's stored 32-bit value.
Você também pode gostar
- Access Control Lists - Win32 Apps - Microsoft LearnDocumento1 páginaAccess Control Lists - Win32 Apps - Microsoft LearnRus de JesusAinda não há avaliações
- 12Documento43 páginas12vatsb22Ainda não há avaliações
- Operating System Access Directory FileDocumento1 páginaOperating System Access Directory FileArslan SaleemAinda não há avaliações
- Chapter 5 Security Mechanisms and Techniques Compatibility ModeDocumento92 páginasChapter 5 Security Mechanisms and Techniques Compatibility Modeyordanos yohannesAinda não há avaliações
- Access ControlDocumento11 páginasAccess ControlSyed LuqmanAinda não há avaliações
- ch04 ModifiedDocumento28 páginasch04 ModifiedFood FeedAinda não há avaliações
- LAB4Documento22 páginasLAB4Norah KhalilAinda não há avaliações
- Common Permissions in Microsoft Windows Server 2008 and Windows VistaDocumento5 páginasCommon Permissions in Microsoft Windows Server 2008 and Windows VistaSri NaniAinda não há avaliações
- Authorisation: by M.O. OdeoDocumento33 páginasAuthorisation: by M.O. OdeoSAinda não há avaliações
- Access Control List: Filesystem AclsDocumento2 páginasAccess Control List: Filesystem AclsMingyar AcostaAinda não há avaliações
- 2 4RQDocumento1 página2 4RQVaidehi IyerAinda não há avaliações
- Acl LINUXDocumento13 páginasAcl LINUXMădălina StănășelAinda não há avaliações
- Part 1 - Access Controls-: Muhammad Rudyanto Arief, MTDocumento28 páginasPart 1 - Access Controls-: Muhammad Rudyanto Arief, MTSamuel SinambelaAinda não há avaliações
- CS687 - Access Control 1 Spring 2013Documento36 páginasCS687 - Access Control 1 Spring 2013Demsewa AyeleAinda não há avaliações
- Computer Security: Principles and PracticeDocumento21 páginasComputer Security: Principles and Practicekrishnakumar velapanAinda não há avaliações
- Access Control ModesDocumento2 páginasAccess Control ModesJetarita Njeri GathituAinda não há avaliações
- Authentication and Access Control Methods in 40 CharactersDocumento21 páginasAuthentication and Access Control Methods in 40 CharactersArif AbdulelamAinda não há avaliações
- Access ControlDocumento51 páginasAccess ControlIbrahimAinda não há avaliações
- Chapter 4 and 5Documento33 páginasChapter 4 and 5faiza abdellaAinda não há avaliações
- 2.1 Access Control ModelsDocumento4 páginas2.1 Access Control ModelsolaAinda não há avaliações
- Chapter No 4 (RS)Documento29 páginasChapter No 4 (RS)PriyanshuAinda não há avaliações
- Access Control Lecture on DAC, MAC and StructuresDocumento23 páginasAccess Control Lecture on DAC, MAC and StructuresSampath DarshanaAinda não há avaliações
- M.ALI ARIF Lab Report 12Documento11 páginasM.ALI ARIF Lab Report 12MUHAMMAD Ali ArifAinda não há avaliações
- L04 Authentication and Access ControlDocumento20 páginasL04 Authentication and Access ControlGetnet BelewAinda não há avaliações
- 7-Access Control List-23!08!2021 (23-Aug-2021) Material I 23-Aug-2021 07 Access Control ListDocumento19 páginas7-Access Control List-23!08!2021 (23-Aug-2021) Material I 23-Aug-2021 07 Access Control ListPIYUSH RAJ GUPTAAinda não há avaliações
- 7-Access Control List-23!08!2021 (23-Aug-2021) Material I 23-Aug-2021 07 Access Control ListDocumento19 páginas7-Access Control List-23!08!2021 (23-Aug-2021) Material I 23-Aug-2021 07 Access Control ListPIYUSH RAJ GUPTAAinda não há avaliações
- CH 15-Securing Windows ObjectsDocumento27 páginasCH 15-Securing Windows ObjectsHenraAinda não há avaliações
- CS687 - Access Control 1 - Spring 2020Documento41 páginasCS687 - Access Control 1 - Spring 2020Dawit GetchoAinda não há avaliações
- Security ArchitectureDocumento20 páginasSecurity ArchitectureluisbragagnoloAinda não há avaliações
- Access Control List Full Notes PDFDocumento6 páginasAccess Control List Full Notes PDFsamweli.mwakatobeAinda não há avaliações
- Protection Mechanism (Protection domain+ACL)Documento2 páginasProtection Mechanism (Protection domain+ACL)gobinathAinda não há avaliações
- Access Control Method PDFDocumento31 páginasAccess Control Method PDFPradeep SinghAinda não há avaliações
- Chapter 11 - Access Control FundamentalsDocumento60 páginasChapter 11 - Access Control FundamentalsmaryaAinda não há avaliações
- Network ACLsDocumento99 páginasNetwork ACLsjanerie71Ainda não há avaliações
- Week10-11-Access Control Models-PoliciesDocumento33 páginasWeek10-11-Access Control Models-Policiesmahtab mahtabAinda não há avaliações
- Exchange Server 2010 Introduction To Supporting AdministrationDocumento105 páginasExchange Server 2010 Introduction To Supporting AdministrationRazdolbaitusAinda não há avaliações
- Access Control Policies: Privacy Challenges and Goals in Mhealth SystemsDocumento11 páginasAccess Control Policies: Privacy Challenges and Goals in Mhealth SystemsClueless LimAinda não há avaliações
- CS 126 Lecture 07 PDFDocumento57 páginasCS 126 Lecture 07 PDFjohnAinda não há avaliações
- Emc Isilon Multiprotocol Data Access With A Unified Security Model For SMB and NfsDocumento30 páginasEmc Isilon Multiprotocol Data Access With A Unified Security Model For SMB and NfslharipaulAinda não há avaliações
- DBSADocumento7 páginasDBSAmuazzamumar65Ainda não há avaliações
- Operating Systems GlossaryDocumento4 páginasOperating Systems GlossaryJosé Ignacio Del Angel Del AngelAinda não há avaliações
- UNIT-3:-Secure Architecture Principles Isolation and LeasDocumento17 páginasUNIT-3:-Secure Architecture Principles Isolation and LeasAryan DixitAinda não há avaliações
- Access Control Fundamentals: 2.1 Protection SystemDocumento14 páginasAccess Control Fundamentals: 2.1 Protection SystemMuhammad Tehseen KhanAinda não há avaliações
- Principles of Information Security-Ch8Documento41 páginasPrinciples of Information Security-Ch8yassine iborkAinda não há avaliações
- Semantic Data ControlDocumento15 páginasSemantic Data ControlArghya ChowdhuryAinda não há avaliações
- Unit 6 Assignment 2Documento2 páginasUnit 6 Assignment 2DKnott86Ainda não há avaliações
- Ias 102 4Documento24 páginasIas 102 4Efren CordonigaAinda não há avaliações
- The Protection of Information in Computer SystemsDocumento3 páginasThe Protection of Information in Computer SystemsemmanuelAinda não há avaliações
- Cram DM1Documento8 páginasCram DM1Del NoitAinda não há avaliações
- ACL access control list guideDocumento28 páginasACL access control list guidezeeshan_knowledgeAinda não há avaliações
- Security Terms and Concepts ExplainedDocumento34 páginasSecurity Terms and Concepts Explainedwdfarmer34Ainda não há avaliações
- 84-01-20.1 Implementing AS/400 Security Controls: PayoffDocumento21 páginas84-01-20.1 Implementing AS/400 Security Controls: PayoffNeil CornelioAinda não há avaliações
- Machine learning identifies anomalies in access control lists under 40 charsDocumento7 páginasMachine learning identifies anomalies in access control lists under 40 charsfarrukhAinda não há avaliações
- CH 04Documento41 páginasCH 04Darwin VargasAinda não há avaliações
- Overview Paper Spring2009Documento14 páginasOverview Paper Spring2009Michael CorselloAinda não há avaliações
- Bio Metrics Sreevidhya@StudentsDocumento30 páginasBio Metrics Sreevidhya@Studentsakilaa_krishAinda não há avaliações
- Operating System Unit 7,6,5Documento40 páginasOperating System Unit 7,6,5dhokebazz00Ainda não há avaliações
- A SurveyDocumento5 páginasA SurveyVibhu YadavAinda não há avaliações
- Oracle Quick Guides: Part 4 - Oracle Administration: Security and PrivilegeNo EverandOracle Quick Guides: Part 4 - Oracle Administration: Security and PrivilegeAinda não há avaliações
- 2010Documento1 página2010bs1237159Ainda não há avaliações
- Submitted For The Partial Fulfillment of Award of MBA DegreeDocumento10 páginasSubmitted For The Partial Fulfillment of Award of MBA DegreeaditimbaAinda não há avaliações
- Practice SQL QueriesDocumento10 páginasPractice SQL QueriesSivakumar BalakrishnanAinda não há avaliações
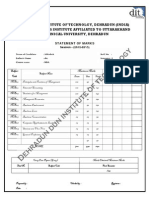
- Statement of Marks: Dehradun Institute of Technology, Dehradun (India)Documento1 páginaStatement of Marks: Dehradun Institute of Technology, Dehradun (India)aditimbaAinda não há avaliações
- MBA Summer Project Report Submission NoticeDocumento2 páginasMBA Summer Project Report Submission NoticeaditimbaAinda não há avaliações
- FMCG Companies Hidden Treasure Rural IndiaDocumento86 páginasFMCG Companies Hidden Treasure Rural IndiaaditimbaAinda não há avaliações
- Submitted For The Partial Fulfillment of Award of MBA DegreeDocumento10 páginasSubmitted For The Partial Fulfillment of Award of MBA DegreeaditimbaAinda não há avaliações
- Dehradun Institute of Technolgy, Dehradun (India) An Autonomous Institute Affiliated To Uttarakhand Technical University, DehradunDocumento1 páginaDehradun Institute of Technolgy, Dehradun (India) An Autonomous Institute Affiliated To Uttarakhand Technical University, DehradunaditimbaAinda não há avaliações
- Astrology MathematicsDocumento34 páginasAstrology MathematicsDrFaisal ShawqeeAinda não há avaliações
- Applying HACCP PrinciplesDocumento88 páginasApplying HACCP Principlesbbeard90% (1)
- 11-1203 Syed Hussain HaiderDocumento16 páginas11-1203 Syed Hussain HaiderSalman Nisar BhattiAinda não há avaliações
- Final QuestionDocumento5 páginasFinal QuestionrahulAinda não há avaliações
- Commodi Cation of Women's Bodies andDocumento9 páginasCommodi Cation of Women's Bodies andunesa fikAinda não há avaliações
- Itp 8Documento5 páginasItp 8Arung IdAinda não há avaliações
- TelecomHall - Mapinfo For Telecom - Part 1Documento6 páginasTelecomHall - Mapinfo For Telecom - Part 1Drio RioAinda não há avaliações
- NAHRIM - Institut Penyelidikan Hidraulik Kebangsaan Malaysia - Rainwater Harvesting SystemDocumento4 páginasNAHRIM - Institut Penyelidikan Hidraulik Kebangsaan Malaysia - Rainwater Harvesting SystemAnonymous e1j2F5Ge0Ainda não há avaliações
- Wilkes PDFDocumento2 páginasWilkes PDFReyes Lopez EstebanAinda não há avaliações
- Data Mining Course Learn Analytics RDocumento5 páginasData Mining Course Learn Analytics RAntonio AlvarezAinda não há avaliações
- CFO To Chief Future OfficerDocumento24 páginasCFO To Chief Future OfficerSuccessful ChicAinda não há avaliações
- A+ Guide to Managing Your PC Hardware & SoftwareDocumento34 páginasA+ Guide to Managing Your PC Hardware & Software2AdvanceAinda não há avaliações
- Đề 1Documento9 páginasĐề 1trung anAinda não há avaliações
- Indonesian Pangasius BrochureDocumento6 páginasIndonesian Pangasius BrochurerobiyullahAinda não há avaliações
- ACS SCPI Programming Guide V1 0Documento29 páginasACS SCPI Programming Guide V1 0Pedro Boanerges Paz RomeroAinda não há avaliações
- Gdot Autoturn User Guide Ds FdsDocumento66 páginasGdot Autoturn User Guide Ds FdsMd Didarul AlamAinda não há avaliações
- The Revised VGB-S-506pg9Documento1 páginaThe Revised VGB-S-506pg9retrogrades retrogradesAinda não há avaliações
- Stuart Wilde: Csodák Pedig VannakDocumento31 páginasStuart Wilde: Csodák Pedig VannakRita AsztalosAinda não há avaliações
- Project Proposal VTP 4Documento35 páginasProject Proposal VTP 4api-245643527Ainda não há avaliações
- Syl LB Hms 240809Documento102 páginasSyl LB Hms 240809sharma_anand73Ainda não há avaliações
- Suppliers of Ese Lightning Conductor Kalre Lightning ArresterDocumento2 páginasSuppliers of Ese Lightning Conductor Kalre Lightning ArresterRemedies EarthingAinda não há avaliações
- Food Chemistry: Analytical MethodsDocumento7 páginasFood Chemistry: Analytical Methodswildan ariefAinda não há avaliações
- Seance 1 Introduction To DystopiaDocumento32 páginasSeance 1 Introduction To DystopiaHanane AmadouAinda não há avaliações
- Justine's Memoirs On Actual Freedom (Part - I)Documento61 páginasJustine's Memoirs On Actual Freedom (Part - I)JustineAinda não há avaliações
- Nueva Vida Outreach Specialist Job DescriptionDocumento2 páginasNueva Vida Outreach Specialist Job DescriptionOffice on Latino Affairs (OLA)Ainda não há avaliações
- 3rd BeatitudeDocumento18 páginas3rd BeatitudeDonna AAinda não há avaliações
- Resume SasDocumento3 páginasResume Saslubasoft0% (1)
- BCGDocumento36 páginasBCGdadaisgreat100% (1)
- Trends in Linguistics - Studies and MonographsDocumento550 páginasTrends in Linguistics - Studies and MonographsNelly PaniaguaAinda não há avaliações