Escolar Documentos
Profissional Documentos
Cultura Documentos
Hardening Your VPN Setup With Iptables
Enviado por
cosasdeangelDescrição original:
Direitos autorais
Formatos disponíveis
Compartilhar este documento
Compartilhar ou incorporar documento
Você considera este documento útil?
Este conteúdo é inapropriado?
Denunciar este documentoDireitos autorais:
Formatos disponíveis
Hardening Your VPN Setup With Iptables
Enviado por
cosasdeangelDireitos autorais:
Formatos disponíveis
Hardening your VPN Setup with iptables - InputOutput.
io
http://www.inputoutput.io/hardening-your-vpn-setup-with...
InputOutput.io
The free-thinkin free-speakin rabble-rousin geek.
Home Contact
Pages
Contact
Archives
January 2013 July 2012 June 2012 July 2011 January 2011 July 2010 January 2010 November 2009 April 2009 March 2009 February 2009 November 2008 July 2008 June 2008 May 2008 Jul 14 2011
Hardening your VPN Setup with iptables
Category: Hacks, How-Tos | Tags :iptables, openvpn, routes, security, SSL, vpn | No Comments Ill be heading out to Defcon 19 next month, so I want my VPN connection to be stable and secure. You probably know the situation. Youre at your local coee shop, using their (hopefully
1 de 4
06/05/13 01:36
Hardening your VPN Setup with iptables - InputOutput.io
http://www.inputoutput.io/hardening-your-vpn-setup-with...
not) wide-open unsecured wi hotspot. But youre smart enough not to send all your data out over the clear, since there might be malicious script kiddies ready to take your sensitive data and sell it to kids on the street. So you use a VPN. You re up OpenVPN and connect to your VPN service. Then you start browsing, comforted by the fact that your trac is encapsulated in a secure SSL tunnel. Better yet, the user experience is transparent: you dont have to congure your applications to manually use a SOCKS5 proxy. OpenVPN handles your routing tables and creates a virtual interface using the tun module. Its so simple, you dont need to think about it. But theres a problem with this setup. No one can reach into your stream and extract or insert data, but theres a caveat. Anyone can destroy your TCP stream by sending you a spoofed RST packet from the remote server, or otherwise making the service unavailable to you. Destroying the TCP stream destroys the virtual (tun) interface, which, in turn, destroys the routes associated with that interface. Now youre using your physical interface unprotected from those pesky hackers. Worse still, you dont realize it. Not a thing has changed from the perspective of user experience. Since everything is transparent, you dont notice any change at all. Now youre screwed. Little did you know that this all could have been avoided by our friend iptables. Sure, you could modify your routes further to ensure that only trac going to the remote server goes over your physical interface, but thats too easy. Plus, routing tables arent intended for security, theyre inteded to move packets along. iptables seems like the tool for the task, so I modied a script I found here to make sure that we disallow any trac that we dont want:
#!/bin/bash if [[ $EUID -ne 0 ]]; then echo "This script must be run as root" 1>&2 exit 1 fi # name of primary network interface (before tunnel) PRIMARY=wlan0 # address of tunnel server SERVER=seattle.vpn.riseup.net # address of vpn server VPN_SERVER=seattle.vpn.riseup.net # gateway ip address (before tunnel - adsl router ip address) # automatically determine the ip from the default route GATEWAY=`route -n | grep $PRIMARY | egrep "^0\.0\.0\.0" | tr -s " " | cut -d" " -f2` # provided by pppd: interface name TUNNEL=tun0 openvpn --config /my/path/to/riseup.ovpn --auth-user-pass /my/path/to/authentication.conf & # iptables rules - important! #LOCAL_NET=192.168.0.0/16 LOCAL_NET=$GATEWAY # Flush all previous filter rules, you might not want to include this line if you already have other r iptables -t filter --flush
2 de 4
06/05/13 01:36
Hardening your VPN Setup with iptables - InputOutput.io
http://www.inputoutput.io/hardening-your-vpn-setup-with...
iptables -t filter -X MYVPN iptables -t filter -N MYVPN # Exceptions for local traffic & vpn server iptables -t filter -A MYVPN -o lo -j RETURN iptables -t filter -A MYVPN -o ${TUNNEL} -j RETURN iptables -t filter -A MYVPN --dst 127.0.0.1 -j RETURN iptables -t filter -A MYVPN --dst $LOCAL_NET -j RETURN iptables -t filter -A MYVPN --dst ${SERVER} -j RETURN iptables -t filter -A MYVPN --dst ${VPN_SERVER} -j RETURN # Add extra local nets here as necessary iptables -t filter -A MYVPN -j DROP # MYVPN traffic leaving this iptables -t filter -A OUTPUT iptables -t filter -A OUTPUT iptables -t filter -A OUTPUT host: -p tcp --syn -j MYVPN -p icmp -j MYVPN -p udp -j MYVPN
echo "nameserver 8.8.8.8" > /etc/resolv.conf
Youll want to modify the openvpn command, interfaces, and servers to meet your needs. And thats it! If your stream is taken down, you have these rules to protect you. I have this script as a post-connect hook for any untrusted networks I connect to (wicd is a nice network manager for adding hooks). Later, if you want your trac to go over the clear again, you can use this script:
#!/bin/bash if [[ $EUID -ne 0 ]]; then echo "This script must be run as root" 1>&2 exit 1 fi iptables -t filter --flush iptables -t filter -X MYVPN
Respond to this post
Name (required)
Mail (will not be published) (required)
Website
3 de 4
06/05/13 01:36
Hardening your VPN Setup with iptables - InputOutput.io
http://www.inputoutput.io/hardening-your-vpn-setup-with...
Submit Comment
2013 InputOutput.io | Theme wpBurn Blue by wpburn.com
4 de 4
06/05/13 01:36
Você também pode gostar
- PDFDocumento30 páginasPDFcosasdeangelAinda não há avaliações
- DRC Guide v1.0Documento17 páginasDRC Guide v1.0anandalaharAinda não há avaliações
- The Guide To VoyageMPD BruteFIR and JACK v1.6Documento20 páginasThe Guide To VoyageMPD BruteFIR and JACK v1.6cosasdeangelAinda não há avaliações
- R LinuxDocumento66 páginasR LinuxAlfonso MartinezAinda não há avaliações
- Use of Kinesio Tape in Pediatrics To Improve Oral Motor ControlDocumento2 páginasUse of Kinesio Tape in Pediatrics To Improve Oral Motor ControlcosasdeangelAinda não há avaliações
- Cold Egypt Sciene Fixionb Abd 88765443678Documento16 páginasCold Egypt Sciene Fixionb Abd 88765443678Iliana AndriaAinda não há avaliações
- Instructions: Therapeutic Taping Home Program ForDocumento2 páginasInstructions: Therapeutic Taping Home Program ForcosasdeangelAinda não há avaliações
- DRC Guide v1.0Documento17 páginasDRC Guide v1.0anandalaharAinda não há avaliações
- Frankenstein SlidesDocumento12 páginasFrankenstein SlidespiokarolAinda não há avaliações
- Sneak Past Pay-For WiFi With DNS TunnelingDocumento5 páginasSneak Past Pay-For WiFi With DNS TunnelingmardefondoAinda não há avaliações
- Master Kinesiotaping HandoutDocumento11 páginasMaster Kinesiotaping HandoutcosasdeangelAinda não há avaliações
- R LinuxDocumento66 páginasR LinuxAlfonso MartinezAinda não há avaliações
- OpenPuff Help enDocumento32 páginasOpenPuff Help enbooklandAinda não há avaliações
- DroolingDocumento5 páginasDroolingcosasdeangelAinda não há avaliações
- HD681Documento2 páginasHD681cosasdeangelAinda não há avaliações
- Hacking The Samsung CLP-315Documento32 páginasHacking The Samsung CLP-315cosasdeangel100% (3)
- Userg RevG eDocumento39 páginasUserg RevG ecosasdeangelAinda não há avaliações
- Unix Command TableDocumento58 páginasUnix Command Tablejeco30001104Ainda não há avaliações
- R LinuxDocumento66 páginasR LinuxAlfonso MartinezAinda não há avaliações
- Algorithms: 2006 S. Dasgupta, C. H. Papadimitriou, and U. V. Vazirani July 18, 2006Documento8 páginasAlgorithms: 2006 S. Dasgupta, C. H. Papadimitriou, and U. V. Vazirani July 18, 2006A.K. MarsAinda não há avaliações
- Algorithms: 2006 S. Dasgupta, C. H. Papadimitriou, and U. V. Vazirani July 18, 2006Documento8 páginasAlgorithms: 2006 S. Dasgupta, C. H. Papadimitriou, and U. V. Vazirani July 18, 2006A.K. MarsAinda não há avaliações
- Macaw: A Media Access Protocol For Wireless LAN'sDocumento14 páginasMacaw: A Media Access Protocol For Wireless LAN'sdspsolutionsAinda não há avaliações
- Openvpn - Secure IP Tunnel DaemonDocumento29 páginasOpenvpn - Secure IP Tunnel DaemoncosasdeangelAinda não há avaliações
- Hyperloop Alpha PDFDocumento58 páginasHyperloop Alpha PDFmleslieAinda não há avaliações
- How To Set Up A TOR Middlebox Routing All VirtualBox Virtual Machine Traffic Over The TOR NetworkDocumento9 páginasHow To Set Up A TOR Middlebox Routing All VirtualBox Virtual Machine Traffic Over The TOR NetworkcosasdeangelAinda não há avaliações
- MK BachelorDocumento60 páginasMK BachelorcosasdeangelAinda não há avaliações
- How To Set Up A TOR Middlebox Routing All VirtualBox Virtual Machine Traffic Over The TOR NetworkDocumento9 páginasHow To Set Up A TOR Middlebox Routing All VirtualBox Virtual Machine Traffic Over The TOR NetworkcosasdeangelAinda não há avaliações
- Paracion CifradosDocumento9 páginasParacion CifradoscosasdeangelAinda não há avaliações
- Install Firefox 21 in Debian WheezyDocumento2 páginasInstall Firefox 21 in Debian WheezycosasdeangelAinda não há avaliações
- Anonymous SSH Sessions With TORDocumento9 páginasAnonymous SSH Sessions With TORcosasdeangelAinda não há avaliações
- Never Split the Difference: Negotiating As If Your Life Depended On ItNo EverandNever Split the Difference: Negotiating As If Your Life Depended On ItNota: 4.5 de 5 estrelas4.5/5 (838)
- Elon Musk: Tesla, SpaceX, and the Quest for a Fantastic FutureNo EverandElon Musk: Tesla, SpaceX, and the Quest for a Fantastic FutureNota: 4.5 de 5 estrelas4.5/5 (474)
- The Subtle Art of Not Giving a F*ck: A Counterintuitive Approach to Living a Good LifeNo EverandThe Subtle Art of Not Giving a F*ck: A Counterintuitive Approach to Living a Good LifeNota: 4 de 5 estrelas4/5 (5782)
- Hidden Figures: The American Dream and the Untold Story of the Black Women Mathematicians Who Helped Win the Space RaceNo EverandHidden Figures: The American Dream and the Untold Story of the Black Women Mathematicians Who Helped Win the Space RaceNota: 4 de 5 estrelas4/5 (890)
- The Yellow House: A Memoir (2019 National Book Award Winner)No EverandThe Yellow House: A Memoir (2019 National Book Award Winner)Nota: 4 de 5 estrelas4/5 (98)
- The Little Book of Hygge: Danish Secrets to Happy LivingNo EverandThe Little Book of Hygge: Danish Secrets to Happy LivingNota: 3.5 de 5 estrelas3.5/5 (399)
- A Heartbreaking Work Of Staggering Genius: A Memoir Based on a True StoryNo EverandA Heartbreaking Work Of Staggering Genius: A Memoir Based on a True StoryNota: 3.5 de 5 estrelas3.5/5 (231)
- Team of Rivals: The Political Genius of Abraham LincolnNo EverandTeam of Rivals: The Political Genius of Abraham LincolnNota: 4.5 de 5 estrelas4.5/5 (234)
- Devil in the Grove: Thurgood Marshall, the Groveland Boys, and the Dawn of a New AmericaNo EverandDevil in the Grove: Thurgood Marshall, the Groveland Boys, and the Dawn of a New AmericaNota: 4.5 de 5 estrelas4.5/5 (265)
- The Hard Thing About Hard Things: Building a Business When There Are No Easy AnswersNo EverandThe Hard Thing About Hard Things: Building a Business When There Are No Easy AnswersNota: 4.5 de 5 estrelas4.5/5 (344)
- The Emperor of All Maladies: A Biography of CancerNo EverandThe Emperor of All Maladies: A Biography of CancerNota: 4.5 de 5 estrelas4.5/5 (271)
- The World Is Flat 3.0: A Brief History of the Twenty-first CenturyNo EverandThe World Is Flat 3.0: A Brief History of the Twenty-first CenturyNota: 3.5 de 5 estrelas3.5/5 (2219)
- The Unwinding: An Inner History of the New AmericaNo EverandThe Unwinding: An Inner History of the New AmericaNota: 4 de 5 estrelas4/5 (45)
- The Gifts of Imperfection: Let Go of Who You Think You're Supposed to Be and Embrace Who You AreNo EverandThe Gifts of Imperfection: Let Go of Who You Think You're Supposed to Be and Embrace Who You AreNota: 4 de 5 estrelas4/5 (1090)
- The Sympathizer: A Novel (Pulitzer Prize for Fiction)No EverandThe Sympathizer: A Novel (Pulitzer Prize for Fiction)Nota: 4.5 de 5 estrelas4.5/5 (119)
- Mental Health Admission & Discharge Dip NursingDocumento7 páginasMental Health Admission & Discharge Dip NursingMuranatu CynthiaAinda não há avaliações
- Israel Bible MapDocumento1 páginaIsrael Bible MapMoses_JakkalaAinda não há avaliações
- Who Are The Prosperity Gospel Adherents by Bradley A KochDocumento46 páginasWho Are The Prosperity Gospel Adherents by Bradley A KochSimon DevramAinda não há avaliações
- Successfull Weight Loss: Beginner'S Guide ToDocumento12 páginasSuccessfull Weight Loss: Beginner'S Guide ToDenise V. FongAinda não há avaliações
- Cognitive Development of High School LearnersDocumento30 páginasCognitive Development of High School LearnersJelo BacaniAinda não há avaliações
- Lab Report FormatDocumento2 páginasLab Report Formatapi-276658659Ainda não há avaliações
- WEEK 4 A. Family Background of Rizal and Its Influence On The Development of His NationalismDocumento6 páginasWEEK 4 A. Family Background of Rizal and Its Influence On The Development of His NationalismVencint LaranAinda não há avaliações
- AOM NO. 01-Stale ChecksDocumento3 páginasAOM NO. 01-Stale ChecksRagnar Lothbrok100% (2)
- Unit 6 Lesson 3 Congruent Vs SimilarDocumento7 páginasUnit 6 Lesson 3 Congruent Vs Similar012 Ni Putu Devi AgustinaAinda não há avaliações
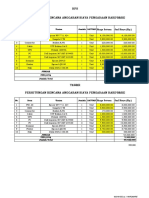
- HPS Perhitungan Rencana Anggaran Biaya Pengadaan Hardware: No. Item Uraian Jumlah SATUANDocumento2 páginasHPS Perhitungan Rencana Anggaran Biaya Pengadaan Hardware: No. Item Uraian Jumlah SATUANYanto AstriAinda não há avaliações
- Review 6em 2022Documento16 páginasReview 6em 2022ChaoukiAinda não há avaliações
- Best Safety Practices in The Philippine Construction PDFDocumento16 páginasBest Safety Practices in The Philippine Construction PDFDione Klarisse GuevaraAinda não há avaliações
- Torts and DamagesDocumento63 páginasTorts and DamagesStevensonYuAinda não há avaliações
- dlp4 Math7q3Documento3 páginasdlp4 Math7q3Therence UbasAinda não há avaliações
- Climbing KnotsDocumento40 páginasClimbing KnotsIvan Vitez100% (11)
- Jason Payne-James, Ian Wall, Peter Dean-Medicolegal Essentials in Healthcare (2004)Documento284 páginasJason Payne-James, Ian Wall, Peter Dean-Medicolegal Essentials in Healthcare (2004)Abdalmonem Albaz100% (1)
- Line GraphDocumento13 páginasLine GraphMikelAgberoAinda não há avaliações
- Runner Cs-47 Link Rev-2 27-09-10Documento29 páginasRunner Cs-47 Link Rev-2 27-09-10bocko74Ainda não há avaliações
- Erp Software Internship Report of Union GroupDocumento66 páginasErp Software Internship Report of Union GroupMOHAMMAD MOHSINAinda não há avaliações
- Ruby Tuesday LawsuitDocumento17 páginasRuby Tuesday LawsuitChloé MorrisonAinda não há avaliações
- Supplier of PesticidesDocumento2 páginasSupplier of PesticidestusharAinda não há avaliações
- Dhikr or Zikr or Remembrance of AllahDocumento27 páginasDhikr or Zikr or Remembrance of AllahMd. Naim KhanAinda não há avaliações
- 14 Worst Breakfast FoodsDocumento31 páginas14 Worst Breakfast Foodscora4eva5699100% (1)
- Indian Wall Paintings - Analysis of Materials and TechniquesDocumento7 páginasIndian Wall Paintings - Analysis of Materials and Techniquesshu_sAinda não há avaliações
- Tattva Sandoha PujaDocumento2 páginasTattva Sandoha PujaSathis KumarAinda não há avaliações
- Industrial and Organizational PsychologyDocumento21 páginasIndustrial and Organizational PsychologyCris Ben Bardoquillo100% (1)
- Global Pre-Qualification - Registration of Vendors For Supply of Various Raw Materials - ProductsDocumento2 páginasGlobal Pre-Qualification - Registration of Vendors For Supply of Various Raw Materials - Productsjavaidkhan83Ainda não há avaliações
- Teacher swap agreement for family reasonsDocumento4 páginasTeacher swap agreement for family reasonsKimber LeeAinda não há avaliações
- Is The Question Too Broad or Too Narrow?Documento3 páginasIs The Question Too Broad or Too Narrow?teo100% (1)
- Cambridge IGCSE: 0500/12 First Language EnglishDocumento16 páginasCambridge IGCSE: 0500/12 First Language EnglishJonathan ChuAinda não há avaliações