Escolar Documentos
Profissional Documentos
Cultura Documentos
MCQ Questions CXC It
Enviado por
Latoya AndersonTítulo original
Direitos autorais
Formatos disponíveis
Compartilhar este documento
Compartilhar ou incorporar documento
Você considera este documento útil?
Este conteúdo é inapropriado?
Denunciar este documentoDireitos autorais:
Formatos disponíveis
MCQ Questions CXC It
Enviado por
Latoya AndersonDireitos autorais:
Formatos disponíveis
INFORMATION TECHNOLOGY 2008 Past Paper I Duration 1 hour 30 minutes
INSTRUCTIONS TO STUDENTS This paper consists of SIXTY multiple choice questions to be completed by students. Answers should be marked on the answer sheet provided. Each item in this test has four suggested answers lettered (A), (B), (C), (D). Read each item carefully then choose the best answer.
Sample Item Which of the following pairs represents general-purpose software tools? Sample Answer (A) Spreadsheet and database software (B) Word processor and accounting software (C)Students record system and database software (D)Insurance processing and spreadsheet software A B C D
The best answer to this item is spreadsheet and database software, so answer space (A) has been shaded.
DO NOT TURN THIS PAGE UNTIL YOU ARE ADVISED TO DO SO
1. When a computer is working on given instructions it is called? a. Output b. Storage c. Processing d. Input 2. Hexadecimal has a base value of? a. 6 b. 8 c. 16 d. 18 3. Which of the following is NOT a function of the control unit? a. Read instructions b. Interpret instruction c. Direct operation d. Execute instructions 4. The unit of storage used to represent a character is? a. Bit b. Byte c. Word d. Kilobyte 5. Which of the following storage media provides sequential access only? a. Floppy disk b. Magnetic disk c. Magnetic tape d. Optical Disk 6. Which of the following storage media used laser technology to store data a. Floppy disk b. Magnetic tape c. CD-ROM d. Hard disk 7. The technology used to read pencil or pen marks on a multiple choice answer sheet is? a. OCR b. OMR c. POS d. MICR 3
8. The MOST suitable device for the output of architectural drawing is a? a. Plotter b. Laser printer c. Graphics tablet d. Lightpen 9. Which of the following output is an example of a hardcopy? a. An oral speech delivered by a speaker b. A bill produced from the printer c. The display on a monitor d. A picture on a wall produced from a multimedia projector 10. a. b. c. d. 11. a. b. c. d. 12. a. b. c. d. 13. a. b. c. d. The decimal equivalent of 000011112 is? 8 12 15 28 The BCD representation of (-15) is? 100000011111 101100101111 000000011111 101100010101 In modern computers, the CPU speed is measured in? Kilohertz gigabytes kilobytes gigahertz Which of the following is not application software? WordProcessor Spreadsheets Windows SmartDraw
14. Which of the following is not a function of the operating system? a. Control input/output operations. b. Provides security c. Perform calculation 4
d. Provide a friendly interface 15. An example of multitasking is? a. Doing a background save while typing a document b. Allowing many users to use the same program c. Allowing one user to use one program d. Operating one program by many users 16. Quality Developers is a company that writes programs to do specific jobs for other companies. These programs are called? a. General-purpose software b. Special-purpose software c. Custom-purpose software d. Off-the-shelf software 17. a. b. c. d. 18. a. b. c. d. Which of the following is not a type of software interface? Command Driven Touch screen Menu-Driven Graphical User Interface(GUI) An airline reservation system is an example of Batch processing Real time processing Interactive processing Distributed processing
19. The name of the interface used by blind persons to perform operation on a computer is a. Sensor b. Icon c. Braille d. Touch screen 20. Which of the following is NOT a type of transmission medium? a. Coaxial b. Twisted pair c. Modem d. Microwave 21. Persons at a downtown caf realized that they were able to access the internet on their laptop computers. The caf could be considered as a? a. Metropolitan area network b. Hotspot c. Local area network 5
d. Satellite 22. Which of the following technologies does NOT facilitate the transferring of data between computers in adjacent buildings a. Fibre optic b. Bluetooth c. Twisted pair d. Microwave
23. A group of persons who share common interests and communicate by posting messages and replies on the internet is called a/an? a. Podcast b. Newsgroup c. Uploader d. Surfer 24. Uploading or downloading data to or from a remote computer is done using? a. File transfer protocol b. Inter relay chat c. Blogging d. Instant messaging 25. Each website on the Internet can be accessed by entering a unique address. This address is referred to as? a. HTTP b. HTML c. FTP d. URL 26. a. b. c. d. Which of the following items cannot be sent via email? Text document Parcels Sound files Graphics images
27. Which of the following pair of items is used to create webpage? a. Homepage and Website b. HTML and authoring tool c. ISP and web browser d. Internet and URL
28. Which one of the following statements BEST describes the term information? a. It is raw facts b. It is meaningful c. It is not the result of processing d. It does not have any value 29. Which of the following actions is NOT considered to be a computer crime? a. Encryption b. Piracy c. Industrial Espionage d. Hacking
30. Which of the following is NOT a physical restriction with respect to data security a. Firewall b. Locking up the hardware c. Fireproof cabinets d. Biometric Systems 31. In word processing, an efficient way to move the 3rd paragraph to place it after the 5th paragraph is? a. Copy and paste b. Copy, cut and paste c. Cut, copy and paste d. Cut and paste 32. a. b. c. d. Presentation software allows the user to Track changes Design tables Enhance public speaking Develop graphs to report on sales data
33. The pair of files used to produce merged letters during a mail merge is? a. Primary document and data source b. Primary document and merged letters c. Data source and merged letters d. Primary document and current letter
34. Text entered into a spreadsheet is aligned towards the left by default. These entries are called a. values b. labels c. formulae d. functions 35. Which of the following formatting features is unique to numbers in spreadsheet? a. Bold b. Custom c. Italics d. Indent 36. a. b. c. d. To center the title rows of a spreadsheet across the column Center align the title rows Center align the title columns Merge and center the title rows Merge and center the title columns
37. a. b. c. d.
Formulae in a spreadsheet involve Cell addresses, values and labels Cell addresses, values and mathematical operators Cell addresses and labels Cell addresses and values
38. Which of the following statements is NOT true of primary keys? a. They do not contain blank value b. They are unique identifiers c. They are always in text form d. They may be composed of one or more attributes 39. The shortcut key that can be used to activate or open the find and replace screen is a. CtrlG b. CtrlH c. AltG d. AltH 40. Footers are found at the ..of a document. a. Bottom of every page b. Top of every page 8
c. End of a page d. end 41. Susan is using the Find and Replace feature of a word processing tool, to search for the word DELL, in a document that she is typing. Which word or words can be found if she has the Match case option disabled? a. dell b. Dell c. DELL d. DeLL e. All of the above 42. The following words could be found in the document that Susan typed sad set star street
Susan performed a Find and Replace action with the Find what entry set to s?t and the Use wildcard option selected. Which string from the list above would be found? a. b. c. d. sad set star street
43.
Software piracy involves a. The authorized copying, use or selling of software that is copyrighted. b. The authorized copying, use or selling of software that is not copyrighted. c. The unauthorized copying, use or selling of software that is copyrighted. d. The unauthorized copying, use or selling of software that is not copyrighted.
44. The purpose of the icon is to a. Move data to the clipboard b. Insert a sum formula on the worksheet c. Access the chart wizard d. Provide on-screen help
45. A field in a table appears as a match of the primary key in another table is called a a. Candidate key b. Secondary key c. Foreign key d. Composite key 46. Given the following algorithm J5 K J J J+K K J+3 Display K The value displayed for K is? a. b. c. d. 10 11 13 14
47. The following variables s, t and u have been assigned the values shown S 5 T 6 U 3 Which of the following statements does NOT evaluate to TRUE? a. b. c. d. U>7 and T <=7 S< T or U < S 2 U 2 >= 1 T <> 4 or s = 5
48. Which of the following algorithms satisfies the requirement of asking the user to input two numbers, calculate the average and displaying the result a. Display Enter two numbers Input a, b C (a+b)/2 Display C b. Input a, b
10
C(a+b)/2 Display c c. Display Enter two numbers Input a,b Ca+b/2 Display C d. Input a, b Ca+b/2 Display C 49. Which of the following algorithms does NOT display four consecutive numbers? a. For v2 to 5 Display v b. h While h<5 Display h hh+1 end while c. for k7 down to 4 step-1 display k d. f 6 while f<3 display f f f-1 50. The variables h and s are assigned the following values, h4 and s3*h. Display h+s*2 will show a. 28 b. 30 c. 32 d. 38
51. Which of the following languages is ONLY understood by computers a. 4GLs b. Machine Languages 11
c. Natural Languages d. Procedural languages 52. Which of the following languages is NOT a high-level language? a. C b. COBOL c. ASSEMBLY d. PASCAL 53. Errors that occur in a program when the rules of the programming languages are NOT obeyed are called a. Syntax errors b. Logical errors c. Execution errors d. Run-time errors 54. a. b. c. d. Which of the following is NOT type of program error Logic error Syntax error Run time error Debug
55. Which of the following term is not a term used to describe the process of manually going through a program looking for errors a. Tracing b. Dry run c. Debugging d. Documentation 56. Which of the following is an example of a conditional construct? a. F-Next b. If-then-else c. While-endwhile d. For-endfor 57. Which of the following reserved words in Pascal displays data and places the cursor on a new line. a. write b. read c. writeln d. readln
12
58. Program implementation involves a number of steps. Which of the following steps is NOT legitimate? a. Executing b. Bonding c. Compiling d. Linking 59. Which of the following identifiers is NOT a valid variable name? a. Input b. totalCost c. 9Count d. NumCount 60. The term used to describe a memory location whose value changes during program execution a. Constant b. Volatile c. Variable d. Dynamic
13
Você também pode gostar
- CXC It May - June 2012Documento12 páginasCXC It May - June 2012jason deruloAinda não há avaliações
- IT Past Paper - May 2012Documento12 páginasIT Past Paper - May 2012Dileya Deonarine100% (3)
- CXC CSEC Information Technology - Practical Paper - January 2005Documento7 páginasCXC CSEC Information Technology - Practical Paper - January 2005Marie Henry100% (1)
- SBA 2 ModifiedDocumento3 páginasSBA 2 Modifiedannmarie100% (1)
- 301 Dock Appointment SchedulingDocumento35 páginas301 Dock Appointment SchedulingraviAinda não há avaliações
- Overview of Oracle Purchasing Open InterfaceDocumento77 páginasOverview of Oracle Purchasing Open InterfaceJai SoniAinda não há avaliações
- CSEC Jan 2011 Paper 1Documento8 páginasCSEC Jan 2011 Paper 1R.D. KhanAinda não há avaliações
- CSEC It Theory Jun 20005Documento11 páginasCSEC It Theory Jun 20005Ronaldo DegazonAinda não há avaliações
- Depression Among Teenagers in Trinidad and TobagoDocumento16 páginasDepression Among Teenagers in Trinidad and TobagoLori-Ann JacobsAinda não há avaliações
- CSEC Information Processing FullDocumento3 páginasCSEC Information Processing Fullakeem lewisAinda não há avaliações
- CSEC IT Jan 2001 PaperDocumento3 páginasCSEC IT Jan 2001 PaperRonaldo DegazonAinda não há avaliações
- CSEC I.T June 2001 AnswersDocumento3 páginasCSEC I.T June 2001 AnswersRonaldo DegazonAinda não há avaliações
- Geography SBADocumento17 páginasGeography SBAkayannaAinda não há avaliações
- CSEC-IT 032-Jan2016Documento20 páginasCSEC-IT 032-Jan2016cuddlesttAinda não há avaliações
- CXC IT Mock Exam 2013 Paper 2Documento10 páginasCXC IT Mock Exam 2013 Paper 2Akini SamuelsAinda não há avaliações
- CSEC Theory Exam 97 - 2002 AnswersDocumento25 páginasCSEC Theory Exam 97 - 2002 AnswersRonaldo Degazon100% (1)
- Practice Information TechnologyDocumento21 páginasPractice Information TechnologyarianaAinda não há avaliações
- CSEC Information Technology January 2018 P2Documento21 páginasCSEC Information Technology January 2018 P2Tyrese SmithAinda não há avaliações
- Hardware Components of a Computer System ExplainedDocumento6 páginasHardware Components of a Computer System ExplainedarianaAinda não há avaliações
- CSEC Information Technology January 2017 P032Documento13 páginasCSEC Information Technology January 2017 P032Jhanett RobinsonAinda não há avaliações
- EDPM CSEC Paper 2018 ReviewDocumento2 páginasEDPM CSEC Paper 2018 ReviewHailey JohnAinda não há avaliações
- CSEC Theory Exam Answers 93 - 96Documento14 páginasCSEC Theory Exam Answers 93 - 96Ronaldo Degazon100% (1)
- CSEC Information Technology June 2007 P02 (Practical)Documento6 páginasCSEC Information Technology June 2007 P02 (Practical)Jhanett RobinsonAinda não há avaliações
- Caribbean Examinations Council: Caribbean Secondary Education Certificate Examination 18 JANUARY 2021 (A.m.)Documento24 páginasCaribbean Examinations Council: Caribbean Secondary Education Certificate Examination 18 JANUARY 2021 (A.m.)Jonathan ThomasAinda não há avaliações
- Edpm 2016 Paper 2pdfDocumento10 páginasEdpm 2016 Paper 2pdfkamesha jamesAinda não há avaliações
- Information Technology Ans 2006 Paper 1Documento7 páginasInformation Technology Ans 2006 Paper 1Hubbak Khan100% (7)
- It Sba Question 2020Documento5 páginasIt Sba Question 2020Pîñëàpplè Ķîđ100% (1)
- CSEC IT Theory Exam Questions 93 - 96Documento9 páginasCSEC IT Theory Exam Questions 93 - 96Ronaldo DegazonAinda não há avaliações
- Information Technology SbaDocumento13 páginasInformation Technology Sbashantay rockettAinda não há avaliações
- CSEC Information Technology June 2013 P1Documento7 páginasCSEC Information Technology June 2013 P1Mik Charlie100% (1)
- Step-by-Step Learning Path designed to help kids learn and grow under 30 charactersDocumento1 páginaStep-by-Step Learning Path designed to help kids learn and grow under 30 charactersJaviene JamesAinda não há avaliações
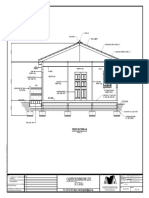
- Cadtech Designs Ltd. (C.T.D.L) : Cross Section A-ADocumento2 páginasCadtech Designs Ltd. (C.T.D.L) : Cross Section A-Aceon sampsonAinda não há avaliações
- CSec Geog SBA GuidelinesDocumento2 páginasCSec Geog SBA GuidelinesJamalAceGl0% (1)
- IT-SBA-2017-2018 Update 2Documento8 páginasIT-SBA-2017-2018 Update 2shakera mcgregorAinda não há avaliações
- Edpm Sba Questions 2023Documento4 páginasEdpm Sba Questions 2023Kimber-Lee SinghAinda não há avaliações
- IT in FOCUS: Secondary Storage DevicesDocumento4 páginasIT in FOCUS: Secondary Storage DevicesarianaAinda não há avaliações
- IT SBA 2015-2016 Problem StatementDocumento5 páginasIT SBA 2015-2016 Problem StatementMaya Willims50% (2)
- Geography SbaDocumento16 páginasGeography SbaMarissa4550% (2)
- Karen Kinglocke EDPM SBADocumento16 páginasKaren Kinglocke EDPM SBALisa B ArnoldAinda não há avaliações
- CSEC Sba Does and Dont'sDocumento2 páginasCSEC Sba Does and Dont'sAnthony hopperpupAinda não há avaliações
- Changes To Structure of Examinations: Csec Change in Structure From 2016 SittingDocumento4 páginasChanges To Structure of Examinations: Csec Change in Structure From 2016 SittingMARK DEFREITASAinda não há avaliações
- Reasons for Cuba's sugar dominance and British Caribbean restorationDocumento10 páginasReasons for Cuba's sugar dominance and British Caribbean restorationMohanie D SudamaAinda não há avaliações
- It Sba 2020 PDFDocumento11 páginasIt Sba 2020 PDFLoganAinda não há avaliações
- Agri S.B.ADocumento27 páginasAgri S.B.Aromiifree100% (3)
- Biology P&D Draft #1Documento9 páginasBiology P&D Draft #1Andre LewisAinda não há avaliações
- CSEC & CAPE RESOURCES LINKS - INVITE LINKS TO DISCORD SERVERS & INVITE LINKS TO TELEGRAM CHANNELS.Documento1 páginaCSEC & CAPE RESOURCES LINKS - INVITE LINKS TO DISCORD SERVERS & INVITE LINKS TO TELEGRAM CHANNELS.Kevin RougierAinda não há avaliações
- Arrays: Yl:information TechnologyDocumento11 páginasArrays: Yl:information TechnologyAntwayne Youcantstopmaprogress HardieAinda não há avaliações
- Landforms of the Morant/Negro RiversDocumento4 páginasLandforms of the Morant/Negro Riverscraig bureyAinda não há avaliações
- Describe How Data Are Stored and Manipulated Within The ComputerDocumento9 páginasDescribe How Data Are Stored and Manipulated Within The Computerapi-247871582100% (1)
- English Sba Oral PieceDocumento2 páginasEnglish Sba Oral PieceXavier CookeAinda não há avaliações
- Document Management EssentialsDocumento13 páginasDocument Management EssentialsJoel WongAinda não há avaliações
- Geo SbaDocumento23 páginasGeo Sbavfebiebfb100% (2)
- It Sba InstructionsDocumento4 páginasIt Sba InstructionsKrama “《•Shem•》” Don'tmiss67% (3)
- It Syllabus CapeDocumento162 páginasIt Syllabus CapeGrace JohnAinda não há avaliações
- HSB Unit Test 2Documento11 páginasHSB Unit Test 2Jessica Kinney0% (1)
- Csec Biology TestDocumento8 páginasCsec Biology TestImmanuel LashleyAinda não há avaliações
- Sba Mark Scheme 2019Documento4 páginasSba Mark Scheme 2019junior subhanAinda não há avaliações
- English SBA BreakdownDocumento4 páginasEnglish SBA BreakdownKamesha WoolcockAinda não há avaliações
- Jamaica Driver's Education Handbook: A Comprehensive Driver Training GuideNo EverandJamaica Driver's Education Handbook: A Comprehensive Driver Training GuideAinda não há avaliações
- Information Technology CXC Multiple Choice Questions PDFDocumento20 páginasInformation Technology CXC Multiple Choice Questions PDFReshawn WorrellAinda não há avaliações
- CSEC IT Sample Exam Papers - 2009 Paper 1 Multiple-Choice QuestionsDocumento10 páginasCSEC IT Sample Exam Papers - 2009 Paper 1 Multiple-Choice Questionsjerome_weirAinda não há avaliações
- Labour Unions or Trade Unions Are Organizations Formed by Workers From Related Fields ThatDocumento2 páginasLabour Unions or Trade Unions Are Organizations Formed by Workers From Related Fields ThatLatoya AndersonAinda não há avaliações
- Chap 02Documento41 páginasChap 02Latoya AndersonAinda não há avaliações
- Word Processing AssessmentDocumento4 páginasWord Processing AssessmentLatoya AndersonAinda não há avaliações
- Lesson Plan On Using Powerpoint - 1Documento4 páginasLesson Plan On Using Powerpoint - 1Latoya AndersonAinda não há avaliações
- cslp2 OsDocumento5 páginascslp2 OsLatoya AndersonAinda não há avaliações
- Lit Assignment Day1Documento1 páginaLit Assignment Day1Latoya AndersonAinda não há avaliações
- Trace Tables: Natalee A. Johnson, ContributorDocumento166 páginasTrace Tables: Natalee A. Johnson, ContributorLatoya AndersonAinda não há avaliações
- Macros Excel PDFDocumento8 páginasMacros Excel PDFWolnei I. S. SimaoAinda não há avaliações
- Introtoprobsolvn PDFDocumento4 páginasIntrotoprobsolvn PDFLatoya AndersonAinda não há avaliações
- Theory TestDocumento1 páginaTheory TestLatoya AndersonAinda não há avaliações
- Bcms - WorkbookDocumento163 páginasBcms - WorkbooklovehsercooAinda não há avaliações
- Database AssessmentDocumento2 páginasDatabase AssessmentLatoya AndersonAinda não há avaliações
- Word ExercisesDocumento1 páginaWord ExercisesLatoya AndersonAinda não há avaliações
- Fieldnames Datatypes: Firstname Lastname Address Telephone GenderDocumento1 páginaFieldnames Datatypes: Firstname Lastname Address Telephone GenderLatoya AndersonAinda não há avaliações
- Pascal NotesDocumento51 páginasPascal NotesChad McdonaldAinda não há avaliações
- Trace Tables: Natalee A. Johnson, ContributorDocumento166 páginasTrace Tables: Natalee A. Johnson, ContributorLatoya AndersonAinda não há avaliações
- Word Processing AssessmentDocumento4 páginasWord Processing AssessmentLatoya AndersonAinda não há avaliações
- Programming Soluions To SyllabusDocumento25 páginasProgramming Soluions To SyllabusChad McdonaldAinda não há avaliações
- Compiled By: Sherry Ann Mohammed-SeuratanDocumento1 páginaCompiled By: Sherry Ann Mohammed-SeuratanLatoya AndersonAinda não há avaliações
- Victoria Philip Graphics Traning Cource BookDocumento37 páginasVictoria Philip Graphics Traning Cource Bookdady odhiamboAinda não há avaliações
- Programing Test 6Documento83 páginasPrograming Test 6Latoya AndersonAinda não há avaliações
- Gradebook Spreadsheet AssessmentDocumento1 páginaGradebook Spreadsheet AssessmentLatoya AndersonAinda não há avaliações
- 990d38f9-fd27-49e8-a956-f61dacc26a12.docDocumento43 páginas990d38f9-fd27-49e8-a956-f61dacc26a12.docLatoya AndersonAinda não há avaliações
- Database AssessmentDocumento2 páginasDatabase AssessmentLatoya AndersonAinda não há avaliações
- Programing Test 7Documento158 páginasPrograming Test 7Latoya AndersonAinda não há avaliações
- PDFDocumento1 páginaPDFLatoya AndersonAinda não há avaliações
- Programming Questions For Form 5Documento3 páginasProgramming Questions For Form 5Latoya AndersonAinda não há avaliações
- I Focus: Echnology For CSECDocumento3 páginasI Focus: Echnology For CSECLatoya AndersonAinda não há avaliações
- Free Preview: Speakers Printer Projector Headphone Microphone Scanner WebcamDocumento1 páginaFree Preview: Speakers Printer Projector Headphone Microphone Scanner WebcamLatoya AndersonAinda não há avaliações
- Speakers Printer Microphone Projector Headphone Scanner WebcamDocumento1 páginaSpeakers Printer Microphone Projector Headphone Scanner WebcamLatoya AndersonAinda não há avaliações
- Sample ASE Exam V1.0Documento2 páginasSample ASE Exam V1.0eyasuAinda não há avaliações
- Allianz FI QuestionsDocumento50 páginasAllianz FI QuestionsDark Cider MortemAinda não há avaliações
- Avaya Predictive Dialing System: 12.0 Service Pack 5 Upgrading To PDS 12.0 Service Pack 5Documento48 páginasAvaya Predictive Dialing System: 12.0 Service Pack 5 Upgrading To PDS 12.0 Service Pack 5Don McMahonAinda não há avaliações
- Pwmaneng PactwareDocumento86 páginasPwmaneng PactwareRafael Martin Anaya FigueroaAinda não há avaliações
- Syntel TechnicalDocumento2 páginasSyntel TechnicalRanjith KumarAinda não há avaliações
- Electric and Magnetic Field Calculations With Finite Element Methods - Stanley HumphriesDocumento130 páginasElectric and Magnetic Field Calculations With Finite Element Methods - Stanley HumphriesHyun Ji LeeAinda não há avaliações
- IT 111 IntroductionDocumento57 páginasIT 111 IntroductionEmmanuelAinda não há avaliações
- Using DataGrid VB6Documento6 páginasUsing DataGrid VB6Erno Bergh100% (1)
- Disk UtilityDocumento2 páginasDisk UtilityFps KaiAinda não há avaliações
- Cluster Synchronization ServicesDocumento4 páginasCluster Synchronization ServicesmramsAinda não há avaliações
- 01 Introduction To Databases (Sept 10)Documento25 páginas01 Introduction To Databases (Sept 10)Nathan WilsonAinda não há avaliações
- ASKVideo Cubase 5 Tutorial DVDDocumento6 páginasASKVideo Cubase 5 Tutorial DVDjonathan100% (1)
- Bikaner Technical University, Bikaner: Web DevelopmentDocumento16 páginasBikaner Technical University, Bikaner: Web DevelopmentMukul PurohitAinda não há avaliações
- Erro 11-05Documento852 páginasErro 11-05matheus felipeAinda não há avaliações
- Business Analyst GlossaryDocumento9 páginasBusiness Analyst GlossaryNu'man FahriansyahAinda não há avaliações
- Opus Userguide2Documento295 páginasOpus Userguide2Purwo DionoAinda não há avaliações
- Red Hat Certified System Administrator (EX200) - RHCSA Exam Prep PDF - 1595884353Documento87 páginasRed Hat Certified System Administrator (EX200) - RHCSA Exam Prep PDF - 1595884353Ricardo SanchezAinda não há avaliações
- Abithana ChintamaniDocumento3 páginasAbithana ChintamaniSarvanRajAinda não há avaliações
- ECE 4180 Embedded Systems Design: Instructor: James HamblenDocumento2 páginasECE 4180 Embedded Systems Design: Instructor: James HamblenRaymondAinda não há avaliações
- DIVA Core 8.1 Install ConfigDocumento324 páginasDIVA Core 8.1 Install Configtharaka18Ainda não há avaliações
- Useful InformationDocumento60 páginasUseful InformationBruno malta da silvaAinda não há avaliações
- EVE Comm BOOK 5.0 2022Documento150 páginasEVE Comm BOOK 5.0 2022teamleaderAinda não há avaliações
- PUNCH-AMNC3IV2 REF-E01-202212 (6796498 - C) - Division-Part 1-11Documento196 páginasPUNCH-AMNC3IV2 REF-E01-202212 (6796498 - C) - Division-Part 1-11anderson pereiraAinda não há avaliações
- (SAP IDOC) - OUTBOUND IDOC CONFIGURATION WITH IDOC OUTPUT TYPE IN SAP - SAP Zero To HeroDocumento20 páginas(SAP IDOC) - OUTBOUND IDOC CONFIGURATION WITH IDOC OUTPUT TYPE IN SAP - SAP Zero To Heroarfath khanAinda não há avaliações
- OpenRISC BasicsDocumento7 páginasOpenRISC BasicsRama DeviAinda não há avaliações
- Incompletion Procedure in SAPDocumento13 páginasIncompletion Procedure in SAPAnupa Wijesinghe100% (1)
- RAHUL CHOUBEY - Updated Term PaperDocumento15 páginasRAHUL CHOUBEY - Updated Term PaperRahul ChoubeyAinda não há avaliações
- Create An Animated GIF in Adobe Photoshop CS3Documento7 páginasCreate An Animated GIF in Adobe Photoshop CS3anon-112642Ainda não há avaliações