Escolar Documentos
Profissional Documentos
Cultura Documentos
Learning Objectives: E-Commerce Security
Enviado por
Lim Cia ChienDescrição original:
Título original
Direitos autorais
Formatos disponíveis
Compartilhar este documento
Compartilhar ou incorporar documento
Você considera este documento útil?
Este conteúdo é inapropriado?
Denunciar este documentoDireitos autorais:
Formatos disponíveis
Learning Objectives: E-Commerce Security
Enviado por
Lim Cia ChienDireitos autorais:
Formatos disponíveis
5/25/11
Chapter 10
E-Commerce Security
Learning Objectives
1. Explain EC-related crimes and why they cannot be stopped. 2. Describe an EC security strategy and why a life cycle approach is needed. 3. Describe the information assurance security principles. 4. Describe EC security issues from the perspective of customers and e-businesses. 5. Identify the major EC security threats, vulnerabilities, and risks.
Chapter 10 Copyright 2009 Pearson Education, Inc. Publishing as Prentice Hall 1
5/25/11
Learning Objectives
6. Identify and describe common EC threats and attacks. 7. Identify and assess major technologies and methods for securing EC communications. 8. Identify and assess major technologies for information assurance and protection of EC networks. 9. Describe types of fraud on the Internet and how to protect against it.
Chapter 10 Copyright 2009 Pearson Education, Inc. Publishing as Prentice Hall 2
Stopping E-Commerce Crimes
Six major reasons why is it difficult for e-tailers to stop cyber criminals and fraudsters:
1. Strong EC security makes online shopping inconvenient for customers 2. Lack of cooperation from credit card issuers and foreign ISPs 3. Online shoppers do not take necessary precautions to avoid becoming a victim 4. IS design and security architecture are vulnerable to attack 5. Software vulnerabilities (bugs) are a huge security problem 6. Managers sometimes ignore due standards of care
Chapter 10
Copyright 2009 Pearson Education, Inc. Publishing as Prentice Hall
5/25/11
Stopping E-Commerce Crimes
Chapter 10
Copyright 2009 Pearson Education, Inc. Publishing as Prentice Hall
Stopping E-Commerce Crimes
due care Care that a company is reasonably expected to take based on the risks affecting its EC business and online transactions.
Chapter 10
Copyright 2009 Pearson Education, Inc. Publishing as Prentice Hall
5/25/11
E-Commerce Security Strategy and Life Cycle Approach
THE INTERNETS VULNERABLE DESIGN THE SHIFT TO PROFIT-MOTIVATED CRIMES
Chapter 10
Copyright 2009 Pearson Education, Inc. Publishing as Prentice Hall
E-Commerce Security Strategy and Life Cycle Approach
IGNORING EC SECURITY BEST PRACTICES
Computing Technology Industry Association (CompTIA) Nonprofit trade group providing information security research and best practices.
Chapter 10
Copyright 2009 Pearson Education, Inc. Publishing as Prentice Hall
5/25/11
Information Assurance
information assurance (IA) The protection of information systems against unauthorized access to or modification of information whether in storage, processing, or transit, and against the denial of service to authorized users, including those measures necessary to detect, document, and counter such threats.
Chapter 10 Copyright 2009 Pearson Education, Inc. Publishing as Prentice Hall 8
Information Assurance
confidentiality Assurance of data privacy and accuracy. Keeping private or sensitive information from being disclosed to unauthorized individuals, entities, or processes. integrity Assurance that stored data has not been modified without authorization; and a message that was sent is the same message that was received. availability Assurance that access to data, the Web site, or other EC data service is timely, available, reliable, and restricted to authorized users.
Chapter 10 Copyright 2009 Pearson Education, Inc. Publishing as Prentice Hall 9
5/25/11
Information Assurance
authentication Process to verify (assure) the real identity of an individual, computer, computer program, or EC Web site. authorization Process of determining what the authenticated entity is allowed to access and what operations it is allowed to perform.
Chapter 10 Copyright 2009 Pearson Education, Inc. Publishing as Prentice Hall 10
Information Assurance
nonrepudiation Assurance that an online customer or trading partner cannot falsely deny (repudiate) their purchase or transaction. digital signature or digital certificate Validates the sender and time stamp of a transaction so it cannot later be claimed that the transaction was unauthorized or invalid.
Chapter 10
Copyright 2009 Pearson Education, Inc. Publishing as Prentice Hall
11
5/25/11
Information Assurance
Chapter 10
Copyright 2009 Pearson Education, Inc. Publishing as Prentice Hall
12
Information Assurance
Chapter 10
Copyright 2009 Pearson Education, Inc. Publishing as Prentice Hall
13
5/25/11
Enterprisewide E-Commerce Security and Privacy Model
EC security program Set of controls over security processes to protect organizational assets. All the policies, procedures, documents, standards, hardware, software, training, and personnel that work together to protect information, the ability to conduct business, and other assets.
Chapter 10 Copyright 2009 Pearson Education, Inc. Publishing as Prentice Hall 14
Enterprisewide E-Commerce Security and Privacy Model
Chapter 10
Copyright 2009 Pearson Education, Inc. Publishing as Prentice Hall
15
5/25/11
Basic E-Commerce Security Issues and Perspectives
From the users perspective:
How can the user know whether the Web server is owned and operated by a legitimate company? How does the user know that the Web page and form have not been compromised by spyware or other malicious code? How does the user know that an employee will not intercept and misuse the information?
From the companys perspective:
How does the company know the user will not attempt to break into the Web server or alter the pages and content at the site?
Copyright 2009 Pearson Education, Inc. Publishing as Prentice Hall
Chapter 10
16
Basic E-Commerce Security Issues and Perspectives
From both parties perspectives:
How do both parties know that the network connection is free from eavesdropping by a third party listening on the line? How do they know that the information sent back and forth between the server and the users browser has not been altered?
Chapter 10
Copyright 2009 Pearson Education, Inc. Publishing as Prentice Hall
17
5/25/11
Threats and Attacks
nontechnical attack An attack that uses chicanery to trick people into revealing sensitive information or performing actions that compromise the security of a network. social engineering A type of nontechnical attack that uses some ruse to trick users into revealing information or performing an action that compromises a computer or network.
Chapter 10 Copyright 2009 Pearson Education, Inc. Publishing as Prentice Hall 18
Threats and Attacks
phishing A crimeware technique to steal the identity of a target company to get the identities of its customers. time-to-exploitation The elapsed time between when a vulnerability is discovered and the time it is exploited.
Chapter 10 Copyright 2009 Pearson Education, Inc. Publishing as Prentice Hall 19
10
5/25/11
Threats and Attacks
SpywareGuide A public reference site for spyware. zero-day incidents Attacks through previously unknown weaknesses in their computer networks.
Chapter 10
Copyright 2009 Pearson Education, Inc. Publishing as Prentice Hall
20
Threats and Attacks
denial of service (DoS) attack An attack on a Web site in which an attacker uses specialized software to send a flood of data packets to the target computer with the aim of overloading its resources. botnet A huge number (e.g., hundreds of thousands) of hijacked Internet computers that have been set up to forward traffic, including spam and viruses, to other computers on the Internet.
Chapter 10 Copyright 2009 Pearson Education, Inc. Publishing as Prentice Hall 21
11
5/25/11
Threats and Attacks
MALICIOUS CODE
malware virus worm macro virus (macro worm) Trojan horse Trojan-Phisher-Rebery banking Trojan
Chapter 10
Copyright 2009 Pearson Education, Inc. Publishing as Prentice Hall
22
Securing E-Commerce Communications
access control Mechanism that determines who can legitimately use a network resource.
biometric systems Authentication systems that identify a person by measurement of a biological characteristic, such as fingerprints, iris (eye) patterns, facial features, or voice.
Copyright 2009 Pearson Education, Inc. Publishing as Prentice Hall
Chapter 10
23
12
5/25/11
Securing E-Commerce Communications
public key infrastructure (PKI) A scheme for securing e-payments using public key encryption and various technical components.
encryption plaintext ciphertext encryption algorithm key (key value) keyspace
Copyright 2009 Pearson Education, Inc. Publishing as Prentice Hall
Chapter 10
24
Securing E-Commerce Communications
symmetric (private) key system An encryption system that uses the same key to encrypt and decrypt the message.
Chapter 10
Copyright 2009 Pearson Education, Inc. Publishing as Prentice Hall
25
13
5/25/11
Securing E-Commerce Communications
Chapter 10
Copyright 2009 Pearson Education, Inc. Publishing as Prentice Hall
26
Securing E-Commerce Communications
public (asymmetric) key encryption Method of encryption that uses a pair of matched keysa public key to encrypt a message and a private key to decrypt it, or vice versa.
public key private key RSA
Copyright 2009 Pearson Education, Inc. Publishing as Prentice Hall
Chapter 10
27
14
5/25/11
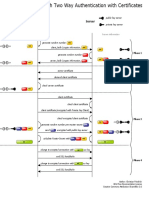
Securing E-Commerce Communications
Digital Signatures and Certificate Authorities
Hash message digest (MD) digital envelope certificate authorities (CAs)
Secure Socket Layer (SSL) Protocol that utilizes standard certificates for authentication and data encryption to ensure privacy or confidentiality.
Chapter 10 Copyright 2009 Pearson Education, Inc. Publishing as Prentice Hall 28
Securing E-Commerce Networks
policy of least privilege (POLP) Policy of blocking access to network resources unless access is required to conduct business.
Chapter 10
Copyright 2009 Pearson Education, Inc. Publishing as Prentice Hall
29
15
5/25/11
Securing E-Commerce Networks
Chapter 10
Copyright 2009 Pearson Education, Inc. Publishing as Prentice Hall
30
Securing E-Commerce Networks
firewall A single point between two or more networks where all traffic must pass (choke point); the device authenticates, controls, and logs all traffic.
packet packet-filtering routers packet filters application-level proxy bastion gateway proxies
Copyright 2009 Pearson Education, Inc. Publishing as Prentice Hall
Chapter 10
31
16
5/25/11
Securing E-Commerce Networks
Chapter 10
Copyright 2009 Pearson Education, Inc. Publishing as Prentice Hall
32
Securing E-Commerce Networks
virtual private network (VPN) A network that uses the public Internet to carry information but remains private by using encryption to scramble the communications, authentication to ensure that information has not been tampered with, and access control to verify the identity of anyone using the network. intrusion detection systems (IDSs) A special category of software that can monitor activity across a network or on a host computer, watch for suspicious activity, and take automated action based on what it sees.
Chapter 10 Copyright 2009 Pearson Education, Inc. Publishing as Prentice Hall 33
17
5/25/11
Securing E-Commerce Networks
honeynet A network of honeypots. honeypots Production system (e.g., firewalls, routers, Web servers, database servers) that looks like it does real work, but which acts as a decoy and is watched to study how network intrusions occur.
Chapter 10 Copyright 2009 Pearson Education, Inc. Publishing as Prentice Hall 34
Fraud and Consumer and Seller Protection
FRAUD ON THE INTERNET CONSUMER PROTECTION
Third-Party Assurance Services
SELLER PROTECTION
What Can Sellers Do?
Chapter 10
Copyright 2009 Pearson Education, Inc. Publishing as Prentice Hall
35
18
5/25/11
Managerial Issues
1. Why should managers learn about EC security? 2. Why is an EC security strategy and life cycle approach needed? 3. How should managers view EC security issues? 4. What is the key to establishing strong e-commerce security? 5. What steps should businesses follow in establishing a security plan? 6. Should organizations be concerned with internal security threats?
Chapter 10
Copyright 2009 Pearson Education, Inc. Publishing as Prentice Hall
36
Summary
1. Stopping e-commerce crimes. 2. EC security strategy and life cycle approach. 3. Information assurance. 4. Enterprisewide EC security and privacy model. 5. Basic EC security issues and perspectives.
Chapter 10 Copyright 2009 Pearson Education, Inc. Publishing as Prentice Hall 37
19
5/25/11
Summary
6. 7. 8. 9. Threats and attacks. Securing EC communications. Technologies for securing networks. Fraud on the Internet and how to protect against it.
Chapter 10
Copyright 2009 Pearson Education, Inc. Publishing as Prentice Hall
38
All rights reserved. No part of this publication may be reproduced, stored in a retrieval system, or transmitted, in any form or by any means, electronic, mechanical, photocopying, recording, or otherwise, without the prior written permission of the publisher. Printed in the United States of America.
Chapter 10
Copyright 2009 Pearson Education, Inc. Publishing as Prentice Hall
39
20
Você também pode gostar
- Chapter09 E-Commerce Security and Fraud Protection 10Documento72 páginasChapter09 E-Commerce Security and Fraud Protection 10Cường Nguyễn100% (1)
- Materi Chpt.5 E-Commerce Security and Payment SystemsDocumento37 páginasMateri Chpt.5 E-Commerce Security and Payment Systemsdonny antaraAinda não há avaliações
- CH11Documento51 páginasCH11svccam1Ainda não há avaliações
- Cybersecurity for Beginners : Learn the Fundamentals of Cybersecurity in an Easy, Step-by-Step Guide: 1No EverandCybersecurity for Beginners : Learn the Fundamentals of Cybersecurity in an Easy, Step-by-Step Guide: 1Ainda não há avaliações
- E-Commerce: Business. Technology. SocietyDocumento49 páginasE-Commerce: Business. Technology. Societymajumderjeta001Ainda não há avaliações
- Accounting Information Systems,: 6 Edition James A. HallDocumento51 páginasAccounting Information Systems,: 6 Edition James A. HalladhystyAinda não há avaliações
- Computers Are Your Future: Chapter 9: Privacy, Crime, and SecurityDocumento44 páginasComputers Are Your Future: Chapter 9: Privacy, Crime, and SecurityRamazan MaçinAinda não há avaliações
- Information Technology INT1001: Privacy, Crime & SecurityDocumento42 páginasInformation Technology INT1001: Privacy, Crime & SecurityDebbie DebzAinda não há avaliações
- 4 5865984522339750213Documento35 páginas4 5865984522339750213Raihan MahdiAinda não há avaliações
- E-Commerce: Business. Technology. SocietyDocumento49 páginasE-Commerce: Business. Technology. SocietyTanmay GharpureAinda não há avaliações
- E-Commerce: Business. Technology. SocietyDocumento51 páginasE-Commerce: Business. Technology. Societyas7Ainda não há avaliações
- Chapter 9 - Study GuideDocumento27 páginasChapter 9 - Study GuideLoretta Lynn AltmayerAinda não há avaliações
- Safe Harbor DatasheetDocumento5 páginasSafe Harbor DatasheetDan ArgynovAinda não há avaliações
- Unit V CSSDocumento12 páginasUnit V CSSAbhishek SrivastavaAinda não há avaliações
- Top 10 Common Cybersecurity Mistakes Employees Make and How To Avoid Them - SecurzeDocumento10 páginasTop 10 Common Cybersecurity Mistakes Employees Make and How To Avoid Them - Securzedanniel foyAinda não há avaliações
- THE SECURITY SYSTEM OF ECOMERCE - FinalDocumento17 páginasTHE SECURITY SYSTEM OF ECOMERCE - FinalDr Yousef ElebiaryAinda não há avaliações
- IT Security and Risk ManagementDocumento10 páginasIT Security and Risk ManagementNikhil GangwarAinda não há avaliações
- Ch05laudon-Traver Ec10Documento62 páginasCh05laudon-Traver Ec10Jihad AounAinda não há avaliações
- Safety of Web Applications: Risks, Encryption and Handling Vulnerabilities with PHPNo EverandSafety of Web Applications: Risks, Encryption and Handling Vulnerabilities with PHPAinda não há avaliações
- Day 1Documento28 páginasDay 1Mayank jainAinda não há avaliações
- Security TechGuide Mobile 1011 v2Documento21 páginasSecurity TechGuide Mobile 1011 v2Victor ChuAinda não há avaliações
- Group 6: CybersecurityDocumento4 páginasGroup 6: CybersecurityCherlie Mae DumaluanAinda não há avaliações
- Final Ecomers AssigmentDocumento16 páginasFinal Ecomers Assigmentnana fosuAinda não há avaliações
- Workshop ISOEHDocumento8 páginasWorkshop ISOEHJeeva JpAinda não há avaliações
- Free Download Network Defense and Countermeasures Principles and Practices 4Th Edition William Easttom Full Chapter PDFDocumento51 páginasFree Download Network Defense and Countermeasures Principles and Practices 4Th Edition William Easttom Full Chapter PDFkimberly.watring349100% (23)
- Network SecurityDocumento53 páginasNetwork SecuritytsayeedctgAinda não há avaliações
- A Complete Strategy For Web Application SecurityDocumento17 páginasA Complete Strategy For Web Application Securitymemoona bibiAinda não há avaliações
- Information Security Awareness & Internet Banking Acceptance-FullDocumento16 páginasInformation Security Awareness & Internet Banking Acceptance-FullPrarthana Srinivasan100% (1)
- Predicting Phishing Websites Based On Self-Structuring Neural NetworkDocumento17 páginasPredicting Phishing Websites Based On Self-Structuring Neural NetworkSebhazz Rios RAinda não há avaliações
- AIS Chapter 12Documento6 páginasAIS Chapter 12Imtiaz SultanAinda não há avaliações
- Introducing To Network SecurityDocumento10 páginasIntroducing To Network SecuritycursantcataAinda não há avaliações
- The Three Pillars of TrustDocumento12 páginasThe Three Pillars of Trustsamir47Ainda não há avaliações
- E Business With DiagramDocumento7 páginasE Business With DiagramJinson VargheseAinda não há avaliações
- E-Policy: How To Develop Computer, E-Policy, and Internet Guidelines To Protect Your Company and Its AssetsDocumento260 páginasE-Policy: How To Develop Computer, E-Policy, and Internet Guidelines To Protect Your Company and Its Assetskevram950Ainda não há avaliações
- Ethical Hacking and Computer Securities for BeginnersNo EverandEthical Hacking and Computer Securities for BeginnersAinda não há avaliações
- E-Commerce Security IssuesDocumento13 páginasE-Commerce Security IssuesAJay Kumar SaklaniAinda não há avaliações
- It Securiyt Ass 2 FinzlDocumento90 páginasIt Securiyt Ass 2 FinzlBehailu DemissieAinda não há avaliações
- Securing Intellectual Property: Protecting Trade Secrets and Other Information AssetsNo EverandSecuring Intellectual Property: Protecting Trade Secrets and Other Information AssetsNota: 3 de 5 estrelas3/5 (3)
- Computer Security Research Paper TopicsDocumento6 páginasComputer Security Research Paper Topicsaflbskroi100% (1)
- Cybersecurity Guidelines Oct 2018Documento36 páginasCybersecurity Guidelines Oct 2018fayezAinda não há avaliações
- Thesis E-Commerce SecurityDocumento5 páginasThesis E-Commerce Securityezknbk5h100% (2)
- CH 5Documento51 páginasCH 5Muhammad SandriAinda não há avaliações
- JAMES A. HALL - Accounting Information System Chapter 12Documento55 páginasJAMES A. HALL - Accounting Information System Chapter 12Joe VaTa100% (2)
- Ctitl10 Onlinesafetyandsecurity 201008065025Documento9 páginasCtitl10 Onlinesafetyandsecurity 201008065025April Joy de LimaAinda não há avaliações
- Securing Cloud Services - A pragmatic guide: Second editionNo EverandSecuring Cloud Services - A pragmatic guide: Second editionAinda não há avaliações
- Best Practices For Securing Your Enterprise:: 10 Things You Need To KnowDocumento10 páginasBest Practices For Securing Your Enterprise:: 10 Things You Need To KnowShubham GuptaAinda não há avaliações
- Employee Training Cybersecurity 101 e Book 1 UntangleDocumento17 páginasEmployee Training Cybersecurity 101 e Book 1 UntangleJuan Carlos Morales100% (2)
- Data ScienceDocumento5 páginasData Sciencerupesh karanamAinda não há avaliações
- Cyber Security: Essential principles to secure your organisationNo EverandCyber Security: Essential principles to secure your organisationAinda não há avaliações
- Cyber Security BacicsDocumento53 páginasCyber Security BacicsJoël KangalaAinda não há avaliações
- Confidentiality and Privacy Controls: Andreas Rudolf AntonDocumento7 páginasConfidentiality and Privacy Controls: Andreas Rudolf AntonAs17 As17Ainda não há avaliações
- The Cyber Security Handbook – Prepare for, respond to and recover from cyber attacksNo EverandThe Cyber Security Handbook – Prepare for, respond to and recover from cyber attacksAinda não há avaliações
- Rakreprt TechfinalDocumento16 páginasRakreprt TechfinalRaghu G JAinda não há avaliações
- Web ProgrammingDocumento14 páginasWeb Programmingalaahusseinn25Ainda não há avaliações
- Cyber Risks for Business Professionals: A Management GuideNo EverandCyber Risks for Business Professionals: A Management GuideAinda não há avaliações
- Understanding Accounting and Financial Information: SeventeenDocumento41 páginasUnderstanding Accounting and Financial Information: SeventeenLim Cia ChienAinda não há avaliações
- Marketing: Helping Buyers Buy: ThirteenDocumento43 páginasMarketing: Helping Buyers Buy: ThirteenLim Cia ChienAinda não há avaliações
- Human Resource Management: Finding and Keeping The Best EmployeesDocumento55 páginasHuman Resource Management: Finding and Keeping The Best EmployeesLim Cia ChienAinda não há avaliações
- Using Effective Promotions: SixteenDocumento40 páginasUsing Effective Promotions: SixteenLim Cia ChienAinda não há avaliações
- Production and Operations Management of Goods and Services: Chapter NineDocumento51 páginasProduction and Operations Management of Goods and Services: Chapter NineLim Cia ChienAinda não há avaliações
- How To Form A Business: Chapter FiveDocumento42 páginasHow To Form A Business: Chapter FiveLim Cia ChienAinda não há avaliações
- Demanding Ethical and Socially Responsible Behavior: Chapter FourDocumento39 páginasDemanding Ethical and Socially Responsible Behavior: Chapter FourLim Cia ChienAinda não há avaliações
- Chapter 02 RevisedDocumento16 páginasChapter 02 RevisedLim Cia ChienAinda não há avaliações
- Chapter 14 RevisedDocumento18 páginasChapter 14 RevisedLim Cia ChienAinda não há avaliações
- Understanding How Economics Affects Business: Chapter TwoDocumento53 páginasUnderstanding How Economics Affects Business: Chapter TwoLim Cia ChienAinda não há avaliações
- Learning Objectives: Retailing in Electronic Commerce: Products and ServicesDocumento17 páginasLearning Objectives: Retailing in Electronic Commerce: Products and ServicesLim Cia ChienAinda não há avaliações
- Software Testing Strategies: These Courseware Materials Are To Be Used in Conjunction WithDocumento24 páginasSoftware Testing Strategies: These Courseware Materials Are To Be Used in Conjunction WithLim Cia ChienAinda não há avaliações
- Software Testing Techniques: These Courseware Materials Are To Be Used in Conjunction WithDocumento24 páginasSoftware Testing Techniques: These Courseware Materials Are To Be Used in Conjunction WithLim Cia ChienAinda não há avaliações
- Pert 10 Desain User InterfaceDocumento19 páginasPert 10 Desain User InterfaceLim Cia ChienAinda não há avaliações
- Security 4CSDocumento6 páginasSecurity 4CSEsraa Sayed Abdelhamed SayedAinda não há avaliações
- Strengthening American Cybersecurity ActDocumento211 páginasStrengthening American Cybersecurity ActJake DraugelisAinda não há avaliações
- Deepak Jeengar Report Part 1Documento7 páginasDeepak Jeengar Report Part 1jayaAinda não há avaliações
- EY Eu General Data Protection Regulation Are You ReadyDocumento16 páginasEY Eu General Data Protection Regulation Are You ReadyAntonio VukadinAinda não há avaliações
- KerberosDocumento15 páginasKerberosChalla KiranAinda não há avaliações
- ODEX Administrators GuideDocumento56 páginasODEX Administrators GuidemoparmAinda não há avaliações
- Secure Email Gateway - Quiz Attempt ReviewDocumento2 páginasSecure Email Gateway - Quiz Attempt Reviewking jumper343Ainda não há avaliações
- ICAO Annexes Booklet enDocumento50 páginasICAO Annexes Booklet enBurcu SaglamAinda não há avaliações
- 03 Security User AuthenticationDocumento56 páginas03 Security User AuthenticationTrus AtholaAinda não há avaliações
- A Cypherpunk'S Manifesto: Eric HughesDocumento12 páginasA Cypherpunk'S Manifesto: Eric Hughesdeni fortranAinda não há avaliações
- Script HTML Password FBDocumento1 páginaScript HTML Password FBAyub PrayogaAinda não há avaliações
- Dealing With Data Breaches Amidst Changes in TechnologyDocumento7 páginasDealing With Data Breaches Amidst Changes in TechnologyAI Coordinator - CSC JournalsAinda não há avaliações
- Part A-Theoretical Questions: CybersecurityDocumento42 páginasPart A-Theoretical Questions: Cybersecurityadikesa100% (1)
- PKI SecurityDocumento64 páginasPKI SecurityVivien Di100% (1)
- SSL Handshake With Two-Way Authentication With CertificatesDocumento1 páginaSSL Handshake With Two-Way Authentication With CertificatesShailendra PandeyAinda não há avaliações
- CS549 Chapter 13 NotesDocumento25 páginasCS549 Chapter 13 NotesafadlallahAinda não há avaliações
- Hacking Web ApplicationsDocumento5 páginasHacking Web ApplicationsDeandryn RussellAinda não há avaliações
- CHAPTER 5 - Attacks, Concepts and Techniques-LESSON 2Documento10 páginasCHAPTER 5 - Attacks, Concepts and Techniques-LESSON 2venugopal_charry1921Ainda não há avaliações
- Documents Posters Encryption PlotterDocumento1 páginaDocuments Posters Encryption PlotterJames HeathAinda não há avaliações
- Solved MCQ of Computer Security Set - 1Documento4 páginasSolved MCQ of Computer Security Set - 1MohammedAinda não há avaliações
- HackingDocumento24 páginasHackingshanvi12Ainda não há avaliações
- Cybersecurity Networked Systems The Average Cost of A Data Breach Was USD 3.86 Million Globally, and USD 8.64 Million in The United StatesDocumento11 páginasCybersecurity Networked Systems The Average Cost of A Data Breach Was USD 3.86 Million Globally, and USD 8.64 Million in The United StatesYzon FabriagAinda não há avaliações
- Risk Report of Task Id 41019Documento20 páginasRisk Report of Task Id 41019Amr KenawyAinda não há avaliações
- C235 - IT Security and Management: Modern Symmetric CiphersDocumento33 páginasC235 - IT Security and Management: Modern Symmetric CiphersSundeel Bin HaleemAinda não há avaliações
- De Sech Able 001Documento3 páginasDe Sech Able 001Yuniioor UrbaezAinda não há avaliações
- IT Incident Reporting 24 Sep 19Documento3 páginasIT Incident Reporting 24 Sep 19krishnaAinda não há avaliações
- MCS-054 Block-4Documento87 páginasMCS-054 Block-4Kamal TiwariAinda não há avaliações
- Course Code: CSE 606 Course Title: Cryptography & Information SecurityDocumento6 páginasCourse Code: CSE 606 Course Title: Cryptography & Information SecurityNazmul HaqueAinda não há avaliações
- OSINT CyberTalentsDocumento8 páginasOSINT CyberTalentsaneyomainstreamAinda não há avaliações
- CLASS 9TH - (CHAP 7 Cyber Safety)Documento4 páginasCLASS 9TH - (CHAP 7 Cyber Safety)Nischith VkAinda não há avaliações