Escolar Documentos
Profissional Documentos
Cultura Documentos
155 Pdfsam TCPIP Professional Reference Guide TQW Darksiderg
Enviado por
bharath_mv7Título original
Direitos autorais
Formatos disponíveis
Compartilhar este documento
Compartilhar ou incorporar documento
Você considera este documento útil?
Este conteúdo é inapropriado?
Denunciar este documentoDireitos autorais:
Formatos disponíveis
155 Pdfsam TCPIP Professional Reference Guide TQW Darksiderg
Enviado por
bharath_mv7Direitos autorais:
Formatos disponíveis
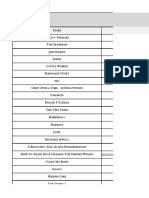
138 Exhibit 7.
9 OSPF Message Types
Type 1 Type 2 Type 3 Type 4 Type 5 Type 6
TCP/IP Professional Reference Guide
Router Links Advertisement Network Links Advertisement Summary Links Advertisement Autonomous System Boundary Router Summary Link Advertisement Autonomous System External Link Advertisement Multicast Group Membership Link State Advertisement
Type 1 Message
A Type 1 LSA message is used to transmit information about a routers interface and the cost associated with the interface. Because an interface is dened with the use of an IP address, the information in a routers Link State Advertisement consists of an IP address-cost metric pair. Exhibit 7.9 lists the six types of SLA messages OSPF routers use.
Type 2 Message
The purpose of a Type 2 LSA message is to inform all routers within an area of the presence of a designated router (DR). Thus, a DR oods a Type 2 LSA upon its election. This message contains information about all routers in the area, as well as the fact that one is now the DR for the area.
Type 3 Message
Because an area border router (BR) connects adjacent areas, a mechanism is needed to describe networks reachable via the adjacent border router (ABR). Thus, an ABR router oods a Type 3 message into an area to inform routers in the area about other networks that are reachable from outside the area.
Type 4 Message
A Type 4 message describes the cost from the router issuing the message to an autonomous system boundary router. Thus, this message allows a boundary router that functions as a gateway to another autonomous system to note the cost associated with accessing different networks via different paths within its system.
Routing and Routing Protocol
139
Type 5 Message
A boundary router that connects autonomous systems generates a Type 5 message. This message describes an external network on another system reachable by the router. Thus, this message ows to routers in one autonomous system to describe a network reachable via a different system.
Type 6 Message
The last type of LSA is a Type 6 message. A Type 6 message enables a multicast-enabled OSPF router to distribute multicast group information instead of having to transmit multiple copies of packets.
Operation
The actual initialization of OSPF in an autonomous area requires a series of packets to be exchanged that enables the Designated Router and Backup to be selected and router adjacencies to be noted prior to routing information being exchanged. The most basic exchange between OSPF routers occurs via the transmission of Hello messages. Such messages ow between routers that enable routers within an area to discover one another, as well as to note the relationship between routers. Once the DR and BDR are selected, additional messages are exchanged that eventually enable one area to become aware of other areas, as well as networks reachable outside of the current autonomous system. Although the initial learning process is complex, once routing table information is constructed, updates only occur when there is a change in the network structure or every 30 minutes. Thus, although OSPF initially requires more bandwidth than RIP, it rapidly reduces its bandwidth requirements.
Chapter 8
Security
One of the key advantages of the TCP/IP protocol suite is also a disadvantage. The advantage is its openness, with RFCs used to identify the manner by which the protocol suite operates. Unfortunately, this openness has a price: it allows just about any person to determine how the various components that make up the protocol suite operate. This capability enables people who wish to do harm to IP networks and computers operating on those networks to develop techniques to do so. In comparison, other protocol suites that were developed by commercial organizations may not be as extensively documented. Thus, people who wish to exploit the weaknesses of a protocol suite developed by a commercial organization may face a far more daunting task. Because the use of the Internet has expanded at an almost exponential rate, another problem associated with the TCP/IP protocol suite involves the connection of private networks to the Internet. With almost 100 million users now connected to the Internet on a global basis, this means that if only a very small fraction of Internet users attempt to break into different hosts, the total number would become considerable. Recognizing the openness of the TCP/IP protocol suite and the ability of people from Bangladesh to Belize to hack computers, security has become a major consideration of network managers and LAN administrators and is the focus of this chapter. This chapter focuses on a series of TCP/IP security-related topics. Because the router represents both the entryway into a network as well as the rst line of defense, this device is considered rst. One can consider using this examining measure to prevent unauthorized entry into a routers conguration sub-system. Also discussed are other methods one can use to create access lists that perform packet ltering. Although the use of router access lists can considerably enhance the security of a network, there are certain functions and features that they do not perform. Thus, many network managers and LAN administrators rightly supplement the security capability of a router with a rewall, the operation of which is also covered in this chapter.
141
142
TCP/IP Professional Reference Guide
Router Access Considerations
Any network connected to the Internet gains connectivity through the use of a router. This means that if a remote user can gain access into an organizations router, it becomes possible for that user to reprogram the router. This reprogramming could result in the creation of a hole in a previously created access list that enables the person to overcome any barrier the access list created to the ow of packets. If the person is not a simple hacker, but a paid agent, he or she might then reprogram an organizations router to initially transport packets to a location where they are recorded and then forwarded onto their destination. Thus, the ability to control access to a routers conguration capability cannot be overlooked. This represents one of the rst facts that one should consider if and when connecting an organizations private network to the Internet.
Router Control
Most routers provide several methods that can be used to control their operation. Although routers produced by different vendors may not support all of the methods to be discussed herein, they will usually support one or more of the methods to be discussed in this section. Those methods include direct cabling via a control port into the router, Telnet access, and Web access.
Direct Cabling
All routers include a control port that enables a terminal device to be directly cabled to a router. The terminal device can be a PC or a dumb asynchronous terminal. Once connected to the router, a user normally must enter a password to access the conguration system of the router. The exception to this is the rst time a person accesses the router via a direct connection, because most routers are shipped without a password being enabled. Thus, if someone has unpacked a router, connected a terminal to its direct connect conguration port, and congured an access password, the next person to use the terminal would have to know the password to be able to congure the router.
Benets and Limitations
The key benet of a direct cabling conguration method is that only people who can physically access the terminal can congure the router. Thus, this conguration method precludes the ability of a remote user (to include potential hackers) from gaining access to an organizations router conguration substation and changing one or more parameters. Unfortunately, this advantage is also a disadvantage: it precludes the ability to remotely congure a router. Thus, if ones organization has trained personnel at each router location, or if ones budget permits the accumulation of frequent yer mileage as one
Security
143
sends employees on the road to recongure routers, one can consider the use of direct cabling. If the organization needs to be responsive to changing requirements and cannot afford to have trained employees at each router location, one would then prefer a technique that provides a remote router management capability. This capability can be obtained through the use of Telnet or Web access to the router.
Telnet and Web Access
Some routers include the ability for remote conguration via Telnet. Other routers extend remote router conguration capability to Web browsers via the use of the HyperText Transport Protocol (HTTP). For either situation, all that is required for a remote user to gain access to the conguration subsystem of a router is its IP address and password, assuming a password was previously congured to block casual access into the routers conguration subsystem. An IP address is required because both Telnet and Web access, while possible via a host name resolved into an IP address as well as via a directly entered IP address, is usually not obtainable via the former. This is because many organizations do not assign a host name to a router. Once a person uses Telnet or a Web browser to connect to a router, that user will then be prompted to enter a password to gain access to the routers subsystem. An example of this situation is illustrated in Exhibit 8.1, which shows the use of the Microsoft Windows Telnet client program in an attempt to gain access to a Cisco Systems router. In the example shown in Exhibit 8.1, access to a Cisco router can require the use of two passwords. The rst password is used to gain access to the routers virtual terminal (vt) port that allows a person to display router information, but precludes the ability to congure the router. If one types the command enable to gain access to the routers privileged mode of operation, one will be prompted to enter a second password. When this password is successfully entered, One obtains the ability to both display information as well as to congure the router. In a Cisco router environment, once one types the command enable and enters an applicable password, the system prompt changes from a greater than sign (>) to a pound sign (#). In the example shown in Exhibit 8.1, the name Macon was previously assigned to the router being accessed, resulting in the router name prexing the prompt that denotes the mode being occupied. Once in the privileged mode, one can change the routers conguration.
Protection Limitation
One of the problems associated with remote access to routers is that the basic method of protection via a password can be overcome if care is not taken during the password creation process. This is because most routers will simply disconnect the Telnet or Web connection after three failed password entry
144
TCP/IP Professional Reference Guide
Exhibit 8.1 Using Telnet to Access the Conguration Subsystem on a Router
Security
145
attempts, enabling a user to try three more passwords. Because of this limitation, several hackers in the past are known to have written scripts that would try three entries at a time from an electronic dictionary. If the network manager or LAN administrator used a name, object, or expression that could be extracted from an electronic dictionary, it was not long before the hacker gained entry into a routers virtual terminal capability and essentially took control of the device. Thus, it is extremely important to use an alphanumeric password combination that is not in a dictionary for password creation. In addition, through the use of an access list, it becomes possible to restrict access to a routers virtual terminal (vt) port from a known IP address. Therefore, it is possible with some effort to make it extremely difcult for a remote user other than a designated employee or group of employees to remotely access an organizations routers. There is one limitation associated with the use of a routers access list that warrants discussion. Because an access list would be developed to allow packets from a known IP address to access a routers virtual terminal (vt) port, this means the address cannot be dynamically assigned. In addition to requiring a xed IP address, the use of an access list to protect access to a vt port also restricts the ability of traveling employees to gain access to a routers vt port. This is because ISPs commonly assign IP addresses dynamically. For example, an employee communication from San Francisco at 3:00 p.m. would have a different temporary IP address than that assigned when he or she accessed the Internet at 2:00 p.m. Similarly, if the employee took a trip to San Jose at 6:00 p.m. and accessed the Internet, another IP address would be temporarily assigned to the employees notebook computer. One method to overcome the previously described problem is for traveling employees to dial an access server that is directly connected to the organizations network. If one congures the server to accept a static IP address assigned to an employees notebook, then a routers access list could be used to allow remote access for authorized employees that travel around the country or around the globe. This action, of course, results in the necessity for employees to use long distance instead of potentially more economical Internet access. Because many organizations only periodically require traveling employees to recongure organizational routers, the cost of potential long-distance support may not represent a detriment to its use. Although the previous discussion focused on Telnet access to a routers vt port, some routers also support conguration via a Web browser that results in similar, but not identical, issues. That is, while one can use a routers access list capability to allow HTTP access from predened IP addresses, Web browsers also support secure HTTP, referred to by the mnemonic HTTPS. If the router supports HTTPS, then one may be able to support the use of public key encryption and preassigned digital certicates between the Web browser and router, adding an additional level of security to gaining remote access to a routers conguration subsystem. Given an appreciation for the manner by which local and remote users can gain access to a routers conguration subsystem, one can now focus on
146
TCP/IP Professional Reference Guide
the use of access lists. In doing so, the author examines the rationale for their use, the basic types of access lists, and new capabilities recently added to access lists that considerably enhance their functionality.
Router Access Lists
Because a router is designed to interconnect geographically separated networks, this device also represents an entry point into a network. Recognizing this fact, one of the earliest features added to routers was an access list capability, which is the subject of this section. An access list, also referred to as an access control list, represents one or more statements that, when executed by a router, perform packet ltering. Access lists can be congured for a variety of network protocols, such as Apple Talk, IP, IPX, DECnet, and Vines. Once an access list is created, it must be applied to an interface to take effect. In doing so, one must consider whether one wants to lter packets owing into the organizations network from an untrusted area, or packets leaving the organizations network, or both.
Rationale for Use
While the primary use of access lists is to bar trafc to enhance network security, there are other reasons to use this router feature. One reason that is gaining acceptance is the ability to lter packets based upon the IP Type of Service (TOS) eld. This allows trafc to be prioritized when entering or leaving a queue. Another reason for using access lists is to implement corporate policy concerning the use of different services on an intranet or accessible via the Internet. For example, corporate policy may be to bar all or certain employees from Web-surng. Two additional reasons for conguring access lists include restricting the contents of routing updates and providing a mechanism for trafc ow. While each of these reasons can be sufcient in and of themselves to use access lists, the primary reason for their use is to obtain a basic level of security. This chapter section primarily focuses on the use of access lists to enhance network security. Because Cisco Systems has a dominant market share of the installed base of routers, examples in this section will be focused on Cisco access lists. However, other router vendors follow a similar methodology by which access lists are created and applied to an interface, either inbound or outbound. While one may have to tailor examples in this section to the access list format supported by other router manufacturers, the basic concepts are applicable to most routers. Thus, the information presented in this section should serve as a guide to the use of a routers access list as the rst line of defense of a network, regardless of the manufacturer of the device. Although access lists were developed to support different protocols, the primary focus here is on the IP. This is because IP is the only protocol supported for use on the Internet, and most organizations that use access lists
Security
147
Exhibit 8.2
Connecting a Private Network Consisting of Two LANs to the Internet
for security do so with respect to data owing to and from the Internet with respect to an organizations private network. Exhibit 8.2 illustrates the use of a router to connect two LANs both to each other as well as to the Internet. In this example, the router provides a gateway from the LANs to the Internet. Because many, if not most, organizations do not want to allow any user that accesses the Internet to gain access to their private network, it is quite common for the network manager or LAN administrator to program the router to restrict the ow of packets. This packet ow restriction is accomplished through the use of a routers access list capability, and the technique used by the router in examining packets specied by an access list is referred to as packet ltering.
Ports Govern Data Flow
In examining Exhibit 8.2, note the three router ports labeled S0, E0, and E1. Port S0 represents a serial port that provides connectivity from the router to and from Internet data ows. Ports labeled E0 and E1 represent Ethernet ports that provide connectivity to individual Ethernet LANs that represent an organizations private network. To use a router to obtain a packet ltering capability requires one to perform two functions. First, one or more access lists must be created. Next, each access list that is created must be applied to a specic port in a specic data ow direction. Data ow direction is dened as follows: data owing toward a router is considered to ow in, while the direction of data leaving a router is considered to ow out. Thus, in a Cisco router environment, the key words in and out are used when an access list is applied to an interface to indicate which data ow direction packet ltering specied by the access list should occur.
148
TCP/IP Professional Reference Guide
Data Flow Direction
Because one can apply up to two access lists per router port (one inbound, one outbound), it becomes possible to lter packets at different locations with respect to a routers interfaces. In general, it is a good rule to apply an access list as close as possible to the data source to be ltered. For example, if one wants to lter packets entering the organizations private network from the Internet, one should apply an access list to port S0 in the inbound direction. Although one could create access lists for ports E0 and E1, if one applies the access list to port S0, it would protect the entire network with one access list and avoid a bit of a duplication of effort. This duplication would be necessary if one needed to permit or deny similar data ows to or from each network. For example, if one wanted to block Web surng from stations on both LANs, one could either code an applicable access list and apply it to interface S0, or code two access lists and apply one to interface E0 and the other to interface E1. Similarly, if one wanted to restrict the ability of network users on LAN A to surf the Web, it would be easier to apply an access list to port E0 in the inbound direction to lter all HTTP data ows than to apply the access list to port S0. If one applied the list to port S0 and simply ltered on HTTP, one could adversely affect the ability of users on LAN B to surf the Internet. This would then require one to program a more complex access list to apply to port S0 to block LAN A users while allowing LAN B users to surf the Web. Thus, for most situations, one should attempt to place an access list as close as possible to the source of data to be ltered. Given an appreciation for the general use of access list, one can now probe deeper into the specic types of access lists that can be used.
Types of Access Lists
There are two basic types of access lists supported by Cisco router: standard and extended. A standard access list is limited to performing ltering on source addresses. In comparison, an extended access list permits ltering based upon source address, destination address, source port, destination port, and even the setting of bits within certain elds of a packet.
Standard Access Lists
The basic format of a standard IP access list is shown below. access-list list # {permit | deny } source [wildcardmask] [log] Although one access list can be assigned to one direction on an interface, a router can support multiple access lists. Thus, the list # represents a decimal from 1 to 99 that identies a particular access list. In addition, because Cisco
Você também pode gostar
- A Heartbreaking Work Of Staggering Genius: A Memoir Based on a True StoryNo EverandA Heartbreaking Work Of Staggering Genius: A Memoir Based on a True StoryNota: 3.5 de 5 estrelas3.5/5 (231)
- The Sympathizer: A Novel (Pulitzer Prize for Fiction)No EverandThe Sympathizer: A Novel (Pulitzer Prize for Fiction)Nota: 4.5 de 5 estrelas4.5/5 (120)
- Devil in the Grove: Thurgood Marshall, the Groveland Boys, and the Dawn of a New AmericaNo EverandDevil in the Grove: Thurgood Marshall, the Groveland Boys, and the Dawn of a New AmericaNota: 4.5 de 5 estrelas4.5/5 (266)
- The Little Book of Hygge: Danish Secrets to Happy LivingNo EverandThe Little Book of Hygge: Danish Secrets to Happy LivingNota: 3.5 de 5 estrelas3.5/5 (399)
- Never Split the Difference: Negotiating As If Your Life Depended On ItNo EverandNever Split the Difference: Negotiating As If Your Life Depended On ItNota: 4.5 de 5 estrelas4.5/5 (838)
- The Emperor of All Maladies: A Biography of CancerNo EverandThe Emperor of All Maladies: A Biography of CancerNota: 4.5 de 5 estrelas4.5/5 (271)
- The Subtle Art of Not Giving a F*ck: A Counterintuitive Approach to Living a Good LifeNo EverandThe Subtle Art of Not Giving a F*ck: A Counterintuitive Approach to Living a Good LifeNota: 4 de 5 estrelas4/5 (5794)
- The World Is Flat 3.0: A Brief History of the Twenty-first CenturyNo EverandThe World Is Flat 3.0: A Brief History of the Twenty-first CenturyNota: 3.5 de 5 estrelas3.5/5 (2259)
- The Hard Thing About Hard Things: Building a Business When There Are No Easy AnswersNo EverandThe Hard Thing About Hard Things: Building a Business When There Are No Easy AnswersNota: 4.5 de 5 estrelas4.5/5 (344)
- Team of Rivals: The Political Genius of Abraham LincolnNo EverandTeam of Rivals: The Political Genius of Abraham LincolnNota: 4.5 de 5 estrelas4.5/5 (234)
- The Gifts of Imperfection: Let Go of Who You Think You're Supposed to Be and Embrace Who You AreNo EverandThe Gifts of Imperfection: Let Go of Who You Think You're Supposed to Be and Embrace Who You AreNota: 4 de 5 estrelas4/5 (1090)
- Hidden Figures: The American Dream and the Untold Story of the Black Women Mathematicians Who Helped Win the Space RaceNo EverandHidden Figures: The American Dream and the Untold Story of the Black Women Mathematicians Who Helped Win the Space RaceNota: 4 de 5 estrelas4/5 (895)
- The Black Box & Other Psychic Generators DavisDocumento119 páginasThe Black Box & Other Psychic Generators DavisIPDENVER85% (27)
- Elon Musk: Tesla, SpaceX, and the Quest for a Fantastic FutureNo EverandElon Musk: Tesla, SpaceX, and the Quest for a Fantastic FutureNota: 4.5 de 5 estrelas4.5/5 (474)
- Brain School by Howard EatonDocumento288 páginasBrain School by Howard Eatonbharath_mv775% (4)
- Brain School by Howard EatonDocumento288 páginasBrain School by Howard Eatonbharath_mv775% (4)
- The Unwinding: An Inner History of the New AmericaNo EverandThe Unwinding: An Inner History of the New AmericaNota: 4 de 5 estrelas4/5 (45)
- The Yellow House: A Memoir (2019 National Book Award Winner)No EverandThe Yellow House: A Memoir (2019 National Book Award Winner)Nota: 4 de 5 estrelas4/5 (98)
- NLP Secrets PDFDocumento64 páginasNLP Secrets PDFchanayireAinda não há avaliações
- 2020 Updated N10-007 Real Exam Questions and AnswersDocumento12 páginas2020 Updated N10-007 Real Exam Questions and AnswersTango CashAinda não há avaliações
- CANON Pixma Ip3000 Service ManualDocumento24 páginasCANON Pixma Ip3000 Service Manualsollers100% (26)
- Fire of Kundalini FDocumento12 páginasFire of Kundalini Fbharath_mv7Ainda não há avaliações
- Market Feasibility Report-OfCDocumento11 páginasMarket Feasibility Report-OfCShashank SaxenaAinda não há avaliações
- Sic Her He Its Hand BuchDocumento85 páginasSic Her He Its Hand BuchgnkameshAinda não há avaliações
- Daniel IngramDocumento392 páginasDaniel Ingramrstarter_og7815Ainda não há avaliações
- Basic ExercisesDocumento17 páginasBasic Exercisesbharath_mv7100% (1)
- Card Captor Sakura Clow Card Fortune Book 4063342980Documento1 páginaCard Captor Sakura Clow Card Fortune Book 4063342980Putu Wisma0% (1)
- 1 - Pdfsam - Network Analysis Architecture and Design (Morgan Kaufmann) (3EdJun2007) PDFDocumento11 páginas1 - Pdfsam - Network Analysis Architecture and Design (Morgan Kaufmann) (3EdJun2007) PDFbharath_mv70% (1)
- LTE Protocol Stack TestingDocumento2 páginasLTE Protocol Stack Testingmohdwajid200950% (4)
- LTEDocumento12 páginasLTEsushiAinda não há avaliações
- Cisco CDocumento701 páginasCisco Ccborn99Ainda não há avaliações
- Dell Guide To Server BasicsDocumento11 páginasDell Guide To Server Basicsswaroop24x7Ainda não há avaliações
- Digital Signage Software EZposter 2018Documento15 páginasDigital Signage Software EZposter 2018Najib HabebAinda não há avaliações
- Lista Firme ConstantaDocumento92 páginasLista Firme ConstantaalinaAinda não há avaliações
- Nps EB6 BGFDGDocumento98 páginasNps EB6 BGFDGbharathvennaAinda não há avaliações
- Nps EB6 BGFDGDocumento98 páginasNps EB6 BGFDGbharathvennaAinda não há avaliações
- What Are Past Participles - SelectionDocumento2 páginasWhat Are Past Participles - Selectionbharath_mv7Ainda não há avaliações
- Meditation On Mind and Feeling AsdfDocumento26 páginasMeditation On Mind and Feeling Asdfbharath_mv7Ainda não há avaliações
- Kriya Yoga: Synthesis of A Personal Experience Pt.1Documento76 páginasKriya Yoga: Synthesis of A Personal Experience Pt.1ludelanesAinda não há avaliações
- Gray, David - Eating The Heart of The Brahmin - Representations of Alterity and The Formation of Identity in Tantric Buddhist DiscourseDocumento25 páginasGray, David - Eating The Heart of The Brahmin - Representations of Alterity and The Formation of Identity in Tantric Buddhist Discoursebharath_mv7Ainda não há avaliações
- Finding Information About Mail Servers at Yale: TCP/IP Professional Reference GuideDocumento11 páginasFinding Information About Mail Servers at Yale: TCP/IP Professional Reference Guidebharath_mv7Ainda não há avaliações
- The Adolescent Brain Prepress Proof (1) AdfDocumento56 páginasThe Adolescent Brain Prepress Proof (1) Adfbharath_mv7100% (1)
- 122 Pdfsam TCPIP Professional Reference Guide TQW DarksidergDocumento11 páginas122 Pdfsam TCPIP Professional Reference Guide TQW Darksidergbharath_mv7Ainda não há avaliações
- Common Grammar Mistakes DFSDDocumento3 páginasCommon Grammar Mistakes DFSDbharath_mv7Ainda não há avaliações
- 210 Pdfsam TCPIP Professional Reference Guide TQW DarksidergDocumento11 páginas210 Pdfsam TCPIP Professional Reference Guide TQW Darksidergbharath_mv7Ainda não há avaliações
- 221 Pdfsam TCPIP Professional Reference Guide TQW DarksidergDocumento11 páginas221 Pdfsam TCPIP Professional Reference Guide TQW Darksidergbharath_mv7Ainda não há avaliações
- 232 Pdfsam TCPIP Professional Reference Guide TQW DarksidergDocumento11 páginas232 Pdfsam TCPIP Professional Reference Guide TQW Darksidergbharath_mv7Ainda não há avaliações
- 122 Pdfsam TCPIP Professional Reference Guide TQW DarksidergDocumento11 páginas122 Pdfsam TCPIP Professional Reference Guide TQW Darksidergbharath_mv7Ainda não há avaliações
- 188 Pdfsam TCPIP Professional Reference Guide TQW DarksidergDocumento11 páginas188 Pdfsam TCPIP Professional Reference Guide TQW Darksidergbharath_mv7Ainda não há avaliações
- 45 Pdfsam TCPIP Professional Reference Guide TQW DarksidergDocumento11 páginas45 Pdfsam TCPIP Professional Reference Guide TQW Darksidergbharath_mv7Ainda não há avaliações
- 100 Pdfsam TCPIP Professional Reference Guide TQW DarksidergDocumento11 páginas100 Pdfsam TCPIP Professional Reference Guide TQW Darksidergbharath_mv7Ainda não há avaliações
- 78 Pdfsam TCPIP Professional Reference Guide TQW DarksidergDocumento11 páginas78 Pdfsam TCPIP Professional Reference Guide TQW Darksidergbharath_mv7Ainda não há avaliações
- 144 Pdfsam TCPIP Professional Reference Guide TQW DarksidergDocumento11 páginas144 Pdfsam TCPIP Professional Reference Guide TQW Darksidergbharath_mv7Ainda não há avaliações
- 100 Pdfsam TCPIP Professional Reference Guide TQW DarksidergDocumento11 páginas100 Pdfsam TCPIP Professional Reference Guide TQW Darksidergbharath_mv7Ainda não há avaliações
- 122 Pdfsam TCPIP Professional Reference Guide TQW DarksidergDocumento11 páginas122 Pdfsam TCPIP Professional Reference Guide TQW Darksidergbharath_mv7Ainda não há avaliações
- Li Fi TechnologyDocumento15 páginasLi Fi TechnologyDambu RAinda não há avaliações
- TNS Lect 03 3Documento43 páginasTNS Lect 03 3Aziz Maqtri100% (1)
- Canon PIXMA MP830 Service ManualDocumento85 páginasCanon PIXMA MP830 Service Manualxx2442Ainda não há avaliações
- Project Proposal Eel 5718 - Computer CommunicationDocumento1 páginaProject Proposal Eel 5718 - Computer CommunicationnrjpoddarAinda não há avaliações
- Excel Crossword PuzzleDocumento5 páginasExcel Crossword PuzzlesaeedAinda não há avaliações
- F2008 Instruction Manual English - 131 AmadaDocumento68 páginasF2008 Instruction Manual English - 131 AmadaJuanJo ToGoAinda não há avaliações
- KDL 46W2000Documento109 páginasKDL 46W2000eselecAinda não há avaliações
- DVD Karaoke System Dks-6100Documento13 páginasDVD Karaoke System Dks-6100dungAinda não há avaliações
- Cisco 2621 Gateway-PBX Interoperability: Ericsson MD-110 With T1 PRI SignalingDocumento11 páginasCisco 2621 Gateway-PBX Interoperability: Ericsson MD-110 With T1 PRI Signalinginr0000zhaAinda não há avaliações
- WANemv11 Setup GuideDocumento12 páginasWANemv11 Setup GuideZul HafizAinda não há avaliações
- Oscar 2020 - Por @heyshazamDocumento12 páginasOscar 2020 - Por @heyshazamTatiana OliveiraAinda não há avaliações
- Communication System by Simon Haykin 3rd Edition PDFDocumento2 páginasCommunication System by Simon Haykin 3rd Edition PDFKaren100% (1)
- Sabrent USB-SND8 - Manual PDFDocumento12 páginasSabrent USB-SND8 - Manual PDFMatias OrtizAinda não há avaliações
- Ricoh Aficio 2020 DDocumento6 páginasRicoh Aficio 2020 DlattimroAinda não há avaliações
- Networked Wireless Meter ReadingDocumento20 páginasNetworked Wireless Meter ReadingChinchu SasiAinda não há avaliações
- List of ZX Spectrum Clones - Wikipedia, The Free EncyclopediaDocumento12 páginasList of ZX Spectrum Clones - Wikipedia, The Free EncyclopediaJUAN ALVAREZ QUEZADAAinda não há avaliações
- Huawei FusionCloud Desktop Solution Overview Presentation (For Governments)Documento56 páginasHuawei FusionCloud Desktop Solution Overview Presentation (For Governments)HUMANMANAinda não há avaliações
- Livestream Studio ManualDocumento42 páginasLivestream Studio ManualTeleQuisqueyacom Saint-Marc HaitiAinda não há avaliações