Escolar Documentos
Profissional Documentos
Cultura Documentos
Power System Security Ebhancement by Phase Shifter Operation
Enviado por
debasishmee5808Direitos autorais
Formatos disponíveis
Compartilhar este documento
Compartilhar ou incorporar documento
Você considera este documento útil?
Este conteúdo é inapropriado?
Denunciar este documentoDireitos autorais:
Formatos disponíveis
Power System Security Ebhancement by Phase Shifter Operation
Enviado por
debasishmee5808Direitos autorais:
Formatos disponíveis
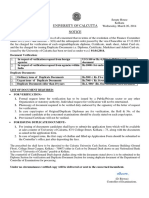
IEEE TRANSACTIONS ON POWER SYSTEMS, VOL. 16, NO.
2, MAY 2001
287
Power System Security Enhancement by OPF with
Phase Shifter
James A. Momoh, Fellow, IEEE, Jizhong Z. Zhu, Senior Member, IEEE, Garfield D. Boswell, and Stephen Hoffman
AbstractThis paper presents an integrated optimal power
flow (OPF) with phase shifter approach to enhance power system
security. The general OPF calculations are hourly based and the
control variables of OPF are continuous. However, the calculations
of phase shifter are daily based, and the variables related to phase
shifter are discrete. Therefore, the general OPF cannot be directly
used to solve this problem. The paper develops the rule-based
OPF with phase shifter scheme to bridge the problems. In order
to effectively alleviate the line overloads, the ranking of phase
shifter locations is conducted based on contingency analysis and
sensitivity analysis. The best phase shifter sites are identified and
selected into rule-based system accordingly. The handshaking
procedure between the adjustment of the selected phase shifters
and OPF calculation is proposed using rule-based method. The
hourly-based OPF problem is solved by the extended quadratic
interior point method. IEEE 30-bus system is used to test the
proposed scheme.
Index TermsLine overloads, optimal power flow, phase shifter,
rule-based method, security, sensitivity analysis.
I. INTRODUCTION
HE PROBLEM of power system security has obtained
much attention in the deregulated power industry. To meet
the load demand in a power system and satisfy the stability and
reliability criteria, either the existing transmission lines must
be utilized more efficiently, or new line(s) should be added to
the system. The latter is often impractical. The reason is that
building a new power line is in many countries, a very time consuming process and sometimes an impossible task, due to environmental problems. Therefore, the first alternative provides
an economically and technically attractive solution to power
system security problem by use of some efficient controls, such
as controllable series capacitors, phase shifters, and load shedding, etc., [1][5]. Several techniques have been proposed in the
past for the adjustment of phase shifter or the adjustment of controllable series capacitor to alleviate line overloads [4], [5].
The main method uses the model of series capacitor or phase
shifter in power flow program without generation rescheduling.
It is possible to alleviate power flow violation and enhance
power system security in an electrical power system by use
of phase shifter without optimal generation rescheduling.
However, it is well known that the phase shifter adjustment
under given contingencies may fail to yield convergence. Thus,
Manuscript received February 10, 2000. This work was supported by Commonwealth Edison, Chicago.
J. A. Momoh, J. Z. Zhu, and G. D. Boswell are with CESaC, Department of
Electrical Engineering, Howard University, Washington, DC 20059 USA.
S. Hoffman is with ComEd, Electric Operations, 1N301 Swift Road, Lombard, IL 60148 USA.
Publisher Item Identifier S 0885-8950(01)03794-4.
optimal power flow (OPF) with phase shifter is a good choice.
The goal of optimal power flow is to determine optimal control
variables and quantities for efficient power system planning and
operation. Several optimization techniques have been proposed
to handle the OPF problem [6][8]. Recently, the research
in OPF such as interior point (IP) using new optimization
techniques, has been gaining wider attention in power system
operation [9], [10]. The interior point method is faster and more
reliable for achieving feasibility and convergence. Due to the
limitation of IP, the model of discrete variable such as phase
shifter has not been investigated in the common OPF.
This paper presents an integrated approach to study the OPF
with phase shifter for removing line overloads. The objective
functions of OPF include minimum line overloads and minimum adjustment of numbers of phase shifters. In order to retain the symmetry of bus, the injection model of phase shifter
used in [1], [2] is adopted in this paper. It is noted that general
OPF calculations are hourly based and the control variables of
OPF are continuous. However, the calculations of phase shifter
are daily based. The control variables associated with the phase
shifter transformers are discrete. Therefore, the general OPF
cannot be directly used to solve this problem. This paper develops the rule-based OPF with phase shifter scheme to bridge
the problems. In order to effectively alleviate the line overloads,
the ranking of phase shifter locations is conducted based on contingency analysis and sensitivity analysis. The sensitivity is defined as the objective function (minimum line overloads) with
respect to the site of phase shifter. The best phase shifter sites are
identified and selected into rule-based system accordingly. The
handshaking procedure between the adjustment of the selected
phase shifters and OPF calculation is proposed using rule-based
method. The hourly-based OPF is solved by extended quadratic
interior point (EQIP) method with improved initial conditions.
The proposed approach is examined using the IEEE 30-bus test
system.
The paper is organized as follows. Section II describes the
model of phase shifter. Section III presents the formulation of
optimal power flow with phase shifters, including the proposed
OPF algorithm and rule-based scheme. In Section IV, the integrated scheme of OPF with phase shifter is illustrated based
on the rule-based method. Section V contains simulation results
followed by conclusions.
II. PHASE SHIFTER MODEL
A phase shifter model can be represented by an equivalent
circuit, which is shown in Fig. 1. It consists of an admittance
08858950/01$10.00 2001 IEEE
288
IEEE TRANSACTIONS ON POWER SYSTEMS, VOL. 16, NO. 2, MAY 2001
for OPF with phase shifter. However, the primary purpose of
installing phase shifter is to remove the line overload. Thus,
the minimal line overload is selected as the primary objective
function in this paper. In addition, since the adjustment numbers of phase shifter are limited in the practical system, the minimal adjustment number of phase shifters is also selected as the
objective function. So this paper focuses on the following two
objective functions.
1) Minimal Line Overloads:
Fig. 1. The circuit diagram of the phase shifter.
(4)
Fig. 2.
Simulation of the presence of the phase shifter.
where
:
in series with an ideal transformer having a complex turns ratio
.
From Fig. 1, network analysis is used to obtain a mathematical model of phase shifter as:
line overload objective function;
the overload power flow on transmission line - at
time stage ;
: transmission limit of line - ;
:
set of overload lines.
2) Minimal Adjustment Numbers of Phase Shifter:
:
(1)
(5)
where
(2)
(3)
Equation (1) shows that the mathematical model of the phase
shifter makes the bus unsymmetrical. In order to make the
bus symmetrical, the phase shifter can be simulated by installing
the additional injections at the terminal buses as shown in Fig. 2.
The additional injections in Fig. 2 can be simplified as follows
[1].
where
:
:
:
:
:
:
:
:
current and real power flow at bus ;
current and real power flow at bus ;
reactive power at bus ;
reactive power at bus ;
complex voltage at bus ;
complex voltage at bus ;
complex turn ratio of the phase shifter;
series admittance of the line .
III. OPF FORMULATION WITH PHASE SHIFTER
where
:
:
:
:
phase shifter adjustment objective function;
the angle of phase shifter transformer ;
priority coefficient of phase shifter;
set of phase shifter transformers.
B. Constraints
In addition to the general linear/nonlinear constraints, the
constraints relating to phase shifter variables such as phase
shifter angle and maximal adjustment numbers should be
included in the OPF formulation with phase shifter. The
candidate constraints are as follows:
Constraint 1: Real power flow equation
Constraint 2: Reactive power flow equation
Constraint 3: Upper and lower limits of real power output of
the generators
Constraint 4: Upper and lower limits of reactive power
output of the generators
Constraint 5: Upper and lower limits of node voltages
Constraint 6: Available transfer capacity of the transmission
lines
Constraint 7: Upper and lower limits of transformer taps
Constraint 8: Upper and lower limits of phase shifter taps
Constraint 9: Maximal adjustment times of phase shifters per
day
Notably, Constraints 8 and 9 are the phase shifter constraints that
were used in the rule-based search technique. And, the limits of
all control and state variables are determined for the specific
system under study.
A. Objective Functions
Due to the installation of phase shifter, the system will have
lots of benefits such as overload release, system loss reduction,
generation cost reduction, and generation adjustment reduction
etc. All these benefits may be selected as objective functions
C. Proposed OPF Algorithm
The above-mentioned OPF model with phase shifter is a nonlinear mathematical programming problem. It can be reduced
by an elimination procedure. The reduction of the OPF model
MOMOH et al.: POWER SYSTEM SECURITY ENHANCEMENT BY OPF WITH PHASE SHIFTER
289
is based on the linearized load flow around base load flow solution for small perturbation. The details refer to the reference
[10]. The reduced OPF model has the format:
(6)
with
(7)
The models (6) and (7) has a quadratic objective function
subject to the linear constraints that satisfy the basic requirements of quadratic interior point (QIP) scheme. Generally,
the effectiveness of interior point methods depends on a good
starting point. The extended quadratic interior point (EQIP)
method with improved initial conditions is presented in this
paper. It features the general starting point (rather than a good
point) and faster convergence. The corresponding calculation
steps are as follows.
S1 given a starting point
S2
S3
S4
S5 if
then go to S10. Otherwise
S7
S8 if
, go to S3.
Otherwise
, go to S3
S9
S10
S11
S12
S13
(where
)
S14
where
S15
(where
is a variable step and its
value is less than 1)
, and go to S11.
Set
, where
is the iteration
End when
counter.
In order to handle Steps 8 and 13, the QUIP use the value
of the phase shifter tap setting that is computed from the rule
base portion of the overall algorithm as specified in the handis frozen when it
shaking procedure. The maximum value of
reaches its maximum value. Otherwise, we use a number within
the fixed length of the phase shifter taps.
D. Sensitivity Analysis
In order to determine the best location for installing phase
shifter, sensitivity analysis is conducted in this paper. The formulation of sensitivity analysis of objective function with respect to phase shifter variable can be expressed as follows.
(8)
where
total line overload before phase shifter is installed;
Fig. 3. OPF with phase shifter using rule-based method.
total line overload after phase shifter is installed;
:
, if power violation is reduced by use of
In (6),
. Obviously, if phase shifter
phase shifter, i.e.,
is not helpful in alleviating line overload, then
.
.
In this case, we define the value of sensitivity
E. Rule-Based OPF with Phase Shifter Scheme
As noted earlier, that the general OPF cannot be directly used
to solve the phase shifter problem. Thus, this paper uses the
rule-based method to bridge the problem. The total structure of
the proposed idea is shown in Fig. 3. In the rule-based system,
the following rules are defined.
Rule 1: If system operates in the normal state without load
change, then none of the existing phase shifters will
change tap.
Rule 2: If system load increases, or system operates in contingency state, then judge:
If no line overload appeared, then none of the existing phase shifters will change tap.
If line overload occurred in system, then go to rule 3
to adjust the tap of some phase shifters.
Rule 3: If phase shifter leads to maximal overload reduce at
time stage , then phase shifter will be recommended
at this time.
Rule 4: If phase shifter and lead to same overload reduce
at time stage , then check the other benefits:
If phase shifter make less generation cost benefit
than phase shifter , then phase shifter will be recommended at this time.
If phase shifter make less system loss benefit than
phase shifter , then phase shifter will be recommended at this time.
Rule 5: If OPF suggest a solution, and RBS confirms that
phase shifter constraints are met, then problem at this
time stage is solved.
Rule 6: If RBS checks OPF solution and OPF solution violates phase shifter constraints, then freeze the corresponding tap of phase shifter.
Rule 7: If RBS checks state of phase shifters and phase
shifter k has a frozen tap, then phase shifter will be
out of service in the subsequent time stages.
290
IEEE TRANSACTIONS ON POWER SYSTEMS, VOL. 16, NO. 2, MAY 2001
Step 1: Assume several contingencies.
Step 2: OPF calculation without phase
shifter for each given contingency from
time step
, first time step).
Step 3: Judge whether OPF is solvable. If
the answer is Yes, there is no need to
use phase shifter. If No, go to step
4.
Step 4: Contingency analysis through
power flow calculation. Check the overload state of lines.
Step 5: Conduct sensitivity analysis
for obtaining a list of phase shifter
ranking according to the amount of releasing the line overload for each phase
shifter. Then decide the corresponding
weighting factor.
Step 6: OPF calculation with the available phase shifter.
Step 7: Use rule base method to check the
operation limitation of phase shifter.
Calculate the operation times
, if the phase shifter
is operated in this time stage.
, freeze
Step 8: If
the corresponding taps of the phase
shifter. That is, this phase shifter
will be out of services in subsequent
time.
Step 9: Check time stages. If
(e.g., 24 hrs), stop. Otherwise,
,
go to step 2.
Fig. 4. Flowchart of the integrated scheme for OPF with phase shifter.
A phase shifter tap is frozen when the number of phase shifter
at time reaches its maximum. The EQIP algorithm
then uses that was fixed or scheduled by the rule-base engine.
IV. INTEGRATED SCHEME OF OPF WITH PHASE SHIFTER
The flowchart of integrated scheme for OPF with phase
shifter can be expressed as Fig. 4. The integrated scheme
consists of interior point model of OPF with phase shifter,
contingency analysis for checking the overloading state of
lines, sensitivity analysis for selecting the sites of phase shifter,
and rule-based system to handshake the adjustment of phase
shifters and OPF calculation.
The solution steps of the integrated algorithm for OPF with
phase shifter are as follows.
Finally, in the search technique of the rule based method used,
the phase shifters are adjusted sequentially and their direction of
adjustments are governed by the impact on the primary objective function of minimal line overload. The engineering rules
are such that the least number of phase shifters are adjusted at
a time, provided that they have the greatest impact in reducing
the line flow overloads. The phase shifter constraints, which are
handled by the rule-based search technique, are adjusted to produces discrete settings and in turn passed on to the EQIP module
of the algorithm.
V. TEST EXAMPLE
For examining the integrated scheme of OPF with phase
shifter, IEEE 30-bus system is tested. The data and parameters
of 30-bus system are taken from reference [7] and the limits of
.
the installed phase shifters were taken as
The total system load of IEEE 30-bus system is 283.4 MW.
The corresponding load scaling factor (LSF) is 1.0. The daily
load demands of IEEE 30-bus system are shown in Fig. 5. In
order to determine the degree of line violations at the line ,
the following performance index is defined in the paper.
(9)
MOMOH et al.: POWER SYSTEM SECURITY ENHANCEMENT BY OPF WITH PHASE SHIFTER
291
TABLE III
RESULTS OF CONTINGENCY ANALYSIS AT THE PEAK LOAD T18
Fig. 5. Daily load curve of IEEE 30-bus system.
TABLE I
TOTAL POWER VIOLATIONS WITHOUT CONTINGENCY
TABLE II
SUMMARY OF CONTINGENCY ANALYSIS
where
: performance index of line overloads;
: the overload flow on transmission line ;
: set of overloaded lines.
Through power flow analysis without contingency for each
time stage, line overloads only appeared at hours 8, 15, 16, 17,
18, and 19, which are peak load periods. The violation amounts
of line flow for each time stage are summarized in Table I.
The line overloads will become more serious if system contingency scenarios are considered. Therefore, OPF with phase
shifter adjustment should be employed for enhancing power
system security.
For the purpose of simulation, the following line contingency
scenarios are given, that is,
,
and
.
Table II is the summary of contingency analysis and the
total power violations for all time stages are shown. It can
be observed from Table II that the line
outage is the
most serious contingency case, where the total line violation is
107.26 MW.
Table III gives the details of contingency calculation under
the peak load (at hour 18).
Fig. 6 shows power violations during the period of peak
) for the given contingency cases. Although the
loads (
Fig. 6.
Power violations at the period of peak loads.
Fig. 7. Contingency analysis result under the worst fault scenario (line L
outage).
contingency ranks for different time stages are not totally the
same, the selected worst contingency case is the same, i.e., line
outage. Fig. 7 gives the detail results of contingency
calculation for all time stages under the worst contingency case
( outage).
292
Fig. 8. Line overload results under the worst fault scenario at the highest load
level.
TABLE IV
RANKING OF PHASE SHIFTER LOCATION BASED ON SENSITIVITY ANALYSIS
(LSF=1.55, OUTAGE LINE L )
IEEE TRANSACTIONS ON POWER SYSTEMS, VOL. 16, NO. 2, MAY 2001
Fig. 9. Object function value with and without phase shifter (Load level
LSF = 1:55; Outage line L ).
TABLE V
RESULTS OF PHASE SHIFTER ADJUSTMENT
before and after phase shifter control action, respectively. This
information will be stored in the rule-based system.
Based on sensitivity analysis and contingency analysis for the
worst fault scenario, we can make the rules to determine the
priority of adjusting the selected phase shifters. Table V lists
the results of phase shifter adjustments during the operation period (24 hours) based on optimal power flow. Simulation results
show that all the line overloads are removed due to use of phase
shifters.
VI. CONCLUSION
Fig. 8 shows the line overload results under the peak load (at
hour 18) and the worst contingency case ( outage). In
order to determine the priority of phase shifters, the sensitivity
analysis of phase shifters is conducted under the peak load and
the worst contingency case. Simulation results show that system
security will be greatly enhanced if the phase shifter is installed
at location
,
respectively.
For the specified worst contingency, it can be seen from
Table IV and Fig. 9 that the best three locations for installing
and
phase shifter are
.
represent the value of the primary objective function value
This paper proposes an integrated approach of optimal power
flow with phase shifter to enhance power system security. Due
to the fact that the general OPF cannot be directly used to solve
the discrete phase shifter variables, this paper develops the rulebased OPF with phase shifter scheme to bridge the problem.
Several tests of contingency cases are performed to check the
overload states of lines. In order to effectively alleviate the line
overloads, the ranking of phase shifter locations is conducted
based on sensitivity analysis. The best phase shifter sites are
identified and selected into rule-based system accordingly. The
handshaking procedure between the adjustment of the selected
phase shifters and OPF calculation is proposed using rule-based
method. Simulation results show that the proposed integrated
OPF with phase shifter scheme is effective.
Finally, by using the EQIP algorithm and the rule-base
method as a search technique for selecting the optimum phase
shifter operating tap size, the computational time is reduced
MOMOH et al.: POWER SYSTEM SECURITY ENHANCEMENT BY OPF WITH PHASE SHIFTER
by order 8 : 1 when compared against other optimization
techniques. The simulations were done on a VAX System with
PC interface capabilities.
REFERENCES
[1] N. Srinivasan, K. S. Prakaesa, and S. S. Venkata, On-line computation of phase shifter distribution factors and line load alleviation, IEEE
Trans. on Power Systems, vol. PAS-104, no. 7, pp. 16561662, 1985.
[2] B. Stott and E. Hobson, Power system security control calculations
using linear programmingPart I, IEEE Trans. on Power Systems, vol.
PAS-97, pp. 17131719, 1978.
[3] R. Baldick and E. Kahn, Contract paths, phase shifters, and efficient
electricity trade, IEEE Trans. on Power Systems, vol. 12, no. 2, pp.
749755, 1997.
[4] M. R. Iravani and D. Maratukulam, Review of semiconductor-controlled (static) phase shifters for power system applications, IEEE
Trans. on Power Systems, vol. 9, no. 4, pp. 18331839, 1994.
[5] T. K. P. Medicherla, R. Billinton, and M. S. Sachdev, Generation
rescheduling and load shedding to alleviate line overloadsAnalysis,
IEEE Trans. on Power Systems, vol. PAS-98, pp. 18761884, 1979.
[6] A. D. Papalexopoulos, C. F. Imparato, and F. F. Wu, Large scale optimal power flow: Effects of initialization decoupling and discretization, IEEE Trans. on Power Systems, vol. 4, pp. 748759, 1989.
[7] O. Alsac and B. Sttot, Optimal power flow with steady-state security,
IEEE Trans. on Power System, vol. 93, pp. 745751, 1974.
[8] J. Z. Zhu and G. Y. Xu, A new real power economic dispatch method
with security, Electric Power Systems Research, vol. 25, no. 1, pp. 915,
1992.
[9] S. Granville, J. C. O. Mello, and A. C. G. Melo, Application of interior point methods to power flow unsolvability, IEEE Trans. on Power
System, vol. 11, pp. 10961103, 1996.
[10] J. A. Momoh, L. G. Dias, S. X. Guo, and R. A. Adapa, Economic operation and planning of multi-area interconnected power system, IEEE
Trans. on Power System, vol. 10, pp. 10441051, 1995.
293
James A. Momoh (M76SM89F99) received the B.S.E.E. degree (1975)
from Howard University, the M.S.E.E. degree (1976) from Camegie Mellon
University, the M.S. degree (1980) in systems engineering from the University of Pennsylvania and the Ph.D. degree (1983) in electrical engineering from
Howard University. Professor Momoh is Chair of the Electrical Engineering Department at Howard University and also the Director of the Center for Energy
System and Controls. His current research activities are concentrated in stability
analysis, system security and expert systems design for utility firms and government agencies. In 1987, he received a National Science Foundation Presidential
Young Investigator Award.
Jizhong Zhu (SM98) received the B.S.E.E. (1985), M.S.E.E. (1987) and Ph.D.
degrees (1990) from Chongqing University, P.R. China. He is a Professor at
Chongqing University, China. He was a Royal Society Fellow and Visiting Research Fellow at Brunel University in the UK during 19951996. He was a Postdoctoral Fellow at National University of Singapore, and is currently a Research
Fellow at Howard University. His research interest is in the analysis, operation,
planning and control of power systems.
Garfield Boswell received the B.S.E.E. degree (1994) from University of the
West Indies (UWI). He was a Teacher at Belair High School during 19941996
and is a Private Contracting Engineer for WelloMed, Ltd. in Jamaica. He is
currently Graduate Student at Howard University. His research interests lie in
the area of power system operation, planning and design.
Stephen Hoffman received the B.S.E.E. degree (1991) from the University of
Missouri-Rolla, and the M.S.E.E. degree (1993) from Purdue University. He
is employed with ComEd in the Electric Operations Department. Areas of expertise and experience include power system operations, on-line transmission
system security applications programs, frequency bias measurement, and automatic generation control. Extensive contributions were made to the development
of the new NREC Control Performance Standard for AGC, and in its implementation at ComEd.
Você também pode gostar
- Investigation of the Usefulness of the PowerWorld Simulator Program: Developed by "Glover, Overbye & Sarma" in the Solution of Power System ProblemsNo EverandInvestigation of the Usefulness of the PowerWorld Simulator Program: Developed by "Glover, Overbye & Sarma" in the Solution of Power System ProblemsAinda não há avaliações
- Simulation of Some Power System, Control System and Power Electronics Case Studies Using Matlab and PowerWorld SimulatorNo EverandSimulation of Some Power System, Control System and Power Electronics Case Studies Using Matlab and PowerWorld SimulatorAinda não há avaliações
- Optimization Methods in Power Systems Application and PerspectivesDocumento6 páginasOptimization Methods in Power Systems Application and Perspectiveshemanta57jenaAinda não há avaliações
- Model-Based H Control of A UPQCDocumento12 páginasModel-Based H Control of A UPQCrakheep123Ainda não há avaliações
- Current Distribution Control Design For Paralleled DC/DC Converters Using Sliding-Mode ControlDocumento10 páginasCurrent Distribution Control Design For Paralleled DC/DC Converters Using Sliding-Mode ControlAnushya RavikumarAinda não há avaliações
- Optimal Power Flow Sensitivity CalculationDocumento8 páginasOptimal Power Flow Sensitivity CalculationEléctrico IngenieríaAinda não há avaliações
- Neural Network Control of Grid-Connected Fuel Cell Plants For Enhancement of Power QualityDocumento7 páginasNeural Network Control of Grid-Connected Fuel Cell Plants For Enhancement of Power Qualityashikhmd4467Ainda não há avaliações
- 1 s2.0 S0019057813000608 Main PDFDocumento6 páginas1 s2.0 S0019057813000608 Main PDFsethukumarkAinda não há avaliações
- Control Techniques For Active Power Filters RevisedDocumento38 páginasControl Techniques For Active Power Filters RevisedBAMMIDI APPALANAIDUAinda não há avaliações
- A Benchmark System For Digital Time-Domain Simulation of An Active Power FilterDocumento8 páginasA Benchmark System For Digital Time-Domain Simulation of An Active Power FilterAndreeaAinda não há avaliações
- Figure 1. Traditional Interleaved Configuration Using A Flyback TopologyDocumento7 páginasFigure 1. Traditional Interleaved Configuration Using A Flyback TopologyaldyAinda não há avaliações
- Power Flow and Dynamic Optimal Power Flow Including Wind FarmsDocumento6 páginasPower Flow and Dynamic Optimal Power Flow Including Wind FarmsMed Nassim KraimiaAinda não há avaliações
- S N SinghDocumento5 páginasS N Singhswapna44Ainda não há avaliações
- A Novel Strategy For Location and Optimum Tuning of Unified Power Flow Controller For Loss Minimization Via Firefly AlgorithmDocumento21 páginasA Novel Strategy For Location and Optimum Tuning of Unified Power Flow Controller For Loss Minimization Via Firefly AlgorithmRavi Kumar BandarulankaAinda não há avaliações
- Uni®ed Power Ow Controller (UPFC) Model in The Framework of Interior Point Based Active and Reactive OPF ProcedureDocumento7 páginasUni®ed Power Ow Controller (UPFC) Model in The Framework of Interior Point Based Active and Reactive OPF ProcedureChaibHabibAinda não há avaliações
- A Single-Stage Three-Phase Grid-Connected Photovoltaic System With Modified MPPT Method and Reactive Power CompensationDocumento6 páginasA Single-Stage Three-Phase Grid-Connected Photovoltaic System With Modified MPPT Method and Reactive Power Compensationsandeepbabu28Ainda não há avaliações
- GioihantinhdudoantaiDocumento10 páginasGioihantinhdudoantaiHung CaoAinda não há avaliações
- An Optimal Model Predictive Control Method For FivDocumento10 páginasAn Optimal Model Predictive Control Method For FivXuân Phú PhạmAinda não há avaliações
- Based Power Tracking For Nonlinear PV SourcesDocumento8 páginasBased Power Tracking For Nonlinear PV SourcesRaveendhra IitrAinda não há avaliações
- Accepted Manuscript: Applied Soft ComputingDocumento24 páginasAccepted Manuscript: Applied Soft ComputingMD AbdullahAinda não há avaliações
- A Simple Single-Input-Single-Output (SISO) ModelDocumento12 páginasA Simple Single-Input-Single-Output (SISO) ModelVisu TamilAinda não há avaliações
- Passivity-Based Control For Charging Batteries in Photovoltaic SystemsDocumento7 páginasPassivity-Based Control For Charging Batteries in Photovoltaic SystemsValentim ErnandesAinda não há avaliações
- A Closed-Loop Selective Harmonic Compensation For Active FiltersDocumento9 páginasA Closed-Loop Selective Harmonic Compensation For Active FiltersLê TêAinda não há avaliações
- Función Real Base PS Feb 07Documento9 páginasFunción Real Base PS Feb 07freddyriveraAinda não há avaliações
- Load Flow Analysis For A 220KV Line - Case StudyDocumento12 páginasLoad Flow Analysis For A 220KV Line - Case StudyNmg KumarAinda não há avaliações
- A Simple Single-Input-Single-Output (SISO) Model For A Three-Phase PWM RectifierDocumento12 páginasA Simple Single-Input-Single-Output (SISO) Model For A Three-Phase PWM RectifierbywhuAinda não há avaliações
- Development of A MATLABSimulink Model of A Single-Phase Grid-Connected Photovoltaic System-IwQDocumento8 páginasDevelopment of A MATLABSimulink Model of A Single-Phase Grid-Connected Photovoltaic System-IwQSaddam HussainAinda não há avaliações
- 0 PepeDocumento7 páginas0 PepeVaisakh_k5683Ainda não há avaliações
- Adjustable Matched Virtual: Photovoltaic PointDocumento5 páginasAdjustable Matched Virtual: Photovoltaic PointChenchu TnvAinda não há avaliações
- PSCAD EMTDC, FuzzyControl, HVDC Transmission, VoltageDependentCurrentOrderLimit VDCOLDocumento9 páginasPSCAD EMTDC, FuzzyControl, HVDC Transmission, VoltageDependentCurrentOrderLimit VDCOLKurniawan Indra LeksanaAinda não há avaliações
- A Novel Approach To Optimal Allocation of SVC Using Genetic Algorithms and Continuation Power FlowDocumento5 páginasA Novel Approach To Optimal Allocation of SVC Using Genetic Algorithms and Continuation Power FlowMadalena TrindadeAinda não há avaliações
- Extended Kalman Filter Tuning in Sensorless PMSM DrivesDocumento6 páginasExtended Kalman Filter Tuning in Sensorless PMSM Drivesbadro1980Ainda não há avaliações
- A Stabilizing, High-Performance Controller For Input Series-Output Parallel ConvertersDocumento12 páginasA Stabilizing, High-Performance Controller For Input Series-Output Parallel ConvertersDipanjan DasAinda não há avaliações
- Adaptive Control For Low-Frequency Power OscillationsDocumento6 páginasAdaptive Control For Low-Frequency Power OscillationsAJER JOURNALAinda não há avaliações
- Average and Small-Signal Modeling of Self-Oscillating Flyback Converter With Applied Switching DelayDocumento8 páginasAverage and Small-Signal Modeling of Self-Oscillating Flyback Converter With Applied Switching DelayMohamed HaddadAinda não há avaliações
- Maximizing Power System Loadability by Optimal Allocation of SVC Using Mixed Integer Linear ProgrammingDocumento7 páginasMaximizing Power System Loadability by Optimal Allocation of SVC Using Mixed Integer Linear ProgrammingMohamed MansourAinda não há avaliações
- Variable Perturbation Size Adaptive P&O MPPT Algorithm For Sudden Changes in IrradianceDocumento11 páginasVariable Perturbation Size Adaptive P&O MPPT Algorithm For Sudden Changes in IrradianceRoberto Alejandro Patiño HaroAinda não há avaliações
- Thu KaramDocumento11 páginasThu KaramSumit VermaAinda não há avaliações
- Performance of A Simple Mixed-Signal Controller of Shunt Active Power Filter Using Ota-Based CircuitDocumento6 páginasPerformance of A Simple Mixed-Signal Controller of Shunt Active Power Filter Using Ota-Based CircuitShivam AgarwalAinda não há avaliações
- UPFC Control Based On New IP Type Controller: Mojtaba Shirvani, Babak Keyvani, Mostafa Abdollahi and Ahmad MemaripourDocumento8 páginasUPFC Control Based On New IP Type Controller: Mojtaba Shirvani, Babak Keyvani, Mostafa Abdollahi and Ahmad MemaripourMmillion AlemayehuAinda não há avaliações
- State of The Art PWM Techniques A Critical EvaluationDocumento10 páginasState of The Art PWM Techniques A Critical EvaluationMilton SepúlvedaAinda não há avaliações
- An Improved Particle Swarm OptimizationDocumento12 páginasAn Improved Particle Swarm OptimizationVisu TamilAinda não há avaliações
- High Precision Position Control of Electro-Hydraulic Servo SystemDocumento10 páginasHigh Precision Position Control of Electro-Hydraulic Servo Systemamin342Ainda não há avaliações
- Control of A Single-Stage Three-Phase Boost Power Factor Correction RectifierDocumento6 páginasControl of A Single-Stage Three-Phase Boost Power Factor Correction RectifierGoriparthi SambasievaraavAinda não há avaliações
- PUCDocumento13 páginasPUCMohd Mohsin KhanAinda não há avaliações
- List of SymbolsDocumento30 páginasList of Symbolskmd_venkatsubbuAinda não há avaliações
- European Journal of Electrical Engineering: Received: 5 June 2020 Accepted: 16 September 2020Documento12 páginasEuropean Journal of Electrical Engineering: Received: 5 June 2020 Accepted: 16 September 2020Dileep VarmaAinda não há avaliações
- Both Turkish Journal TemplateDocumento9 páginasBoth Turkish Journal TemplateSiva ForeviewAinda não há avaliações
- Robust Power System Stabilizer Design For An Industrial Power System in Taiwan Using Linear Matrix Inequality TechniquesDocumento6 páginasRobust Power System Stabilizer Design For An Industrial Power System in Taiwan Using Linear Matrix Inequality TechniquesDiego Martinez AranedaAinda não há avaliações
- Space-Vector Modulation in A Two-Phase Induction Motor Drive For Constant-Power OperationDocumento8 páginasSpace-Vector Modulation in A Two-Phase Induction Motor Drive For Constant-Power OperationinfodotzAinda não há avaliações
- Control H BridgeDocumento5 páginasControl H BridgeFahad Al-shammeriAinda não há avaliações
- An Approach To Fault-Tolerant Three-Phase Matrix Converter DrivesDocumento9 páginasAn Approach To Fault-Tolerant Three-Phase Matrix Converter DrivesSherif M. DabourAinda não há avaliações
- Hysteresis Model Predictive Control For High-Power Grid-Connected Inverters With Output LCL FilterDocumento11 páginasHysteresis Model Predictive Control For High-Power Grid-Connected Inverters With Output LCL FilterDaniel PGAinda não há avaliações
- Mitigation of Lower Order Harmonics in A Grid-Connected Single-Phase PV InverterDocumento14 páginasMitigation of Lower Order Harmonics in A Grid-Connected Single-Phase PV Invertersandeepbabu28Ainda não há avaliações
- Evaluation of IEEE 57 Bus System For Optimal Power Flow AnalysisDocumento5 páginasEvaluation of IEEE 57 Bus System For Optimal Power Flow AnalysisAnkur MaheshwariAinda não há avaliações
- IEEE Energy Harvesting VibrationDocumento6 páginasIEEE Energy Harvesting VibrationCarlo ScocciaAinda não há avaliações
- 6open Circuit Fault Tolerance Method For Three Level Hybrid Active Neutral Point Clamped ConvertersDocumento23 páginas6open Circuit Fault Tolerance Method For Three Level Hybrid Active Neutral Point Clamped Convertersyasin bayatAinda não há avaliações
- An Integrated Control Algorithm For A Single-Stage PV Pumping System Using An Open-End Winding Induction MotorDocumento10 páginasAn Integrated Control Algorithm For A Single-Stage PV Pumping System Using An Open-End Winding Induction MotorHashim KhanAinda não há avaliações
- Doubly Fed Induction Generator Using Back To Back PWM Converters and Its Application To Variable-Speed Wind-Energy GenerationDocumento11 páginasDoubly Fed Induction Generator Using Back To Back PWM Converters and Its Application To Variable-Speed Wind-Energy GenerationVally ZazaAinda não há avaliações
- Power Electronics Applied to Industrial Systems and Transports, Volume 3: Switching Power SuppliesNo EverandPower Electronics Applied to Industrial Systems and Transports, Volume 3: Switching Power SuppliesAinda não há avaliações
- nRF24L01P Product Specification 1 0Documento78 páginasnRF24L01P Product Specification 1 0CaelumBlimpAinda não há avaliações
- RID 1 ModrobDocumento4 páginasRID 1 ModrobbalakaleesAinda não há avaliações
- Adjunct 2Documento5 páginasAdjunct 2debasishmee5808Ainda não há avaliações
- Extramural Funding2012-13Documento2 páginasExtramural Funding2012-13debasishmee5808Ainda não há avaliações
- TrademarksDocumento1 páginaTrademarksDhyan SwaroopAinda não há avaliações
- RID 1 ModrobDocumento6 páginasRID 1 Modrobdebasishmee5808Ainda não há avaliações
- Bhimbra-Generalized Theory Electrical MachinesDocumento10 páginasBhimbra-Generalized Theory Electrical Machinesdebasishmee5808Ainda não há avaliações
- 10 1109@91 481843Documento12 páginas10 1109@91 481843debasishmee5808Ainda não há avaliações
- Control SystemDocumento22 páginasControl SystemKamran RazaAinda não há avaliações
- AssignmentsDocumento11 páginasAssignmentsdebasishmee5808Ainda não há avaliações
- Adaptive Control of Linearizable Systems: Fully-StateDocumento9 páginasAdaptive Control of Linearizable Systems: Fully-Statedebasishmee5808Ainda não há avaliações
- Sophus 3Documento1 páginaSophus 3debasishmee5808Ainda não há avaliações
- Electromagnetic Field TheoryDocumento3 páginasElectromagnetic Field Theorydebasishmee5808Ainda não há avaliações
- T Year B.tech Sylla1sbus Revised 18.08.10Documento33 páginasT Year B.tech Sylla1sbus Revised 18.08.10Manoj KarmakarAinda não há avaliações
- Lec 1Documento18 páginasLec 1cavanzasAinda não há avaliações
- AssignmentsDocumento11 páginasAssignmentsdebasishmee5808Ainda não há avaliações
- Duplicate Doc Diploma CertiDocumento1 páginaDuplicate Doc Diploma Certidebasishmee5808Ainda não há avaliações
- Control System - I: Weekly Lesson PlanDocumento5 páginasControl System - I: Weekly Lesson Plandebasishmee5808Ainda não há avaliações
- 2 14 24Documento11 páginas2 14 24debasishmee5808Ainda não há avaliações
- Book ListDocumento6 páginasBook Listdebasishmee58080% (1)
- Introduction To Nba 16 NovDocumento32 páginasIntroduction To Nba 16 Novdebasishmee5808Ainda não há avaliações
- Lec 2Documento25 páginasLec 2debasishmee5808Ainda não há avaliações
- Best Practices of Report Writing Based On Study of Reports: Venue: India Habitat Centre, New DelhiDocumento24 páginasBest Practices of Report Writing Based On Study of Reports: Venue: India Habitat Centre, New Delhidebasishmee5808Ainda não há avaliações
- Graphical AbstractDocumento2 páginasGraphical Abstractdebasishmee5808Ainda não há avaliações
- Syllabus For B.Tech (Electrical Engineering) Up To Fourth YearDocumento67 páginasSyllabus For B.Tech (Electrical Engineering) Up To Fourth YearDr. Kaushik MandalAinda não há avaliações
- Lec 1Documento18 páginasLec 1cavanzasAinda não há avaliações
- Lec 2Documento25 páginasLec 2debasishmee5808Ainda não há avaliações
- Time ManagementDocumento19 páginasTime ManagementShyam_Nair_9667Ainda não há avaliações
- Comparison Between Integer Order and Fractional Order ControllersDocumento6 páginasComparison Between Integer Order and Fractional Order Controllersdebasishmee5808Ainda não há avaliações
- Evaluation of Graduate Students Employability From Employer Perspective: Review of The LiteratureDocumento6 páginasEvaluation of Graduate Students Employability From Employer Perspective: Review of The LiteraturerizkiAinda não há avaliações
- Joist Size ScheduleDocumento1 páginaJoist Size Schedulecaliangel1Ainda não há avaliações
- MSE Walls For Support of Highway BridgesDocumento28 páginasMSE Walls For Support of Highway Bridgestalaati50% (2)
- Computer Science & Engineering: An International Journal (CSEIJ)Documento2 páginasComputer Science & Engineering: An International Journal (CSEIJ)cseijAinda não há avaliações
- CV Abishek 18.12.2021Documento6 páginasCV Abishek 18.12.2021Krishnaveni PenkiAinda não há avaliações
- Developing A Structural Design Method For Pervious Concrete PavementDocumento20 páginasDeveloping A Structural Design Method For Pervious Concrete PavementMarcelo HenriqueAinda não há avaliações
- 019 Atec Cavalca Custody Transfer Metering System For Natural Gas Refinery ApplicationDocumento24 páginas019 Atec Cavalca Custody Transfer Metering System For Natural Gas Refinery ApplicationSugeng SAinda não há avaliações
- 26 05 43 Underground Ducts and Raceways For Electrical SystemsDocumento7 páginas26 05 43 Underground Ducts and Raceways For Electrical SystemsjopaypagasAinda não há avaliações
- PVP2014-28958 Writing and Reviewing FEA Reports Under ASME Div 1 and 2 Design PDFDocumento5 páginasPVP2014-28958 Writing and Reviewing FEA Reports Under ASME Div 1 and 2 Design PDFmatteo_1234Ainda não há avaliações
- What's Next After 12thDocumento5 páginasWhat's Next After 12thriyanshuAinda não há avaliações
- NYSDOT Bridge Manual US 2017Documento595 páginasNYSDOT Bridge Manual US 2017Ayoub Zekraoui100% (1)
- Engagement Contract PDFDocumento6 páginasEngagement Contract PDFRyan De Vera PagalAinda não há avaliações
- ISO 9001 CertifiedDocumento7 páginasISO 9001 Certifiedselva mechAinda não há avaliações
- Concrete Slab TypesDocumento6 páginasConcrete Slab TypesMukovhe MuvhaliAinda não há avaliações
- Free Download Here: Besavilla Engineering Mathematics PDFDocumento2 páginasFree Download Here: Besavilla Engineering Mathematics PDFMhorien MacatangayAinda não há avaliações
- Comparison ChartDocumento9 páginasComparison Chartfreanne_0527Ainda não há avaliações
- Transportation Engineering - I: Introduction To Bridge EngineeringDocumento33 páginasTransportation Engineering - I: Introduction To Bridge Engineeringmit rami0% (1)
- Writing Software Requirements SpecificationsDocumento16 páginasWriting Software Requirements Specificationskicha0230Ainda não há avaliações
- Computer Applications in TextilesDocumento2 páginasComputer Applications in Textilesnatarajan1234Ainda não há avaliações
- International Conference On Information, Signal and Communication (ICISC-2011)Documento2 páginasInternational Conference On Information, Signal and Communication (ICISC-2011)Renu AroraAinda não há avaliações
- AcronymsDocumento3 páginasAcronymsNestor CzerwackiAinda não há avaliações
- Heritage Art Cafe - Case Study PDFDocumento7 páginasHeritage Art Cafe - Case Study PDFSreelakme100% (2)
- HVAC Rules of ThumbDocumento8 páginasHVAC Rules of Thumbsam7sAinda não há avaliações
- Btech 4th Year Me Pesit Batch 2014-18Documento25 páginasBtech 4th Year Me Pesit Batch 2014-18api-294538209Ainda não há avaliações
- Lesson 1 - Basic Concept of DesignDocumento32 páginasLesson 1 - Basic Concept of DesignSithara BandaraAinda não há avaliações
- Reinforced Concrete Design On ACI - Part 1 PDFDocumento45 páginasReinforced Concrete Design On ACI - Part 1 PDFshahrol905Ainda não há avaliações
- Crane Control and Automation: Global SolutionsDocumento32 páginasCrane Control and Automation: Global SolutionsstoneminerAinda não há avaliações
- Triggering CreativityDocumento21 páginasTriggering CreativityedAinda não há avaliações
- Nonlinear Dynamic AnalysisDocumento9 páginasNonlinear Dynamic AnalysistrabajosicAinda não há avaliações
- All India Merchant Navy Entrance ExamDocumento2 páginasAll India Merchant Navy Entrance ExamRekha Abhyankar50% (2)