Escolar Documentos
Profissional Documentos
Cultura Documentos
Final 4
Enviado por
Aek Benabadja0 notas0% acharam este documento útil (0 voto)
23 visualizações5 páginasCCNA 4 Final Exam Answers -2014. Deliberately misspell words when creating passwords. Create passwords that are at least 8 characters in length.
Descrição original:
Título original
final 4
Direitos autorais
© © All Rights Reserved
Formatos disponíveis
TXT, PDF, TXT ou leia online no Scribd
Compartilhar este documento
Compartilhar ou incorporar documento
Você considera este documento útil?
Este conteúdo é inapropriado?
Denunciar este documentoCCNA 4 Final Exam Answers -2014. Deliberately misspell words when creating passwords. Create passwords that are at least 8 characters in length.
Direitos autorais:
© All Rights Reserved
Formatos disponíveis
Baixe no formato TXT, PDF, TXT ou leia online no Scribd
0 notas0% acharam este documento útil (0 voto)
23 visualizações5 páginasFinal 4
Enviado por
Aek BenabadjaCCNA 4 Final Exam Answers -2014. Deliberately misspell words when creating passwords. Create passwords that are at least 8 characters in length.
Direitos autorais:
© All Rights Reserved
Formatos disponíveis
Baixe no formato TXT, PDF, TXT ou leia online no Scribd
Você está na página 1de 5
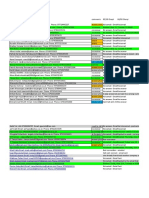
CCNA 4 Final Exam Answers -2014
1. What functionality do access control lists provide in the implementation of d
ynamic NAT on a Cisco router?
define which addresses can be translated
2. Which three guidelines would help contribute to creating a strong password po
licy? (Choose three.)
Deliberately misspell words when creating passwords.
Create passwords that are at least 8 characters in length.
Use combinations of upper case, lower case, and special characters.
3. Refer to the exhibit. Every time the administrator reboots this router, the b
oot process ends in setup mode. What is a possible problem?
The configuration register is set to ignore the startup configuration.
4. Which option correctly defines the capacity through the local loop guaranteed
to a customer by the service provider?
CIR
5. Refer to the exhibit. A host connected to Fa0/0 is unable to acquire an IP ad
dress from the DHCP server. The output of the debug ip dhcp server command shows
"DHCPD: there is no address pool for 10.1.1.1". What is the problem?
The pool of addresses for the 10Network pool is incorrect.
6. Which data link layer encapsulation protocol is used by default for serial co
nnections between two Cisco routers?
HDLC
7. Refer to the exhibit. Which statement correctly describes how Router1 process
es an FTP request that enters interface s0/0/0 and is destined for an FTP server
at IP address 192.168.1.5?
The router matches the incoming packet to the statement that was created by the
access-list 101 permit ip any 192.168.1.0 0.0.0.255 command and allows the packe
t into the router.
8. Compared with IDS systems, what can IPS systems do to provide further protect
ion of computer systems?
Stop the detected attack from executing
9. Which IEEE 802.16 broadband wireless technology allows users to connect to th
e ISP at speeds comparable to DSL and cable?
WiMAX
10. A network administrator has changed the VLAN configurations on his network s
witches over the past weekend. How can the administrator determine if the additi
ons and changes improved performance and availability on the company intranet?
Conduct a performance test and compare with the baseline that was established pr
eviously.
11. Refer to the exhibit. What is the meaning of the term dynamic in the output
of the command?
The Serial0/0/1 interface acquired 172.16.3.1 from a DHCP server.
12. Which type of ACL will permit traffic inbound into a private network only if
an outbound session has already been established between the source and destina
tion?
reflexive
13. Which two statements are true about IPv6 link local addresses? (Choose two.)
They begin with the 2000::/3 prefix.
They are assigned by IANA to an organization.
14. A company is looking for a WAN solution to connect its headquarters site to
four remote sites. What are two advantages that dedicated leased lines provide c
ompared to a shared Frame Relay solution? (Choose two.)
Reduced jitter
Reduced latency
15. Refer to the exhibit. A network administrator is trying to connect R1 remote
ly to make configuration changes. Based on the exhibited command output, what wi
ll be the result when attempting to connect to R1?
A successful connection and ability to make configuration changes
16. What are two effective measures for securing routers? (Choose two.)
Protect all active router interfaces by configuring them as passive interfaces.
Configure remote administration through VTY lines for Telnet access.
17. An issue of response time has recently arisen on an application server. The
new release of a software package has also been installed on the server. The con
figuration of the network has changed recently. To identify the problem, individ
uals from both teams responsible for the recent changes begin to investigate the
source of the problem. Which statement applies to this situation?
It will be difficult to isolate the problem if two teams are implementing change
s independently.
18. Refer to the exhibit. From the output of the show interfaces and ping comman
ds, at which layer of the OSI model is a fault indicated?
network
19. Which technology is used to dynamically map next hop, network layer addresse
s to virtual circuits in a Frame Relay network?
Inverse ARP
20. An administrator learns of an e-mail that has been received by a number of u
sers in the company. This e-mail appears to come from the office of the administ
rator. The e-mail asks the users to confirm their account and password informati
on. Which type of security threat does this e-mail represent?
Phishing
21. Refer to the exhibit. Which data transmission technology is being represente
d?
TDM
22. Refer to the exhibit. Results of the show vlan and show vtp status commands
for switches S1 and S2 are displayed in the exhibit. VLAN 11 was created on S1.
Why is VLAN 11 missing from S2?
The VTP domain names do not match.
23. What is the result of adding the global command service password-encryption
to the configuration of a router?
All services must provide an encrypted password to function.
24. While troubleshooting a problem with an e-mail server, an administrator obse
rves that the switch port used by the server shows "up, line protocol up". The a
dministrator cannot ping the server. At which layer of the OSI model is the prob
lem most likely to be found?
Network layer
25. Where does a service provider assume responsibility from a customer for a WA
N connection?
Demarcation point
26. What will be the result of adding the command ip dhcp excluded-address 192.1
68.24.1 192.168.24.5 to the configuration of a local router that has been config
ured as a DHCP server?
The DHCP server will not issue the addresses ranging from 192.168.24.1 to 192.16
8.24.5.
27. Refer to the exhibit. Partial results of the show access-lists and show ip i
nterface FastEthernet 0/1 commands for router Router1 are shown. There are no ot
her ACLs in effect. Host A is unable to telnet to host B. Which action will corr
ect the problem but still restrict other traffic between the two networks?
Reverse the order of the TCP protocol statements in the ACL.
28. Refer to the exhibit. The corporate network that is shown has been assigned
network 172.16.128.0/19 for use at branch office LANs. If VLSM is used, what mas
k should be used for addressing hosts at Branch4 with minimal waste from unused
addresses?
/22
29. Refer to the exhibit. RIPv2 has been configured on all routers in the networ
k. Routers R1 and R3 have not received any RIP routing updates. What will fix th
e issue?
Enable RIP authentication on R2.
30. Refer to the exhibit. This serial interface is not functioning correctly. Ba
sed on the output shown, what is the most likely cause?
PPP negotiation failure
31. Which statement is true about PAP in the authentication of a PPP session?
PAP uses a two-way handshake.
32. An administrator is configuring a dual stack router with IPv6 and IPv4 using
RIPng. The administrator receives an error message when trying to enter the IPv
4 routes into RIPng. What is the cause of the problem?
IPv4 is incompatible with RIPng.
33. What is tunneling?
Encapsulating an entire packet within another packet for transmission over a net
work
34. Which statement is true about NCP?
Each network protocol has a corresponding NCP.
35. Refer to the exhibit. A network administrator is creating a prototype to ver
ify the new WAN design. However, the communication between the two routers canno
t be established. Based on the output of the commands, what can be done to solve
the problem?
Configure RA with a clock rate command.
36. Refer to the exhibit. Based on the output as shown, which two statements cor
rectly define how the router will treat Telnet traffic that comes into interface
FastEthernet 0/1? (Choose two).
Telnet to 172.16.10.0/24 is permitted.
37. Which Frame Relay flow control mechanism is used to signal routers that they
should reduce the flow rate of frames?
FECN
38. Refer to the exhibit. A network administrator configures a standard access c
ontrol list on Router1 to prohibit traffic from the 192.168.0.0/24 network from
reaching the Internet. The access control list also permits traffic from the 192
.168.0.0/24 network to reach the 192.168.1.0/24 network. On which interface and
in which direction should the access control list be applied?
Interface S0/0/0, outbound
39. Which configuration on the vty lines provides the best security measure for
network administrators to remotely access the core routers at headquarters?
Answer: 3nd option
40. Refer to the exhibit. What can be concluded from the exhibited output of the
debug ip nat command?
The 192.168.0.0/24 network is the inside network.
41. A network administrator is instructing a technician on best practices for ap
plying ACLs. Which suggestion should the administrator provide?
Extended ACLs should be applied closest to the source that is specified by the A
CL.
42. Refer to the exhibit. Headquarters is connected through the Internet to bran
ch office A and branch office B. Which WAN technology would be best suited to pr
ovide secure connectivity between headquarters and both branch offices?
VPN
43. Which three physical network problems should be checked when a bottom-up tro
ubleshooting approach has been chosen to troubleshoot network performance? (Choo
se three.)
Cable connectivity
High collision counts
High CPU utilization rates
44. Refer to the exhibit. A network administrator is attempting to configure a F
rame Relay network. The administrator enters the commands as shown in the exhibi
t on R2, but the Frame Relay PVCs are inactive. What is the problem?
The incorrect DLCI numbers are being configured on R2.
45. Which IP address and wildcard mask would be used in an ACL to block traffic
from all hosts on the same subnet as host 192.168.16.43/28?
Access-list 10 deny 192.168.16.43 0.0.0.16
46. Which combination of Layer 2 protocol and authentication should be used to e
stablish a link without sending authentication information in plain text between
a Cisco and a non-Cisco router?
PPP with CHAP
47. When would the multipoint keyword be used in Frame Relay PVCs configuration?
When participating routers are in the same subnet
48. A network technician analyzes the network and notices late collisions. The c
ollisions occur accompanied by jabber that originates from the server. What is t
he likely cause of the problem?
Web server CPU overload
49. Refer to the exhibit. R1 is performing NAT overload for the 10.1.1.0/24 insi
de network. Host A has sent a packet to the web server. What is the destination
IP address of the return packet from the web server?
172.30.20.1:3333
50. Refer to the exhibit. All devices are configured as shown in the exhibit. PC
1 is unable to ping the default gateway. What is the cause of the problem?
Port Fa0/2 on S2 is assigned to the wrong VLAN.
51. When Frame Relay encapsulation is used, what feature provides flow control a
nd exchanges information about the status of virtual circuits?
LMI
52. A network administrator is tasked with maintaining two remote locations in t
he same city. Both locations use the same service provider and have the same ser
vice plan for DSL service. When comparing download rates, it is noticed that the
location on the East side of town has a faster download rate than the location
on the West side of town. How can this be explained?
The service provider is closer to the location on the East side.
Você também pode gostar
- The Subtle Art of Not Giving a F*ck: A Counterintuitive Approach to Living a Good LifeNo EverandThe Subtle Art of Not Giving a F*ck: A Counterintuitive Approach to Living a Good LifeNota: 4 de 5 estrelas4/5 (5794)
- The Yellow House: A Memoir (2019 National Book Award Winner)No EverandThe Yellow House: A Memoir (2019 National Book Award Winner)Nota: 4 de 5 estrelas4/5 (98)
- Hidden Figures: The American Dream and the Untold Story of the Black Women Mathematicians Who Helped Win the Space RaceNo EverandHidden Figures: The American Dream and the Untold Story of the Black Women Mathematicians Who Helped Win the Space RaceNota: 4 de 5 estrelas4/5 (895)
- The Hard Thing About Hard Things: Building a Business When There Are No Easy AnswersNo EverandThe Hard Thing About Hard Things: Building a Business When There Are No Easy AnswersNota: 4.5 de 5 estrelas4.5/5 (344)
- The Little Book of Hygge: Danish Secrets to Happy LivingNo EverandThe Little Book of Hygge: Danish Secrets to Happy LivingNota: 3.5 de 5 estrelas3.5/5 (399)
- The Emperor of All Maladies: A Biography of CancerNo EverandThe Emperor of All Maladies: A Biography of CancerNota: 4.5 de 5 estrelas4.5/5 (271)
- Devil in the Grove: Thurgood Marshall, the Groveland Boys, and the Dawn of a New AmericaNo EverandDevil in the Grove: Thurgood Marshall, the Groveland Boys, and the Dawn of a New AmericaNota: 4.5 de 5 estrelas4.5/5 (266)
- Never Split the Difference: Negotiating As If Your Life Depended On ItNo EverandNever Split the Difference: Negotiating As If Your Life Depended On ItNota: 4.5 de 5 estrelas4.5/5 (838)
- A Heartbreaking Work Of Staggering Genius: A Memoir Based on a True StoryNo EverandA Heartbreaking Work Of Staggering Genius: A Memoir Based on a True StoryNota: 3.5 de 5 estrelas3.5/5 (231)
- Elon Musk: Tesla, SpaceX, and the Quest for a Fantastic FutureNo EverandElon Musk: Tesla, SpaceX, and the Quest for a Fantastic FutureNota: 4.5 de 5 estrelas4.5/5 (474)
- Team of Rivals: The Political Genius of Abraham LincolnNo EverandTeam of Rivals: The Political Genius of Abraham LincolnNota: 4.5 de 5 estrelas4.5/5 (234)
- The World Is Flat 3.0: A Brief History of the Twenty-first CenturyNo EverandThe World Is Flat 3.0: A Brief History of the Twenty-first CenturyNota: 3.5 de 5 estrelas3.5/5 (2259)
- The Unwinding: An Inner History of the New AmericaNo EverandThe Unwinding: An Inner History of the New AmericaNota: 4 de 5 estrelas4/5 (45)
- The Gifts of Imperfection: Let Go of Who You Think You're Supposed to Be and Embrace Who You AreNo EverandThe Gifts of Imperfection: Let Go of Who You Think You're Supposed to Be and Embrace Who You AreNota: 4 de 5 estrelas4/5 (1090)
- The Sympathizer: A Novel (Pulitzer Prize for Fiction)No EverandThe Sympathizer: A Novel (Pulitzer Prize for Fiction)Nota: 4.5 de 5 estrelas4.5/5 (121)
- T&B Detailed Plan: Ceiling LineDocumento1 páginaT&B Detailed Plan: Ceiling LineKuthbert NoceteAinda não há avaliações
- Sappi Mccoy 75 Selections From The AIGA ArchivesDocumento105 páginasSappi Mccoy 75 Selections From The AIGA ArchivesSappiETCAinda não há avaliações
- Business Occupancy ChecklistDocumento5 páginasBusiness Occupancy ChecklistRozel Laigo ReyesAinda não há avaliações
- TokyoDocumento6 páginasTokyoMarcio BonziniAinda não há avaliações
- Permit To Work Audit Checklist OctoberDocumento3 páginasPermit To Work Audit Checklist OctoberefeAinda não há avaliações
- Relay Interface ModulesDocumento2 páginasRelay Interface Modulesmahdi aghamohamadiAinda não há avaliações
- Change Language DynamicallyDocumento3 páginasChange Language DynamicallySinan YıldızAinda não há avaliações
- D6a - D8a PDFDocumento168 páginasD6a - D8a PDFduongpn63% (8)
- DevelopmentPermission Handbook T&CPDocumento43 páginasDevelopmentPermission Handbook T&CPShanmukha KattaAinda não há avaliações
- GSMDocumento11 páginasGSMLinduxAinda não há avaliações
- Erickson Transformer DesignDocumento23 páginasErickson Transformer DesigndonscogginAinda não há avaliações
- Solutions To Questions - Chapter 6 Mortgages: Additional Concepts, Analysis, and Applications Question 6-1Documento16 páginasSolutions To Questions - Chapter 6 Mortgages: Additional Concepts, Analysis, and Applications Question 6-1--bolabolaAinda não há avaliações
- A Study On Effective Training Programmes in Auto Mobile IndustryDocumento7 páginasA Study On Effective Training Programmes in Auto Mobile IndustrySAURABH SINGHAinda não há avaliações
- Fin 3 - Exam1Documento12 páginasFin 3 - Exam1DONNA MAE FUENTESAinda não há avaliações
- 7373 16038 1 PBDocumento11 páginas7373 16038 1 PBkedairekarl UNHASAinda não há avaliações
- Sigma Valve 2-WayDocumento2 páginasSigma Valve 2-WayRahimAinda não há avaliações
- Inspection and Test Plan Piling: 1. Document ReviewDocumento3 páginasInspection and Test Plan Piling: 1. Document ReviewZara BhaiAinda não há avaliações
- Seminar Report of Automatic Street Light: Presented byDocumento14 páginasSeminar Report of Automatic Street Light: Presented byTeri Maa Ki100% (2)
- Analysis of Brand Activation and Digital Media On The Existence of Local Product Based On Korean Fashion (Case Study On Online Clothing Byeol - Thebrand)Documento11 páginasAnalysis of Brand Activation and Digital Media On The Existence of Local Product Based On Korean Fashion (Case Study On Online Clothing Byeol - Thebrand)AJHSSR JournalAinda não há avaliações
- Computer System Sevicing NC Ii: SectorDocumento44 páginasComputer System Sevicing NC Ii: SectorJess QuizzaganAinda não há avaliações
- Software Testing Notes Prepared by Mrs. R. Swetha M.E Unit I - Introduction at The End of This Unit, The Student Will Be Able ToDocumento30 páginasSoftware Testing Notes Prepared by Mrs. R. Swetha M.E Unit I - Introduction at The End of This Unit, The Student Will Be Able ToKabilan NarashimhanAinda não há avaliações
- Gowtham Kumar Chitturi - HRMS Technical - 6 YrsDocumento4 páginasGowtham Kumar Chitturi - HRMS Technical - 6 YrsAnuAinda não há avaliações
- Mathematical Geophysics: Class One Amin KhalilDocumento13 páginasMathematical Geophysics: Class One Amin KhalilAmin KhalilAinda não há avaliações
- The Website Design Partnership FranchiseDocumento5 páginasThe Website Design Partnership FranchiseCheryl MountainclearAinda não há avaliações
- Step-7 Sample ProgramDocumento6 páginasStep-7 Sample ProgramAmitabhaAinda não há avaliações
- Jainithesh - Docx CorrectedDocumento54 páginasJainithesh - Docx CorrectedBala MuruganAinda não há avaliações
- Computerized AccountingDocumento14 páginasComputerized Accountinglayyah2013Ainda não há avaliações
- Brother Fax 100, 570, 615, 625, 635, 675, 575m, 715m, 725m, 590dt, 590mc, 825mc, 875mc Service ManualDocumento123 páginasBrother Fax 100, 570, 615, 625, 635, 675, 575m, 715m, 725m, 590dt, 590mc, 825mc, 875mc Service ManualDuplessisAinda não há avaliações
- S200 For Sumber RezekiDocumento2 páginasS200 For Sumber RezekiIfan JayusdianAinda não há avaliações
- Emco - Unimat 3 - Unimat 4 LathesDocumento23 páginasEmco - Unimat 3 - Unimat 4 LathesEnrique LueraAinda não há avaliações