Escolar Documentos
Profissional Documentos
Cultura Documentos
A Family of Suboptimum Detectors For Coherent MUD
Enviado por
issayed0 notas0% acharam este documento útil (0 voto)
22 visualizações8 páginasSuboptimum Detectors for Coherent MUD
Título original
A Family of Suboptimum Detectors for Coherent MUD
Direitos autorais
© © All Rights Reserved
Formatos disponíveis
PDF, TXT ou leia online no Scribd
Compartilhar este documento
Compartilhar ou incorporar documento
Você considera este documento útil?
Este conteúdo é inapropriado?
Denunciar este documentoSuboptimum Detectors for Coherent MUD
Direitos autorais:
© All Rights Reserved
Formatos disponíveis
Baixe no formato PDF, TXT ou leia online no Scribd
0 notas0% acharam este documento útil (0 voto)
22 visualizações8 páginasA Family of Suboptimum Detectors For Coherent MUD
Enviado por
issayedSuboptimum Detectors for Coherent MUD
Direitos autorais:
© All Rights Reserved
Formatos disponíveis
Baixe no formato PDF, TXT ou leia online no Scribd
Você está na página 1de 8
683
I EEE J OURNAL ON SELECTED AREAS I N COMMUNICATIONS. VOL. 8. NO. 4. MAY 1990
A Family of Suboptimum Detectors for Coherent
Multiuser Communications
ZHENHUA XI E, ROBERT T. SHORT. A ND CRAIG K. RUSHFORTH
Abstract-In this paper we consider a class of suboptimum detectors
for data transmitted asynchronously by K users employing direct se-
quence spread spectrum multiple access (DS/SSMA) on the additive
white Gaussian noise (AWGN) channel. The general structure of these
detectors consists of a bank of matched filters, a linear transformation
that operates on the matched-filter outputs, and a set of threshold de-
vices. The linear transformations are chosen to minimize either a mean
squared error or a weighted squared error performance criterion. Each
detector can be implemented using a tapped delay line. The number of
computations performed per detected bit is linear in K in each case,
and the resulting detectors are thus much simpler than the optimum
detector. Under typical operating conditions, these detectors will per-
form much better than the conventional receiver and often nearly as
well as the optimum detector.
I . I NTRODUCTI ON
E consider in this paper a coherent asynchronous
W K-user DS/SSMA system for transmitting signals
on the additive white Gaussian noise channel. The re-
ceiver makes symbol estimates using a detector that con-
sists of a bank of matched filters followed by a decision
algorithm. Two well-known detectors of this type are the
conventional receiver, which simply compares each
matched-filter output to a threshold, and the maximum-
likelihood (ML) sequence detector whose decision algo-
rithm is the Viterbi algorithm [ 1 1-[4]. The complexity of
the ML detector grows exponentially with K, and is thus
impractical unless the number of users is quite small. At
the same time, the performance of the conventional re-
ceiver deteriorates rapidly as the number of users in-
creases. We are therefore led to study suboptimum detec-
tors that are easier to implement than the ML receiver but
that perform much better than the conventional receiver.
Some examples of suboptimum detectors that have been
previously studied are a sequential decoding algorithm [ 5 ] ,
a decision-feedback equalizer [6], 171 for asynchronous
DS/SSMA systems, and an optimized linear multiuser de-
tector for synchronous DS/SSMA systems [SI .
In this paper, we consider a class of suboptimum de-
tectors for the asynchronous DS/SSMA system whose de-
Manuscript received February 21, 1989; revised September 18. 1989.
This work was supported by the Unisys Corporation under the University
of Utah Contract 5-20516. This paper was presented in part at MILCOM
'89, Boston, MA, October 15-18, 1989.
Z. Xie and C. K . Rushforth are with the Department of Electrical En-
gineering, University of Utah, Salt Lake City, UT 841 12.
R. T. Short is with Communication Systems Division. Unisys Corpo-
ration, Salt Lake City, UT 841 16.
IEEE Log Number 9034793.
cision algorithms consist of a linear transformation T fol-
lowed by a set of threshold devices. This approach is
motivated by equalization techniques developed for chan-
nels with intersymbol interference [ 111 and by the ap-
proaches taken in [6] and [SI. Because of the similarities
between the two problems, it should not be surprising that
techniques which are effective in combatting intersymbol
interference can also be used to advantage in the multi-
access problem. In addition to the obvious similarities,
however, there are some important differences. For ex-
ample, the near-far problem (i.e., the problem of signif-
icantly different user powers) encountered in multiple-ac-
cess communications has no counterpart in the
intersymbol interference context. Moreover, the system
designcr can typically exercise more control over the level
of interference in designing a multiple-access system
through his or her choice of signature sequences than
would be possible in the intersymbol interference prob-
lem. Thus, we might reasonably expect suboptimum mul-
tiple-access receivers to perform well under a broader
range of conditions than their intersymbol-interference
counterparts.
We obtain two different versions of T using two differ-
ent performance criteria: minimum mean squared error
and weighted least squares. These choices, though not op-
timum in terms of bit-error probability, are mathemati-
cally tractable and lead to elegant and simple detection
structures that can be implemented using tapped delay
lines. These structures have computational complexities
per detected bit which are linear in K, and are thus much
simpler than the optimum detector. This result rests on
the assumption that the parameters of the system have
been computed and are fixed. The practical problems as-
sociated with estimating the parameters of the system and
adapting the structure of the detector must be faced re-
gardless of the decision rule adopted and thus do not ap-
preciably affect the comparisons we make.
Our initial results are based on the assumption that the
linear transformation operates on the entire received
waveform to estimate the entire transmitted sequence.
This approach requires too much memory and entails too
much decoding delay to be practical, so we next consider
some modified algorithms that have small fixed decoding
delays. We also discuss appropriately modified versions
of two schemes that have been widely used to combat in-
tersymbol interference: the linear equalizer and the deci-
sion-feedback equalizer.
0733-87 16/90/0500-0683$01 .OO @ 1990 IEEE
684
IEEE JOURNAL ON SELECTED AREAS IN COMMUNICATIONS. VOL. 8. NO. 4. MAY 1990
Matched
Filter
Bank
In Section 11, we review the DS/SSMA signaling
scheme and present a discrete model for its analysis. The
minimum mean squared error (MMSE) detector, its per-
formance, its implementation, and various suboptimum
modifications of it are developed and discussed in Section
111. The computational complexity of the MMSE detector
is shown to be 3K multiplications/bit. In Section I V, the
linear equalizer is derived and its performance is ana-
lyzed. One common feature of the MMSE detector and
the linear equalizer is that the preliminary estimate of the
transmitted bit sequence obtained using the linear trans-
formation T is biased. This complicates the analysis and
leads to a performance that depends on the interfering sig-
nal power. The weighted least squares (WLS) detector de-
scribed in Section V avoids this problem by providing an
unbiased estimate of the transmitted sequence. The com-
putational complexity of the WLS detector is once again
3K multiplications /bit, and its bit-error probability and
asymptotic efficiency are independent of the interfering
users powers.
A natural suboptimum implementation of the WLS de-
tector yields the well-known decision feedback equalizer
[6], which we discuss in Section VI. In Section VII, we
summarize the results of several computer simulations
conducted to illustrate the performances of the detectors
described in this paper and to compare them to the per-
formances of the conventional receiver and the optimum
(ML) receiver. In many circumstances of interest, the re-
ceivers described here perform much better than the con-
ventional receiver and nearly as well as the more compli-
cated ML receiver.
Dension
Algorithm
+
11. PRELIMINARIES
We consider BPSK transmission through a common
AWGN channel shared by K asynchronous users employ-
ing DS/SSMA, as illustrated in Fig. 1. The received sig-
nal r ( r ) can be written in the form 131
M K
r ( t ) = C C b , ( i ) ~ , ( t - i ~ - 7 ! , ) + n ( r )
1 = I ,=I
MK
= C h 1 1 1 ) ( r ( 4 ) %11l , ( f - r ( m) T
111 =I
- 7 , ( 1 1 1 ) +n( r )
( 2. 1)
where n ( t ) is additive white Gaussian noise with two-
sided power spectral density N 0 / 2 , k ( m ) - 1 =m mod
K , ~ ( m ) - 1 is the integer part of m/K, and M is the
number of bits transmitted by each user. b, ( i ) E {- I ,
1 } is the ith transmitted bit of the kth user,
S, ( r ) =J ~ w , U!, ( 1) COS ( act +0, ),
t E [o, T )
( 2 . 2 )
is the signature waveform of the kth user, a, ( r ) is the
spreading signal of the kth user normalized to unit power,
Fig. I . Systemmodel for asynchronous DSiSSMA communications.
carrier phase, a, is the common carrier frequency, and w!,
is the received signal power of the kth user. The powers,
phases, and time delays of all users are assumed to be
known, and without loss of generality the users are or-
dered in such a way that the time delays satisfy 0 I T~
I I T~ <T. In practice, these system parameters
must of course be estimated and continually updated, a
problem that we are currently studying.
The spreading signal a, ( t ) , which is used to reduce
multiuser interference, is a signal of duration T seconds
that can be written in the form
L
( r ) = ut ~pTf ( I - ( m - (2.3)
111 =I
where pT, ( t ) is the spreading chip waveform whose du-
ration is T, =T / L seconds and { at , E ( - 1, is
the spreading sequence of the kth user. The assumption
regarding the duration of the signature waveform has been
made almost universally by others working on this prob-
lem [l ], [ 2 ] , [ 3 ] , and our results show that it does not
seriously limit multiple-access performance. If additional
protection against jamming or unauthorized interception
were required, the generalization would be analytically
straightforward, although the implementation would be
somewhat more complicated.
The matched-filter output y, ( 1,1 ) ( 7 ( m ) ) associated with
the k(m)th user in the r(m)th bit interval is given by [3]
( 9( 11l ) + l ) T +T i ( l r l I
J h d ~ ( ~ ) ) =i7,,),lr+,h
r ( f ) %O, I , ( t - 7 ( m) T - Q , I 1 1 , ) dr
111 +K - I
= b m ( T ( i ) )
K (,,I 1 !, ( 1 , ( r ( m 1
! = ! t i - K + l
- r ( 4 ) +% 1 1 1 ) ( d ~ ) )
(2.4)
where
m
H1,(m) =1 s , ( r -
s,(t +mT - 7,) dr
(2.5)
is the signal crosscorrelation function. We see that
y, (7 ( m ) ) depends upon the transmitted bits, the sig-
-m
rk is the time delay of the kth user, 0, is the kth users nal crosscorrelations, and the noise.
XI E (' 1 ( I / . : SUBOPTI MUM DETECTORS FOR MUL TI USER COMMUNI CATI ONS 685
Using vector notation, it is not difficult to show that the
MK matched-filter outputs yL(,,! ( q ( t n ) ) can be expressed
as [ I O]
y =PMb +n (2.6)
where
y(i ) =[yl (i >, y2(i>, . * , Y K ( i ) l T ~ R ~ ,
b( i ) =[bl (i ), b2(i ), * * * , bK (i )l TE {- I , I I ",
n =[ n ( l)', n(2)', * . * , n(M)']' E RMK,
y =[y( I )', y(2)', * * . , y(M)']' E RMK,
b =[ b( l ) ' , l ~( 2) ~,
* . , ~(M)']'E {- 1 , I } MK ,
n( i > =[nl (i >, n2(i ), .
, nK(i )]'E R ~ ,
and
PM =
H( 0 ) H(1f 0
H ( l ) H ( 0 ) H( 1) ' 0
0 . . . 0 H( 0
0
. . .
0
-
-
0
0
. . .
. . .
The vector y is a sufficient statistic for estimating the
transmitted bits b. The elements of all vectors are ordered
in accordance with their relative appearances in time. PM
is a symmetric matrix which we assume to be positive
definite and hence invertible, but most of the results we
present can be easily generalized.
All decision algorithms considered in this paper com-
prise two steps. First, a linear estimate b =Ty of the
transmitted bits b is obtained from the matched-filter out-
put y. The constraint that b E {- 1 , 1 } is dropped in this
process and arbitrary real-valued estimates are allowed.
Second, the components of the estimate b are compared
to a threshold of zero, and the Cnal bit estimates are taken
to be the components of sgn [ b].
111. THE MMSE DETECTOR
We first study the linear minimum-mean-squared-error
(MMSE) detector. Formally, the problem can be stated as
follows: first a mapping T: R,"" --t RMK such that the per-
formance criterion E {( b - b ) ' ( b - 8 ) }is minimized,
where the estimate b is given by b =Ty. The mapping
that achieves this minimum is
T =( P M +NO/2Z)-'.
( P M +N, / Wb =y,
( 3. 1 )
In practice, we could estimate b by solving the linear
equation
( 3 . 2 )
a process that can be carried out efficiently using LU de-
composition, forward elimination, and back substitution
[ 1 I] by the system shown in Fig. 2. The inputs are the
MK matched-filter outputs y, the outputs are the estimated
bits sgn [ b ] , and the L, and U, are matrices that arise dur-
ing the process of block LU decomposition [ 12, p. 11 1 1 .
The basic operations of matrix-vector multiplication and
vector addition can be simply implemented using a tapped-
delay-line architecture. To detect MK transmitted bits re-
quires 3 MK2 multiplications. Therefore, the complexity
of this detector is 3 K multiplications/bit, which is linear
in K and is independent of the transmission length M.
In the absence of noise, the MMSE estimate becomes
b =PGly. At the other extreme, i.e., when No >>w, for
all j , T reduces to the identity mapping and the MMSE
detector reduces to the well-known conventional receiver.
A. Performance of the MMSE Detector
We now consider the performance of the MMSE detec-
tor. The performance criteria we are the bit-error prob-
ability and the asymptotic efficiency as defined by Verdu
We show in Appendix A that the probability that the ith
141.
bit of the kth user is detected in error is given by
c
p,MMSE(i) =2 - MK + I
h l , l ( V ( / l I { - 1 . 1 )
( 3 . 3 )
where a is the [ ( i - 1 ) K +k]th diagonal entry of ( PM
is the [ ( i - l ) K +k]th row of ( PM +iVo/2Z)-'flM, and
+NO/2Z)-I PM( PI z . I +N0/2Z)-I 3 [gl, g,, . * * 9 gMK 1
dv.
e - ( u ' / 2 1
Q ( x ) =-
& I sm
Each term in the sum in ( 3. 3) is the error probability for
the ith bit of the kth user, conditioned on a particular
combination of the remaining bits. Each such combina-
tion is equally likely, thus accounting for the factor
, and the sum is taken over all 2 M K - I such com-
binations.
Verdu [4] defines the asymptotic efficiency of the kth
user, whose bit error probability is Pk, to be
qk =sup 0 I r
2 - MK +I
{
I 1 1 limo+O Pk(u)/Q[(m;L)"L/u] <+ CO] . ( 3. 4)
To determine the asymptotic efficiency qpMSE of the
MMSE detector, we note that the dominant term in (3. 3)
as No -+ 0 is
Q
2 - MK+ I
~
686 I EEE J OURNAL ON SELECTED AREAS IN COMMUNI CATI ONS. VOL X. NO 4. MAY I990
It follows that
Fig. 2 . MMSE and WLS detector architecture
6
(3.5)
V pMSE =max2
Equations (3.3) and (3.5) characterize the performance of
the MMSE detector. We see that ypMSF is, in general,
dependent on the interfering signal power. This depen-
dence is a consequence of the fact that the estimate b =
Ty defined by (3.2) is biased.
To compare the performance of the MMSE detector
with that of the conventional receiver, we consider the
special case for which No <<w, for all j . We then have
( O M +No/2Z)-I =picl', and (3.5) can be simplified to
1
p S E = . (3.6)
Asi mpl ecal cul ati onofthe[(i - 1) K + k, ( i - 1) K +
k]th cofactor and the determinant of OM shows that the
denominator in (3.6) is independent of the interfering sig-
nal power. In contrast, the asymptotic efficiency of the
canventional receiver decreases monotonically as the
power in the interfering signal increases [4]. The advan-
tage to the MMSE detector can be substantial.
To illustrate, we consider a synchronous two-user
DS/SSMA system. In this case, we have H ( 1 ) =0 and
wA ( f i . ' ) , , - , , K+, . , , - I ) K + ,
Fig. 3 shows plots of the asymptotic efficiency of the first
user as a function of the ratio of the two signal powers for
the conventional receiver, the ML receiver [8], the MMSE
detector, and the WLS detector which will be discussed
in Section V. In all cases, we have pI =8 dB and Hl ,,(0)
=0.3. These plots show that when the interference is
small, i.e., when w2 -+0, the asymptotic efficiency of the
MMSE detector is the same as that of the conventional
receiver. In the presence of strong interference, i.e., w2
\
\ ,
-20 -10 0 10 20
0.0
lologlo(pz/Pl)
Fig. 3. Asymptotic etficiencies of ML receiver, conventional receiL-er.
MMSE detector. and WLS detector i n a two-user hynchronous DSiSSMA
\ystem.
-+ W, V l MMSE 2. 1 - Hl ,,(0)2, a constant independent of
p ?, whereas qf"" approaches zero.
B. Suboptimum Implementation
The MMSE detector described above operates on the
entire sequence at once. When M is large, as it will almost
always be in practice, the resulting detection delay will
be unacceptably large. Therefore, the implementation
shown in Fig. 2 must be modified to incorporate a prac-
tical constraint on the delay.
One obvious possibility is to divide the entire sequence
of M blocks into subsequences, each I blocks long, and
then to detect these subsequences one by one as in Fig.
2. Some modifications could be introduced to reinforce
the connection between the subsequences. For example,
the initial condition b ( 0 ) in Fig. 2 could be provided by
the already reconstructed symbols, and a hard-limited
version of y ( I +1 ) could be used in place of b( M +1 ).
The interconnection between the sections could be further
reinforced by overlapping.
Equation (3.6) will no longer be true for the subopti-
mum scheme described above, and its asymptotic perfor-
mance will depend on the power in the interfering signal.
Because of the nature of the multiuser interference terms.
XIE PI U / . . SUBOPTIMUM DETECTOKS FOK MULTIUSkK COMMUNICATIONS 687
it is reasonable to expect this type of behavior for any
detection scheme that operates on only a subset of the
matched-filter outputs.
IV. LI NEAR EQUALI ZER
I n this section, we formulate the MMSE detection prob-
lem under a constraint that the detector delay be finite,
say approximately J KT seconds with J <<M. Formally,
this corresponds to the following: find the mapping T:
R ' 2 J + 1 ) K +RK such that !he performance criterion
?{ ( b ( i ) - 6(i))T(b(i) - b ( i ) ) } is minimized where
b ( i ) =Ty. The ( 2 5 +l)K-dimensional matched-filter
outputvectoryisdefinedasy =[ y ( i - J ) ' , y ( i - J +
1 ) T, * '. This approach produces a var-
iant of the linear equalizer frequently used to combat in-
tersymbol interference [ 1 1 1 .
For i +J <M and i - J >0, y can be expressed as
, y ( i +J )
y =PZJ+lb +n +Pz (4.1 )
where b =[ b ( i - J ) r , b ( i - J +I )', * , b ( i +
0, * . . , 0, b ( i +J +
l ) T ] T , P 2 J + I is defined as in ( 2. 7) with the proper di-
mension, and
J y I T , z =[ b( i - J -
H(1) 0 . - . 0
P = [: ... 1. (4.2)
The term Pz in (4.1) is a consequence of the edge effects
associated with previous and future bits outside the ob-
servation window.
* - H( l ) T
The optimizing transformation in this case is
T = [ O , ~ ~ ~ O , H ( l ) , H ( 0 ) , H ( l ) T , O , e * - , 0 ]
which is well defined because the matrix in parentheses is
positive definite. Calculation of the estimate b( i) requires
( 2 5 +1 ) K2 multiplications; the computational complex-
ity of the linear equalizer is thus ( 2 5 +1 ) K multiplica-
tions/bit, which is linear in both K and J .
Since J is usually chosen to be greater than one, the
linear equalizer requires more computation than the sub-
optimum MMSE detector. However, its performance is
also expected to be somewhat better than that of the sub-
optimum MMSE detector. To see this, we neglect the term
PP' in (4.3) and write
T
[ 0,
* * , 0, I , 0, . . . , 01 ( P ~ J + I +No / 2 I ) ,
(4.4)
from which the primary difference between the linear
equalizer and the suboptimum LMS detector can be de-
duced. In the suboptimum LMS detector, the ( 2 5 +l ) K
estimated bits [ b ( i - J ) ' , b ( i - J +I ) ' , . * , b ( i +
J ) '1 Tare obtained using the ( 2 3 +1 ) K-dimensional in-
Fig. 4. Linear equalizer.
put vector y, while in the linear equalizer only the K bits
b ( i ) are estimated using ;he same input y and a similar
algorithm. The quality of b( i ) is apt to be better than that
of b( i k j ) f or j = 1,2, **.J becauseofedgeeffects.
One possible implementation of the linear equalizer is
shown i n Fig. 4. This implementation consists of a trans-
versal discrete-time filter with a finite delay to account for
the inherently noncausal nature of the algorithm.
Since the linear equalizer uses only a portion of the
matched-filter outputs, its asymptotic performance is de-
pendent on the power in the interfering signal because of
the edge effects discussed earlier.
V. THE WLS DETECTOR
As we have seen, both the MMSE detector and the lin-
ear equalizer produce preliminary estimates of the trans-
mitted bits that are biased. One important consequence of
this fact is that the performances of these two detectors
depend upon the interfering signal power. To avoid this
problem, we take the likelihood function f ( y 1 b ) as an
alternative performance criterion. Since the matched-filter
output y is Gaussian with conditional mean P,b and co-
variance matrix ( N0/ 2) P, , maximizing the likelihood
function is equivalent to minimizing
Q =( Y - P M b ) ' P G ' ( Y - P d ) . ( 5 . 1 )
In order to avoid confusing the detector that minimizes
(5.1) with the nonlinear ML sequence detector, we call
the former detector the weighted least-squares (WLS) de-
tector.
The vector that minimizes Q is
b =Oi l y. ( 5 . 2 )
Once again the estimation problem reduces to solving the
linear equation P,b =y. This WLS detector was pro-
posed previously by Lupas and Verdu [ 8] as a "decorre-
lating detector" in a study of the synchronous DS/SSMA
problem. We are grateful to an anonymous reviewer for
calling our attention to further results of Lupas and Verdu
on the asynchronous problem [ 9 ] , [I O]. and to Professor
Verdu for subsequently providing us with a preprint of
[I O]. I n view of the overlap between these results and our
own, our discussion of the WLS detector will be brjef.
Since y =P,b +n, it follows from ( 5. 2) thaLb =b
+/ 3i 1n, and thus that the preliminary estimate b of the
transmitted bit sequence is unbiased. One consequence of
this property is a performance that is independent of the
interfering signal power.
688 IEEE JOURNAL ON SELECTED AREAS I N COMMUNI CATI ONS. VOL 8. NO 4. MAY 1990
As in the case of the MMSE detector, the estimate of
(5.2) can be efficiently determined using block LU de-
composition followed by forward and backward substi-
tution [12]. The system shown in Fig. 2 can also be used
to implement the WLS detector, and the computational
complexity of the WLS detector is 3 K multiplica-
tions /bit.
In a manner similar to that described in Appendix A, i t
can be shown that the probability that the ith bit of the
kth user is in error is
a great simplification over the expressions for PpMSE( i )
and PkE(i ). Furthermore, PyLs( i ) is independent of the
interfering signal power [8].
The asymptotic efficiency of the WLS detector is
which is also independent of the interfering signal power
and is often substantially superior to the efficiency of the
conventional receiver. This result is identical to that ob-
tained for the MMSE detector when No <<wj for all j .
The asymptotic efficiencies of the first user in a two-
user synchronous DS/SSMA system employing the ML
detector, the conventional receiver, the MMSE detector,
and the WLS detector, respectively, are plotted as func-
tions of p 2 / p I in Fig. 3 . As we have already noted,
qyLs =1 - H, , , ( O) * is a constant independent of p 2 / p I
for a given cross-correlation coefficient. As p 2 +03,
qrMSE =qyLs. We further observe that there is a value
of p 2 , representing the worst condition for the ML detec-
tor, at which the asymptotic efficiencies of the ML detec-
tor and the WLS detector are equal [8].
As we pointed out in connection with the MMSE de-
tector, operating on the entire transmitted sequence at once
entails an unacceptable delay and must be avoided. A sub-
optimum version of the WLS detector can be imple-
mented in essentially the same way as previously de-
scribed. Because of edge effects, the asymptotic efficiency
and the bit-error probability of this partitioned scheme will
depend on the interfering signal power.
VI. DECI SI ON FEEDBACK EQUALI ZER
To obtain an alternative suboptimum implementation of
the WLS detector, we rewrite (5.2) in the form
i - I
I 1
w
Fig. S . Decision feedback equalizer
f ori =1, 2, - , MK. The form of (6.1) makes i t clear
that we can regard the WLS detector as a cancellation
scheme. Because the multiuser interference is noncausal,
(6.1) cannot be solved exactly in a sequential fashion. The
estimate of b, (7 ( i ) ) depends upon the estimates of
both past and future bits, and the entire observed se-
quence must be processed at once.
An obvious alternative is to make some preliminary de-
cisions regarding the future bits, and then to use these
preliminary estimates in (6.1). If these preliminary deci-
sions are very accurate, this scheme will perform nearly
as well as the optimum singer-user system because the
multiuser interference will be almost completely can-
celled. I n practice, however, there will be some perfor-
mance loss because of inaccuracies in the preliminary de-
cisions and the consequent imperfect cancellation of the
interference.
One way to provide the preliminary decisions for
b, ( , f l ) ( ( m ) ) is to make hard decisions on the correspond-
ing matched-filter outputs; i.e., to use sgn [ y k , f , r ) ( q ( m ) ) l
as a preliminary estimate for b, ( 1 , 1 ) ( 11 ( m ) ). The resulting
scheme is a form of the well-known decision-feedback
equalizer (DFE) [6], [7], which was originally proposed
to combat intersymbol interference [ 1 11. Because of the
similarities between multiuser interference and intersym-
bo1 interference, it seems reasonable that an appropriate
version of the DFE would be an effective detector in the
former case as well as in the latter.
From (6.1), we see that the DFE can be implemented
using feedback and feedforward filters as shown in Fig.
5 . The inputs to the feedback filter are the previously es-
timated symbols, while the inputs to the feedforward filter
are the symbols obtained from the preliminary decisions.
The feedforward filter is anticausal because its input is
derived from the matched-filter outputs J,,,~! ) ( q ( m ) ) for
m =i +1, , i +K - 1 . For the binary antipodal
signaling scheme considered here, the DFE is a multipli-
cation-free structure with a computational complexity of
2 K additions per bit.
Since the DFE is a nonlinear estimator, simple closed-
form expressions for the bit-error probability are difficult
to obtain. It is possible to find bounds and approxima-
tions, but these tend to be either computationally inten-
sive or grossly inaccurate 161, [7], [ 1 1 1 . Moreover, an ex-
act analysis of the asymptotic efficiency of the DFE seems
difficult and is omitted here. Consequently. the most ef-
fective way of examining the performance of the DFE is
through simulation. We describe the results of several
simulations in the next section.
VI I . SI MULATI ONS
To provide a basis for comparing the various detectors
discussed in this paper, we conducted an extensive series
of Monte-Carlo simulations. The schemes we evaluated
were finite-delay versions of the MMSE and WLS detec-
tors, each with subsequence length I =9 K and an overlap
of K bits between adjacent subsequences; a linear equal-
izer with J =4; the DFE; the conventional receiver; and
the ML sequence detector. In all cases, the modulation
was equiprobable BPSK with rectangular bit and chip
waveforms. In cases for which the ML receiver was too
complex to simulate, we used the performance of the sin-
gle-user system to provide a bound.
Among the examples studied were two asynchronous
DSISSMA configurations with K =2 and 18 and spread-
ing codes of lengths S and 127, respectively. The cross-
correlation coefficients in the two-user system were taken
to be H1,?(0) =0.3 and HI, ?( 1 ) =0.1, and the code
sequences for K = 18 were taken from [ 131. We used
relative time delays of 0.05 ( i - 1 ) T, i =1, 2, . . . 18,
for the eighteen-user system, and we set all its phase lags
to zero.
Fig. 6 shows plots of the average bit-error probabilities
of several different receivers as functions of the signal-to-
noise ratio for K =18. In this example, the powers of all
users are equal. Fig. 7 shows plots of the bit-error prob-
ability of the first-user versus the power of the interfering
user in the two-user asynchronous system to illustrate the
near-far capabilities of the various detectors. These re-
sults are typical of the many configurations we simulated.
From these plots, and from the many other simulations
we conducted, we make the following observations. First,
all the suboptimum detectors proposed in this paper per-
form much better than the conventional receiver and
nearly as well as the ML receiver under a wide variety of
conditions. Second, these detectors are quite robust in the
face of widely different signal powers. The linear equal-
izer and the DFE perform somewhat better than the sub-
optimum finite-delay versions of the MMSE and WLS de-
tectors. As predicted, the DFE is more robust than the
linear equalizer in the face of widely different signal power
levels.
To compare these results to those obtained previously
using a sequential decoding algorithm [SI, we plot in Fig.
8 the bit-error probability achieved in the eighteen-user
configuration using the linear equalizer, the DFE, and the
sequential decoding algorithm. We see that these three
detectors exhibit about the same performance. The advan-
tage of the detectors studied in this paper, as compared
with the sequential decoding algorithm, is their simpler
structure. Their simplicity, combined with their excellent
performance as demonstrated by these examples, makes
them very attractive practical algorithms.
VI I I . CONCLUSI ONS
The primary contribution of this paper is the develop-
ment and evaluation of a family of suboptimum DS/SSMA
Conve nud Receiver
opunum Single-Usa Detector
Suboptimum WLS Detector
Suboplimum MMSE Detector
Decision Feedkk Equalizer
10-
0 1 2 3 4 5 6 7 8 9
Fig. 6 . Bit-error probability for conventional receiver, optimumsingle-user
detector, suboptimumMMSE detector. suboptimumWLS detector. lin-
ear equalizer, and decision feedback equalizer with K =18 and L =
127.
/.'
/.'
- - - - Convenuonal Receiver
Subopumum ML Receiver WLS Detector
Suboplmum MMSE Dewtor
_ _ _ _ _
- Declsion FeedbaJ: Equalizer
Llnear F4uallzer
---__
689 XIE ~ ' f r r l SUBOPTI MUM DFTFCTORY FOR MULTI UYFR COMMUNI CATI ON\
I
~
_ _ ~~
~ _ _ _ _ _ ~ ~ ~~~ ~~~ ~
t 1
I
3 6 9 12 15
10.. 1
Fig. 7. Bit-error probability versus interfering user's power. for conven-
tional receiver, ML receiver. suboptimumMMSE detector. suboptimum
WLS detector. linear equalizer, and decision feedback equalizer with K
=2. L =5 . and w , / N , ) =5 dB.
lo-' 4
10-
~o~oglo(wlmolo)
Fig. 8. Bit-error probability for linear equalizer. decision feedback equal-
izer. and sequential decoding algorithmwith K =18 and L =127.
detectors whose computational complexity is only linear
in the number of users and yet which perform much better
than the conventional receiver and nearly as well as the
ML sequence detector in many practical circumstances.
The simple structures and excellent performances of these
690 l EEE J OURNAL ON SELECTED AREAS IN COMMUNI CATI ONS, VOL. 8. NO 4. MAY 1990
detectors make them very attractive alternatives to the
conventional receiver and the ML detector.
The results described in this paper were obtained under
the assumption that all system parameters (signal phase.
power, and delay) are known. I n practice, these parame-
ters must be estimated and the receiver structure contin-
ually modified to reflect the updated estimates. The ul ti -
mate evaluation and comparison of the detectors studied
here cannot be carried out without considering the effects
of noisy estimates on their performances. We are cur-
rently investigating this issue.
APPENDI X
I n this Appendix, we consider the bit-error probability
of the MMSE detector. The probability that the kth user's
ith bit is detected in erro; is given by
pFMSE =Pr {[sgn ( TY) l , l - , ) , +, =- 1 I b , ( i ) =1 )
b, ( i ) =1 )
quences." /EI,.E Tr t r m. Coi mrt u.. vol. COM-35. pp. 87-98. J an.
1987. .
131 S. Verdu. "Miniinurn prohability of error for asynchronous Gaussian
multiple-access channels." / FEE Trti i i .!. /fifitrrti. Tlioor?, vol. IT-32.
pp. 85-96, J an. 1986.
141 -. "Optimum inultiuser asymptotic eflicicncy." l EEE Trctm.
Cornmuti.. vol. COM-34, pp. 890-897. Sept. 1986.
IS] Z. Xie, C. K. Rushforth, and R. T. Short, "Multi-user signal detec-
tion using sequential decoding." l EEE Trutis. Cotntnun., vol. 37,
1989.
161 R. T. Short, "Multiple user receiver structures." Ph.D. dissertation.
Dcp. Elcc. Eng.. Uni v. Utah. Dec. 1988.
171 M. K . Varanasi and B. Aazhang. "An iterative detector l o r asyn-
chronous spread-spectrum multiple-access syateins," i n Proc..
181 R. Lupas and S. Vcrdu, "Linear multiuser detectors for synchronous
code-division multiple-access channels." / EEE Trtrris. /r!fitriti. T l i ~
or y , vol. 35, pp. 123-136, J an. 1989.
191 R. Lupas and S. Verdu, "Optimum near-far resistance of linear de-
tectors for code-division multiple-access channels,"in Proc. I nf .
Symp. Inform. Theorv, J une 19-24, 1988, Kobe. J apan. p. 14.
1101 -. "Near-far re\istance of linear detectors for code-division mul-
tiple-access channels." / EEE Truris. Conirtiuu., vol. COM-37, 1989.
[ I I I J . G. Proakis, Di gi f t i / Co,r i r t r i oi i c.t r r i t ~r i . New York: McGraw-Hill.
1983.
[ 121 G. H. Goluh and C. F. Van Loan. Mt i rri i Compuftrfioti.\. Baltimore.
MD: The J ohns Hopkins University Press, 1983.
[ 131 F. Gebhardt and C. L. Weber. "Aperiodic correlation properties of
pseudonoise codes." Tech. Rep., USCEE-430. Dcp. Elec. Eng..
Uni v. Southern California. Oct., 1972.
GLOBECOM'88. Hollywood. FL. NOV. 1988, pp. 556-560.
Zhenhua Xie wa\ born i n Zhejidng, China, on
J uly 15, 1958 He received the B S degree i n
electrical engineering fromZhejiang Univer\ity,
China. i n 1982, and the M S dnd Ph D degrees
in electrical engineering from the Univer\ity ot
Utah. i n 1985 and 1989, respectively
He I\ currently d po\t-doc fellow in Electrical
Engineering at the University of Utah Hi5 re-
search interest\ include digital signal proces\ing,
vision. and multiu\er communication\
where ( . ) I symbolizes the the kth element of the vector
inside the parentheses. Since the noise component [ ( PM
+N0/2Z)-'nl cl - is Gaussian with zero mean and
of
E { Pw +N 0 / 2 N ' nnT( f i w +N , ) / 2 C }
variance equal to the [ ( i - 1 ) K +k]th diagonal element
= ( Ow +&/ 2Z)- ' P,( @, VI +NI ) / ~Z) - ' , ( A. 2)
L
PyMSE(i ) can be expressed as a sum of Q-functions,
where
Specifically, if we denote the [ ( i - 1 ) K +k]th diagonal
entry of the matrix in (A.2) as NU/ 2 a and the [ ( i - 1 ) K
+k]th row ofthe matrix ( PM +N0 / 2 Z )-'Pwas [gI, g, ,
* * , &,,I, then p,MMsE(i can be written as
c Q
pY M S E ( j ) =2-MK+I
(A.3)
h!.l,l(V( / ) ) E ( - 1 . 1 )
of Electrical Engineerii
research interests lie i n
cessing.
Robert T. Short was born i n Boulder, CO. on
May 8, 1954. He received the B.S. degree i n elec-
trical engineering from New Mexico State Uni-
versity i n December of 1975.
He worked for Motorola Government Electron-
ics Division, Scottsdale. AZ, (1976-1981). Hew-
lett-Packard Corporation, Fort Collins, CO (1981-
1984). and Unisys Corporation, Salt Lake City,
UT (1984-1989). before receiving the Ph.D. de-
gree in electrical engineering in December of
1988. He is now on the faculty in the Department
ng at the University of Utah i n Salt Lake City. His
the areas of communication theory and signal pro-
which can, in principle, be calculated if ( p,,, +N0 / 2 Z ) - '
is given.
REFERENCES
I I ] M. B. Pursley, D. V. Sarwate. and W. E. Stark. "Error probability
for direct-sequence spread-spectrum multiple-access coinmunica-
tions-Part I : Upper and lower bounds." /FEE Trtrris. Cortirtlrtrr. . vol.
121 J . S. Lehnert and M. B. Pursley. "Error probability tor binary direct-
sequence spread-spectrumcommunication with randomsignature se-
COM-30. pp. 975-984. May 1982.
Craig K. Rushforth was born in Ogden. UT. He
received the B.S.. M.S., and Ph.D. degrees i n
electrical engineering from Stanford University,
Stanford. CA. i n 1958, 1960. and 1962. respec-
tively.
He has served on the facultieb of Utah State
University and Montana State University and has
held research positions at Stanford Research I n-
stitute. the Institute for Defense Analyses. and
ESL. Inc. He has been with the Department of
Electrical Engineering at the University of Utah
since 1974. He has served as Department Chairman from 1982 to 1985,
and from 1988 to the present. His research interests lie in communication
theory and signal processing. with current emphasis on multiple-access
communications. coded modulation. VLSI implementation of algorithms.
and signal restoration.
Você também pode gostar
- The Yellow House: A Memoir (2019 National Book Award Winner)No EverandThe Yellow House: A Memoir (2019 National Book Award Winner)Nota: 4 de 5 estrelas4/5 (98)
- Hidden Figures: The American Dream and the Untold Story of the Black Women Mathematicians Who Helped Win the Space RaceNo EverandHidden Figures: The American Dream and the Untold Story of the Black Women Mathematicians Who Helped Win the Space RaceNota: 4 de 5 estrelas4/5 (895)
- Paper 15-Eyes Based Eletric Wheel Chair Control SystemDocumento8 páginasPaper 15-Eyes Based Eletric Wheel Chair Control SystemFederico LopezAinda não há avaliações
- Optical Fiber Communication TutorialDocumento16 páginasOptical Fiber Communication TutorialAdamStoneAinda não há avaliações
- Quality Assurance & Accreditation Unit Course SpecificationsDocumento4 páginasQuality Assurance & Accreditation Unit Course SpecificationsissayedAinda não há avaliações
- Optical Fiber Communication TutorialDocumento16 páginasOptical Fiber Communication TutorialAdamStoneAinda não há avaliações
- 11 DatacommunicationDocumento56 páginas11 DatacommunicationWoldemariam WorkuAinda não há avaliações
- ProjectsDocumento50 páginasProjectsissayedAinda não há avaliações
- Comm NetworkDocumento198 páginasComm NetworkRavi YalalaAinda não há avaliações
- Digital Signal Processing A Practical Guide For Engineers and ScientistsDocumento26 páginasDigital Signal Processing A Practical Guide For Engineers and ScientistsissayedAinda não há avaliações
- Critical ThinkingDocumento181 páginasCritical ThinkingAhmed Ali HAinda não há avaliações
- Near-Far Resistant Detection of CDMA Signals Via Isolation Bit InsertionDocumento5 páginasNear-Far Resistant Detection of CDMA Signals Via Isolation Bit InsertionissayedAinda não há avaliações
- Huawei Model Echolife HG520b WIF Static IPDocumento6 páginasHuawei Model Echolife HG520b WIF Static IPissayedAinda não há avaliações
- How To Setup TP-Link Router (Dynamic Configuration)Documento4 páginasHow To Setup TP-Link Router (Dynamic Configuration)Mohamed SayedAinda não há avaliações
- Thyristor Theory and Design ConsiderationsDocumento240 páginasThyristor Theory and Design Considerationsvijai daniel100% (4)
- One-Shot Linear Decorrelating Detector For Asynchronous CDMADocumento5 páginasOne-Shot Linear Decorrelating Detector For Asynchronous CDMAissayedAinda não há avaliações
- Handbook of Operational Amplifier ApplicationsDocumento94 páginasHandbook of Operational Amplifier Applicationshermiit89% (9)
- Basic InstrumentationDocumento24 páginasBasic InstrumentationGoldie EspedillonAinda não há avaliações
- Sampling TheoremDocumento12 páginasSampling TheoremMohamed Mounir FekriAinda não há avaliações
- Ofdm Simulation in MatlabDocumento59 páginasOfdm Simulation in MatlabBinh ThanhAinda não há avaliações
- FPGA Design Flow: Muthuswamy@msoe - EduDocumento32 páginasFPGA Design Flow: Muthuswamy@msoe - EduissayedAinda não há avaliações
- Measurements and TestingDocumento3 páginasMeasurements and TestingissayedAinda não há avaliações
- Artificial Bee Colony AlgorithmDocumento25 páginasArtificial Bee Colony AlgorithmissayedAinda não há avaliações
- PHD ProDocumento13 páginasPHD ProissayedAinda não há avaliações
- The Multi-User Detection For The MIMO-OFDM System Based On The Genetic Simulated Annealing AlgorithmDocumento4 páginasThe Multi-User Detection For The MIMO-OFDM System Based On The Genetic Simulated Annealing AlgorithmissayedAinda não há avaliações
- The Subtle Art of Not Giving a F*ck: A Counterintuitive Approach to Living a Good LifeNo EverandThe Subtle Art of Not Giving a F*ck: A Counterintuitive Approach to Living a Good LifeNota: 4 de 5 estrelas4/5 (5794)
- The Little Book of Hygge: Danish Secrets to Happy LivingNo EverandThe Little Book of Hygge: Danish Secrets to Happy LivingNota: 3.5 de 5 estrelas3.5/5 (399)
- Devil in the Grove: Thurgood Marshall, the Groveland Boys, and the Dawn of a New AmericaNo EverandDevil in the Grove: Thurgood Marshall, the Groveland Boys, and the Dawn of a New AmericaNota: 4.5 de 5 estrelas4.5/5 (266)
- Elon Musk: Tesla, SpaceX, and the Quest for a Fantastic FutureNo EverandElon Musk: Tesla, SpaceX, and the Quest for a Fantastic FutureNota: 4.5 de 5 estrelas4.5/5 (474)
- Never Split the Difference: Negotiating As If Your Life Depended On ItNo EverandNever Split the Difference: Negotiating As If Your Life Depended On ItNota: 4.5 de 5 estrelas4.5/5 (838)
- A Heartbreaking Work Of Staggering Genius: A Memoir Based on a True StoryNo EverandA Heartbreaking Work Of Staggering Genius: A Memoir Based on a True StoryNota: 3.5 de 5 estrelas3.5/5 (231)
- The Emperor of All Maladies: A Biography of CancerNo EverandThe Emperor of All Maladies: A Biography of CancerNota: 4.5 de 5 estrelas4.5/5 (271)
- The World Is Flat 3.0: A Brief History of the Twenty-first CenturyNo EverandThe World Is Flat 3.0: A Brief History of the Twenty-first CenturyNota: 3.5 de 5 estrelas3.5/5 (2259)
- The Hard Thing About Hard Things: Building a Business When There Are No Easy AnswersNo EverandThe Hard Thing About Hard Things: Building a Business When There Are No Easy AnswersNota: 4.5 de 5 estrelas4.5/5 (344)
- Team of Rivals: The Political Genius of Abraham LincolnNo EverandTeam of Rivals: The Political Genius of Abraham LincolnNota: 4.5 de 5 estrelas4.5/5 (234)
- The Unwinding: An Inner History of the New AmericaNo EverandThe Unwinding: An Inner History of the New AmericaNota: 4 de 5 estrelas4/5 (45)
- The Gifts of Imperfection: Let Go of Who You Think You're Supposed to Be and Embrace Who You AreNo EverandThe Gifts of Imperfection: Let Go of Who You Think You're Supposed to Be and Embrace Who You AreNota: 4 de 5 estrelas4/5 (1090)
- The Sympathizer: A Novel (Pulitzer Prize for Fiction)No EverandThe Sympathizer: A Novel (Pulitzer Prize for Fiction)Nota: 4.5 de 5 estrelas4.5/5 (121)
- Liquitex Soft Body BookletDocumento12 páginasLiquitex Soft Body Booklethello belloAinda não há avaliações
- Sheltered 2 Item Recycle ListDocumento5 páginasSheltered 2 Item Recycle ListRachel GAinda não há avaliações
- RPH Week 31Documento8 páginasRPH Week 31bbwowoAinda não há avaliações
- Notice: Premerger Notification Waiting Periods Early TerminationsDocumento5 páginasNotice: Premerger Notification Waiting Periods Early TerminationsJustia.comAinda não há avaliações
- IMDSI22Documento82 páginasIMDSI22Dang JinlongAinda não há avaliações
- Crisis of The World Split Apart: Solzhenitsyn On The WestDocumento52 páginasCrisis of The World Split Apart: Solzhenitsyn On The WestdodnkaAinda não há avaliações
- Preparing For CPHQ .. An Overview of Concepts: Ghada Al-BarakatiDocumento109 páginasPreparing For CPHQ .. An Overview of Concepts: Ghada Al-BarakatiBilal SalamehAinda não há avaliações
- Past Simple Vs Past ContinuousDocumento3 páginasPast Simple Vs Past ContinuousNatalia SalinasAinda não há avaliações
- 21 Tara Mantra-Wps OfficeDocumento25 páginas21 Tara Mantra-Wps OfficeAlteo FallaAinda não há avaliações
- Outline Calculus3Documento20 páginasOutline Calculus3Joel CurtisAinda não há avaliações
- Positive Psychology in The WorkplaceDocumento12 páginasPositive Psychology in The Workplacemlenita264Ainda não há avaliações
- Cosmopolitanism in Hard Times Edited by Vincenzo Cicchelli and Sylvie MesureDocumento433 páginasCosmopolitanism in Hard Times Edited by Vincenzo Cicchelli and Sylvie MesureRev. Johana VangchhiaAinda não há avaliações
- Lightning Protection Measures NewDocumento9 páginasLightning Protection Measures NewjithishAinda não há avaliações
- Nfpa 1126 PDFDocumento24 páginasNfpa 1126 PDFL LAinda não há avaliações
- Neet Question Paper 2019 Code r3Documento27 páginasNeet Question Paper 2019 Code r3Deev SoniAinda não há avaliações
- A Case On Marketing Strategy of Xiaomi IndiaDocumento39 páginasA Case On Marketing Strategy of Xiaomi IndiaSoumyajeet Rout0% (1)
- LPS 1131-Issue 1.2-Requirements and Testing Methods For Pumps For Automatic Sprinkler Installation Pump Sets PDFDocumento19 páginasLPS 1131-Issue 1.2-Requirements and Testing Methods For Pumps For Automatic Sprinkler Installation Pump Sets PDFHazem HabibAinda não há avaliações
- ACCA F2 2012 NotesDocumento18 páginasACCA F2 2012 NotesThe ExP GroupAinda não há avaliações
- SAFE RC Design ForDocumento425 páginasSAFE RC Design ForMarlon Braggian Burgos FloresAinda não há avaliações
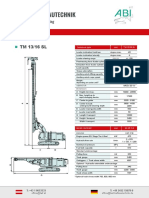
- ABI TM 13 16 SL - EngDocumento1 páginaABI TM 13 16 SL - EngJuan Carlos Benitez MartinezAinda não há avaliações
- DR S GurusamyDocumento15 páginasDR S Gurusamybhanu.chanduAinda não há avaliações
- Sap New GL: Document Splitting - Configuration: ChooseDocumento3 páginasSap New GL: Document Splitting - Configuration: ChooseChandra Sekhar PAinda não há avaliações
- Loop Types and ExamplesDocumento19 páginasLoop Types and ExamplesSurendran K SurendranAinda não há avaliações
- What You Need To Know About Your Drive TestDocumento12 páginasWhat You Need To Know About Your Drive TestMorley MuseAinda não há avaliações
- Getting Started With Citrix NetScalerDocumento252 páginasGetting Started With Citrix NetScalersudharaghavanAinda não há avaliações
- Inventions Over The Last 100 YearsDocumento3 páginasInventions Over The Last 100 YearsHombreMorado GamerYTAinda não há avaliações
- Song LyricsDocumento13 páginasSong LyricsCyh RusAinda não há avaliações
- BÀI TẬP LESSON 7. CÂU BỊ ĐỘNG 1Documento4 páginasBÀI TẬP LESSON 7. CÂU BỊ ĐỘNG 1Yến Vy TrầnAinda não há avaliações
- 160kW SOFT STARTER - TAP HOLE 1Documento20 páginas160kW SOFT STARTER - TAP HOLE 1Ankit Uttam0% (1)
- Chapter 20 AP QuestionsDocumento6 páginasChapter 20 AP QuestionsflorenciashuraAinda não há avaliações