Escolar Documentos
Profissional Documentos
Cultura Documentos
An Algorithm To Detect and Terminate Orphan Process in A Distributed System
Enviado por
TJPRC PublicationsTítulo original
Direitos autorais
Formatos disponíveis
Compartilhar este documento
Compartilhar ou incorporar documento
Você considera este documento útil?
Este conteúdo é inapropriado?
Denunciar este documentoDireitos autorais:
Formatos disponíveis
An Algorithm To Detect and Terminate Orphan Process in A Distributed System
Enviado por
TJPRC PublicationsDireitos autorais:
Formatos disponíveis
International Journal of Computer Science Engineering
and Information Technology Research (IJCSEITR)
ISSN(P): 2249-6831; ISSN(E): 2249-7943
Vol. 4, Issue 6, Dec 2014, 15-22
TJPRC Pvt. Ltd.
AN ALGORITHM TO DETECT AND TERMINATE ORPHAN PROCESS IN A
DISTRIBUTED SYSTEM
LIMI KALITA
Research Scholar, Department of Computer Science and Engineering, Assam Down Town University
Guwahati, Assam, India
ABSTRACT
Orphans in the distributed system waste system resources by holding these for completing the unwanted
computations. Many ways are put forward to detect and kill orphans in the distributed system. The algorithm which is
proposed in this paper will detect and kill the orphan process after regressive connection testing between server and client.
To detect and kill orphan process IP address of the particular client which is disconnected due to some unavoidable
circumstances and the PIN (Process Identification Number) of the process which was requested by the client which is no
longer connected to the server are used. Server will send kill command to particular process which was requested by the
client which is no more connected to the server and hence orphan process is detected and killed.
KEYWORDS: Orphan Process, Client Process, Server Process, Test Connection, Kill Command, PIN
INTRODUCTION
Orphan Process
An orphan process is nearly the same thing we see in the real world. Orphan means someone whose parents are
dead. The same way orphan process is a child process whose parent process is dead, that means the parent is either
terminated, killed or aborted but the child process is still alive. A process can be orphaned unintentionally, such as when
the parent process terminates or crashes. A process may also be intentionally orphaned so that it becomes detached from
the user's session and left running in the background; usually to allow a long-running job to complete without further user
attention, or to start an indefinitely running service.
Disadvantages of Orphan Process in a Distributed System
Orphan process is harmful for the system because they utilize resources while they are in the system and can
potentially leave a server starved for resources. Having too many orphan processes can hang up a system. So, orphan
processes are unwanted computations executing either on behalf of aborted and crashed processes or even the
communication link between the client and server may fail. Apart from these failures, there may be hardware and software
failures, database corruption, memory mismanagement etc. and they need to be dealt with. They are undesirable because
they squander system resources, increasing computational costs, wastage of CPU time, memory, databases, creates
deadlock by holding locks/resources needed by non-orphans, and produces inconsistent data etc.
Orphan process also creates havoc in a persons daily life [1]. Consider a scenario where we are visiting an ATM
to withdraw money. So we insert the card and enter the PIN, then press Enter followed by the selection of transaction etc.
But due to some communication failures or any technical/mechanical/power failures, the ATM fails to dispense the money.
www.tjprc.org
editor@tjprc.org
16
Limi Kalita
And the worst part of this situation is that the intended cash has been deducted from the account without dispensing the
intended withdrawal at the user end. This situation has been created due to orphans. So orphan process should be detected
and killed followed by their birth.
RELATED WORKS
Nelsons Approaches
Nelson proposed four approaches for termination of orphans. They are Extermination, Reincarnation, Gentle
reincarnation, Expiration.
Extermination: In the extermination [4], before a client sends an RPC message, it makes a log entry telling what
it is about to do. The log is kept on disk or some other medium that survives crashes. After reboot, the log is
checked and the orphan is explicitly killed off. Here, the killing of orphan is done only after the rebooting of the
parent process that made the remote call. Until then, the orphan is active at the server site, just because the fact
that the server processes do not know the current status of the parent process that made the RPC to get some
services from the server process. Here the client sends the same request twice and gets the results back. Both
replies come back while resuming the client after crash. This type of scenario is not a promising one and it makes
data in an inconsistent state and the system an unreliable one.
Reincarnation: In the case of reincarnation [4], the RPCs do not record in the log; instead divide time up into
sequentially numbered epochs. When a client reboots, it broadcasts a message to all machines declaring the start
of a new epoch. When such broadcast comes in, all remote computations on behalf of that client are killed. When
they report back, their replies will contain an obsolete epoch number making them easy to detect. Here the client
sends epoch broadcast throughout the system and the server receives it regardless of the fact that it is meant for it
or not. The reply to the client is transmitted by the server if any RPC is there on behalf of the client.
Gentle Reincarnation: Another method put forward by Nelson called gentle reincarnation [4] which is slightly
different from the above method. The protocol works as follows, when epoch broadcast comes in, each machine
checks to see if it has any remote computations, and if so, tries to locate their owner. The computation is killed
only if the owner of a particular computation cannot be found.
Expiration: In this scheme [3], each process is assigned a time limit. If a process is still running when its time
limits arrives, it is simply destroyed. This scheme sets a time bound an orphan can exist before being destroyed.
Unfortunately, the expiration can lead to the destruction of non-orphaned processes.
Global Log and Monitor Approach
Shamsudeen. E and Dr. V. Sundaram[2][4] proposed a global log approach, where orphans are killed immediately
after their birth. In the global log and monitor approach, a global log mechanism is introduced. While an RPC is made by a
process, it is recorded in the global log and it keeps details of all RPCs made by the processes of the distributed system.
The global log keeps updated and if a server makes an RPC, i.e, a nested transaction, it also be recorded in the global log.
The global log also monitors the processes which made RPCs so that node crashes can easily be detected by sending a
token message with a time stamp which revolves round the network and passes through all the clients who participates in
the RPCs. If a node crash occurs, then the monitor associated with the global log immediately sends a message to
corresponding processes where the orphan process and nested orphans being run and kill them off. Here, the orphans are
Impact Factor (JCC): 6.8785
Index Copernicus Value (ICV): 3.0
17
An Algorithm to Detect and Terminate Orphan Process in a Distributed System
killed immediately after the node crash. No waiting until the crash node gets rebooted.
HOW ORPHAN PROCESS EFFECT DISTRIBUTED SYSTEMS?
In a distributed system, the client communicates with the server through remote procedure calls. Here a client
process will request for some services from the server process. The server processes the request and sends it back to the
clients. Meanwhile, if the client process which sent a request aborts or crashes or even communication link between the
client and server fails, but then the server process who is unaware of these failures at the client side will continue to
compute on the request at its end and try to send back the result. But the result is no longer needed just because of the fact
that no client process is waiting for the result. So the server process that was initiated by the failed client process is now
transformed into orphan process.
So orphan process are unwanted computations in distributed systems which create problems like inconsistency of
data[1] and wasting of computer resources usage time just because of the orphan processes continue to compute at the
server site, where the requests of clients are fulfilled, and its results are no longer needed. The resources held by the orphan
processes are remain locked and even it may lead to the problem of deadlock for a certain period of time.
PROPOSED SYSTEM
Design
Network Setup: It is a computer environment where many computers are connected directly or indirectly to
single computer. That single computer is known as server and rest of the computers are known as clients; basically this
type of computer layout is known computer network or setting up computer network. In this kind of scenario clients used
to send request to the server and server takes their request and processes it and then sends the output to the respective
clients.
Methodology
Connect the server with the clients with the help of wired or wireless medium.
Test Connection: To check whether the server is connected properly with the client we can use a simple
technique that is by sending hello messages from server to all clients. Meanwhile if the server receive
acknowledgement from all the clients then we can say that the clients and the server are connected. Make sure that
the clients and the server are connected properly otherwise the proposed algorithm will fail.
Client process: After the successful connection between server and clients, now the clients can request some
service from the server.
Server process: Server is a centralized device which is centrally connected to all the clients in a given network.
Servers main task is to fulfill the requests sent by the clients. Server will process the request and send it back to
the clients. After processing the request server will be waiting for the acknowledgement by the clients.
If acknowledgement is received then there is no orphan process and everything is fine in the given network. And
if the server does not receive acknowledgement within the given period of time then check the connection
between server and client. If connection is successful then server will wait for acknowledgement, and if
connection failed then it is due to orphan process.
www.tjprc.org
editor@tjprc.org
18
Limi Kalita
Since the client is not connected with server anymore and the process which is serving that particular clients
request will become orphan. Now using PIN, server will send the kill command to that particular orphan process which
was created upon the disconnected clients request and hence the orphan process is killed.
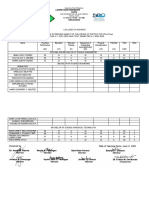
Flowchart to Detect and Terminate Orphan Process in a Distributed System
Figure 1
Server Flowchart
Figure 2
Impact Factor (JCC): 6.8785
Index Copernicus Value (ICV): 3.0
19
An Algorithm to Detect and Terminate Orphan Process in a Distributed System
Step 1: Set up client server platform.
Step 2: Test condition
Step 2.1: Hello message from server to all other clients which are connected to it.
Step 2.2: If clients are active they will reply by acknowledging the HELLO message with client hello message.
Step 2.3: If all clients acknowledge to the servers then test condition succeeded or all clients are active.
Step 3: Clients may request some service from the server, server will process that request and send it back to the
clients, after successful completion of the request the client will send acknowledgement to the server.
If any of the clients does not send ack. to server then that client is not active and request made by that client will
lead to orphan process.
When the client does not ack. to the server, then the server can test the connection between that particular client. If
the test connection failed, then it is proved that the client is no more active and the process created by the client is orphan
process which is in server system. Now the server will kill that orphan process using the PIN (Process Identification
Number) with help of the kill command.
The Proposed Algorithm for Detecting and Terminating Orphan Process in a Distributed System
Server Side Algorithm
www.tjprc.org
editor@tjprc.org
20
Limi Kalita
Client Side Algorithm
Set i, a, b, c as integer;
Set j as Boolean variable (j = true or false);
# Test connection to check whether server is connected to that client or not
Test connection()
{
Send j to server
if(j==true)
Server connected
else if(j==false)
Server not connected
}
#if test connection is successful
send a, b;
# indicate the operation to be performed on this variable and wait for result(c)
# if result received operation successful else send variables again
#if result received
send acknowledgement;
CONCLUSIONS
A distributed system can consist of any number of possible configurations, such as mainframes, personal
computers, workstations, minicomputers, and so on. The goal of distributed computing is to make such a network work as
a single computer. In distributed computing all the computing devices are independent and can operate individually, there
is no problem even if a single system/computing device break down. Distributed computing has many advantages as well
as it has some drawbacks such as node failure, false computation and many more. One of the major drawbacks of
distributed computing is Orphan Process, the algorithm presented in this paper works on principle of connection testing. In
this algorithm before the start of any transaction there is a connection testing phase to check whether the clients are
connected or not if not then no transaction will take place. Only after successful connection transaction will start and
before dispatching the result to the various clients there is again connection testing phase if connection is successful only
then results will be dispatched. If connection testing fails then the server finds out the process which is now orphan
requested by the inactive client from the process table and terminates it by sending kill command. This algorithm
guarantees successful detection and termination of orphan process because each transaction has to go through two
connection testing phase, so there are maximum chances for detection of orphan process.
Impact Factor (JCC): 6.8785
Index Copernicus Value (ICV): 3.0
21
An Algorithm to Detect and Terminate Orphan Process in a Distributed System
REFERENCES
1.
Shamsudeen. E, V. Sundaram, Issues with Orphan Computations in Distributed Computing Systems,
International Journal of Computer Applications (0975 8887) Volume 62 No.20, January 2013
2.
Shamsudeen. E, V. Sundaram, An Approach for Orphan Detection, International journal of computer
applications, Vol.10.No.5, 2010, 28-29.
3.
Shamsudeen. E and Dr. V. Sundaram, A Protocol to Detect and Kill Orphan Processes in Distributed Computer
Systems, IOSR Journal of Computer Engineering (IOSRJCE), Volume 5, Issue 1 (Sep-Oct. 2012).
4.
Shamsudeen.E and Dr. V. Sundaram, Comparison of Global Log and Monitor Approach with Various Orphan
Detection Algorithms, International Journal of Engineering Science Invention, Volume 2 Issue 7, July 2013
5.
Shamsudeen. E, V. Sundaram, Time Stamp Based Global log and monitor approach to handle orphans in
distributed systems, International journal of computer science and network security, Vol 11 No.8, August 2011,
123-125.
6.
http://docs.kde.org/stable/en/kde-workspace/ksysguard/process-controller.html
7.
http://www.cs.unc.edu/~dewan/242/s06/notes/pm/node3.html
8.
http://www.technologyuk.net/computing/operating_systems/process_management.shtml
9.
P. Balakrishna Prasad, Operating systems and systems programming, Second Edition, Scitech, October 2012.
10. Andrew S. Tanenbaum, Distributed Systems-Principles and Paradigms, Prentice-Hall, 2003
11. A. D. Birrell and B.J. Nelson, Implementing remote procedure calls, ACM Trans. Comput. Syst,Vol. 2. no.1,
pp. 39-59, Feb 1984
12. S. K Shrivastava ,On the treatment of Orphans in a Distributed System, 3rd IEEE Symposium on Reliability in
Distributed Software and Database Systems, Florida, October 1983
13. M. P. Herlihy and M. S. McKendry, Time-Stamp based orphan elimination, IEEE Transactions on Software
Engineering, vol. 15, no. 7, pp. 825-831, 1989.
14. Maurice Herlihy, Nancy Lynch, Michael Merritt, and William Weihl, On the correctness of orphan elimination
algorithms. In Proceedings of the 17th Annual IEEE Symposium on Fault-Tolerant Computing, July 1987.
15. Fabio Panzieri, Santosh K. Shrivastava , A Remote Procedure Call Mechanism Supporting Orphan Detection
and Killing Proc. IEEE Transaction on Software Engineering, Vol. 14, No. 1, 1988.
www.tjprc.org
editor@tjprc.org
Você também pode gostar
- The Subtle Art of Not Giving a F*ck: A Counterintuitive Approach to Living a Good LifeNo EverandThe Subtle Art of Not Giving a F*ck: A Counterintuitive Approach to Living a Good LifeNota: 4 de 5 estrelas4/5 (5794)
- Flame Retardant Textiles For Electric Arc Flash Hazards: A ReviewDocumento18 páginasFlame Retardant Textiles For Electric Arc Flash Hazards: A ReviewTJPRC PublicationsAinda não há avaliações
- The Little Book of Hygge: Danish Secrets to Happy LivingNo EverandThe Little Book of Hygge: Danish Secrets to Happy LivingNota: 3.5 de 5 estrelas3.5/5 (399)
- Comparative Study of Original Paithani & Duplicate Paithani: Shubha MahajanDocumento8 páginasComparative Study of Original Paithani & Duplicate Paithani: Shubha MahajanTJPRC PublicationsAinda não há avaliações
- A Heartbreaking Work Of Staggering Genius: A Memoir Based on a True StoryNo EverandA Heartbreaking Work Of Staggering Genius: A Memoir Based on a True StoryNota: 3.5 de 5 estrelas3.5/5 (231)
- The Conundrum of India-China Relationship During Modi - Xi Jinping EraDocumento8 páginasThe Conundrum of India-China Relationship During Modi - Xi Jinping EraTJPRC PublicationsAinda não há avaliações
- Hidden Figures: The American Dream and the Untold Story of the Black Women Mathematicians Who Helped Win the Space RaceNo EverandHidden Figures: The American Dream and the Untold Story of the Black Women Mathematicians Who Helped Win the Space RaceNota: 4 de 5 estrelas4/5 (894)
- 2 31 1648794068 1ijpptjun20221Documento8 páginas2 31 1648794068 1ijpptjun20221TJPRC PublicationsAinda não há avaliações
- The Yellow House: A Memoir (2019 National Book Award Winner)No EverandThe Yellow House: A Memoir (2019 National Book Award Winner)Nota: 4 de 5 estrelas4/5 (98)
- Development and Assessment of Appropriate Safety Playground Apparel For School Age Children in Rivers StateDocumento10 páginasDevelopment and Assessment of Appropriate Safety Playground Apparel For School Age Children in Rivers StateTJPRC PublicationsAinda não há avaliações
- Using Nanoclay To Manufacture Engineered Wood Products-A ReviewDocumento14 páginasUsing Nanoclay To Manufacture Engineered Wood Products-A ReviewTJPRC PublicationsAinda não há avaliações
- Elon Musk: Tesla, SpaceX, and the Quest for a Fantastic FutureNo EverandElon Musk: Tesla, SpaceX, and the Quest for a Fantastic FutureNota: 4.5 de 5 estrelas4.5/5 (474)
- 2 33 1641272961 1ijsmmrdjun20221Documento16 páginas2 33 1641272961 1ijsmmrdjun20221TJPRC PublicationsAinda não há avaliações
- Never Split the Difference: Negotiating As If Your Life Depended On ItNo EverandNever Split the Difference: Negotiating As If Your Life Depended On ItNota: 4.5 de 5 estrelas4.5/5 (838)
- Baluchari As The Cultural Icon of West Bengal: Reminding The Glorious Heritage of IndiaDocumento14 páginasBaluchari As The Cultural Icon of West Bengal: Reminding The Glorious Heritage of IndiaTJPRC PublicationsAinda não há avaliações
- 2 29 1645708157 2ijtftjun20222Documento8 páginas2 29 1645708157 2ijtftjun20222TJPRC PublicationsAinda não há avaliações
- Devil in the Grove: Thurgood Marshall, the Groveland Boys, and the Dawn of a New AmericaNo EverandDevil in the Grove: Thurgood Marshall, the Groveland Boys, and the Dawn of a New AmericaNota: 4.5 de 5 estrelas4.5/5 (265)
- 2 4 1644229496 Ijrrdjun20221Documento10 páginas2 4 1644229496 Ijrrdjun20221TJPRC PublicationsAinda não há avaliações
- 2 52 1642055366 1ijpslirjun20221Documento4 páginas2 52 1642055366 1ijpslirjun20221TJPRC PublicationsAinda não há avaliações
- 2 52 1649841354 2ijpslirjun20222Documento12 páginas2 52 1649841354 2ijpslirjun20222TJPRC PublicationsAinda não há avaliações
- The Emperor of All Maladies: A Biography of CancerNo EverandThe Emperor of All Maladies: A Biography of CancerNota: 4.5 de 5 estrelas4.5/5 (271)
- 2 51 1656420123 1ijmpsdec20221Documento4 páginas2 51 1656420123 1ijmpsdec20221TJPRC PublicationsAinda não há avaliações
- 2 44 1653632649 1ijprjun20221Documento20 páginas2 44 1653632649 1ijprjun20221TJPRC PublicationsAinda não há avaliações
- The Hard Thing About Hard Things: Building a Business When There Are No Easy AnswersNo EverandThe Hard Thing About Hard Things: Building a Business When There Are No Easy AnswersNota: 4.5 de 5 estrelas4.5/5 (344)
- Dr. Gollavilli Sirisha, Dr. M. Rajani Cartor & Dr. V. Venkata RamaiahDocumento12 páginasDr. Gollavilli Sirisha, Dr. M. Rajani Cartor & Dr. V. Venkata RamaiahTJPRC PublicationsAinda não há avaliações
- Team of Rivals: The Political Genius of Abraham LincolnNo EverandTeam of Rivals: The Political Genius of Abraham LincolnNota: 4.5 de 5 estrelas4.5/5 (234)
- Covid-19: The Indian Healthcare Perspective: Meghna Mishra, Dr. Mamta Bansal & Mandeep NarangDocumento8 páginasCovid-19: The Indian Healthcare Perspective: Meghna Mishra, Dr. Mamta Bansal & Mandeep NarangTJPRC PublicationsAinda não há avaliações
- An Observational Study On-Management of Anemia in CKD Using Erythropoietin AlphaDocumento10 páginasAn Observational Study On-Management of Anemia in CKD Using Erythropoietin AlphaTJPRC PublicationsAinda não há avaliações
- 2 51 1651909513 9ijmpsjun202209Documento8 páginas2 51 1651909513 9ijmpsjun202209TJPRC PublicationsAinda não há avaliações
- 2 51 1647598330 5ijmpsjun202205Documento10 páginas2 51 1647598330 5ijmpsjun202205TJPRC PublicationsAinda não há avaliações
- Self-Medication Prevalence and Related Factors Among Baccalaureate Nursing StudentsDocumento8 páginasSelf-Medication Prevalence and Related Factors Among Baccalaureate Nursing StudentsTJPRC PublicationsAinda não há avaliações
- The Unwinding: An Inner History of the New AmericaNo EverandThe Unwinding: An Inner History of the New AmericaNota: 4 de 5 estrelas4/5 (45)
- Effect of Degassing Pressure Casting On Hardness, Density and Tear Strength of Silicone Rubber RTV 497 and RTV 00A With 30% Talc ReinforcementDocumento8 páginasEffect of Degassing Pressure Casting On Hardness, Density and Tear Strength of Silicone Rubber RTV 497 and RTV 00A With 30% Talc ReinforcementTJPRC PublicationsAinda não há avaliações
- The World Is Flat 3.0: A Brief History of the Twenty-first CenturyNo EverandThe World Is Flat 3.0: A Brief History of the Twenty-first CenturyNota: 3.5 de 5 estrelas3.5/5 (2219)
- Effectiveness of Reflexology On Post-Operative Outcomes Among Patients Undergoing Cardiac Surgery: A Systematic ReviewDocumento14 páginasEffectiveness of Reflexology On Post-Operative Outcomes Among Patients Undergoing Cardiac Surgery: A Systematic ReviewTJPRC PublicationsAinda não há avaliações
- 2 67 1648211383 1ijmperdapr202201Documento8 páginas2 67 1648211383 1ijmperdapr202201TJPRC PublicationsAinda não há avaliações
- A Review of "Swarna Tantram"-A Textbook On Alchemy (Lohavedha)Documento8 páginasA Review of "Swarna Tantram"-A Textbook On Alchemy (Lohavedha)TJPRC PublicationsAinda não há avaliações
- The Gifts of Imperfection: Let Go of Who You Think You're Supposed to Be and Embrace Who You AreNo EverandThe Gifts of Imperfection: Let Go of Who You Think You're Supposed to Be and Embrace Who You AreNota: 4 de 5 estrelas4/5 (1090)
- Analysis of Bolted-Flange Joint Using Finite Element MethodDocumento12 páginasAnalysis of Bolted-Flange Joint Using Finite Element MethodTJPRC PublicationsAinda não há avaliações
- Numerical Analysis of Intricate Aluminium Tube Al6061T4 Thickness Variation at Different Friction Coefficient and Internal Pressures During BendingDocumento18 páginasNumerical Analysis of Intricate Aluminium Tube Al6061T4 Thickness Variation at Different Friction Coefficient and Internal Pressures During BendingTJPRC PublicationsAinda não há avaliações
- Vitamin D & Osteocalcin Levels in Children With Type 1 DM in Thi - Qar Province South of Iraq 2019Documento16 páginasVitamin D & Osteocalcin Levels in Children With Type 1 DM in Thi - Qar Province South of Iraq 2019TJPRC PublicationsAinda não há avaliações
- 2 67 1653022679 1ijmperdjun202201Documento12 páginas2 67 1653022679 1ijmperdjun202201TJPRC PublicationsAinda não há avaliações
- The Sympathizer: A Novel (Pulitzer Prize for Fiction)No EverandThe Sympathizer: A Novel (Pulitzer Prize for Fiction)Nota: 4.5 de 5 estrelas4.5/5 (119)
- 2 67 1645871199 9ijmperdfeb202209Documento8 páginas2 67 1645871199 9ijmperdfeb202209TJPRC PublicationsAinda não há avaliações
- 2 67 1645017386 8ijmperdfeb202208Documento6 páginas2 67 1645017386 8ijmperdfeb202208TJPRC PublicationsAinda não há avaliações
- Productivity Software ApplicationsDocumento2 páginasProductivity Software ApplicationsAngel MoralesAinda não há avaliações
- Manual Lymph DrainageDocumento6 páginasManual Lymph DrainageArdelean Dragos100% (1)
- Hildegard Peplau TheoryDocumento28 páginasHildegard Peplau TheoryAlthea Grace AbellaAinda não há avaliações
- (Form2) Certificate of English As Medium of InstructionDocumento2 páginas(Form2) Certificate of English As Medium of InstructionasadAinda não há avaliações
- Extension Cord MakingDocumento3 páginasExtension Cord MakingAaron VillanuevaAinda não há avaliações
- Step-By-Step Analysis and Planning Guide: The Aira ApproachDocumento5 páginasStep-By-Step Analysis and Planning Guide: The Aira ApproachDaniel Osorio TorresAinda não há avaliações
- ENGL-111 / Week 20: Second Quarter Exam / Second Quarter ExamDocumento5 páginasENGL-111 / Week 20: Second Quarter Exam / Second Quarter ExamChristopher Camilo100% (1)
- Different Software Development Models ExplainedDocumento17 páginasDifferent Software Development Models Explainedcmp256Ainda não há avaliações
- Guide To IBM PowerHA SystemDocumento518 páginasGuide To IBM PowerHA SystemSarath RamineniAinda não há avaliações
- Understanding Language VariationDocumento10 páginasUnderstanding Language VariationHesti AnandaAinda não há avaliações
- Sample Nursing Cover LetterDocumento1 páginaSample Nursing Cover LetterFitri Ayu Laksmi100% (1)
- Lesson Plan Biology 6th ClassDocumento4 páginasLesson Plan Biology 6th ClassManju kotturAinda não há avaliações
- The King's CoatDocumento6 páginasThe King's CoatbillcrewsAinda não há avaliações
- 0452 s18 Ms 12Documento14 páginas0452 s18 Ms 12Seong Hun LeeAinda não há avaliações
- Collaboration and Feeling of Flow With An Online Interactive H5P Video Experiment On Viscosity.Documento11 páginasCollaboration and Feeling of Flow With An Online Interactive H5P Video Experiment On Viscosity.Victoria Brendha Pereira FelixAinda não há avaliações
- OmorakaDocumento7 páginasOmorakaDamean SamuelAinda não há avaliações
- Assignment OutlineDocumento3 páginasAssignment OutlineQian Hui LeeAinda não há avaliações
- Attitudes of student teachers towards teaching professionDocumento6 páginasAttitudes of student teachers towards teaching professionHuma Malik100% (1)
- Research Problem and Objectives 2 - 1Documento17 páginasResearch Problem and Objectives 2 - 1kimberly torcino0% (1)
- More 2 Teacher Book PDFDocumento98 páginasMore 2 Teacher Book PDFHuyen Mi100% (2)
- Faculty Screening J.ODocumento2 páginasFaculty Screening J.OIvy CalladaAinda não há avaliações
- Identify Your Type With Jung Typology TestDocumento2 páginasIdentify Your Type With Jung Typology TestRade BarisicAinda não há avaliações
- M1-Lesson 1 Part 2 Context Clue Week 2Documento26 páginasM1-Lesson 1 Part 2 Context Clue Week 2Jeneros PartosAinda não há avaliações
- Project CloseoutDocumento9 páginasProject Closeoutjansen_krystyn06100% (1)
- Group CohesivenessDocumento26 páginasGroup CohesivenessRaviWadhawanAinda não há avaliações
- Sgs Cbe Academy Sri Lanka Training Prospectus 2021 enDocumento10 páginasSgs Cbe Academy Sri Lanka Training Prospectus 2021 enKaisigmazen Quality QwestAinda não há avaliações
- Training Course Information Form: Arab Academy For Science, Technology and Maritime Transport Port Training InstituteDocumento2 páginasTraining Course Information Form: Arab Academy For Science, Technology and Maritime Transport Port Training Instituteخيري محمدAinda não há avaliações
- Lesson Plan 7e's Sea BreezeDocumento3 páginasLesson Plan 7e's Sea BreezeMark Joel Macaya GenoviaAinda não há avaliações
- HIP Online Reporting Template - 9 JUNEDocumento23 páginasHIP Online Reporting Template - 9 JUNEpejabatAinda não há avaliações
- Key Words: Idioms, Idiomatic Expression, Semantic Extension, and SemanticsDocumento13 páginasKey Words: Idioms, Idiomatic Expression, Semantic Extension, and SemanticsCherinet SamAinda não há avaliações