Escolar Documentos
Profissional Documentos
Cultura Documentos
Quizbuilder - Fortify Security Report
Enviado por
TamiiDireitos autorais
Formatos disponíveis
Compartilhar este documento
Compartilhar ou incorporar documento
Você considera este documento útil?
Este conteúdo é inapropriado?
Denunciar este documentoDireitos autorais:
Formatos disponíveis
Quizbuilder - Fortify Security Report
Enviado por
TamiiDireitos autorais:
Formatos disponíveis
Fortify Security Report
Sep 30, 2010
Aleks
Fortify Security Report
Executive Summary
Issues Overview
On Sep 30, 2010, a source code review was performed over the src code base. 124 files, 9053 LOC (Executable) were scanned
and reviewed for defects that could lead to potential security vulnerabilities. A total of 389 reviewed findings were uncovered
during the analysis.
Issues by Fortify Priority Order
349
38
2
Low
High
Critical
Recommendations and Conclusions
The Issues Category section provides Fortify recommendations for addressing issues at a generic level. The recommendations for
specific fixes can be extrapolated from those generic recommendations by the development group.
Copyright 2010 Fortify Software Inc.
Page 2 of 9
Fortify Security Report
Project Summary
Code Base Summary
Code location: C:\Users\Aleks\Documents\Skole\INF226\ezquiz\quizbuilder\trunk\src
Number of Files: 124
Lines of Code: 9053
Build Label: <No Build Label>
Scan Information
Scan time: 02:36
SCA Engine version: 5.9.5.0007
Machine Name: Aleks-Gaming
Username running scan: Aleks
Results Certification
Results Certification Valid
Details:
Results Signature:
SCA Analysis Results has Valid signature
Rules Signature:
There were no custom rules used in this scan
Attack Surface
Attack Surface:
Command Line Arguments:
no.jafu.Quizbuilder.DecryptTool.main
no.jafu.Quizbuilder.EncryptTool.main
no.jafu.Quizbuilder.Quizbuilder.main
no.jafu.Quizbuilder.UserEncrypt.main
no.jafu.Quizbuilder.Gui.Menu.LNFSwitcher.main
File System:
java.io.FileInputStream.FileInputStream
GUI Form:
javax.swing.JPasswordField.getPassword
javax.swing.JPasswordField.getText
javax.swing.text.JTextComponent.getText
Private Information:
Copyright 2010 Fortify Software Inc.
Page 3 of 9
Fortify Security Report
null.null.null
javax.swing.JPasswordField.getPassword
javax.swing.JPasswordField.getText
Java Properties:
java.lang.System.getProperty
Serialized Data:
java.io.ObjectInputStream.readObject
Stream:
java.io.FileInputStream.read
System Information:
null.null.null
java.awt.HeadlessException.getMessage
java.lang.Throwable.getMessage
org.xml.sax.SAXException.getMessage
Web:
java.net.URLConnection.getInputStream
Filter Set Summary
Current Enabled Filter Set:
Security Auditor View
Filter Set Details:
Folder Filters:
If [fortify priority order] contains critical Then set folder to Critical
If [fortify priority order] contains high Then set folder to High
If [fortify priority order] contains medium Then set folder to Medium
If [fortify priority order] contains low Then set folder to Low
Visibility Filters:
Audit Guide Summary
File System Inputs
Hide issues involving file system inputs.
Depending on your system, inputs from files may or may not come from trusted users. AuditGuide can hide issues that are based
on data coming from the file system if it is trusted.
Enable if you trust file system inputs.
Filters:
If taint contains file_system Then hide issue
If taint contains constantfile Then hide issue
Copyright 2010 Fortify Software Inc.
Page 4 of 9
Fortify Security Report
If taint contains stream Then hide issue
If category is file access race condition Then hide issueTaint from Command-Line Arguments
Hide issues involving taint from command-line arguments.
Depending on your system, inputs from command-line arguments may or may not come from trusted users. AuditGuide can hide
issues that are based on data coming from command-line arguments if they are trusted.
Enable if you trust command-line arguments.
Filters:
If taint contains args Then hide issueProperty File Inputs
Hide inputs from properties files.
Depending on your system, inputs from properties files may or may not come from trusted users. AuditGuide can hide issues that
are based on data coming from properties files if they are trusted.
Enable if you trust inputs from properties files.
Filters:
If taint contains property Then hide issueEnvironment Variable Inputs
Hide issues involving environment variable inputs.
Depending on your system, inputs from environment variables may or may not come from trusted users. AuditGuide can hide
issues that are based on data coming from environment variables if they are trusted.
Enable if you trust environment variable inputs.
Filters:
If taint contains environment Then hide issueJ2EE Bad Practices
Hide warnings about J2EE bad practices.
Depending on whether your application is a J2EE application, J2EE bad practice warnings may or may not apply. AuditGuide can
hide J2EE bad practice warnings.
Enable if J2EE bad practice warnings do not apply to your application because it is not a J2EE application.
Filters:
If category contains j2ee Then hide issue
If category is race condition: static database connection Then hide issue
Copyright 2010 Fortify Software Inc.
Page 5 of 9
Fortify Security Report
Results Outline
Overall number of results
The scan found 389 issues.
Vulnerability Examples by Category
Category: Password Management: Empty Password (2 Issues)
Number of Issues
0.00
0.25
0.50
0.75
1.00
1.25
1.50
1.75
2.00
<Unaudited>
Analysis
Not an Issue
Reliability Issue
Bad Practice
Suspicious
Exploitable
Abstract:
Empty passwords can compromise system security in a way that cannot be easily remedied.
Explanation:
It is never a good idea to assign an empty string to a password variable. If the empty password is used to successfully
authenticate against another system, then the corresponding account's security is likely compromised because it accepts an empty
password. If the empty password is merely a placeholder until a legitimate value can be assigned to the variable, then it can
confuse anyone unfamiliar with the code and potentially cause problems on unexpected control flow paths.
Example 1: The code below attempts to connect to a database with an empty password.
...
DriverManager.getConnection(url, "scott", "");
...
If the code in Example 1 succeeds, it indicates that the database user account "scott" is configured with an empty password,
which can be easily guessed by an attacker. Even worse, once the program has shipped, updating the account to use a non-empty
password will require a code change.
Example 2: The code below initializes a password variable to an empty string, attempts to read a stored value for the password,
and compares it against a user-supplied value.
...
String storedPassword = "";
String temp;
if ((temp = readPassword()) != null) {
storedPassword = temp;
}
if(storedPassword.equals(userPassword))
// Access protected resources
...
}
...
If readPassword() fails to retrieve the stored password due to a database error or another problem, then an attacker could trivially
bypass the password check by providing an empty string for userPassword.
Copyright 2010 Fortify Software Inc.
Page 6 of 9
Fortify Security Report
Recommendations:
Always read stored password values from encrypted, external resources and assign password variables meaningful values.
Ensure that sensitive resources are never protected with empty or null passwords.
Starting with Microsoft(R) Windows(R) 2000, Microsoft(R) provides Windows Data Protection Application Programming
Interface (DPAPI), which is an OS-level service that protects sensitive application data, such as passwords and private keys [1].
Tips:
The Fortify Java Annotations FortifyPassword and FortifyNotPassword can be used to indicate which fields and variables
represent passwords.
OpenFromXML.java, line 545 (Password Management: Empty Password)
Sink:
High
Folder
High
Security Features
Empty passwords can compromise system security in a way that cannot be easily
remedied.
OpenFromXML.java:545 VariableAccess: password()
543
544
545
546
547
}
String username = "";
String password = "";
// Dealing with HTTP protocol.
HttpURLConnection connection = (HttpURLConnection) urlConnection;
Fortify Priority:
Kingdom:
Abstract:
Copyright 2010 Fortify Software Inc.
Page 7 of 9
Fortify Security Report
Issue Count by Category
Issues by Category
Poor Error Handling: Overly Broad Catch
System Information Leak
Poor Logging Practice: Use of a System Output Stream
Poor Error Handling: Empty Catch Block
Unreleased Resource: Streams
Password Management: Password in Comment
Poor Error Handling: Overly Broad Throws
Code Correctness: Erroneous String Compare
Dead Code: Expression is Always true
Denial of Service
Code Correctness: Class Does Not Implement equals
Null Dereference
Object Model Violation: Just one of equals() and hashCode() Defined
Dead Code: Unused Field
Password Management: Password in Configuration File
Poor Logging Practice: Logger Not Declared Static Final
Poor Style: Value Never Read
Dead Code: Unused Method
Unchecked Return Value
Insecure Randomness
Password Management: Empty Password
Path Manipulation
Poor Error Handling: Program Catches NullPointerException
Code Correctness: Misspelled Method Name
Missing Check against Null
Poor Style: Non-final Public Static Field
Poor Style: Redundant Initialization
Weak Cryptographic Hash
Copyright 2010 Fortify Software Inc.
88
75
50
30
25
21
20
15
9
6
5
5
5
4
4
4
4
3
3
2
2
2
2
1
1
1
1
1
Page 8 of 9
Fortify Security Report
Issue Breakdown by Analysis
Issues by Analysis
<none>: (389, 100%)
<none>
Copyright 2010 Fortify Software Inc.
Page 9 of 9
Você também pode gostar
- SSL VPN : Understanding, evaluating and planning secure, web-based remote accessNo EverandSSL VPN : Understanding, evaluating and planning secure, web-based remote accessAinda não há avaliações
- OracleDocumento66 páginasOracleAnusha SrsAinda não há avaliações
- CompTia CH7 Host, Data, and Application SecurityDocumento5 páginasCompTia CH7 Host, Data, and Application SecurityVVetoAinda não há avaliações
- Cryptography ModelDocumento142 páginasCryptography ModelHamzah AminAinda não há avaliações
- PDF XML Signture PDFDocumento155 páginasPDF XML Signture PDFAdaikalam Alexander RayappaAinda não há avaliações
- OWASP SCP Quick Reference Guide v1Documento12 páginasOWASP SCP Quick Reference Guide v1shimaasAinda não há avaliações
- Owasp - Microsoft - Threat - Modelling & Threats Models PDFDocumento10 páginasOwasp - Microsoft - Threat - Modelling & Threats Models PDFKaisSlimeniAinda não há avaliações
- Accredited Configuration Engineer (ACE) Exam - PAN-OS 7.0 VersionDocumento12 páginasAccredited Configuration Engineer (ACE) Exam - PAN-OS 7.0 VersionBillAlwaysAinda não há avaliações
- Udemy Dump 2Documento111 páginasUdemy Dump 2Gani RKAinda não há avaliações
- Secure Coding Guidelines For JavaDocumento42 páginasSecure Coding Guidelines For JavaVs VadivelanAinda não há avaliações
- Secure Coding Quick Reference-Version1bDocumento11 páginasSecure Coding Quick Reference-Version1bJagdish annayaAinda não há avaliações
- IPT 102 Module 2Documento5 páginasIPT 102 Module 2Roel PialesAinda não há avaliações
- Java Security, Part 1: Crypto BasicsDocumento26 páginasJava Security, Part 1: Crypto BasicsJamyJamesAinda não há avaliações
- Test - Accredited Configuration Engineer (ACE) Exam - PAN-OS 7.0 VersionDocumento13 páginasTest - Accredited Configuration Engineer (ACE) Exam - PAN-OS 7.0 VersiongustavoAinda não há avaliações
- Secure Configuration Guide For Oracle E-Business Suite Release 12Documento68 páginasSecure Configuration Guide For Oracle E-Business Suite Release 12Kinjal NandyAinda não há avaliações
- Apple SecureCodingGuideDocumento123 páginasApple SecureCodingGuidePhilli OneromAinda não há avaliações
- Tech Interviews: Windows Server 2003 Interview and Certification QuestionsDocumento6 páginasTech Interviews: Windows Server 2003 Interview and Certification QuestionsSaurabh GugnaniAinda não há avaliações
- Firewall Leak TestingDocumento6 páginasFirewall Leak TestingdasxaxAinda não há avaliações
- By Ken Huang and James Hewitt, CGI NYS Cyber Security Conference 2010Documento41 páginasBy Ken Huang and James Hewitt, CGI NYS Cyber Security Conference 2010Ken HuangAinda não há avaliações
- Securing Application Deployment with Obfuscation and Code Signing: How to Create 3 Layers of Protection for .NET Release BuildNo EverandSecuring Application Deployment with Obfuscation and Code Signing: How to Create 3 Layers of Protection for .NET Release BuildAinda não há avaliações
- Srs DST: Casting From ToDocumento37 páginasSrs DST: Casting From Tog007adam759Ainda não há avaliações
- Module 9: Designing Security SpecificationsDocumento56 páginasModule 9: Designing Security Specificationsapi-3775463Ainda não há avaliações
- It's Your Data - Are You Sure It's Safe?: Team Mag 5Documento14 páginasIt's Your Data - Are You Sure It's Safe?: Team Mag 5Sami Lo'o Lo'oAinda não há avaliações
- Comptia Ca1-001Documento160 páginasComptia Ca1-001Nelson VelascoAinda não há avaliações
- AZURE AZ 500 STUDY GUIDE-1: Microsoft Certified Associate Azure Security Engineer: Exam-AZ 500No EverandAZURE AZ 500 STUDY GUIDE-1: Microsoft Certified Associate Azure Security Engineer: Exam-AZ 500Ainda não há avaliações
- Security PDFDocumento11 páginasSecurity PDFElja MohcineAinda não há avaliações
- Asterisx Limpio Results - Fortify Security ReportDocumento46 páginasAsterisx Limpio Results - Fortify Security ReportXiamir LuquezAinda não há avaliações
- Assignment 2: CS 458/658 Computer Security and Privacy Winter 2010Documento6 páginasAssignment 2: CS 458/658 Computer Security and Privacy Winter 2010randolmAinda não há avaliações
- Oracle Metalink Hacking UsDocumento8 páginasOracle Metalink Hacking UsoumarousAinda não há avaliações
- Secure Coding Practices For: White PaperDocumento15 páginasSecure Coding Practices For: White Papererica jayasunderaAinda não há avaliações
- Securing Windows Server 2008: Prevent Attacks from Outside and Inside Your OrganizationNo EverandSecuring Windows Server 2008: Prevent Attacks from Outside and Inside Your OrganizationAinda não há avaliações
- Test - Accredited Configuration Engineer (ACE) Exam - PAN-OS 7.0 VersionDocumento13 páginasTest - Accredited Configuration Engineer (ACE) Exam - PAN-OS 7.0 VersiongustavoAinda não há avaliações
- PCI DSS-Payment Card Industry Data Security Standard: Alfredo Valenza Master Principal Sales Consultant - Oracle ItaliaDocumento43 páginasPCI DSS-Payment Card Industry Data Security Standard: Alfredo Valenza Master Principal Sales Consultant - Oracle ItaliaAhmedAliyevAinda não há avaliações
- Back Door Into Java EE Application ServersDocumento17 páginasBack Door Into Java EE Application ServerssmjainAinda não há avaliações
- Programming For SecurityDocumento25 páginasProgramming For SecurityaloshbennettAinda não há avaliações
- Hacking and Securing OracleDocumento43 páginasHacking and Securing OracleAntonio Kalet Apaza TorresAinda não há avaliações
- 20BCA1335 Ashish-Yadav AssinmentDocumento4 páginas20BCA1335 Ashish-Yadav AssinmentimyadashuAinda não há avaliações
- Networking Basics and TerminologyDocumento25 páginasNetworking Basics and Terminologyنكت مضحكةAinda não há avaliações
- Client Risk Report Sample ReportDocumento17 páginasClient Risk Report Sample ReportFrancky MarolopAinda não há avaliações
- Why Care About Database Security?Documento14 páginasWhy Care About Database Security?dnedevAinda não há avaliações
- Test - Accredited Configuration Engineer (ACE) Exam - PAN-OS 7.0 VersionDocumento9 páginasTest - Accredited Configuration Engineer (ACE) Exam - PAN-OS 7.0 VersiongustavoAinda não há avaliações
- Summer Internship ProjectDocumento15 páginasSummer Internship ProjectadityaAinda não há avaliações
- Network SecurityDocumento59 páginasNetwork SecurityAhmad AliAinda não há avaliações
- Windows 10Documento2.148 páginasWindows 10Gabriela MoralesAinda não há avaliações
- OWASP Top 10 Exhaustive EditionDocumento29 páginasOWASP Top 10 Exhaustive EditionKumar SauravAinda não há avaliações
- IT276 FALL 2011 Midterm Student Version LittleDocumento7 páginasIT276 FALL 2011 Midterm Student Version LittleChuck LittleAinda não há avaliações
- Java Feels SecureDocumento4 páginasJava Feels SecurethangmleAinda não há avaliações
- PDF Application SecurityDocumento5 páginasPDF Application SecuritystudydatadownloadAinda não há avaliações
- Self Service Procurement Punchout ChecklistDocumento1 páginaSelf Service Procurement Punchout ChecklistSrinivasa Rao AsuruAinda não há avaliações
- EmctlDocumento23 páginasEmctlmastertdsiAinda não há avaliações
- Institute of Road and Transport Technology: ErodeDocumento13 páginasInstitute of Road and Transport Technology: ErodeRishikaa RamAinda não há avaliações
- Dsouza Fortify 07 ReportDocumento10 páginasDsouza Fortify 07 ReportPrasadAinda não há avaliações
- OWASP Top Ten Proactive Controls v3Documento110 páginasOWASP Top Ten Proactive Controls v3Avinash KumarAinda não há avaliações
- NSE2 PsalinasDocumento48 páginasNSE2 PsalinasPablo SalinasAinda não há avaliações
- Web Security ThreatsDocumento22 páginasWeb Security ThreatsScliartArtAinda não há avaliações
- Practicedump: Free Practice Dumps - Unlimited Free Access of Practice ExamDocumento7 páginasPracticedump: Free Practice Dumps - Unlimited Free Access of Practice Examram4uintpt2Ainda não há avaliações
- Java Attendance ManagementDocumento12 páginasJava Attendance Managementsakshamjain5gAinda não há avaliações
- Ajp MP 2Documento15 páginasAjp MP 2LalitAinda não há avaliações
- Doctor Appointment PortalDocumento104 páginasDoctor Appointment PortalMohamed Ahmed AbdiAinda não há avaliações
- JDK Installation TutorialDocumento43 páginasJDK Installation TutorialJacob RyanAinda não há avaliações
- Cse Vii Java and J2EE (10cs753) SolutionDocumento60 páginasCse Vii Java and J2EE (10cs753) SolutionAkilesh Parivar100% (1)
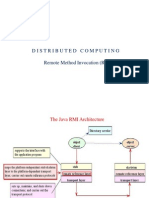
- Distributed Computing Remote Method Invocation (RMI)Documento16 páginasDistributed Computing Remote Method Invocation (RMI)Venu Gopal PAinda não há avaliações
- Self Study Guidelines To JAVA SEDocumento4 páginasSelf Study Guidelines To JAVA SEAnjana Jayasekara100% (1)
- All PDFDocumento40 páginasAll PDFCharli PatilAinda não há avaliações
- Java Aptitude Inreview Questions N AnswersDocumento125 páginasJava Aptitude Inreview Questions N Answersnikeld89100% (1)
- WTL Assignment No.4Documento3 páginasWTL Assignment No.4Sujit KhandareAinda não há avaliações
- Cq5 Guide ArchitectDocumento22 páginasCq5 Guide ArchitectGeorge SmithAinda não há avaliações
- Log 1Documento272 páginasLog 1Muhar DaniAinda não há avaliações
- A Project Synopsis Animation Using Applet: Doraemon: Submitted byDocumento22 páginasA Project Synopsis Animation Using Applet: Doraemon: Submitted byDS55Sahil JadhavAinda não há avaliações
- Introduction To Programming Using Java, Part IIDocumento374 páginasIntroduction To Programming Using Java, Part IIohyeah08Ainda não há avaliações
- CSE 219 Computer Science III: Code ProfilingDocumento25 páginasCSE 219 Computer Science III: Code ProfilingZeb AslamAinda não há avaliações
- CH 5. Exception Handling & MultithreadingDocumento60 páginasCH 5. Exception Handling & MultithreadingMegha GuptaAinda não há avaliações
- Informix-4GL and The Informix Toolset: ObjectivesDocumento12 páginasInformix-4GL and The Informix Toolset: ObjectivesRodolfo J. PeñaAinda não há avaliações
- Guide To OSPLDocumento74 páginasGuide To OSPLtestuzermanAinda não há avaliações
- 9 0 With 8 98 Standalone Installation Rev1Documento35 páginas9 0 With 8 98 Standalone Installation Rev1gmanikanta5Ainda não há avaliações
- OCP Java SE 11 Study PlanDocumento2 páginasOCP Java SE 11 Study PlanSaidiAinda não há avaliações
- Mockito - First Application - TutorialspointDocumento5 páginasMockito - First Application - TutorialspointIndar GuptaAinda não há avaliações
- Detailed Java RoadMapDocumento8 páginasDetailed Java RoadMapdipeshkumarchaudhary7Ainda não há avaliações
- Online Insurance Management SystemDocumento45 páginasOnline Insurance Management SystemRohit VkAinda não há avaliações
- Are Ethics Just Business PretenceDocumento3 páginasAre Ethics Just Business Pretencenick_KGECAinda não há avaliações
- 6ov PDFDocumento86 páginas6ov PDFkatfy1Ainda não há avaliações
- Oracle 11i and R12 DifferencesDocumento58 páginasOracle 11i and R12 DifferencesSrihari GullaAinda não há avaliações
- Lindo Api 12.0Documento6 páginasLindo Api 12.0Muhammad Ro'yun NuhaAinda não há avaliações
- Module 2-Java Servlets: I) IntroductionDocumento11 páginasModule 2-Java Servlets: I) IntroductionAkshay ChinnanAinda não há avaliações
- Palamida DataSheet Enterprise EditionDocumento4 páginasPalamida DataSheet Enterprise EditionKate EbneterAinda não há avaliações
- Tourism Management 1 Project Report On TDocumento12 páginasTourism Management 1 Project Report On TgggAinda não há avaliações