Escolar Documentos
Profissional Documentos
Cultura Documentos
RFID - Broad Band Antenna
Enviado por
HarrakMohamedTítulo original
Direitos autorais
Formatos disponíveis
Compartilhar este documento
Compartilhar ou incorporar documento
Você considera este documento útil?
Este conteúdo é inapropriado?
Denunciar este documentoDireitos autorais:
Formatos disponíveis
RFID - Broad Band Antenna
Enviado por
HarrakMohamedDireitos autorais:
Formatos disponíveis
the new broadband antenna Tag in RFID UHF
passif communication
El Harrak Hajri Mohammad, Asselman Adel
Departement of physics
Science faculty, Abdelmalek Essaadi University.
Tetuan, Morroco
E_mail : harrakmed@gmail.com, asselman57@gmail.com
Abstract---The functioning and use of Radio frequency
Identification (RFID) is growing rapidly across many different
industries. The technology is not only in traditional applications
such as asset tracking, inventory tracking but also in security
services such as electronic passports and RFID enabled credit
cards. However RFID technology also raises number of
concerns regarding privacy, security and law enforcement. In
this paper the basic concepts of RFID technology are
introduced, and also the associated security issues and threats in
using This technology are discussed.
The first goal of writing this paper is to deliver a better
understanding of basics of RFID and its applications and
security issues.[1]
Each tag contains a unique identity code. An RFID reader
emits a low-level radio frequency magnetic field that
energizes the tag. The tag responds to the readers query and
announces its presence via radio waves, transmitting its
unique identification data. This data is decoded by the reader
and passed to the local application system via middleware.
The middleware acts as an interface between the reader and
the RFID application system. The system will then search
and match the identity code with the information stored in the
host database or backend system.
the second goal is to Design and simulate for a broadband
antenna for RFID communication near and far field
Keywords: RFID, Tag, middleware, antenna
I.
Introduction
The source of RFID technology lies in the 19th century
when luminaries of that era made great scientific advances in
electromagnetism, Radio frequency Identification technology
is automatic identification technology that uses radio signals
to identify ,track variety of objects including people, vehicles
goods and assets without the need for contact or line of sight
contact. As this technology is best candidate in place of
barcode.
Fig1. RFID UHF system historique
At the same time it is leaving many privacy and security
issues lets discuss the in the next part of the paper.[2]
II.Working of RFID System
An integrated circuit for modulating and demodulating
radio signals and performing other functions. An antenna for
receiving and transmitting the signal.
Systems that make use of RFID technology are composed
of three basic elements: An RFID tag, or transponder, that
carries object-identifying data. An RFID tag reader, or
transceiver, that reads and writes tag data. A back-end
database, that stores records associated with tag contents As
shon in the fig 2
Fig. 2. RFID system components
A.Communication
The communication process between the reader and tag is
managed and controlled by one of several protocols, such as
the ISO 15693 and ISO 18000-3 for HF or the ISO 18000-6,
and EPC for UHF. Basically what happens is that when the
reader is switched on, it starts emitting a signal at the selected
frequency band (typically 860 - 915MHz for UHF or
13.56MHz for HF) . Any corresponding tag in the vicinity of
the reader will detect the signal and use the energy from it to
wake up and supply operating power to its internal circuits.
Once the Tag has decoded the signal as valid, it replies to the
reader, and indicates its presence by modulating (affecting)
the reader field.[2]
B RFID Tags
An RFID tag is an object that can be applied to or
incorporated into a product, animal, or person for the purpose
of identification and tracking using radio waves.
Some tags can be read from several meters away and
beyond the line of sight of the reader. Most tags carry a plain
text inscription and a barcode as complements for direct
reading and for cases of any failure of radio frequency
electronics.
The tags contain electronically stored information. .Tags
can be attached to any item, goods, and objects to track or
value the objects.[3]
Page 1
Fig.4 RFID Applications
F.RFID middleware components
Fig2. RFID Tags example
Tags are basically classified in two types Passive Tags
Passive Tags
Do not require power. Draws from Interrogator field
Lower storage capacities(few bits to 1 KB)
Shorter read ranges(4 Inches to 15 feet)
Usually Write once Read many /Read Only tags
Cost around 25 cents to few dollars
Active Tags
A RFID middleware is the interface that sits between the
RFID hardware and RFID applications. It provides the
following advantages:
It hides the RFID hardware details from the
applications;
It handles and processes the raw RFID data before
passing it as aggregated events to the applications;
It provides an application level interface for
managing RFID readers and querying the RFID
data.
Manufacturing and Processing
Battery powered
Higher Storage capacities(512 KB)
Longer read range(300 feet)
D. RFID Readers
Reader Functions
Remotely power tags
Establish a bidirectional data link
Inventory tags filter results
Communicate with networked servers
Can read 100-300 tags per second
Readers can be at a fixed point such as entrance
exit
Readers can also be mobile/ hand held
E. RFID Middleware
Inventory and production process monitoring
Warehouse order fulfillment Supply Chain
Management
Inventory tracking systems
Logistics management Retail
Inventory control and customer insight
Auto checkout with reverse logistics Security
Access control
Counterfeiting and Theft control/prevention
Location Tracking
Traffic movement control and parking management
Wildlife/Livestock
monitoring and
tracking
Location Tracking
Traffic movement control and parking management
Wildlife/Livestock monitoring and tracking
The middleware refers broadly to software or devices that
connect RFID readers and the data they collect, to enterprise
information systems. RFID middleware helps making sense
of RFID tag reads, applies filtering, formatting and logic to
tag data captured by a reader, and provides this processed
data to back-end applications (Burnell, 2008). RFID
middleware serves in managing the flow of data between tag
readers and enterprise applications, and is responsible for the
quality, and therefore usability of the information. It provides
readers connectivity, context-based filtering and routing, and
enterprise / B2B integration [4]
Fig. 5. RFID middleware components
III-Privacy and Security issues
Page 2
Many concerns have been expressed over the security and
privacy of RFID systems. Traditional applications, like
largeasset tracking, were typically closed systems where tags
did not contain sensitive information. However, as more
consumer applications are developed, security, and especially
privacy, will become important issues. Much work has
recently focused on issues of RFID security and
privacy.[2][5]
Denial of Service It is an attempt to make a machine or
network resource unavailable to its intended users Spoofing
In addition to threats of passive eavesdropping and tracking,
an infrastructure dependent on RFID tags may be susceptible
to tag spoofing. There are two kinds of security issues about
spoofing. One is theft and the other is counterfeiting which
are discussed as follows.
Theft By spoofing valid tags, a thief could fool automated
checkout or security systems into thinking a product still on a
shelf. Alternatively, a thief could rewrite or replace tags on
expensive items with spoofed data from cheaper items.
Saboteurs could disrupt supply chains by disabling or
corrupting a large batch of tags.
A.Eavesdropping
As organizations adopt and integrate RFID into their
supply chain and inventory control infrastructure, more and
more sensitive data will be entrusted on RFID tags. As these
tags inevitably end up in consumer hands, they could leak
sensitive data or be used for tracking individuals. An attacker
able to eavesdrop from long range could possibly spy on a
passive RFID system.
RFID technology operates through radio, so
communication can be surreptitiously overheard. In Ref. [35],
the possible distances at which an attacker can listen to the
messages exchanged between a tag and a reader are
categorized (see Figure 6).
Forward channel eavesdropping range: In the
reader-to-tag channel (forward channel) the reader
broadcasts a strong signal, allowing its monitoring
from a long distance.
Backward channel eavesdropping range: The
signal transmitted in the tag-to-reader (backward
channel) is relatively weak, and may only be
monitored in close proximity to the tag.
Operating range: The read ranges shown in Section
2.3.1 are the operating read range using
salesstandard readers.
Malicious scanning range: An adversary may build
his own reader-archiving longer read ranges,
especially if regulations about radio devices are not
respected.A conversation between a reader and a tag
can be eavesdropped over a greater distance than is
possible with direct communication.
For example, tags compliant to ISO 14443 have a reading
distance of around 10cm (using standard equipment).
However, Kfir et al. showed that this distance can be
increased to 55cm employing a loop antenna and signal
processing
FI 6 Eavesdropping range classification.
B.Tag Cloning
Rather than simply trying to steal data from RFID tags,
adversaries might try to imitate tags to readers. This is a
threat to RFID systems currently being used for access.
Intruder can steal the content of tag and similar tag can
develop to imitate the behavior of original tag this we call as
cloning of tag this he can use it further misuse create
nuisance to users. Hence now RFID based systems are facing
huge difficulties. In future applications like RFID based
passport applications cloning is a more serious threat.[3]
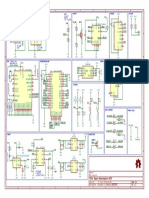
IV- ULB Antenne large bande pour la communication
RFID en champ proche et lointain
In this work, we present the design of a new antenna
passive UHF RFID Tag for communications in near and far
field. This antenna is matching for a chip and optimized for
operation in near field. The minimum bandwidth of the
measured Tag antenna is 140 MHz. It covers the entire UHF
band (820-960 MHz). In our simulations, we used sequence
impedance of the chip given by the manufacturer and that of
the measured impedance.
A.Conception de lantenne propose
1.) Utilisation de la puce 1 : Impdance donne dans la
fiche technique
The structure that we propose for Tag antenna is shown in
Figure 5. The antenna consists of a rectangular adaptation
loop, fueling a gradual meander dipole.
Fig 5. Meander antenna proposed
The geometrical dimensions of the antenna are given in
mm in box 1. The antenna is simulated on a substrate
Rogers Duroid RT / 5880 thickness H = 0787 mm, constant
relative dielectric r = 2.2 and loss tangent tan = 0.009, with
an overall size of 77 14 mm2.
Page 3
Table 1. Antenna parameters meander proposed
The chip used in this design is of type Alien Higgs-3
RFID IC [6]. Fixed values of resistance and its parallel
capacity provided by thedatasheet was 1500 and 0.85 pF.
First, we have optimized the structuree antenna to a 868 MHz
resonance frequency, using these fixed values of impedance,
ie Z c datasheet =(30.4 -j208) . This allows us to see that the
antenna impedance is Z a=(30.4 +j208) to allow
maximum power transfer from the antenna to the chip. The
simulated reflection coefficient in this case is shown in
Figure 6, where we note a S11 14.2 dB at 867.7 MHz
corresponding impedance is 26.09 + J158 .7 . As we work
in the European RFID band (865-868MHz), we had to make
a compromise by adjusting L3 = 16 mm and we could thus
obtain a better reflection coefficient of 21.9 dB at a frequency
of 867.7 MHz.
Figure 8. Tag the reflection coefficient for different values of L1
To minimize the uncertainties due to the manufacturing
Figure 6. Reflection coefficient of the meander antenna
2). Impdance mesure
In this case, we use a measured impedance of the chip,
this one is different because it has been modified by the
frequency and the power received by the chip. OSL a
calibration procedure is used to extract the impedance values
of this chip. The measured impedance [7] of the chip is then
Zc = (26 - J163) W measured. Because this impedance is
different from the first chip 1, we adjusted the rectangular
loop to obtain the adaptation between the antenna and the tag
chip for a better power transfer.
For this, we have maintained constant L1 = 24.6 mm and
we varied L3. Our simulation results, shown in Figure 4,
shows that the best reflection coefficient obtained is 38.3 dB
at a frequency of 852.5 MHz and L3 = 19mm.
process, as well as the chip of the tag antenna and due to the
proximity of metal objects, liquids or human bodies, that can
change the frequency behavior of our RFID system and
impair operation, it is always better to have a tag antenna
covering the entire UHF RFID band, that is to say from 860
to 960 MHz, to ensure at least partial operation. That is why
we have made sure that the design of our antenna is best
reflection losses 10 dB at the working frequency. So we
could get a S11> 10dB approximately 155 MHz around 868
MHz, e 17.8%, from 730 to 885MHz.
The antenna has a gain meander of 1.5 dB. Del'antenne
the 3D radiation pattern is shown in Figure 5.The antenna has
a gain meander of 1.5 dB. The del'antenne 3D radiation
pattern is shown in Figure 9.
Figure 7. Tag reflection coefficient of variation with L3
As the impedance matching, and thus the reflection
Fig 9 Diagramme de rayonnement 3D de lantenne mandre
coefficient, strongly depends on the different geometrical
parameters of the antenna, we also set L3 = 19 mm and L1 is
The current distribution of our antenna is shown in Figure
10.
varied. Our simulation results shown in Figure 8, show that
improved 37.7 dB reflection coefficient is obtained at a
frequency of 857.6 MHz for L1 = 24mm, and the
Page 4
Fig10. Antenna current distributor 867 MHz (z = 0 mm)
The interest in UHF RFID systems is that they can also be
used in near field communication applications. Tag antennas
used for far-field communications (FFC) can not be operated
well in the near field (NFC). However, this may be achieved
by designing antenna structures Tag for generating and
radiating a strong magnetic field sufficient.
V Conclusion
In the present context RFID tags revolutionize society
with their wonderful applications; we must understand their
risks g
also. Implementing ubiquitous network connectivity in
society will demand a close examination of personal privacy
from both the technical and social and aspects. The privacy
problems raised by their are serious enough to demand a
comprehensive and effective technique that can ensure user
privacy while retaining their benefits As we go with
technology there will be certain advantages and
disadvantages Understanding RFID security today will aid in
development of secure ubiquitous computing systems in the
future. Our job is to provide better security features for the
stakeholders to make this technology popular and user
friendly. This is my little effort learn the basics of RFID
systems.
REFERENCES.
[1] RFID (Radio Frequency Identification): Principles and
Applications,Stephen A. Weis MIT CSAIL
[2] RFID SECURITY The Government of the HongKong
Special Administrative Region February 2008
[3] RFID : Technology and Applications by Sridhar Iyer IIT
Bombay
[4][RFID Middleware Design and Architecture Mehdia Ajana El
Khaddar1, Mohammed Boulmalf3Hamid arroud2 and Mohammed
Elkoutbi1 1SI2M Lab, ENSIAS 2WML Lab, Alakhawayn
University in Ifrane Canadian University of Dubai 1,2Morocco
3UAE]
[5] Security challenges for RFID key applications Thomas
Hollstein, Manfred Glesner; TU Darmstadt Ulrich Waldmann;
Fraunhofer SIT Darmstadt Henk Birkholz, Karsten Sohr; Universitt
Bremen
[6] Higgs 3 UHF RFID Tag IC, lien:
http://www.alientechnology.com/wp
content/uploads/Alien Technology-Higgs-3-ALC-360.pdf .
[7] J.-H. Cho, H.-W. Son, S.-H. Jeong, W.-K. Choi, C.-W.Park, A
*Flexible, Wideband RFID Tag Antenna for Metallic Surfaces, in
Proc. APSURSI, Jul. 2012, pp.1-2.
Page 5
Você também pode gostar
- The Subtle Art of Not Giving a F*ck: A Counterintuitive Approach to Living a Good LifeNo EverandThe Subtle Art of Not Giving a F*ck: A Counterintuitive Approach to Living a Good LifeNota: 4 de 5 estrelas4/5 (5794)
- The Yellow House: A Memoir (2019 National Book Award Winner)No EverandThe Yellow House: A Memoir (2019 National Book Award Winner)Nota: 4 de 5 estrelas4/5 (98)
- Hidden Figures: The American Dream and the Untold Story of the Black Women Mathematicians Who Helped Win the Space RaceNo EverandHidden Figures: The American Dream and the Untold Story of the Black Women Mathematicians Who Helped Win the Space RaceNota: 4 de 5 estrelas4/5 (895)
- The Hard Thing About Hard Things: Building a Business When There Are No Easy AnswersNo EverandThe Hard Thing About Hard Things: Building a Business When There Are No Easy AnswersNota: 4.5 de 5 estrelas4.5/5 (344)
- The Little Book of Hygge: Danish Secrets to Happy LivingNo EverandThe Little Book of Hygge: Danish Secrets to Happy LivingNota: 3.5 de 5 estrelas3.5/5 (399)
- The Emperor of All Maladies: A Biography of CancerNo EverandThe Emperor of All Maladies: A Biography of CancerNota: 4.5 de 5 estrelas4.5/5 (271)
- Devil in the Grove: Thurgood Marshall, the Groveland Boys, and the Dawn of a New AmericaNo EverandDevil in the Grove: Thurgood Marshall, the Groveland Boys, and the Dawn of a New AmericaNota: 4.5 de 5 estrelas4.5/5 (266)
- Never Split the Difference: Negotiating As If Your Life Depended On ItNo EverandNever Split the Difference: Negotiating As If Your Life Depended On ItNota: 4.5 de 5 estrelas4.5/5 (838)
- A Heartbreaking Work Of Staggering Genius: A Memoir Based on a True StoryNo EverandA Heartbreaking Work Of Staggering Genius: A Memoir Based on a True StoryNota: 3.5 de 5 estrelas3.5/5 (231)
- Elon Musk: Tesla, SpaceX, and the Quest for a Fantastic FutureNo EverandElon Musk: Tesla, SpaceX, and the Quest for a Fantastic FutureNota: 4.5 de 5 estrelas4.5/5 (474)
- Team of Rivals: The Political Genius of Abraham LincolnNo EverandTeam of Rivals: The Political Genius of Abraham LincolnNota: 4.5 de 5 estrelas4.5/5 (234)
- The World Is Flat 3.0: A Brief History of the Twenty-first CenturyNo EverandThe World Is Flat 3.0: A Brief History of the Twenty-first CenturyNota: 3.5 de 5 estrelas3.5/5 (2259)
- The Unwinding: An Inner History of the New AmericaNo EverandThe Unwinding: An Inner History of the New AmericaNota: 4 de 5 estrelas4/5 (45)
- The Gifts of Imperfection: Let Go of Who You Think You're Supposed to Be and Embrace Who You AreNo EverandThe Gifts of Imperfection: Let Go of Who You Think You're Supposed to Be and Embrace Who You AreNota: 4 de 5 estrelas4/5 (1090)
- The Sympathizer: A Novel (Pulitzer Prize for Fiction)No EverandThe Sympathizer: A Novel (Pulitzer Prize for Fiction)Nota: 4.5 de 5 estrelas4.5/5 (120)
- English: Chapter 1-Answers CCNA 1Documento3 páginasEnglish: Chapter 1-Answers CCNA 1Jorge MingüerAinda não há avaliações
- IT - 703A - Question BankDocumento14 páginasIT - 703A - Question BankMainak DeAinda não há avaliações
- F5 Passcertification 301b v2021!04!28 by Omar 125qDocumento115 páginasF5 Passcertification 301b v2021!04!28 by Omar 125qsdfsgAinda não há avaliações
- 3G Huawei RAN Resource Monitoring and ManagementDocumento53 páginas3G Huawei RAN Resource Monitoring and ManagementgiorginoAinda não há avaliações
- LOGODocumento10 páginasLOGOAurellioAinda não há avaliações
- Data Communication: Data Communications and Networking, 5th Edition by Behrouz A. ForouzanDocumento28 páginasData Communication: Data Communications and Networking, 5th Edition by Behrouz A. ForouzanDhanwanth JPAinda não há avaliações
- PCM SamplingDocumento11 páginasPCM SamplingErRajivAmieAinda não há avaliações
- Zxr10 5960 SwitchDocumento208 páginasZxr10 5960 SwitchEdivaldoVianaAinda não há avaliações
- Nortel VPN Router Configuration Contivity 221 251Documento24 páginasNortel VPN Router Configuration Contivity 221 251Rod MarinAinda não há avaliações
- Sample House Design Project by CJ Del RosarioDocumento6 páginasSample House Design Project by CJ Del RosarioCeejAinda não há avaliações
- Ctharc 2025Documento28 páginasCtharc 2025Gao TianmingAinda não há avaliações
- Nokia Small Cells Expanding Indoor and Outdoor Coverage and Capacity Bro PDFDocumento8 páginasNokia Small Cells Expanding Indoor and Outdoor Coverage and Capacity Bro PDFNouvric IntAinda não há avaliações
- Quarter 4 Radio Technical NecessitiesDocumento5 páginasQuarter 4 Radio Technical Necessitiesjhon klein chavezAinda não há avaliações
- Security Services ApplianceDocumento19 páginasSecurity Services ApplianceDarlene HillAinda não há avaliações
- 13 - Datasheet - DH-PFS4218-16GT-190 12dec18 - OKDocumento2 páginas13 - Datasheet - DH-PFS4218-16GT-190 12dec18 - OKRen RenAinda não há avaliações
- U5 Usb-Otg: Vbat: 3.7-4.2V Vbat 5.55 B - MONDocumento1 páginaU5 Usb-Otg: Vbat: 3.7-4.2V Vbat 5.55 B - MONMikael IsakssonAinda não há avaliações
- DSP 123Documento111 páginasDSP 123Kirana007Ainda não há avaliações
- Exemplar Implementation: Further ReadingDocumento6 páginasExemplar Implementation: Further ReadingMohamed SyllaAinda não há avaliações
- 20 FM Demodulators PLLDocumento9 páginas20 FM Demodulators PLLMohamed shabanaAinda não há avaliações
- Vita 65 Openvpx 31 60Documento30 páginasVita 65 Openvpx 31 60林熙騰Ainda não há avaliações
- AR9281 WirelessCardBulletinDocumento2 páginasAR9281 WirelessCardBulletintrebz36Ainda não há avaliações
- Ericsson Rbs 2111 PDFDocumento2 páginasEricsson Rbs 2111 PDFTravisAinda não há avaliações
- Hype Cycle For Enter 441509 NDXDocumento61 páginasHype Cycle For Enter 441509 NDXGustavo CarvalhoAinda não há avaliações
- AAU5942 Technical Specifications (V100R016C10 - 02) (PDF) - ENDocumento31 páginasAAU5942 Technical Specifications (V100R016C10 - 02) (PDF) - ENOndra Cizek100% (1)
- List2020 PDFDocumento20 páginasList2020 PDFSamAinda não há avaliações
- AUTOSAR SWS DiagnosticCommunicationManagerDocumento421 páginasAUTOSAR SWS DiagnosticCommunicationManagerTitiUraAinda não há avaliações
- Gilat Product Sheet SkyEdge II IPDocumento2 páginasGilat Product Sheet SkyEdge II IPaxj42128Ainda não há avaliações
- Lab StackingDocumento7 páginasLab StackingIbrahim M EspinozaAinda não há avaliações
- 3G: Cdma2000 and Td-Scdma: CDMA2000 (Also Known As C2K or IMT Multi-Carrier (IMT-MC) ) Is A Family of 3GDocumento3 páginas3G: Cdma2000 and Td-Scdma: CDMA2000 (Also Known As C2K or IMT Multi-Carrier (IMT-MC) ) Is A Family of 3GAdarsh VenugopalAinda não há avaliações
- Aws Best Practices Ddos ResiliencyDocumento29 páginasAws Best Practices Ddos Resiliencyaashiq aliAinda não há avaliações