Escolar Documentos
Profissional Documentos
Cultura Documentos
Cloud-Based - An Intrusion Detection and Response System For Mobile Phones PDF
Enviado por
Kleber Magno Vieira0 notas0% acharam este documento útil (0 voto)
32 visualizações2 páginasTítulo original
Cloud-based- An Intrusion detection and response system for mobile phones.pdf
Direitos autorais
© © All Rights Reserved
Formatos disponíveis
PDF, TXT ou leia online no Scribd
Compartilhar este documento
Compartilhar ou incorporar documento
Você considera este documento útil?
Este conteúdo é inapropriado?
Denunciar este documentoDireitos autorais:
© All Rights Reserved
Formatos disponíveis
Baixe no formato PDF, TXT ou leia online no Scribd
0 notas0% acharam este documento útil (0 voto)
32 visualizações2 páginasCloud-Based - An Intrusion Detection and Response System For Mobile Phones PDF
Enviado por
Kleber Magno VieiraDireitos autorais:
© All Rights Reserved
Formatos disponíveis
Baixe no formato PDF, TXT ou leia online no Scribd
Você está na página 1de 2
A Cloud-based Intrusion Detection and Response System for Mobile Phones
Amir Houmansadr, Saman A. Zonouz, and Robin Berthier
University of Illinois at Urbana-Champaign
{ahouman2, saliari2, rgb}@illinois.edu
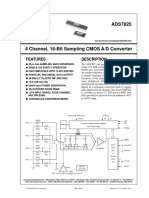
AbstractAs smart mobile phones, so called smartphones,
are getting more complex and more powerful to efficiently pro- Internet
vide more functionalities, concerns are increasing regarding Network Network Traffic
security threats against the smartphone users. Since smart- Traffic Response Action
phones use the same software architecture as in PCs, they are Proxy Forwarded Traffic
vulnerable to similar classes of security risks such as viruses,
trojans, and worms [6]. In this paper, we propose a cloud-
based smartphone-specific intrusion detection and response
engine, which continuously performs an in-depth forensics
analysis on the smartphone to detect any misbehavior. In
case a misbehavior is detected, the proposed engine decides Cell Tower
Virus
Detected
upon and takes optimal response actions to thwart the on- Secloud
Agent
going attacks. Despite the computational and storage resource
Real-time Smartphone Emulation Environment
limitations in smartphone devices, The engine can perform a Smartphone (Instrumented with Intrusion Detection Systems)
complete and in-depth analysis on the smartphone, since all
the investigations are carried out on an emulated device in a
cloud environment. Figure 1. High-level Architecture
by looking for some specific signatures downloaded from
I. I NTRODUCTION a database. This, first of all, requires a large amount of
Smartphones, as extremely fast-growing type of commu- storage on the device, and, secondly, such a signature-
nication devices, offer more advanced computing and con- based approach is easily evaded by introducing zero-day
nectivity functionalities than contemporary mobile phones threats. Another class of smartphone security solutions
by conceptually integrating handheld computers capabil- perform network-based intrusion detection [5]. Although
ities with phone devices. While most traditional mobile this addresses the resource limitations affecting previously
phones are able to run applications based on specific mentioned approach, their accuracy and performance is
platforms such as Java ME, a smartphone usually allows the affected by their lack of knowledge on smartphones inter-
user to install and run more advanced third-party software nal activities. As another issue, none of the past proposed
applications. Being an all-in-one device, smartphones are techniques provide automated response and recovery for
increasingly getting attractive to a wide range of users. A the detected security threats. This is essential in order to
recent study by ComScore Inc. indicates that over 45.5 quickly terminate the attack and restore the phone back to
million people in the United States owned smartphones its normal operational mode.
in 2010, a 20% share of the total devices sold, and a
continuous annual growth rate of 156% [1] is estimated. II. S YSTEM D ESIGN
Following smartphones increasing popularity, attackers To address the critical challenge of keeping smartphone
have also been interested in attacking to such platforms. In secure, cloud-based intrusion detection has recently been
fact, a large number of smartphone malware have attempted introduced [7], [8]. We build on top of this concept and
to exploit unique vulnerabilities of smartphones. As a propose a synchronized cloud-based intrusion detection and
case in point, the smartphone virus Cabir [2] spreads and response framework for smartphone devices. We seek the
populates through the Bluetooth interface of smartphones. following objectives: 1) transparent operation to the users
Another recent smartphone security study shows that tro- who are mostly technically unskilled; 2) light resource re-
jans, using voice-recognition algorithms, can steal sensi- quirement, and 3) real-time and accurate intrusion detection
tive information that are talked through smartphones [9]. and response. The proposed framework targets a practical
Such threats not only invade privacy and security of the scenario in which most smartphones cannot be equipped
smartphone users, but also manage to generate coordinated with heavyweight anti-malware software, but need to be
large-scale attacks on the communication infrastructures by protected against attacks. The proposed framework is in
forming botnets. fact a cloud service which provides intrusion detection
The past solutions for smartphone security encounter and response capabilities to the registered smartphones.
several limitations in practice. Many of such approaches are It emulates the actual smartphone device in a virtual
based on running a lightweight intrusion detection process machine in cloud using a proxy which duplicates the
on the smartphones [4]; these schemes fail to provide in-coming traffic to the devices and forwards the traffic
effective protection as they are constrained by the limited to the emulation platform. The real-time emulation on
memory, storage, and computational resources, and battery powerful servers allows the framework to instrument the
power of the smartphone devices [3]. In addition, most of emulated environment with a rich set of (possibly resource
such approaches are based on detecting malware/intrusions intensive) off-the-shelf intrusion forensics and detection
systems, which do not necessarily have to be lightweight,
and perform a run-time in-depth detection analysis. The
key difference with previous attempts is to replicate user
input in real time. This enables our solution to have very
limited bandwidth requirements while keeping the replica
always synchronized. In case a misbehavior is detected, the
intrusion response decides upon the best countermeasure
actions and sends it to a non-intrusive software agent in the
device, which is in charge of only carrying out the received
actions.
Figure 1 shows the high-level architecture of the pro-
posed framework and how its components interact with
each other. A smartphone to be protected by the framework
should be registered by its owner to the frameworks online
registration system. To register, the client should first spec- Figure 2. A sample system dependency graph
ify his or her device, it operating system and the application dependency graph is later augmented with triggered IDS
list, so that the framework can instantiate an identical alerts to automatically generate the system attack graph [10]
image of the smartphone in cloud. Additionally, the client which encodes the possible attack paths according to the
is asked to install a very light-weight software agent on the provided information. The attack graph is later analyzed to
smartphone that automatically would configure the proxy identify the misbehaving smartphone application. For more
settings. A proxy server is responsible for duplicating the information, the reader is referred to the original paper [10].
communication between the smartphone and the Internet
and forwarding it to the emulation environment in cloud IV. C ONCLUSIONS
where the detection and forensics analyses are performed. We presented a cloud-based service to provide security
Note that this does not disrupt the usual communication and tolerance to resource limited mobile phone devices.
between the smartphone and the Internet. The light-weight We are currently deploying the framework on the Android-
agent on the smartphone performs three main tasks. It gath- equipped HTC Droid Incredible smartphones. Our long-
ers all user and sensor inputs to the device, it sends them term plan is to later leverage the generated attack-graph to
to the emulation environment, and it waits for potential automatically decide upon response actions in an emulated
response and recovery commands, e.g., killing the malicious smartphone environment as our intrusion response and
application, from the emulation environment in order to recovery engine [11] does in computer systems.
take the required actions. R EFERENCES
The real-time emulation environment is instrumented [1] 2010. Windows mobile business value for mobile operators:
with several accurate off-the-shelf intrusion detection sys- http://download.microsoft.com/.
tems (IDSes), which currently cannot be deployed in smart- [2] 2010. Virus Library: http://www.viruslibrary.com/.
phone devices due to their high resource requirements. The [3] C. Biever, 2005. Phone viruses: how bad is it?: http://www.
deployed set of detectors monitor different parts of the newscientist.com/article.ns?id=dn7080.
[4] A. Boukerche and M. S. M. A. Notare. Behavior-based
smartphones software stack and perform an online and in- intrusion detection in mobile phone systems. Jour. Paral.
depth analysis to identify any malicious activity. In case a & Dist. Comp., 62(9):1476 1490, 2002.
misbehavior is detected, our intrusion response engine [11] [5] J. Cheng, S. H. Wong, H. Yang, and S. Lu. Smartsiren: virus
detection and alert for smartphones. In MobiSys, pages 258
in the emulation environment solves an resource intensive 271, New York, NY, USA, 2007. ACM.
game-theoretic optimization, and sends the selected optimal [6] J. Jamaluddin, N. Zotou, and P. Coulton. Mobile phone
response action to the agent running on the smartphone vulnerabilities: a new generation of malware. In Consumer
device. The agent, then, can take the required actions Electronics, 2004 IEEE International Symposium on, pages
199 202, 2004.
and recover the smartphone back to its normal secure [7] J. Oberheide, K. Veeraraghavan, E. Cooke, J. Flinn, and
operational mode. F. Jahanian. Virtualized in-cloud security services for mobile
devices. In Proceedings of the First Workshop on Virtual-
III. I MPLEMENTATION ization in Mobile Computing, pages 3135. Citeseer, 2008.
[8] G. Portokalidis, P. Homburg, K. Anagnostakis, and H. Bos.
We have implemented a working prototype of the intru- Paranoid Android: versatile protection for smartphones. In
sion forensics analysis engine for the Linux kernel, and we Proceedings of the 26th Annual Computer Security Applica-
tions Conference, pages 347356. ACM, 2010.
are currently working on the emulation environment. The
[9] R. Schlegel, K. Zhang, X. Zhou, M. Intwala, A. Kapadia,
forensics engine makes use of two sources of information: and X. Wang. Soundminer: A Stealthy and Context-Aware
1) set of IDSes that are deployed, and monitoring various Sound Trojan for Smartphones. In NDSS, 2011.
aspects of the system; and 2) system calls which are logged [10] S. A. Zonouz, K. Joshi, and W. H. Sanders. Cost-aware
by a loadable kernel module that we developed by manip- systemwide intrusion defense via online forensics and on-
demand detector deployment. In CCS-SafeConfig, pages 71
ulating the system call table, and in particular, replacing 74, 2010.
each system call function with a wrapper logging function. [11] S. A. Zonouz, H. Khurana, W. Sanders, and T. Yardley. Rre:
System call logs are used to create an information flow A game-theoretic intrusion response and recovery engine. In
DSN, pages 439 448, 2009.
graph (see Figure 2) in which nodes are OS-level objects,
e.g., processes, and directed edges represent data flows. The
Você também pode gostar
- Intrusion Detection For Grid and Cloud ComputingDocumento6 páginasIntrusion Detection For Grid and Cloud ComputingKleber Magno VieiraAinda não há avaliações
- Anomaly-Based IDS Implementation in Cloud Environment Using BOAT AlgorithmDocumento6 páginasAnomaly-Based IDS Implementation in Cloud Environment Using BOAT AlgorithmKleber Magno VieiraAinda não há avaliações
- Chemogenomics: Hugo KubinyiDocumento35 páginasChemogenomics: Hugo KubinyiKleber Magno VieiraAinda não há avaliações
- Computer System Intrusion Detection - A SurveyDocumento25 páginasComputer System Intrusion Detection - A SurveyKleber Magno VieiraAinda não há avaliações
- PLSQL Just Got FasterDocumento27 páginasPLSQL Just Got FasterKleber Magno VieiraAinda não há avaliações
- Reconsidering Intrusion Monitoring Requirements in Shared Cloud PlatformsDocumento8 páginasReconsidering Intrusion Monitoring Requirements in Shared Cloud PlatformsKleber Magno VieiraAinda não há avaliações
- Internet Intrusion Detection System Service in A CloudDocumento8 páginasInternet Intrusion Detection System Service in A CloudKleber Magno VieiraAinda não há avaliações
- VMs Hypervisor-Based Intrusion Detection SystemDocumento5 páginasVMs Hypervisor-Based Intrusion Detection SystemKleber Magno VieiraAinda não há avaliações
- Autonomic Cheng SlidesDocumento8 páginasAutonomic Cheng SlidesKleber Magno VieiraAinda não há avaliações
- Response Taxonomy TechReport06-05Documento18 páginasResponse Taxonomy TechReport06-05Kleber Magno VieiraAinda não há avaliações
- XUju3b 06547755Documento12 páginasXUju3b 06547755Kleber Magno VieiraAinda não há avaliações
- Zooplankton change after dredging worksDocumento9 páginasZooplankton change after dredging worksKleber Magno VieiraAinda não há avaliações
- NRC Publications Archive (Nparc) Archives Des Publications Du CNRC (Nparc)Documento7 páginasNRC Publications Archive (Nparc) Archives Des Publications Du CNRC (Nparc)Kleber Magno VieiraAinda não há avaliações
- Zooplankton change after dredging worksDocumento9 páginasZooplankton change after dredging worksKleber Magno VieiraAinda não há avaliações
- Hidden Figures: The American Dream and the Untold Story of the Black Women Mathematicians Who Helped Win the Space RaceNo EverandHidden Figures: The American Dream and the Untold Story of the Black Women Mathematicians Who Helped Win the Space RaceNota: 4 de 5 estrelas4/5 (894)
- The Yellow House: A Memoir (2019 National Book Award Winner)No EverandThe Yellow House: A Memoir (2019 National Book Award Winner)Nota: 4 de 5 estrelas4/5 (98)
- The Little Book of Hygge: Danish Secrets to Happy LivingNo EverandThe Little Book of Hygge: Danish Secrets to Happy LivingNota: 3.5 de 5 estrelas3.5/5 (399)
- The Subtle Art of Not Giving a F*ck: A Counterintuitive Approach to Living a Good LifeNo EverandThe Subtle Art of Not Giving a F*ck: A Counterintuitive Approach to Living a Good LifeNota: 4 de 5 estrelas4/5 (5794)
- Never Split the Difference: Negotiating As If Your Life Depended On ItNo EverandNever Split the Difference: Negotiating As If Your Life Depended On ItNota: 4.5 de 5 estrelas4.5/5 (838)
- Elon Musk: Tesla, SpaceX, and the Quest for a Fantastic FutureNo EverandElon Musk: Tesla, SpaceX, and the Quest for a Fantastic FutureNota: 4.5 de 5 estrelas4.5/5 (474)
- A Heartbreaking Work Of Staggering Genius: A Memoir Based on a True StoryNo EverandA Heartbreaking Work Of Staggering Genius: A Memoir Based on a True StoryNota: 3.5 de 5 estrelas3.5/5 (231)
- The Emperor of All Maladies: A Biography of CancerNo EverandThe Emperor of All Maladies: A Biography of CancerNota: 4.5 de 5 estrelas4.5/5 (271)
- The Gifts of Imperfection: Let Go of Who You Think You're Supposed to Be and Embrace Who You AreNo EverandThe Gifts of Imperfection: Let Go of Who You Think You're Supposed to Be and Embrace Who You AreNota: 4 de 5 estrelas4/5 (1090)
- The World Is Flat 3.0: A Brief History of the Twenty-first CenturyNo EverandThe World Is Flat 3.0: A Brief History of the Twenty-first CenturyNota: 3.5 de 5 estrelas3.5/5 (2219)
- Team of Rivals: The Political Genius of Abraham LincolnNo EverandTeam of Rivals: The Political Genius of Abraham LincolnNota: 4.5 de 5 estrelas4.5/5 (234)
- The Hard Thing About Hard Things: Building a Business When There Are No Easy AnswersNo EverandThe Hard Thing About Hard Things: Building a Business When There Are No Easy AnswersNota: 4.5 de 5 estrelas4.5/5 (344)
- Devil in the Grove: Thurgood Marshall, the Groveland Boys, and the Dawn of a New AmericaNo EverandDevil in the Grove: Thurgood Marshall, the Groveland Boys, and the Dawn of a New AmericaNota: 4.5 de 5 estrelas4.5/5 (265)
- The Unwinding: An Inner History of the New AmericaNo EverandThe Unwinding: An Inner History of the New AmericaNota: 4 de 5 estrelas4/5 (45)
- The Sympathizer: A Novel (Pulitzer Prize for Fiction)No EverandThe Sympathizer: A Novel (Pulitzer Prize for Fiction)Nota: 4.5 de 5 estrelas4.5/5 (119)
- FW3505 19.5v1 Introducing Authentication On Sophos FirewallDocumento17 páginasFW3505 19.5v1 Introducing Authentication On Sophos FirewallAndré MouraAinda não há avaliações
- FL Switch SFN 16TX PDFDocumento4 páginasFL Switch SFN 16TX PDFGustavo FavaroAinda não há avaliações
- Sebol Training Manual PDFDocumento277 páginasSebol Training Manual PDFPaulJohnPosadasGimena100% (3)
- BIT2117 Accounting Information SystemsDocumento85 páginasBIT2117 Accounting Information SystemsJames MuthuriAinda não há avaliações
- ModemLog - Hisense 1xEVDO USB Modem PhoneDocumento2 páginasModemLog - Hisense 1xEVDO USB Modem PhoneYayan CahyanaAinda não há avaliações
- Create Decouple Infotype - SAP BlogsDocumento6 páginasCreate Decouple Infotype - SAP BlogsArun Varshney (MULAYAM)100% (1)
- Yealink SIP Phones Relese Note of Version72Documento37 páginasYealink SIP Phones Relese Note of Version72Luis Toledo LopezAinda não há avaliações
- Features Description: 1996 Burr-Brown Corporation PDS-1304B Printed in U.S.A. October, 1997Documento16 páginasFeatures Description: 1996 Burr-Brown Corporation PDS-1304B Printed in U.S.A. October, 1997Hector Jose Murillo CordobaAinda não há avaliações
- Curriculum Vitae: of Nandintyo ArwantoDocumento3 páginasCurriculum Vitae: of Nandintyo ArwantoScribduser160Ainda não há avaliações
- Cloud Computing: Unit-1 - Introduction To Cloud TechnologiesDocumento78 páginasCloud Computing: Unit-1 - Introduction To Cloud TechnologiesSarika80% (5)
- EXASOL User Manual 6.0.9 enDocumento512 páginasEXASOL User Manual 6.0.9 enHeinz DoofenshmirtzAinda não há avaliações
- Toshiba e Studio163 203 165 205 Printer Brochure PDFDocumento2 páginasToshiba e Studio163 203 165 205 Printer Brochure PDFMohamed ZayedAinda não há avaliações
- 1788-ENBT ManualDocumento136 páginas1788-ENBT ManualNestor CalaAinda não há avaliações
- Resources for OSINT toolsDocumento2 páginasResources for OSINT toolsAneudy Hernandez PeñaAinda não há avaliações
- Metastability and Clock Domain Crossing: IN3160 IN4160Documento30 páginasMetastability and Clock Domain Crossing: IN3160 IN4160kumarAinda não há avaliações
- SDR Software Defined Radio Overview and ApplicationsDocumento20 páginasSDR Software Defined Radio Overview and ApplicationsseesharpaAinda não há avaliações
- Wolkite University College of Computing and Informatics Department of Information Systems Web Based Cost Sharing Management System For Ethiopian Higher EducationDocumento72 páginasWolkite University College of Computing and Informatics Department of Information Systems Web Based Cost Sharing Management System For Ethiopian Higher EducationIbrãhîm MõWdätAinda não há avaliações
- Hit 7080 IcmaDocumento62 páginasHit 7080 IcmaJoseMiguelBlancoAlvarezAinda não há avaliações
- MemoCam Application User Guide V01 PDFDocumento173 páginasMemoCam Application User Guide V01 PDFJorge HuangAinda não há avaliações
- Module 3Documento33 páginasModule 34SF19IS024 DiyonaAinda não há avaliações
- FRZ Indicator Automater v11.1 MANUALDocumento35 páginasFRZ Indicator Automater v11.1 MANUALyusuf iping100% (3)
- Data ScienceDocumento87 páginasData Sciencetha9s9catal9Ainda não há avaliações
- Language ModellingDocumento3 páginasLanguage ModellingPrakash SawantAinda não há avaliações
- Business Level 3 Btec Extended Diploma CourseworkDocumento7 páginasBusiness Level 3 Btec Extended Diploma Courseworkemlwymjbf100% (1)
- Corporate Approver User Manual For E-GovDocumento12 páginasCorporate Approver User Manual For E-GovRemz Prin Ting LaoagAinda não há avaliações
- Virtuoso MmsimDocumento12 páginasVirtuoso Mmsim刘航Ainda não há avaliações
- ABAP ALV Tree ExemploDocumento13 páginasABAP ALV Tree ExemploLeonardo NobreAinda não há avaliações
- MN042 - Commander Echo Quickstart GuideDocumento12 páginasMN042 - Commander Echo Quickstart GuideMahdi LahdiliAinda não há avaliações
- G7-L03C469B530 HW La Software Upgrade GuidelineDocumento8 páginasG7-L03C469B530 HW La Software Upgrade GuidelineSoporAinda não há avaliações
- Med PDFDocumento30 páginasMed PDFSharfuddin ShariffAinda não há avaliações