Escolar Documentos
Profissional Documentos
Cultura Documentos
Therory Last PPR
Enviado por
Muhammad IshaqTítulo original
Direitos autorais
Formatos disponíveis
Compartilhar este documento
Compartilhar ou incorporar documento
Você considera este documento útil?
Este conteúdo é inapropriado?
Denunciar este documentoDireitos autorais:
Formatos disponíveis
Therory Last PPR
Enviado por
Muhammad IshaqDireitos autorais:
Formatos disponíveis
Distance
Distance is the cost of reaching a destination, usually based on the number of hosts the path
passes through, or the total of all the administrative metrics assigned to the links in the path.
Vector
From the standpoint of routing protocols, the vector is the interface traffic will be forwarded
out in order to reach an given destination network along a route or path selected by the
routing protocol as the best path to the destination network.
SMTP
SMTP stands for Simple Mail Transfer Protocol. SMTP is used when email is delivered from an
email client, such as Outlook Express, to an email server or when email is delivered from one
email server to another. SMTP uses port 25.
POP3
POP3 stands for Post Office Protocol. POP3 allows an email client to download an email from an
email server. The POP3 protocol is simple and does not offer many features except for download.
Its design assumes that the email client downloads all available email from the server, deletes
them from the server and then disconnects. POP3 normally uses port 110.
IMAP
IMAP stands for Internet Message Access Protocol. IMAP shares many similar features with POP3.
It, too, is a protocol that an email client can use to download email from an email server.
However, IMAP includes many more features than POP3. The IMAP protocol is designed to let
users keep their email on the server.
Non-persistent
HTTP/1.0
server parses request, responds, and closes TCP connection
2 RTTs to fetch each object
Each object transfer suffers from slow start
Persistent
default for HTTP/1.1
on same TCP connection: server, parses request, responds, parses new request,..
Client sends requests for all referenced objects as soon as it receives base HTML.
Fewer RTTs and less slow start.
"When the name space is large, searching a name in hierarchical structure (tree) is much faster
that searching it in a flat structure (linear). The first can use a binary search; the second needs
to use a sequential search."
Segmentation :
1. Segmentation takes place at Layer 4 i.e Transport Layer.
2. This occurs during the original creation of the packets when a set of data doesn’t fit within the
“Maximum Segment Size (MSS)”. The data is then chopped into multiple segments referred
as “Protocol Data Unit”. This process is known as segmentation.
3. Something about MSS : MSS is set as a TCP option initially in the TCP SYN packet during
the 3 way handshake. This value cannot be changed after the connection is established.
Default Maximum TCP segment size = 576 Bytes.
4. In order to avoid Fragmentation (which we will see further) ,
note that (Number of bytes in the data segment + the header) < MTU
B] Fragmentation :
1. Fragmentation takes place at Layer 3 i.e Network Layer.
2. This occurs during the original creation of frames where the network layer must send packets
down to the Data Link Layer for transmission. Some Data Link Layer technologies have
limits on the length of the data that can be sent. Inshort some links have smaller MTU
(Maximum Transmission Unit).
3. If the packet that is to be sent is larger than the MTU then it is chopped. This process is
known as fragmentation. These pieces are reassembled once they arrive at the network layer
of the destination.
advantages of circuit switching
Following are the benefits or advantages of circuit switching type:
➨As there is very less delay for the call to be established and also during the conversation, the circuit switching
network is widely used for realtime voice services throughtout the world since years. There is almost no waiting time
at voice switches used for the call.
➨It will have realistic voice communication and consecutively speaking persons are easily identified due to higher
sampling rates used.
Advantages of virtual circuit switching are:
Packets are delivered in order,
since they all take the same route;
The overhead in the packets is smaller,
since there is no need for each packet to contain the full address;
The connection is more reliable,
network resources are allocated at call setup so that even during times of congestion,
provided that a call has been setup, the subsequent packets should get through;
Advantages of Datagram Approach
1. Datagrams can contain the full destination address rather than
using some number.
2. There is no set up phase required for the datagram circuits. This
means that no resources are consumed.
3. If it happens during a transmission that one router goes down, the
datagrams that will suffer will include only those routers which would
have been queued up in that specific router. The other datagrams will
not suffer.
Advantages of flooting in routing
If a packet can be delivered, it will (probably multiple times).
Since flooding naturally utilizes every path through the network, it will also use the shortest path.
This algorithm is very simple to implement.[citation needed]
Disadvantages[edit]
Flooding can be costly in terms of wasted bandwidth. While a message may only have one
destination it has to be sent to every host. In the case of a ping flood or a denial of service
attack, it can be harmful to the reliability of a computer network.
Messages can become duplicated in the network further increasing the load on the networks
bandwidth as well as requiring an increase in processing complexity to disregard duplicate
messages.
Duplicate packets may circulate forever, unless certain precautions are taken:
Use a hop count or a time to live (TTL) count and include it with each packet. This value
should take into account the number of nodes that a packet may have to pass through on
the way to its destination.
Have each node keep track of every packet seen and only forward each packet once.
Enforce a network topology without loops.
Você também pode gostar
- The Subtle Art of Not Giving a F*ck: A Counterintuitive Approach to Living a Good LifeNo EverandThe Subtle Art of Not Giving a F*ck: A Counterintuitive Approach to Living a Good LifeNota: 4 de 5 estrelas4/5 (5794)
- Hidden Figures: The American Dream and the Untold Story of the Black Women Mathematicians Who Helped Win the Space RaceNo EverandHidden Figures: The American Dream and the Untold Story of the Black Women Mathematicians Who Helped Win the Space RaceNota: 4 de 5 estrelas4/5 (890)
- The Yellow House: A Memoir (2019 National Book Award Winner)No EverandThe Yellow House: A Memoir (2019 National Book Award Winner)Nota: 4 de 5 estrelas4/5 (98)
- The Little Book of Hygge: Danish Secrets to Happy LivingNo EverandThe Little Book of Hygge: Danish Secrets to Happy LivingNota: 3.5 de 5 estrelas3.5/5 (399)
- A Heartbreaking Work Of Staggering Genius: A Memoir Based on a True StoryNo EverandA Heartbreaking Work Of Staggering Genius: A Memoir Based on a True StoryNota: 3.5 de 5 estrelas3.5/5 (231)
- Never Split the Difference: Negotiating As If Your Life Depended On ItNo EverandNever Split the Difference: Negotiating As If Your Life Depended On ItNota: 4.5 de 5 estrelas4.5/5 (838)
- Elon Musk: Tesla, SpaceX, and the Quest for a Fantastic FutureNo EverandElon Musk: Tesla, SpaceX, and the Quest for a Fantastic FutureNota: 4.5 de 5 estrelas4.5/5 (474)
- The Hard Thing About Hard Things: Building a Business When There Are No Easy AnswersNo EverandThe Hard Thing About Hard Things: Building a Business When There Are No Easy AnswersNota: 4.5 de 5 estrelas4.5/5 (344)
- The Emperor of All Maladies: A Biography of CancerNo EverandThe Emperor of All Maladies: A Biography of CancerNota: 4.5 de 5 estrelas4.5/5 (271)
- Devil in the Grove: Thurgood Marshall, the Groveland Boys, and the Dawn of a New AmericaNo EverandDevil in the Grove: Thurgood Marshall, the Groveland Boys, and the Dawn of a New AmericaNota: 4.5 de 5 estrelas4.5/5 (265)
- The Gifts of Imperfection: Let Go of Who You Think You're Supposed to Be and Embrace Who You AreNo EverandThe Gifts of Imperfection: Let Go of Who You Think You're Supposed to Be and Embrace Who You AreNota: 4 de 5 estrelas4/5 (1090)
- Team of Rivals: The Political Genius of Abraham LincolnNo EverandTeam of Rivals: The Political Genius of Abraham LincolnNota: 4.5 de 5 estrelas4.5/5 (234)
- The World Is Flat 3.0: A Brief History of the Twenty-first CenturyNo EverandThe World Is Flat 3.0: A Brief History of the Twenty-first CenturyNota: 3.5 de 5 estrelas3.5/5 (2219)
- The Unwinding: An Inner History of the New AmericaNo EverandThe Unwinding: An Inner History of the New AmericaNota: 4 de 5 estrelas4/5 (45)
- The Sympathizer: A Novel (Pulitzer Prize for Fiction)No EverandThe Sympathizer: A Novel (Pulitzer Prize for Fiction)Nota: 4.5 de 5 estrelas4.5/5 (119)
- Class 2Documento36 páginasClass 2mohamad rezaAinda não há avaliações
- Explore Weather Trends: Data Analyst NanodegreeDocumento8 páginasExplore Weather Trends: Data Analyst NanodegreeLulua KSAinda não há avaliações
- Efront ArchitectureDocumento5 páginasEfront ArchitectureAhmed Al-AntaryAinda não há avaliações
- Linux CommandsDocumento160 páginasLinux Commandsdev4444reachme100% (1)
- Varistor Data SheetDocumento17 páginasVaristor Data SheetJimmy CalderonAinda não há avaliações
- Online Instructions For Chapter 2: Divide-And-Conquer: Algorithms Analysis and Design (CO3031)Documento20 páginasOnline Instructions For Chapter 2: Divide-And-Conquer: Algorithms Analysis and Design (CO3031)Trần Quốc KhangAinda não há avaliações
- Bootp DHCPDocumento42 páginasBootp DHCPKamalesh Lunkad0% (1)
- Data - Table Tutorial (With 50 Examples) PDFDocumento13 páginasData - Table Tutorial (With 50 Examples) PDFRizqoh FatichahAinda não há avaliações
- Introduction To Digital CommunicationsDocumento12 páginasIntroduction To Digital CommunicationsYashwanthReddyAinda não há avaliações
- AWS DB Licensing ModelDocumento1 páginaAWS DB Licensing ModelVinu3012Ainda não há avaliações
- Bitcoin Address Generation in Pure Python - OPSXCQ BlogDocumento1 páginaBitcoin Address Generation in Pure Python - OPSXCQ BlogMegan KosAinda não há avaliações
- DAC May 2021 SyllabusDocumento8 páginasDAC May 2021 SyllabusDandwate TataAinda não há avaliações
- DTE DCE InterfaceDocumento25 páginasDTE DCE InterfaceHB33% (3)
- Chapter2 PDFDocumento24 páginasChapter2 PDFvrhdzvAinda não há avaliações
- DM 1012datastudiohealth PDFDocumento25 páginasDM 1012datastudiohealth PDFaamir_malikAinda não há avaliações
- HTTP API User Guide for ValueFirst SMS Version 1.3.2Documento17 páginasHTTP API User Guide for ValueFirst SMS Version 1.3.2Daljeet Singh SeniAinda não há avaliações
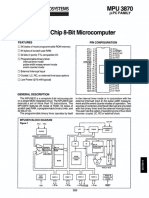
- Standard Microsystems MPU3870 Single-Chip MicrocomputerDocumento8 páginasStandard Microsystems MPU3870 Single-Chip MicrocomputerВячеслав НебесныйAinda não há avaliações
- Car Dealers Dtabase SamplesDocumento25 páginasCar Dealers Dtabase SamplesFanieAinda não há avaliações
- Semrush-Keyword Analytics Overview (Desktop) - Data Analysis-18th Aug 2023Documento5 páginasSemrush-Keyword Analytics Overview (Desktop) - Data Analysis-18th Aug 2023John KelvinAinda não há avaliações
- Mcsa Senario - Part5Documento7 páginasMcsa Senario - Part5Hedieh MadahAinda não há avaliações
- Data ConversionDocumento25 páginasData ConversionCherinet dubaleAinda não há avaliações
- TMW 61850 ClientDocumento51 páginasTMW 61850 ClientNirmala AllamAinda não há avaliações
- Tape RotationDocumento21 páginasTape Rotationsubhrajitm470% (1)
- 73 - Useful SQL Queries in WordDocumento43 páginas73 - Useful SQL Queries in WordSuriya Babu50% (2)
- Data Warehouse and Data Mining NotesDocumento31 páginasData Warehouse and Data Mining NotesSamrat SaxenaAinda não há avaliações
- Serial Communications: ObjectivesDocumento26 páginasSerial Communications: ObjectivesAmy OliverAinda não há avaliações
- CRUSH: Controlled, Scalable, Decentralized Placement of Replicated DataDocumento12 páginasCRUSH: Controlled, Scalable, Decentralized Placement of Replicated DataBhawesh RanjanAinda não há avaliações
- IBM Pure Flex PDFDocumento512 páginasIBM Pure Flex PDFDhanuka PathinayakeAinda não há avaliações
- SST Cli User Guide Public 727329 006usDocumento110 páginasSST Cli User Guide Public 727329 006usIman Teguh PAinda não há avaliações
- 01-14 STP RSTP ConfigurationDocumento67 páginas01-14 STP RSTP ConfigurationKiKi MaAinda não há avaliações