Escolar Documentos
Profissional Documentos
Cultura Documentos
Chapter 1: Beginning With Kali Linux
Enviado por
Kamakhya Gurukulam Kamarupa0 notas0% acharam este documento útil (0 voto)
61 visualizações150 páginasThis document outlines chapters in a book about using the Kali Linux platform to perform penetration testing and security assessments. It covers beginning with Kali Linux and setting it up, gathering information about targets, discovering targets on networks, enumerating details about targets, mapping vulnerabilities, using social engineering techniques, exploiting targets, escalating privileges on systems, maintaining persistent access, testing wireless networks, using Kali Linux on Android with Nethunter, and lists supplementary tools.
Descrição original:
Título original
KaliLinux2AssuringSecuritybyPenetrationTesting_thirdEdition_ColorImages.pdf
Direitos autorais
© © All Rights Reserved
Formatos disponíveis
PDF, TXT ou leia online no Scribd
Compartilhar este documento
Compartilhar ou incorporar documento
Você considera este documento útil?
Este conteúdo é inapropriado?
Denunciar este documentoThis document outlines chapters in a book about using the Kali Linux platform to perform penetration testing and security assessments. It covers beginning with Kali Linux and setting it up, gathering information about targets, discovering targets on networks, enumerating details about targets, mapping vulnerabilities, using social engineering techniques, exploiting targets, escalating privileges on systems, maintaining persistent access, testing wireless networks, using Kali Linux on Android with Nethunter, and lists supplementary tools.
Direitos autorais:
© All Rights Reserved
Formatos disponíveis
Baixe no formato PDF, TXT ou leia online no Scribd
0 notas0% acharam este documento útil (0 voto)
61 visualizações150 páginasChapter 1: Beginning With Kali Linux
Enviado por
Kamakhya Gurukulam KamarupaThis document outlines chapters in a book about using the Kali Linux platform to perform penetration testing and security assessments. It covers beginning with Kali Linux and setting it up, gathering information about targets, discovering targets on networks, enumerating details about targets, mapping vulnerabilities, using social engineering techniques, exploiting targets, escalating privileges on systems, maintaining persistent access, testing wireless networks, using Kali Linux on Android with Nethunter, and lists supplementary tools.
Direitos autorais:
© All Rights Reserved
Formatos disponíveis
Baixe no formato PDF, TXT ou leia online no Scribd
Você está na página 1de 150
Chapter 1: Beginning with Kali Linux
Chapter 4: Information Gathering
Chapter 5: Target Discovery
Chapter 6: Enumerating Target
Chapter 7: Vulnerability Mapping
Chapter 8: Social Engineering
Chapter 9: Target Exploitation
Chapter 10: Privilege Escalation
Chapter 11: Maintaining Access
Chapter 12: Wireless Penetration Testing
Chapter 13: Kali Nethunter
Appendix A: Supplementary Tools
Você também pode gostar
- Kali Linux – Assuring Security by Penetration TestingNo EverandKali Linux – Assuring Security by Penetration TestingNota: 3.5 de 5 estrelas3.5/5 (2)
- Kali Linux 3 in 1 Beginners GuideDocumento420 páginasKali Linux 3 in 1 Beginners GuideQuod AntichristusAinda não há avaliações
- (@spi Dev) Kali Linux Simple and EffectiveDocumento193 páginas(@spi Dev) Kali Linux Simple and EffectiveSiavash :DAinda não há avaliações
- Basic Kali LinuxDocumento1 páginaBasic Kali LinuxSanjayAinda não há avaliações
- Gcih Giac Certified Incident Handler All in One Exam Guide Nick Mitropoulos Full ChapterDocumento67 páginasGcih Giac Certified Incident Handler All in One Exam Guide Nick Mitropoulos Full Chapterbruce.glinski869100% (7)
- Penetration Testing With Kali Linux (PWK)Documento6 páginasPenetration Testing With Kali Linux (PWK)DF QWERTAinda não há avaliações
- Cyber Security Course OutlineDocumento2 páginasCyber Security Course OutlineHamidAinda não há avaliações
- Ethical Hacking BrochureDocumento7 páginasEthical Hacking BrochureMR. EASYAinda não há avaliações
- 0Documento10 páginas0michal hanaAinda não há avaliações
- Deception Counterdeception and CounterintelligenceDocumento458 páginasDeception Counterdeception and CounterintelligenceBrigada OsintAinda não há avaliações
- Gpen Giac Certified Penetration Tester All in One Exam Guide Raymond Nutting Full ChapterDocumento67 páginasGpen Giac Certified Penetration Tester All in One Exam Guide Raymond Nutting Full Chapterashley.herrera794100% (5)
- Chapter VI - Introduction To Deep LearningDocumento38 páginasChapter VI - Introduction To Deep LearningHalbeega WaayahaAinda não há avaliações
- Gpen Giac Certified Penetration Tester All in One Exam Guide 1St Edition Raymond Nutting Full ChapterDocumento67 páginasGpen Giac Certified Penetration Tester All in One Exam Guide 1St Edition Raymond Nutting Full Chapterashley.herrera794100% (4)
- Machine LearningDocumento4 páginasMachine LearningRajit ShettyAinda não há avaliações
- Ebook Computer Security Principles and Practice 4Th Edition Stallings Test Bank Full Chapter PDFDocumento28 páginasEbook Computer Security Principles and Practice 4Th Edition Stallings Test Bank Full Chapter PDFjoanneesparzagwjxmyqont100% (10)
- Detailed Description About Course Module Wise:: Module 1: Basics of Networking and Major ProtocolsDocumento7 páginasDetailed Description About Course Module Wise:: Module 1: Basics of Networking and Major ProtocolsankushAinda não há avaliações
- Ethical Hacking Using Kali LinuxDocumento10 páginasEthical Hacking Using Kali LinuxJovelyn Dela RosaAinda não há avaliações
- Machine Learning: Course CurriculumDocumento4 páginasMachine Learning: Course Curriculumkhushoo pandeyAinda não há avaliações
- Arcilla Etech M4Documento1 páginaArcilla Etech M4Quin Kylo Pilapil ArcillaAinda não há avaliações
- Hacking With LinuxDocumento102 páginasHacking With LinuxAndres Pedroza100% (1)
- UntitledDocumento742 páginasUntitledDaniel Lima CarvalhoAinda não há avaliações
- DigitalForensic FlyerDocumento3 páginasDigitalForensic Flyercmpn.20102a0032Ainda não há avaliações
- What Is The Use of Kali Linux in Android - Systran BoxDocumento5 páginasWhat Is The Use of Kali Linux in Android - Systran BoxErrol HernanbezAinda não há avaliações
- Cs-Eh Content Year 2022Documento3 páginasCs-Eh Content Year 2022yixapef822Ainda não há avaliações
- Guide To Kali Linux PDFDocumento50 páginasGuide To Kali Linux PDFDewa PerangAinda não há avaliações
- Modul Praktek - Beginning With Kali LinuxDocumento27 páginasModul Praktek - Beginning With Kali LinuxDandy PermanaAinda não há avaliações
- Training Offerings EN Dec2022Documento1 páginaTraining Offerings EN Dec2022jerritto.pablitoAinda não há avaliações
- Elements of Cyber Security (BCY402)Documento55 páginasElements of Cyber Security (BCY402)Lakshmi SrinivasuluAinda não há avaliações
- ETHICAL HACKING A Beginners Guide To Learn About Ethical Hacking From Scratch and Reconnaissance - SCDocumento130 páginasETHICAL HACKING A Beginners Guide To Learn About Ethical Hacking From Scratch and Reconnaissance - SCsdjfnAinda não há avaliações
- Digital Forensics With Kali Lin - Shiva v. N. ParasramDocumento536 páginasDigital Forensics With Kali Lin - Shiva v. N. ParasramstroganovborisAinda não há avaliações
- Cyber Security: Professional Diploma inDocumento5 páginasCyber Security: Professional Diploma inAnshpreet SinghAinda não há avaliações
- Junior Data Science Program (12-15)Documento14 páginasJunior Data Science Program (12-15)FOR KIND ONESAinda não há avaliações
- IntroductionDocumento17 páginasIntroductionElisha NdhlovuAinda não há avaliações
- Kali Linux On Android Using Linux Deploy - Kali LinuxDocumento6 páginasKali Linux On Android Using Linux Deploy - Kali LinuxZasuvi LCAinda não há avaliações
- About KaliDocumento3 páginasAbout KaliArun SangwanAinda não há avaliações
- WWW - Incar.tw-Mastering Kali Linux For Advanced Penetration TestingDocumento5 páginasWWW - Incar.tw-Mastering Kali Linux For Advanced Penetration TestingDele AdigunAinda não há avaliações
- Varsha T2 2021: ICT741 Digital Forensics Tutorial 7Documento4 páginasVarsha T2 2021: ICT741 Digital Forensics Tutorial 7Nimra ZaheerAinda não há avaliações
- Introduction - Kali Linux DocumentationDocumento2 páginasIntroduction - Kali Linux DocumentationJeremy SyddallAinda não há avaliações
- Ensilo/Fortiedr: Course DescriptionDocumento2 páginasEnsilo/Fortiedr: Course DescriptionhoadiAinda não há avaliações
- One Year Cyber Security Diploma - 100 - Job Garment CourseDocumento6 páginasOne Year Cyber Security Diploma - 100 - Job Garment CourseJohnAinda não há avaliações
- London 15 Mayer Blackbox IOS Application Assessments Using IDBDocumento53 páginasLondon 15 Mayer Blackbox IOS Application Assessments Using IDBIts LYCANAinda não há avaliações
- Information Strategies For Communicators 1538571118Documento345 páginasInformation Strategies For Communicators 1538571118m KAinda não há avaliações
- MIT6 858F14 q14 2 Review1Documento16 páginasMIT6 858F14 q14 2 Review1jarod_kyleAinda não há avaliações
- Hackathon NotesDocumento4 páginasHackathon NotesaavvvAinda não há avaliações
- Cyber Security CourseDocumento5 páginasCyber Security Coursesanghi ranjithkumarAinda não há avaliações
- 4.1 Introductory Activity: Prepared By: Noted: Jose C. Lita JR Celma N. Miraran SHS-Teacher 1 School Principal IIDocumento1 página4.1 Introductory Activity: Prepared By: Noted: Jose C. Lita JR Celma N. Miraran SHS-Teacher 1 School Principal IIJose C. Lita JrAinda não há avaliações
- Kali Linux 2 – Assuring Security by Penetration Testing - Third EditionNo EverandKali Linux 2 – Assuring Security by Penetration Testing - Third EditionAinda não há avaliações
- Linux IntroductionDocumento18 páginasLinux IntroductionAlexis CamanoAinda não há avaliações
- Chapter No Chapter Name: List of FiguresDocumento2 páginasChapter No Chapter Name: List of FiguresPunith RaajAinda não há avaliações
- Computer Vision Ii: Ai Courses by OpencvDocumento3 páginasComputer Vision Ii: Ai Courses by OpencvJorge Wanderley RibeiroAinda não há avaliações
- DNN - 1 - M1 - Fundamentals of Neural NetworkDocumento95 páginasDNN - 1 - M1 - Fundamentals of Neural NetworkManju Prasad NAinda não há avaliações
- Grouen RHCTDocumento3 páginasGrouen RHCTamrsalahAinda não há avaliações
- A Hacker PDFDocumento169 páginasA Hacker PDFHarshdeep SinghAinda não há avaliações
- Penetration Testing and Ethical Hacking Syllabus 2023Documento11 páginasPenetration Testing and Ethical Hacking Syllabus 2023Amrit RanaAinda não há avaliações
- iOS 6 Programming Pushing the Limits: Advanced Application Development for Apple iPhone, iPad and iPod TouchNo EverandiOS 6 Programming Pushing the Limits: Advanced Application Development for Apple iPhone, iPad and iPod TouchAinda não há avaliações
- Hacking With Kali Linux A Beginner's Guide To Study PenetrationDocumento113 páginasHacking With Kali Linux A Beginner's Guide To Study PenetrationJorge J. Trujillo Ramirez100% (1)
- Hack Windows 7 With Metasploit Using Kali Linux - LINUX DIGESTDocumento22 páginasHack Windows 7 With Metasploit Using Kali Linux - LINUX DIGESTPrabarisma DewantaraAinda não há avaliações
- The Color Purple Alice WalkerDocumento17 páginasThe Color Purple Alice WalkerKamakhya Gurukulam Kamarupa100% (1)
- Companies and Intellectual Property Commission Republic of South AfricaDocumento5 páginasCompanies and Intellectual Property Commission Republic of South AfricaKamakhya Gurukulam KamarupaAinda não há avaliações
- Moi Help PDFDocumento167 páginasMoi Help PDFKamakhya Gurukulam KamarupaAinda não há avaliações
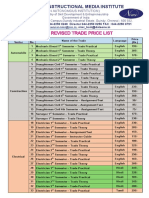
- NSQF Revised Trade Price List: An Autonomous Institution)Documento3 páginasNSQF Revised Trade Price List: An Autonomous Institution)Kamakhya Gurukulam KamarupaAinda não há avaliações
- 0620 Barr 2018Documento6 páginas0620 Barr 2018Kamakhya Gurukulam KamarupaAinda não há avaliações
- Lakulish Yoga University: Lakulish Yoga University Is Established To Propagate, Educate and Train The Students and TheDocumento1 páginaLakulish Yoga University: Lakulish Yoga University Is Established To Propagate, Educate and Train The Students and TheKamakhya Gurukulam KamarupaAinda não há avaliações
- Heramba Upanishad 2Documento3 páginasHeramba Upanishad 2Kamakhya Gurukulam KamarupaAinda não há avaliações
- Before We Knew It: An Empirical Study of Zero-Day Attacks in The Real WorldDocumento12 páginasBefore We Knew It: An Empirical Study of Zero-Day Attacks in The Real WorldAbhishek MishraAinda não há avaliações
- Legal Aspects Belgian Electronic Identity Card: Samoera Jacobs - November 2008Documento30 páginasLegal Aspects Belgian Electronic Identity Card: Samoera Jacobs - November 2008ChanduChandranAinda não há avaliações
- Comparison Study Ethical Hacking For IoTDocumento11 páginasComparison Study Ethical Hacking For IoTcliff ekwenyeAinda não há avaliações
- Key LoggingDocumento3 páginasKey Loggingapi-624664881Ainda não há avaliações
- Guide To Internet Cryptography: Jörg SchwenkDocumento535 páginasGuide To Internet Cryptography: Jörg SchwenkWilliam Danilo Saboya BautistaAinda não há avaliações
- Introduction To Cybersecurity v2 EOC Assessment - Final Exam AnswersDocumento10 páginasIntroduction To Cybersecurity v2 EOC Assessment - Final Exam AnswersEnvy VoiceAinda não há avaliações
- Cs2001g0041 002 Data Security E-BookDocumento10 páginasCs2001g0041 002 Data Security E-BookAvanish DivyaAinda não há avaliações
- Lab 4Documento5 páginasLab 4Nguyen Dinh Quan (K15 HCM)Ainda não há avaliações
- Guidelines On Cyber Resilience For Participants of Paynet's Services - 004Documento1 páginaGuidelines On Cyber Resilience For Participants of Paynet's Services - 004Soda JuiAinda não há avaliações
- Chapter 15Documento23 páginasChapter 15ayush singhAinda não há avaliações
- Authorizalion Lester: Ausihiess IDocumento1 páginaAuthorizalion Lester: Ausihiess Iwael radiAinda não há avaliações
- Linux Privilege Escalation - Writable Passwd FileDocumento15 páginasLinux Privilege Escalation - Writable Passwd FileLok . ComAinda não há avaliações
- Shubh AmDocumento2 páginasShubh AmChhotuAinda não há avaliações
- Blockchain PDFDocumento42 páginasBlockchain PDFSam S100% (1)
- A Complex Polyalphabetic Cipher TechniqueDocumento9 páginasA Complex Polyalphabetic Cipher Techniqueirfan123456Ainda não há avaliações
- Research Paper On Cyber Security & CryptographyDocumento2 páginasResearch Paper On Cyber Security & CryptographyInternational Journal of Innovative Science and Research Technology100% (1)
- CEH ToolsDocumento7 páginasCEH ToolsLordWaderAinda não há avaliações
- E Business Notes For GgsipuDocumento41 páginasE Business Notes For GgsipubasantAinda não há avaliações
- Chapter 8b: AcknowledgementDocumento29 páginasChapter 8b: AcknowledgementVioleta GjiniAinda não há avaliações
- Lesson Plan 10a1 Ao1 3Documento2 páginasLesson Plan 10a1 Ao1 3api-169562716Ainda não há avaliações
- OSWA (Offensive Security Web Attacks) - Study Overview PT.1 PDFDocumento399 páginasOSWA (Offensive Security Web Attacks) - Study Overview PT.1 PDFJames BondAinda não há avaliações
- GPC 2.2-B RAM Over HTTP v1.1.3Documento36 páginasGPC 2.2-B RAM Over HTTP v1.1.3Xavier EtedAinda não há avaliações
- File5983othdoc0 1284352860890Documento21 páginasFile5983othdoc0 1284352860890pkm_77Ainda não há avaliações
- E-Authentication Using QR Code and OTPDocumento12 páginasE-Authentication Using QR Code and OTPAnusha GiriAinda não há avaliações
- ECIH Exam Blueprint v1Documento3 páginasECIH Exam Blueprint v1dhazh0070% (1)
- GIDS v2.0Documento223 páginasGIDS v2.0namtranvanptitAinda não há avaliações
- ESET Dynamic Threat Defense Product Overview 2021Documento16 páginasESET Dynamic Threat Defense Product Overview 2021RJ BevyAinda não há avaliações
- CloudEngine 6800 V200R005C20 Configuration Guide - IP MulticastDocumento544 páginasCloudEngine 6800 V200R005C20 Configuration Guide - IP Multicastdl_maheshAinda não há avaliações
- GOOD GPG Reference Gpg-Com-4Documento62 páginasGOOD GPG Reference Gpg-Com-4bacooAinda não há avaliações
- UserManual For ConsultantsDocumento13 páginasUserManual For ConsultantsmjdAinda não há avaliações