Escolar Documentos
Profissional Documentos
Cultura Documentos
Database Security Attacks Threats and Control Methods IJERTCONV5IS10011
Enviado por
wali ahmedDireitos autorais
Formatos disponíveis
Compartilhar este documento
Compartilhar ou incorporar documento
Você considera este documento útil?
Este conteúdo é inapropriado?
Denunciar este documentoDireitos autorais:
Formatos disponíveis
Database Security Attacks Threats and Control Methods IJERTCONV5IS10011
Enviado por
wali ahmedDireitos autorais:
Formatos disponíveis
Special Issue - 2017 International Journal of Engineering Research & Technology (IJERT)
ISSN: 2278-0181
ICCCS - 2017 Conference Proceedings
Database Security: Attacks, Threats and Control
Methods
Sakshi Gahlot Bhawna Verma Anurag Khandelwal Dayanand
B.Tech Student B.Tech Student B.Tech Student Assistant Professor
Dept. of CSE, Dept. of CSE Dept. of CSE Dept. of CSE
HMRITM, INDIA HMRITM, INDIA HMRITM, INDIA HMRITM, INDIA
Abstract:-Nowadays the speed at which data is generated is
very high and rapid; so store and manage this enormous data,
it is placed in the Database System. In this Database System
the data is maintained and manipulated. Since this vast data is
stored in the Database, this Database needs to be secured.
Security involves protecting and shielding the data and the
Database from unauthorized usage and malicious attacks.
With the increase in the complicatedness of the Database the
types of attacks increases and so security becomes a crucial
issue. Through this paper, various techniques are presented
which will make the Database more secure and strengthened.
Keywords- DBMS, SQL, Privileges, Queries, Encryption,
Cryptography, Steganography
I. INTRODUCTION
A database is a collection of information or data that is
organized such that it can easily be accessed, managed, or
updated. In context to computer science, databases are Fig. 1 Database Security Properties
sometimes classified according to their organizational
approaches and one of the most common approaches is the II. DATABASE ATTACKS
relational database which is a tabular representation of data
[1]. The data is defined such that it can be reorganized and The attacks can be categorised as follows:
accessed in a number of different ways. In distributed 1. Direct attacks: When the attack is directly on the
database, it can be circulated or replicated among different targeted data, it is called a direct attack. This attack
points in a network. is successful when the database does not contain any
Databases allow any authorized user to access, enter or protection mechanism.
analyse the data quickly and easily. It is a collection of 2. Indirect attacks: These attacks do not directly attack
queries, views and tables. The data which is stored in the the target but the information regarding the data can
databases is usually organised to form the aspects that be collected using other objects. Combinations of
support the processes that require information storage and different types of queries are used but are difficult to
retrieval. The database management system (DBMS), is a track.
computer software program that is designed as the means These are further classified as follows:
of managing all the databases that are currently installed on i. Active attacks: In such attacks, the actual
any system hard drive or network [2].The database contains database values are modified. These are more
vital information of the system. So database security cannot problematic because they can mislead a user.
be ignored. Protecting the confidential and sensitive data Spoofing, Splicing and Replay are the different
which is stored in a database is what we call as database ways of performing such attacks.
security [3]. It works on making database secure from any ii. Passive attacks: In such attacks the attacker only
kind of unauthorized or illegal access or threat at any level. observes the data present in the database
without making any modifications to any data.
This can be done in the following three ways:-
● Static leakage- Attacker observes the snapshot of the
database to acquire information about database
plaintext values.
● Dynamic leakage- The attacker observes the changes
made to the database over a period of time to acquire
information about the plaintext values.
Volume 5, Issue 10 Published by, www.ijert.org 1
Special Issue - 2017 International Journal of Engineering Research & Technology (IJERT)
ISSN: 2278-0181
ICCCS - 2017 Conference Proceedings
● Linkage leakage- The attacker links the database IV. WEB SECURITY THREATS
values to the position of index values.
1. Ajax Security: AJAX (Asynchronous JavaScript
III. DATABASE THREATS and XML) technology is a mainstream technology
of Web2.0 which facilitates the browser to provide
Since database contains vital information therefore it users with more natural browsing experience. It
also faces a lots of threats. The threats can be supports asynchronous communication. With
categorized as follows: asynchronous communication, user is able to
1. Excessive privileges: If users are granted database submit, wait and refresh freely, update partial page
privileges that exceed their use or requirements, dynamically. So it allows users to have a smooth
then these privileges can be used to gain some experience similar in desktop applications [3].
confidential information. The solution to this However, it is lacking the ability to solve security
problem (besides good hiring policies) is query- problems.
level access control. Query-level access control Ajax Security (Server Side)- AJAX-based
restricts privileges to minimum-required Web applications also use the same server-
operations and data[4]. side security schemes which the regular
2. Privilege abuse: Users may abuse or misuse the Web applications do. You just need to
access privileges for unauthorized purpose. The specify authentication, authorization, and
solution is access control policies that apply not data protection requirements in your
only to what data is accessible, but how data is web.xml file or in your program. But the
accessed. By enforcing policies for time of day, AJAX-based Web applications are also
location, and application client and volume of data vulnerable to the same security threats as
retrieved, it is possible to identify users who are regular Web applications.
abusing access privileges[4]. Ajax Security (Client Side)- The JavaScript
3. Unauthorized privilege elevation: Attackers may code is visible to the user as well as to any
convert some low-level access privileges to high- hacker. Hacker can use this JavaScript code
level access privileges. for extracting the server-side weaknesses.
4. Platform vulnerabilities: The platform or operating 2. Cross Site Scripting: Cross-site Scripting occurs
system may be vulnerable to leakage and when dynamically generated web pages display
corruption of data. input that is not properly authenticated [3]. These
5. SQL injection: SQL injection specifically targets a attacks occur when an attacker uses some web
user to send unauthorized database queries which application to send some malicious code, which is
makes the server to reveal the information (which generally in the form of a browser side script, to a
it wouldn’t do normally). Using this user can also different end user. So the attacker can use this to
access the entire database. send some malicious script to any user and the
6. Denial of service: This attack involves making the end user’s browser will have no way to know that
resource unavailable for the purpose it was the script shouldn’t be trusted, and will therefore
designed. This means that the access to data or the execute the script. Since, it thinks the script came
application is denied to the user. from some trusted source that malicious script
7. Backup Exposure: The backup storage media can access any of the cookies or sessions, tokens,
remains unprotected from any attacks. As a result or any other sensitive information which the
there are several attacks on the database backup browser contains.
disks and tapes.
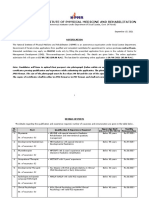
Fig. 2 Avenues of Attack Fig. 3 Cross Scripting Attack
Volume 5, Issue 10 Published by, www.ijert.org 2
Special Issue - 2017 International Journal of Engineering Research & Technology (IJERT)
ISSN: 2278-0181
ICCCS - 2017 Conference Proceedings
V. CONTROL METHODS FOR DATABASE 2. Correlated data: when visible data is connected to
THREATS invisible data semantically.
Inference detection can be done through:
Access control is responsible for the direct access to the i. Semantic inference model: represents all possible
system with the control of rules which are accompanied by relations between attributes of data resources.
some security policies. It is basically used to restrict the ii. Security violation detection and knowledge
access of confidential information. In access control, the acquisition: it adds the new query request to the
owner of the resource is eligible to give the rights to the request log and checks if the further request is
other user of that resource based on his discretion[6]. allowed [8].
An access control system includes who can access the
objects (data, programs), subjects (users, processes), 3. User identification/authentication
through operations (read, write, run)[7]. The most important security requirement is that there must
b authorized and authenticated users to access the database
Access control can be classified as: or you must identify your users before they can access the
1. Discretionary access control: it is a means of resources. In authentication, server or the client needs to
restricting access to objects based on identity of know the identity of the user or computer. It cannot control
subjects or groups to which they belong. These are what the user is accessing but it controls who is accessing
defined by user identification during the resources. Therefore the user identification is must for
authentication ex- username, password. Its main the security concerns of the database. However, the
aim to grant and revoke privileges to users. unauthorized user may take different approaches like
2. Mandatory access control: this security default password or bypassing authentication etc. user
mechanism restricts the ability of owner of identification can be implemented by using the secure
resource to deny or grant access to a file. Criteria socket layer (SSL) [9].
is defined by the administrator. It enforces
multilevel security by categorizing both the users
and the data into security classes and then the
appropriate policy is implemented.
FIG. 5 USER IDENTIFICATION
4. ACCOUNTABILITY AND AUDITING
Fig.4 Access Control
Auditing is the monitoring and recording of all the
1. Inference policy suspicious activities. If any user is trying to change or
Integrity of the entire database may be endangered by delete the data from any resource then the suspicious
the inference attack. In this, malicious users infer the activity is captured by the administrator and he can audit all
confidential and sensitive information at a high level. the connections to the database. Basically, it gathers data
Sensitive information may be leaked to the outsiders if and keeps records of all the database activities, it prevent
the inference problems are not resolved. One way is users from taking the inappropriate actions. This is used to
querying the database based on the confidential ensure physical integrity of data. The log of all successful
information. Inference policy basically aims at how to and unsuccessful attempts appears in the audit trail file.
protect information from the attackers from being Audit trails helps in detecting security violation and flaws
leaked. Data is protected at some specific level. in application [6].
Information inference occurs when some data x is read There are different types of auditing:
by user which can be further used to get data y. it is 1. Statement auditing: it allows to audits SQL
done through inference channels, where users find data statements by the statement’s type not by the
x, then uses data x to get data y as y=f(x). object on which they operate.
Main inference channels are: 2. Privilege auditing: it audits only a particular type
1. Indirect access: occurs when the user get access to of action, enables to audit the use of powerful
unauthorized data from authorized resource. system privilege.
Volume 5, Issue 10 Published by, www.ijert.org 3
Special Issue - 2017 International Journal of Engineering Research & Technology (IJERT)
ISSN: 2278-0181
ICCCS - 2017 Conference Proceedings
3. Schema object auditing: it audits only a single and secure communication in the presence of third parties
specified type of statement on a properly defined called adversaries. It prevents third party from reading
schema object, which always apply to all users of private messages by constructing and analyzing protocols.
database. Mixed cryptography involved encrypting database in a
4. Fine grained auditing: enables auditing based on diversified form over the unsecured network [12].
access to or changes in a column. It audits at the
most granular level, actions based on content and B. Securing database using steganography
data access. It is the process of hiding the confidential messages with
5. Encryption ordinary messages and extraction of its destination. It hides
Encryption is a process that convert the information into the encrypted data so that no one suspects it exists, thus
‘cipher text’ that is stored in the database. The information everyone fail to know that the file contains encrypted data.
is converted into some code and that code is only readable In steganography, data is encrypted using an algorithm into
to that person who holds the key for that particular code. redundant data. Various techniques used are audio
steganography, video steganography, IP datagram
steganography.
VII. CONCLUSION
To summarize, security of data is very important for an
organization at every level. Databases are usually attacked
because of the confidential and secret data that the attacker
can use against the organization. There are many
techniques by which we can secure the databases and there
are many more techniques which need more research in
order to develop better techniques. There is no standard for
the security model. This paper gives information about the
various threats and attacks with the common techniques
Fig.6 Encryption Process used to control these threats[14].
The advantage of the encryption is that even if an attacker REFERENCES
attacks the database to get some information, the encrypted
data is of no use for him. But one disadvantage is that [1] Data electronically available at
encryption is not secure without good key http://www.databasecompare.com/what-is-data-database-(db)-
dbms-and-dbs.html
management[11].
[2] Mubina Malik, Trisha Patel, “Database security- attacks and
control methods” International Journal of Scientific &
Engineering Research, Volume 7, Issue 12, December-2016
313 ISSN 2229-5518.
[3] Sweety R.Lodha, S.Dhande, Web database security techniques,
International Journal of Advance Research in Computer
Science and Management Studies
[4] Data electronically available at
http://www.bcs.org/content/conWebDoc/8852
[5] Data electronically available at
https://www.shrm.org/resourcesandtools/hr-topics/risk-
management/pages/top-database-security-threats.aspx
[6] Data electronically available at
http://www.techmahindra.com/sites/blogs/types_of_access_con
trol_mechanisms.aspx
[7] Data electronically available at
http://www.fit.vutbr.cz/~cvrcek/confers98/datasem/datasem.ht
ml.cz
[8] Data electronically available at
https://www.techopedia.com/definition/7711/inference
[9] Data electronically available at
Fig. 7 Encryption Architecture and Process https://www.bu.edu/tech/about/security-
resources/bestpractice/auth/
[10] Data electronically available at
VI. RECENTLY USED DATABASE https://docs.oracle.com/cd/B14117_01/network.101/b10773/au
SECURITY TECHNIQUES diting.htm
A. Securing database using cryptography [11] Data electronically available at
https://en.n.wikipedia.org/wiki/Database_encryption
Cryptography is a method of storing and transmitting data [12] Data electronically available at
in a particular form so that only those for whom it is https://en.m.wikipedia.org/wiki/cryptography
intended can read and process it. Cryptography concerns [13] Data electronically available at
with the confidentiality, integrity, non-repudiation and https://searchsecurity.techtarget.com/definition/steganography
authentication. It is the practice and study of techniques for
Volume 5, Issue 10 Published by, www.ijert.org 4
Você também pode gostar
- Information Security Science: Measuring the Vulnerability to Data CompromisesNo EverandInformation Security Science: Measuring the Vulnerability to Data CompromisesAinda não há avaliações
- Forensics Research Paper Uploaded by Ivneet SinghDocumento24 páginasForensics Research Paper Uploaded by Ivneet SinghivneetsinghanandAinda não há avaliações
- 07 SP800-34-Rev1 Bia TemplateDocumento4 páginas07 SP800-34-Rev1 Bia TemplateDarthFerenczyAinda não há avaliações
- MobilesecurityintroDocumento35 páginasMobilesecurityintronarsingthakur100% (1)
- Cyber Security: BY:-Dhwani Palejwala Diya Anand Ria ShahDocumento34 páginasCyber Security: BY:-Dhwani Palejwala Diya Anand Ria ShahChitra ShahAinda não há avaliações
- Windows 7-10 Deployment Notes 2017 For ISDs (V1.4 2017.09.29)Documento21 páginasWindows 7-10 Deployment Notes 2017 For ISDs (V1.4 2017.09.29)Alejandro TonelliAinda não há avaliações
- Department of State Pt. 121Documento25 páginasDepartment of State Pt. 121Shade BlackAinda não há avaliações
- MSFT Cloud Architecture SecurityDocumento9 páginasMSFT Cloud Architecture SecurityPratik KadamAinda não há avaliações
- Linux Administrator Guide1Documento31 páginasLinux Administrator Guide1Moe Thet HninAinda não há avaliações
- The Worst Mobile Apps: Def Con 28Documento69 páginasThe Worst Mobile Apps: Def Con 28Hira AftabAinda não há avaliações
- Linuxfun PDFDocumento365 páginasLinuxfun PDFrmarques_30164Ainda não há avaliações
- IT Security Audit and ControlDocumento1 páginaIT Security Audit and ControljbascribdAinda não há avaliações
- FortiOS 5.0 HandbookDocumento277 páginasFortiOS 5.0 HandbookpewichaliAinda não há avaliações
- Sun Recommended Patch Management ProcessDocumento5 páginasSun Recommended Patch Management ProcessTolulope AbiodunAinda não há avaliações
- Difference Between Domain and WorkgroupDocumento1 páginaDifference Between Domain and WorkgroupVivek DubeyAinda não há avaliações
- Privileged Attack Vectors: Building Effective Cyber-Defense Strategies to Protect OrganizationsNo EverandPrivileged Attack Vectors: Building Effective Cyber-Defense Strategies to Protect OrganizationsAinda não há avaliações
- Information Privacy Resources: Global Technology Audit Guide (GTAG 5: Managing and Auditing Privacy Risks Is Intended ToDocumento7 páginasInformation Privacy Resources: Global Technology Audit Guide (GTAG 5: Managing and Auditing Privacy Risks Is Intended ToSreekarAinda não há avaliações
- 2017 U.S. State of Cybercrime SurveyDocumento8 páginas2017 U.S. State of Cybercrime SurveyIDG_WorldAinda não há avaliações
- Weaknesses & ObservationsDocumento3 páginasWeaknesses & ObservationsWadek1960Ainda não há avaliações
- Cyber Security Resilience A Complete Guide - 2021 EditionNo EverandCyber Security Resilience A Complete Guide - 2021 EditionAinda não há avaliações
- 2-FDA Medical Device Cybersecurity Regulatory RequirementsDocumento3 páginas2-FDA Medical Device Cybersecurity Regulatory RequirementsMayank KakkarAinda não há avaliações
- Comparative Analysis of Phishing ToolsDocumento3 páginasComparative Analysis of Phishing ToolsEditor IJTSRDAinda não há avaliações
- Defender For Office 365 DatasheetDocumento2 páginasDefender For Office 365 DatasheetMd. Ariful IslamAinda não há avaliações
- Data SecurityDocumento120 páginasData SecurityAsad NaveedAinda não há avaliações
- Gartner Magic Quadrant For Application Security Testing April 2019 PDFDocumento32 páginasGartner Magic Quadrant For Application Security Testing April 2019 PDFJerry KellyAinda não há avaliações
- ITF+ CompTIA IT Fundamentals A Step by Step Study Guide to Practice Test Questions With Answers and Master the ExamNo EverandITF+ CompTIA IT Fundamentals A Step by Step Study Guide to Practice Test Questions With Answers and Master the ExamAinda não há avaliações
- DoorDash Merchant Portal Step-By-Step GuideDocumento86 páginasDoorDash Merchant Portal Step-By-Step GuideTruc LeAinda não há avaliações
- CIS Controls v8 Mapping To SOC2!2!2023Documento152 páginasCIS Controls v8 Mapping To SOC2!2!2023GillaAinda não há avaliações
- Daily PlanDocumento3 páginasDaily PlancuthrellfamilyAinda não há avaliações
- 3 Secure Development With GitHub SlidesDocumento39 páginas3 Secure Development With GitHub SlidesJorge UsecheAinda não há avaliações
- ESS Patching Policy v1.0.1Documento6 páginasESS Patching Policy v1.0.1vijayarAinda não há avaliações
- Face To Face Communication: EvaluationDocumento24 páginasFace To Face Communication: EvaluationMarko StojanovskiAinda não há avaliações
- Recon Cheat Sheet: For Further Information VisitDocumento2 páginasRecon Cheat Sheet: For Further Information Visit123Ainda não há avaliações
- Cyber Security Risk Management A Complete Guide - 2021 EditionNo EverandCyber Security Risk Management A Complete Guide - 2021 EditionAinda não há avaliações
- Non Relational Database-NoSQLDocumento4 páginasNon Relational Database-NoSQLRam kumarAinda não há avaliações
- Understanding Information SecurityDocumento347 páginasUnderstanding Information SecurityANA CRISTINA CHIRINOS MAinda não há avaliações
- The Laws of IdentityDocumento12 páginasThe Laws of IdentityVaibhav GuptaAinda não há avaliações
- Cybersecurity Management and Policies: The Future of Secure Digital Environments: 1, #1No EverandCybersecurity Management and Policies: The Future of Secure Digital Environments: 1, #1Ainda não há avaliações
- The Physiological ResponseDocumento25 páginasThe Physiological ResponseDaiana Rusu100% (1)
- Fight Fire with Fire: Proactive Cybersecurity Strategies for Today's LeadersNo EverandFight Fire with Fire: Proactive Cybersecurity Strategies for Today's LeadersAinda não há avaliações
- An A-Z Index of The Apple MacOS (OSX) Command Line - SS64 Command Line ReferenceDocumento6 páginasAn A-Z Index of The Apple MacOS (OSX) Command Line - SS64 Command Line Reference2BooksAinda não há avaliações
- CIS Apple macOS 10.13 Benchmark v1.0.0 PDFDocumento196 páginasCIS Apple macOS 10.13 Benchmark v1.0.0 PDFJohn DavisonAinda não há avaliações
- WGU IT - Capstone - Proposal-Excellent-CWDocumento18 páginasWGU IT - Capstone - Proposal-Excellent-CWT.c. FlattAinda não há avaliações
- Amazon Response To House Antitrust Committee On Third-Party Seller DataDocumento3 páginasAmazon Response To House Antitrust Committee On Third-Party Seller DataGeekWireAinda não há avaliações
- USDA Security Manual PDFDocumento30 páginasUSDA Security Manual PDFahjohnston25Ainda não há avaliações
- 5 Ways To Maintain Patient ConfidentialityDocumento2 páginas5 Ways To Maintain Patient ConfidentialityPrincess BalloAinda não há avaliações
- OSINTDocumento2 páginasOSINTjohnAinda não há avaliações
- Guide To Reset Password: Huawei Technologies Co., LTDDocumento4 páginasGuide To Reset Password: Huawei Technologies Co., LTDPhillip RamirezAinda não há avaliações
- Point Of Zero Trust A Complete Guide - 2019 EditionNo EverandPoint Of Zero Trust A Complete Guide - 2019 EditionAinda não há avaliações
- Eeo Storyboard 3Documento93 páginasEeo Storyboard 3api-482724270Ainda não há avaliações
- Database Security Attacks Threats and Challenges IJERTCONV5IS10008Documento4 páginasDatabase Security Attacks Threats and Challenges IJERTCONV5IS10008Hussein AbdullahAinda não há avaliações
- Jurnal Ilyas Awaludin Jaelani PDFDocumento5 páginasJurnal Ilyas Awaludin Jaelani PDFilyasjaelaniAinda não há avaliações
- Database Encryption - An Overview of Contemporary Challenges and Design ConsiderationsDocumento6 páginasDatabase Encryption - An Overview of Contemporary Challenges and Design ConsiderationsKRediAinda não há avaliações
- Database Security PDFDocumento23 páginasDatabase Security PDFUmesh Hengaju0% (1)
- Security of DBMSDocumento6 páginasSecurity of DBMSAshour MostafaAinda não há avaliações
- Security of Database Management Systems: January 2016Documento7 páginasSecurity of Database Management Systems: January 2016aAinda não há avaliações
- DSM Assignment 1Documento15 páginasDSM Assignment 1Malik GoharAinda não há avaliações
- Bit 420 Cat 1 and 2 Gs180289bsitDocumento24 páginasBit 420 Cat 1 and 2 Gs180289bsitMERCY-JEDIDIAH-BELOVED OF JEHOVAH Nungari mukuruAinda não há avaliações
- Quality Assurance Process For Web Applications: March 2018Documento5 páginasQuality Assurance Process For Web Applications: March 2018wali ahmedAinda não há avaliações
- Final Android ManualDocumento96 páginasFinal Android Manualwali ahmedAinda não há avaliações
- Dr. Atif Sher ASCVD CardioConDocumento21 páginasDr. Atif Sher ASCVD CardioConwali ahmedAinda não há avaliações
- Mah Ru Nisa .: Education SkillsDocumento1 páginaMah Ru Nisa .: Education Skillswali ahmedAinda não há avaliações
- Project Appraisal and FinanceDocumento11 páginasProject Appraisal and Financewali ahmedAinda não há avaliações
- Values of RespectDocumento19 páginasValues of Respectwali ahmedAinda não há avaliações
- Working Capital ManagementDocumento4 páginasWorking Capital Managementwali ahmedAinda não há avaliações
- Factors Affecting The Quality of Auditing: The Case of Jordanian Commercial BanksDocumento3 páginasFactors Affecting The Quality of Auditing: The Case of Jordanian Commercial Bankswali ahmedAinda não há avaliações
- Social Issues in Private and Public Schools at Secondary LevelDocumento1 páginaSocial Issues in Private and Public Schools at Secondary Levelwali ahmedAinda não há avaliações
- Name PageDocumento1 páginaName Pagewali ahmedAinda não há avaliações
- Corrected 5th CapterDocumento11 páginasCorrected 5th Capterwali ahmedAinda não há avaliações
- Research Ethics: Research Ethics Involves The Application of Fundamental Ethical Principles To A VarietyDocumento4 páginasResearch Ethics: Research Ethics Involves The Application of Fundamental Ethical Principles To A Varietywali ahmedAinda não há avaliações
- Lahore College For Women University, Lahore Department of EducationDocumento1 páginaLahore College For Women University, Lahore Department of Educationwali ahmedAinda não há avaliações
- Chapter 3Documento4 páginasChapter 3wali ahmedAinda não há avaliações
- Chapter 3Documento4 páginasChapter 3wali ahmedAinda não há avaliações
- Literature Review: Definition of Social IssuesDocumento17 páginasLiterature Review: Definition of Social Issueswali ahmedAinda não há avaliações
- 3rd PageDocumento1 página3rd Pagewali ahmedAinda não há avaliações
- Questionnaire Page (End)Documento1 páginaQuestionnaire Page (End)wali ahmedAinda não há avaliações
- Project Proposal Taxi Booking ServiceDocumento5 páginasProject Proposal Taxi Booking Servicewali ahmedAinda não há avaliações
- Practical Architectural Approach For Composing Egocentric TrustDocumento3 páginasPractical Architectural Approach For Composing Egocentric Trustwali ahmedAinda não há avaliações
- Punjab Group of Colleges: Spring 2019Documento6 páginasPunjab Group of Colleges: Spring 2019wali ahmedAinda não há avaliações
- Country Report On Decentralization in The Education System of Pakistan: Policies and StrategiesDocumento14 páginasCountry Report On Decentralization in The Education System of Pakistan: Policies and Strategieswali ahmedAinda não há avaliações
- Topic For ThisisDocumento15 páginasTopic For Thisiswali ahmedAinda não há avaliações
- LITERATURE MATRIX PLAN LastimosaDocumento2 páginasLITERATURE MATRIX PLAN LastimosaJoebelle LastimosaAinda não há avaliações
- Di Franco Amended Factum 2021-05-03Documento30 páginasDi Franco Amended Factum 2021-05-03Michael BueckertAinda não há avaliações
- Elements of Visual Design in The Landscape - 26.11.22Documento15 páginasElements of Visual Design in The Landscape - 26.11.22Delnard OnchwatiAinda não há avaliações
- Mohd Ali 17: By:-Roll NoDocumento12 páginasMohd Ali 17: By:-Roll NoMd AliAinda não há avaliações
- EP105Use of English ArantxaReynosoDocumento6 páginasEP105Use of English ArantxaReynosoArantxaSteffiAinda não há avaliações
- Simplified Cost Accounting Part Ii: Solutions ManualDocumento58 páginasSimplified Cost Accounting Part Ii: Solutions ManualAnthony Koko CarlobosAinda não há avaliações
- RCPI V VerchezDocumento2 páginasRCPI V VerchezCin100% (1)
- Philippines My Beloved (Rough Translation by Lara)Documento4 páginasPhilippines My Beloved (Rough Translation by Lara)ARLENE FERNANDEZAinda não há avaliações
- Biology Chapter 23.1Documento2 páginasBiology Chapter 23.1Carlos Enrique Altamar BorjaAinda não há avaliações
- Caste & PoliticsDocumento4 páginasCaste & PoliticsGIRISHA THAKURAinda não há avaliações
- Breast Cancer ChemotherapyDocumento7 páginasBreast Cancer Chemotherapydini kusmaharaniAinda não há avaliações
- Read Chapter 4 Minicase: Fondren Publishing, Inc. From The Sales Force Management Textbook by Mark W. Johnston & Greg W. MarshallDocumento1 páginaRead Chapter 4 Minicase: Fondren Publishing, Inc. From The Sales Force Management Textbook by Mark W. Johnston & Greg W. MarshallKJRAinda não há avaliações
- 2 Beginner 2nd GradeDocumento12 páginas2 Beginner 2nd GradesebAinda não há avaliações
- Berms For Stablizing Earth Retaining Structures: Youssef Gomaa Youssef Morsi B.SC., Civil EngineeringDocumento212 páginasBerms For Stablizing Earth Retaining Structures: Youssef Gomaa Youssef Morsi B.SC., Civil EngineeringChan KAinda não há avaliações
- Appraising The Secretaries of Sweet Water UniversityDocumento4 páginasAppraising The Secretaries of Sweet Water UniversityZain4uAinda não há avaliações
- Mus Culo SkeletalDocumento447 páginasMus Culo SkeletalKristine NicoleAinda não há avaliações
- Afghanistan Law Bibliography 3rd EdDocumento28 páginasAfghanistan Law Bibliography 3rd EdTim MathewsAinda não há avaliações
- Mount Athos Plan - Healthy Living (PT 2)Documento8 páginasMount Athos Plan - Healthy Living (PT 2)Matvat0100% (2)
- NIPMR Notification v3Documento3 páginasNIPMR Notification v3maneeshaAinda não há avaliações
- CB Insights Venture Report 2021Documento273 páginasCB Insights Venture Report 2021vulture212Ainda não há avaliações
- IPA Digital Media Owners Survey Autumn 2010Documento33 páginasIPA Digital Media Owners Survey Autumn 2010PaidContentUKAinda não há avaliações
- Lesson Plan 2 Revised - Morgan LegrandDocumento19 páginasLesson Plan 2 Revised - Morgan Legrandapi-540805523Ainda não há avaliações
- Neuromarketing EssayDocumento3 páginasNeuromarketing Essayjorge jmzAinda não há avaliações
- Singular & Plural Nouns: Regular PluralsDocumento4 páginasSingular & Plural Nouns: Regular PluralsМарина ВетерAinda não há avaliações
- WatsuDocumento5 páginasWatsuTIME-TREVELER100% (1)
- Simple Linear Regression Analysis: Mcgraw-Hill/IrwinDocumento16 páginasSimple Linear Regression Analysis: Mcgraw-Hill/IrwinNaeem AyazAinda não há avaliações
- The Acceptability of Indian Mango Leaves Powdered As A Tea: (Mangifera Indica Linn.)Documento22 páginasThe Acceptability of Indian Mango Leaves Powdered As A Tea: (Mangifera Indica Linn.)Marissa M. DoriaAinda não há avaliações
- LDS Conference Report 1930 Semi AnnualDocumento148 páginasLDS Conference Report 1930 Semi AnnualrjjburrowsAinda não há avaliações
- AVEVA Work Permit ManagerDocumento2 páginasAVEVA Work Permit ManagerMohamed Refaat100% (1)
- Autobiography of A 2nd Generation Filipino-AmericanDocumento4 páginasAutobiography of A 2nd Generation Filipino-AmericanAio Min100% (1)