Escolar Documentos
Profissional Documentos
Cultura Documentos
Class Loader Architecture
Enviado por
satyanarayana0 notas0% acharam este documento útil (0 voto)
27 visualizações9 páginasJava's security model is focused on protecting end-users from hostile programs. To accomplish this goal, Java provides a customizable "sandbox" in which programs run. A program can do anything within the boundaries of its sandbox, but it can't take any action outside those boundaries.
Descrição original:
Direitos autorais
© Attribution Non-Commercial (BY-NC)
Formatos disponíveis
PPT ou leia online no Scribd
Compartilhar este documento
Compartilhar ou incorporar documento
Você considera este documento útil?
Este conteúdo é inapropriado?
Denunciar este documentoJava's security model is focused on protecting end-users from hostile programs. To accomplish this goal, Java provides a customizable "sandbox" in which programs run. A program can do anything within the boundaries of its sandbox, but it can't take any action outside those boundaries.
Direitos autorais:
Attribution Non-Commercial (BY-NC)
Formatos disponíveis
Baixe no formato PPT ou leia online no Scribd
0 notas0% acharam este documento útil (0 voto)
27 visualizações9 páginasClass Loader Architecture
Enviado por
satyanarayanaJava's security model is focused on protecting end-users from hostile programs. To accomplish this goal, Java provides a customizable "sandbox" in which programs run. A program can do anything within the boundaries of its sandbox, but it can't take any action outside those boundaries.
Direitos autorais:
Attribution Non-Commercial (BY-NC)
Formatos disponíveis
Baixe no formato PPT ou leia online no Scribd
Você está na página 1de 9
A sandbox refresher
Java's security model is focused on
protecting end-users from hostile
programs downloaded from untrusted
sources across a network. To accomplish
this goal, Java provides a customizable
"sandbox" in which Java programs run. A
Java program can do anything within the
boundaries of its sandbox, but it can't take
any action outside those boundaries. The
sandbox for untrusted Java applets, for
example, prohibits many activities,
including:
reading or writing to the local disk
making a network connection to any host,
except the host from which the applet
came
creating a new process
loading a new dynamic library and directly
calling a native method
CLASS LOADER Architecture
Types
• Primitive Types
• Reference Types
• Array Types
• Subtypes and Compatibility
• Signatures and Subsumption
shadowing
• http://www.perisic.com/shadow/
The following rules determine when a type t1 is a subtype of a type t2:
• Every type is a subtype of itself.
• If t1 is a subtype of t2, and t2 is a subtype of t3, then t1 is a subtype of t3.
• char is a subtype of int, long, float, and double.
• byte is a subtype of short, int, long, float, and double.
• short is a subtype of int, long, float, and double.
• int is a subtype of long, float, and double.
• long is a subtype of float and double.
• float is a subtype of double.
• If t1 and t2 are classes, then t1 is a subtype of t2 if t1 is a subclass of t2.
• If t1 and t2 are interfaces, then t1 is a subtype of t2 if t1 is a subinterface
of t2.
• If t1 is a class and t2 is an interface, then t1 is a subtype of t2 provided
that t1 (is a
• subclass of a class that) implements t2 or implements a subinterface of t2.
• Array type t1 [] is a subtype of array type t2 [] if reference type t1 is a
subtype of
• reference type t2.
• Any reference type t, including any array type, is also a subtype of
predefined class Object.
• No primitive type is a subtype of a reference type. No reference type is a
subtype of a primitive type.
Command Line argument
• A Java application can accept any number
of arguments from the command line
• When an application is launched, the
runtime system passes the command-line
arguments to the application's main
method via an array of Strings.
Operator Precedence
() [] .
! ~ ++ -- + - (Data Type)
* / %
+ -
<< >> >>>
< <= > >= instance
== !=
&^|
&&
||
? :
= += -= *= /= %= &= ^= |= <<= >>= >>>=
Not all combinations of instance and class variables
and methods are allowed:
• Instance methods can access instance variables
and instance methods directly.
• Instance methods can access class variables
and class methods directly.
• Class methods can access class variables and
class methods directly.
• Class methods cannot access instance variables
or instance methods directly—they must use an
object reference. Also, class methods cannot
use the this keyword as there is no instance for
this to refer
Você também pode gostar
- A Heartbreaking Work Of Staggering Genius: A Memoir Based on a True StoryNo EverandA Heartbreaking Work Of Staggering Genius: A Memoir Based on a True StoryNota: 3.5 de 5 estrelas3.5/5 (231)
- The Sympathizer: A Novel (Pulitzer Prize for Fiction)No EverandThe Sympathizer: A Novel (Pulitzer Prize for Fiction)Nota: 4.5 de 5 estrelas4.5/5 (121)
- Devil in the Grove: Thurgood Marshall, the Groveland Boys, and the Dawn of a New AmericaNo EverandDevil in the Grove: Thurgood Marshall, the Groveland Boys, and the Dawn of a New AmericaNota: 4.5 de 5 estrelas4.5/5 (266)
- The Little Book of Hygge: Danish Secrets to Happy LivingNo EverandThe Little Book of Hygge: Danish Secrets to Happy LivingNota: 3.5 de 5 estrelas3.5/5 (400)
- Never Split the Difference: Negotiating As If Your Life Depended On ItNo EverandNever Split the Difference: Negotiating As If Your Life Depended On ItNota: 4.5 de 5 estrelas4.5/5 (838)
- The Emperor of All Maladies: A Biography of CancerNo EverandThe Emperor of All Maladies: A Biography of CancerNota: 4.5 de 5 estrelas4.5/5 (271)
- The Subtle Art of Not Giving a F*ck: A Counterintuitive Approach to Living a Good LifeNo EverandThe Subtle Art of Not Giving a F*ck: A Counterintuitive Approach to Living a Good LifeNota: 4 de 5 estrelas4/5 (5794)
- The World Is Flat 3.0: A Brief History of the Twenty-first CenturyNo EverandThe World Is Flat 3.0: A Brief History of the Twenty-first CenturyNota: 3.5 de 5 estrelas3.5/5 (2259)
- The Hard Thing About Hard Things: Building a Business When There Are No Easy AnswersNo EverandThe Hard Thing About Hard Things: Building a Business When There Are No Easy AnswersNota: 4.5 de 5 estrelas4.5/5 (344)
- Team of Rivals: The Political Genius of Abraham LincolnNo EverandTeam of Rivals: The Political Genius of Abraham LincolnNota: 4.5 de 5 estrelas4.5/5 (234)
- The Gifts of Imperfection: Let Go of Who You Think You're Supposed to Be and Embrace Who You AreNo EverandThe Gifts of Imperfection: Let Go of Who You Think You're Supposed to Be and Embrace Who You AreNota: 4 de 5 estrelas4/5 (1090)
- Hidden Figures: The American Dream and the Untold Story of the Black Women Mathematicians Who Helped Win the Space RaceNo EverandHidden Figures: The American Dream and the Untold Story of the Black Women Mathematicians Who Helped Win the Space RaceNota: 4 de 5 estrelas4/5 (895)
- Elon Musk: Tesla, SpaceX, and the Quest for a Fantastic FutureNo EverandElon Musk: Tesla, SpaceX, and the Quest for a Fantastic FutureNota: 4.5 de 5 estrelas4.5/5 (474)
- The Unwinding: An Inner History of the New AmericaNo EverandThe Unwinding: An Inner History of the New AmericaNota: 4 de 5 estrelas4/5 (45)
- The Yellow House: A Memoir (2019 National Book Award Winner)No EverandThe Yellow House: A Memoir (2019 National Book Award Winner)Nota: 4 de 5 estrelas4/5 (98)
- Python Programming Training CourseDocumento8 páginasPython Programming Training CourseShahirul AzamAinda não há avaliações
- Ruby NotesDocumento234 páginasRuby NotesTrung LeeAinda não há avaliações
- Nurbs PythonDocumento92 páginasNurbs PythonFutui MasaAinda não há avaliações
- Cs193i - Internet Technologies Summer 2004 Stanford UniversityDocumento63 páginasCs193i - Internet Technologies Summer 2004 Stanford Universitysathya_mca17Ainda não há avaliações
- Spring XML and Annotation DifferenceDocumento4 páginasSpring XML and Annotation DifferencesatyanarayanaAinda não há avaliações
- Collection FrameworkDocumento3 páginasCollection FrameworksatyanarayanaAinda não há avaliações
- Mysql Editor Shorcut KeysDocumento3 páginasMysql Editor Shorcut KeyssatyanarayanaAinda não há avaliações
- Introduction To Application Server: EJB 3.0 BasicsDocumento4 páginasIntroduction To Application Server: EJB 3.0 BasicssatyanarayanaAinda não há avaliações
- 100+ Run CommandsDocumento3 páginas100+ Run CommandsRamu MalayathiAinda não há avaliações
- Inventory Management ERPDocumento35 páginasInventory Management ERPsatyanarayanaAinda não há avaliações
- TomcatSSL ErrorDocumento1 páginaTomcatSSL ErrorsatyanarayanaAinda não há avaliações
- JDBC Drivers and UrlDocumento14 páginasJDBC Drivers and Urlsatyanarayana100% (1)
- JSP Interview QuestionsDocumento21 páginasJSP Interview Questionssatyanarayana100% (3)
- JF1 3Documento3 páginasJF1 3satyanarayanaAinda não há avaliações
- Service Oriented ArchitectureDocumento5 páginasService Oriented ArchitecturesatyanarayanaAinda não há avaliações
- Some Important Faqs On JavaDocumento57 páginasSome Important Faqs On JavasatyanarayanaAinda não há avaliações
- Answer Answer: ServletsDocumento9 páginasAnswer Answer: ServletssatyanarayanaAinda não há avaliações
- Complete Java&J2 EEDocumento120 páginasComplete Java&J2 EEVenkata Hari PrasadAinda não há avaliações
- JDBCDocumento28 páginasJDBCsatyanarayanaAinda não há avaliações
- JDBC 13Documento13 páginasJDBC 13satyanarayanaAinda não há avaliações
- ServletsDocumento17 páginasServletssatyanarayanaAinda não há avaliações
- 7 ServletDocumento15 páginas7 ServletsatyanarayanaAinda não há avaliações
- Java Server Faces (JSF) : JAVA SERVER FACES (Not To Be Confused With JSP..JAVA SERVER PAGES), Is TheDocumento30 páginasJava Server Faces (JSF) : JAVA SERVER FACES (Not To Be Confused With JSP..JAVA SERVER PAGES), Is ThesatyanarayanaAinda não há avaliações
- Parsing HTTP Requests Handling Connections To Web ClientsDocumento31 páginasParsing HTTP Requests Handling Connections To Web ClientssatyanarayanaAinda não há avaliações
- 7 ServletDocumento15 páginas7 ServletsatyanarayanaAinda não há avaliações
- Joshi: Presentation byDocumento26 páginasJoshi: Presentation bysatyanarayanaAinda não há avaliações
- Joshi: Presentation byDocumento26 páginasJoshi: Presentation bysatyanarayanaAinda não há avaliações
- Srujan JSPDocumento38 páginasSrujan JSPsatyanarayanaAinda não há avaliações
- Roles in Web-Application DevelopmentDocumento7 páginasRoles in Web-Application DevelopmentsatyanarayanaAinda não há avaliações
- 8 JSPDocumento50 páginas8 JSPsatyanarayanaAinda não há avaliações
- 8 JSPDocumento50 páginas8 JSPsatyanarayanaAinda não há avaliações
- Overview of Enterprise Java BeansDocumento39 páginasOverview of Enterprise Java BeanssatyanarayanaAinda não há avaliações
- Srujan TaglibDocumento9 páginasSrujan TaglibsatyanarayanaAinda não há avaliações
- Lecture1 StringsDocumento16 páginasLecture1 StringsFoainaAinda não há avaliações
- 4 CoeDocumento46 páginas4 Coe27296621Ainda não há avaliações
- Project2 KRR 2011Documento1 páginaProject2 KRR 2011Manuel Adelin ManolacheAinda não há avaliações
- Software Engineering B.Tech IT/II Sem-IIDocumento34 páginasSoftware Engineering B.Tech IT/II Sem-IIgouthami reddyAinda não há avaliações
- MultipleChoicePractice Final Solution PDFDocumento15 páginasMultipleChoicePractice Final Solution PDFĐặng Phương AnhAinda não há avaliações
- INT402 Quiz (Unit 1 To 6)Documento143 páginasINT402 Quiz (Unit 1 To 6)Hancy NixonAinda não há avaliações
- Arguments Question 1Documento9 páginasArguments Question 1rahul rastogiAinda não há avaliações
- Java 9 Real - TimeDocumento57 páginasJava 9 Real - TimeDiego AmayaAinda não há avaliações
- IED Object Models: Dr. Alexander ApostolovDocumento44 páginasIED Object Models: Dr. Alexander ApostolovIDI EnergyAinda não há avaliações
- Kebele Managemnet System OneDocumento64 páginasKebele Managemnet System OneNega AgmasAinda não há avaliações
- Chitrank It - FinalDocumento36 páginasChitrank It - FinalChitrank ShuklAinda não há avaliações
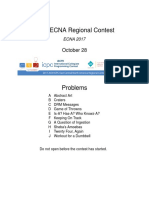
- Acmicpc East Central North America Regional Contest Ecna 2017 enDocumento22 páginasAcmicpc East Central North America Regional Contest Ecna 2017 enDuarte Garcia JorgeAinda não há avaliações
- Syllabus:: Punyashlok Ahilyadevi Holkar Solapur University, SolapurDocumento22 páginasSyllabus:: Punyashlok Ahilyadevi Holkar Solapur University, SolapurRohan YadavAinda não há avaliações
- Polymorphism Lecture 1.ppsDocumento86 páginasPolymorphism Lecture 1.ppsMarin_1wqAinda não há avaliações
- Hyperjaxb 2 - Relation Persistence For JAXB Objects: Reference DocumentationDocumento54 páginasHyperjaxb 2 - Relation Persistence For JAXB Objects: Reference DocumentationhumbertorochaAinda não há avaliações
- Java Generics TutorialDocumento2 páginasJava Generics TutorialManoj Kumar GAinda não há avaliações
- Online Investment and Loan Application: Tan WeiDocumento87 páginasOnline Investment and Loan Application: Tan WeimafuyucAinda não há avaliações
- Access Modifiers in C#Documento6 páginasAccess Modifiers in C#AshokAinda não há avaliações
- 2100 (Aug15) Tutorials - Complete SetDocumento16 páginas2100 (Aug15) Tutorials - Complete SetLim Weng SeongAinda não há avaliações
- Travel Chaperon 4052Documento83 páginasTravel Chaperon 4052addssdfaAinda não há avaliações
- Microsoft 98-361 Dumps With Valid 98-361 Exam Questions PDF (2018)Documento10 páginasMicrosoft 98-361 Dumps With Valid 98-361 Exam Questions PDF (2018)Luis CuroAinda não há avaliações
- Document XamarinDocumento1.756 páginasDocument XamarinCepi SupriadiAinda não há avaliações
- Ns 3 TutorialDocumento105 páginasNs 3 TutorialGwangwoo ParkAinda não há avaliações
- SCJA (Exam 310-019) Questions ExamDocumento0 páginaSCJA (Exam 310-019) Questions ExamDexter SouzaAinda não há avaliações
- Developing Task Model Applications: Aneka Tutorial SeriesDocumento41 páginasDeveloping Task Model Applications: Aneka Tutorial SeriessnaveenrajaAinda não há avaliações
- Class Diagram - 2023Documento9 páginasClass Diagram - 2023shivank tiwariAinda não há avaliações
- Oopr211 MidtermDocumento120 páginasOopr211 MidtermChristine Marie CasasAinda não há avaliações