DocumentoHacking - CEH Cheat Sheet Exercisesenviado por
DocumentoHacking - CEH Cheat Sheet Exercisesenviado por rgolfnut1
rgolfnut1 DocumentoRapsodo Mobile Launch Monitor Review The Breakfast Ballenviado por
DocumentoRapsodo Mobile Launch Monitor Review The Breakfast Ballenviado por rgolfnut1
rgolfnut1 DocumentoSheriff's Sale No. 2018-13893enviado por
DocumentoSheriff's Sale No. 2018-13893enviado por rgolfnut1
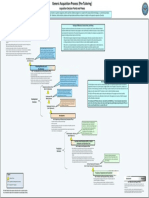
rgolfnut1 DocumentoDefense Acquisition Process Waterfall Methodenviado por
DocumentoDefense Acquisition Process Waterfall Methodenviado por rgolfnut1
rgolfnut1 DocumentoFundamentals of System Acquisition Mgmt Part2enviado por
DocumentoFundamentals of System Acquisition Mgmt Part2enviado por rgolfnut1
rgolfnut1 DocumentoATTACKS by OSI model Layers DDoS Quick Guide.pdfenviado por
DocumentoATTACKS by OSI model Layers DDoS Quick Guide.pdfenviado por rgolfnut1
rgolfnut1 DocumentoSteganographic Embedding Undetectable by JPEG Compatibility Steganalysis Newman etal2002.pdfenviado por
DocumentoSteganographic Embedding Undetectable by JPEG Compatibility Steganalysis Newman etal2002.pdfenviado por rgolfnut1
rgolfnut1 DocumentoSteganographic Embedding Undetectable by JPEG Compatibility Steganalysis Newman Etal2002enviado por
DocumentoSteganographic Embedding Undetectable by JPEG Compatibility Steganalysis Newman Etal2002enviado por rgolfnut1
rgolfnut1 DocumentoShavlik Patch User Guideenviado por
DocumentoShavlik Patch User Guideenviado por rgolfnut1
rgolfnut1 DocumentoRegistryDecoder Offline Analysis Instructions v1.1 (1)enviado por
DocumentoRegistryDecoder Offline Analysis Instructions v1.1 (1)enviado por rgolfnut1
rgolfnut1 DocumentoFundamental Computer Investigation Guide for Windowsenviado por
DocumentoFundamental Computer Investigation Guide for Windowsenviado por rgolfnut1
rgolfnut1 DocumentoGolf Swing Speed Training Logenviado por
DocumentoGolf Swing Speed Training Logenviado por rgolfnut1
rgolfnut1 DocumentoRotator Cuff and AB Exercisesenviado por
DocumentoRotator Cuff and AB Exercisesenviado por rgolfnut1
rgolfnut1 DocumentoLinear Codes - cryptographyenviado por
DocumentoLinear Codes - cryptographyenviado por rgolfnut1
rgolfnut1 DocumentoCryptography - Lecture1enviado por
DocumentoCryptography - Lecture1enviado por rgolfnut1
rgolfnut1 DocumentoOrthogonal Matricesenviado por
DocumentoOrthogonal Matricesenviado por rgolfnut1
rgolfnut1 DocumentoLouisian Private Investigator Lawsenviado por
DocumentoLouisian Private Investigator Lawsenviado por rgolfnut1
rgolfnut1 DocumentoInstallShield AdminStudio ConfiguringRepackage PHrenviado por
DocumentoInstallShield AdminStudio ConfiguringRepackage PHrenviado por rgolfnut1
rgolfnut1 DocumentoInstallShield AdminStudio ConfiguringRepackage PHrenviado por
DocumentoInstallShield AdminStudio ConfiguringRepackage PHrenviado por rgolfnut1
rgolfnut1 DocumentoInstallShield AdminStudio ConfiguringRepackage PHrenviado por
DocumentoInstallShield AdminStudio ConfiguringRepackage PHrenviado por rgolfnut1
rgolfnut1 DocumentoTypes of Forgeriesenviado por
DocumentoTypes of Forgeriesenviado por rgolfnut1
rgolfnut1 DocumentoStat Formulasenviado por
DocumentoStat Formulasenviado por rgolfnut1
rgolfnut1 DocumentoEcryptfs Enterprise Linuxenviado por
DocumentoEcryptfs Enterprise Linuxenviado por rgolfnut1
rgolfnut1 DocumentoFatness to Fitness Digital Versionenviado por
DocumentoFatness to Fitness Digital Versionenviado por rgolfnut1
rgolfnut1 DocumentoFEMA ICS200_Student Manualenviado por
DocumentoFEMA ICS200_Student Manualenviado por rgolfnut1
rgolfnut1 DocumentoMold_remediation Instructions Univ South Carolinaenviado por
DocumentoMold_remediation Instructions Univ South Carolinaenviado por rgolfnut1
rgolfnut1 Documento09.02.10.HashingPasswords Class.csci4621enviado por
Documento09.02.10.HashingPasswords Class.csci4621enviado por rgolfnut1
rgolfnut1 Documento09.02.10.BirthdayParadox.CSC4621enviado por
Documento09.02.10.BirthdayParadox.CSC4621enviado por rgolfnut1
rgolfnut1 Documento9.23.10.Polyinstantiation PDFenviado por
Documento9.23.10.Polyinstantiation PDFenviado por rgolfnut1
rgolfnut1 DocumentoSocket Programmingenviado por
DocumentoSocket Programmingenviado por rgolfnut1
rgolfnut1 Documento47349048 Malware Detection Using OWA Measureenviado por
Documento47349048 Malware Detection Using OWA Measureenviado por rgolfnut1
rgolfnut1 DocumentoGeologic Conditions Beneath New Orleansenviado por
DocumentoGeologic Conditions Beneath New Orleansenviado por rgolfnut1
rgolfnut1 DocumentoAbsolute Value Inequalitiesenviado por
DocumentoAbsolute Value Inequalitiesenviado por rgolfnut1
rgolfnut1 DocumentoPenetration Testing Sample Reportenviado por
DocumentoPenetration Testing Sample Reportenviado por rgolfnut1
rgolfnut1 DocumentoLinux Security Quick Reference Guideenviado por
DocumentoLinux Security Quick Reference Guideenviado por rgolfnut1
rgolfnut1 DocumentoLimits of Steganographyenviado por
DocumentoLimits of Steganographyenviado por rgolfnut1
rgolfnut1 Documentogdb-refcardenviado por
Documentogdb-refcardenviado por rgolfnut1
rgolfnut1 DocumentoEmacs Referenceenviado por
DocumentoEmacs Referenceenviado por rgolfnut1
rgolfnut1 DocumentoArray List ADT'senviado por
DocumentoArray List ADT'senviado por rgolfnut1
rgolfnut1 DocumentoComplex Networksenviado por
DocumentoComplex Networksenviado por rgolfnut1
rgolfnut1 DocumentoSet Theory Functionsenviado por
DocumentoSet Theory Functionsenviado por rgolfnut1
rgolfnut1
Escolar Documentos
Profissional Documentos
Cultura Documentos